
How To: Create a MySQL Server BruteForce Tool with Python
Hello aspiring hackers, It's been a while since I wrote a tutorial, so I figured I might just share one of the tools that I have created to help the community grow.


Hello aspiring hackers, It's been a while since I wrote a tutorial, so I figured I might just share one of the tools that I have created to help the community grow.
I've been doing tutorials on Rasberry Pi and I would like to thank everyone that have both read the tutorials and gave me feedback on how well I'm doing. But now I've decided to take a small break and start a mini series that I'm hoping to be at least five tutorials. This doesn't mean I'm gonna stop posting Raspberry Pi tutorials, but since I'm learning so much at the same time I've decided to share some of that knowledge. Hence this tutorial. Please sit back, relax and read on.

Welcome back to a tutorial on malware. We'll be discovering a method to beef up our little trooper. Without further ado, let's jump right in!

In an article published in early-2015 by Peninsula Press, it was reported that the demand and the salaries for cyber security professionals are exploding! They cite that 209,000 cyber security jobs were unfilled last year, and that job postings have increased over 74% in the last 5 years. Job opening are expected to grow by another 53% over the next 3 years. You are definitely in the right field, my tenderfoot hackers! Some researchers are expecting information security jobs to continue to gr...

When it's time to get down to work, a clean, organized workstation is key to accomplishing tasks and being more productive. Or, so we thought.

Though you can use the Social Engineering Toolkit to clone websites, this way is much more customisable.

From day to day, it can be difficult to remember everything that's required of you. I tend to forget exactly where it is I'm supposed to be during my busiest moments, and it's even easier to delete each day's events out of your brain when there's so much else that dominates your mind. Yet taking the time to remember exactly what it is that happens during each of our days can be a vital part of our memory—and with nothing more than 15 minutes, we can strengthen our brains and remember more tha...

Brought to you by Brother International Corporation. Whether you are looking to complete a home improvement task, or you are hoping to start a new hobby, staying focused and energized during projects can be daunting. With emphasis on organization, planning, and creativity, we gathered together tips that will help you successfully tackle any project on your plate!

We're a little butter-obsessed here, and that includes topics on why butter should always be browned, the rationale behind clarifying butter, and even how to make a DIY butter candle. And while some may consider the problem strictly one for the first world, we're always very interested in ways to spread cold butter on toast without ripping the bread to shreds. If you read that post, you know the ingenious solutions are many and range from grating your butter to buying a heated butter knife.

When I was young, I wanted nothing more but to be able to freeze things just like one of my favorite X-Men characters, Iceman. Now, Disney's most successful animated film to date, Frozen, brought another icy childhood favorite to the scene—The Snow Queen. And with Halloween right around the corner, all of the princesses out there can get their chance at being ice royalty. While Princess Anna and Olaf the Snowman were the biggest characters in Frozen, Elsa is one of the movie's most memorable ...

While the adoption of Apple's newest mobile operating system, iOS 8, was smoother than its predecessor, there were still a lot of bugs and features that needed ironed out. There were lost cellular signals, missing Camera Rolls, a confusing iCloud Drive, and no functioning Apple Pay yet, among other things. Now it's just over a month later from its first release to the public and things are finally looking pretty good.

Investing is like exercise—we all know we should be doing more of it, but we often just can't find the time. I mean, really, who's got the hours, inclination, and skill to pour through volumes of data and put together a balanced yet sophisticated portfolio of investment vehicles tailored specifically to optimize their returns while mitigating potential risks. Not me, that's for sure.

While LG G3 users have been patiently waiting, developer the cubed and his Codefire team have been diligently working on a successful unlock method for the heavily locked-down bootloader. Now it's finally here, and the unlocking method is extremely easy to do—and it works for all G3 variants.

Admit it: you've been caught muttering to yourself under your breath in very public places. Maybe you've gotten stares while wandering the grocery store talking to yourself out loud. If you're like me, you might even talk yourself through various tasks, giving the atmosphere a little background noise.

More and more devices are using iOS 8 over iOS 7, and that means more and more developers are adding iOS 8-friendly features to their apps, especially widgets. However, not every widget available for your Notification Center right now is awesome. Take for example the Dropbox widget—it's essentially nothing more than a real-time notification, as the only action it performs is opening a recently updated file within the app.

Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective.
Loaded with a gorgeous display and a powerful processor, the Kindle Fire HDX is an impressive all-around tablet, especially when it's used for what Amazon Kindles were built for—reading electronic versions of novels, textbooks, and other printed works.

Clash of Clans is one of the most successful games ever to come out for Android and iOS. It has been downloaded over 50 million times from Google Play alone, and shows no signs of decline.
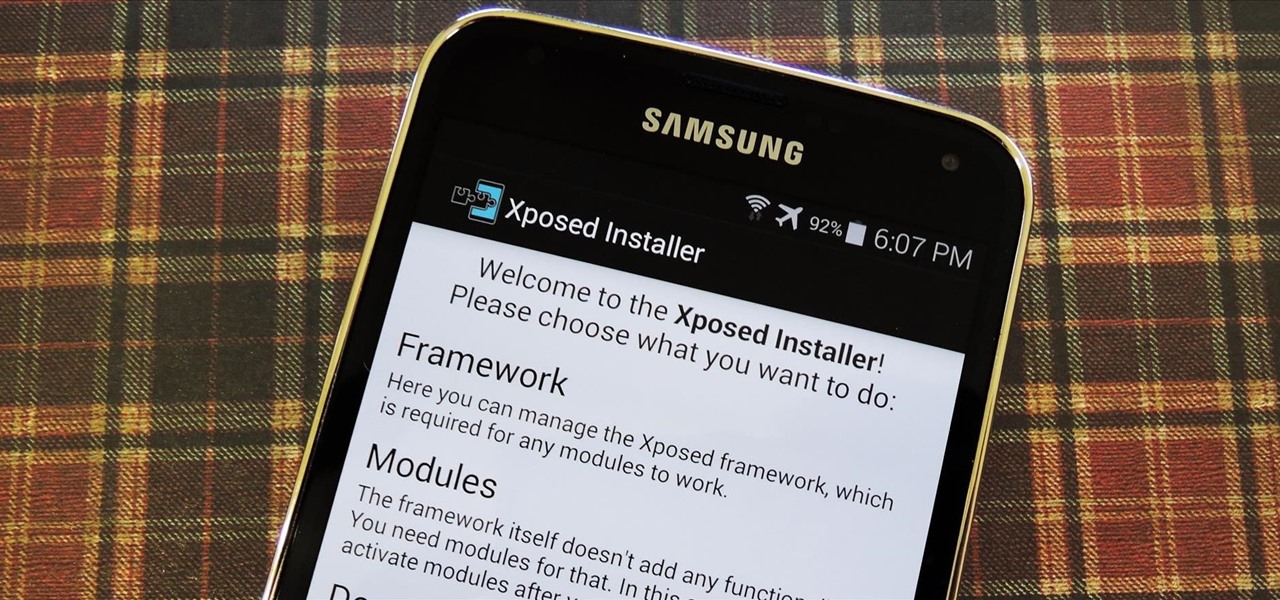
Now that all variants of the Galaxy S5 have finally been rooted, we can start exploring all of the tweaks and hacks that Superuser privileges open up to us.

Veering from common practice, XDA commenter, "the_commenter", discovered a changelog for the upcoming version of Android 4.4.3 tucked away on Google's servers.

Doritos Locos Tacos were the brilliant concoction of a man named Todd Mills who never worked for Taco Bell, and never made any money from his creation. He originally pitched the idea to Frito-Lay, and when they said no, he took matters into his own hands by creating a Facebook page.
Applying for jobs can be a truly miserable experience. Sending out endless résumés, filling out those janky online applications, and creating cover letters can really wear a person down. So, any suggestions that make that process easier are always welcome.

Communication is the key to any healthy relationship, and when I say any, I mean human and non-human. Previously, one of the biggest culprits for not understanding what you meant was Siri, but now it looks like it has some competition with the new Kinect system, which can control practically everything on your Xbox One—if it can understand you.

Welcome back, my fledgling hackers! Awhile back, I demonstrated one of my favorite little tools, netcat, which enables us to create a connection between any two machines and transfer files or spawn a command shell for "owning" the system. Despite the beauty and elegance of this little tool, it has one major drawback—the transfers between the computers can be detected by security devices such as firewalls and an intrusion detection system (IDS).

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

You may not notice it when you're intoxicated and banging your head to the music, but when you're at a club or concert, your ears are getting seriously damaged. The noise level is usually above most people's pain threshold for sound, which begins around 120 to 140 decibels. At that level, it only takes a few minutes to damage your hearing. For me, there's something even worse than long-term hearing loss in a loud environment—not being able to hear or talk to your friends.

Search Engine Optimization is important for every successful SEO or blogging campaign. Therefore it is required to be implemented in the correct manner. Google consider many factors while ranking a webpage and it keeps on changing. Some of the common SEO mistakes which you must avoid are as follows:

While the majority of America was watching the Super Bowl yesterday, the crew over at the evad3rs was finishing its work on their untethered iOS 6.1 jailbreak called evasi0n. Well, the wait is finally over!
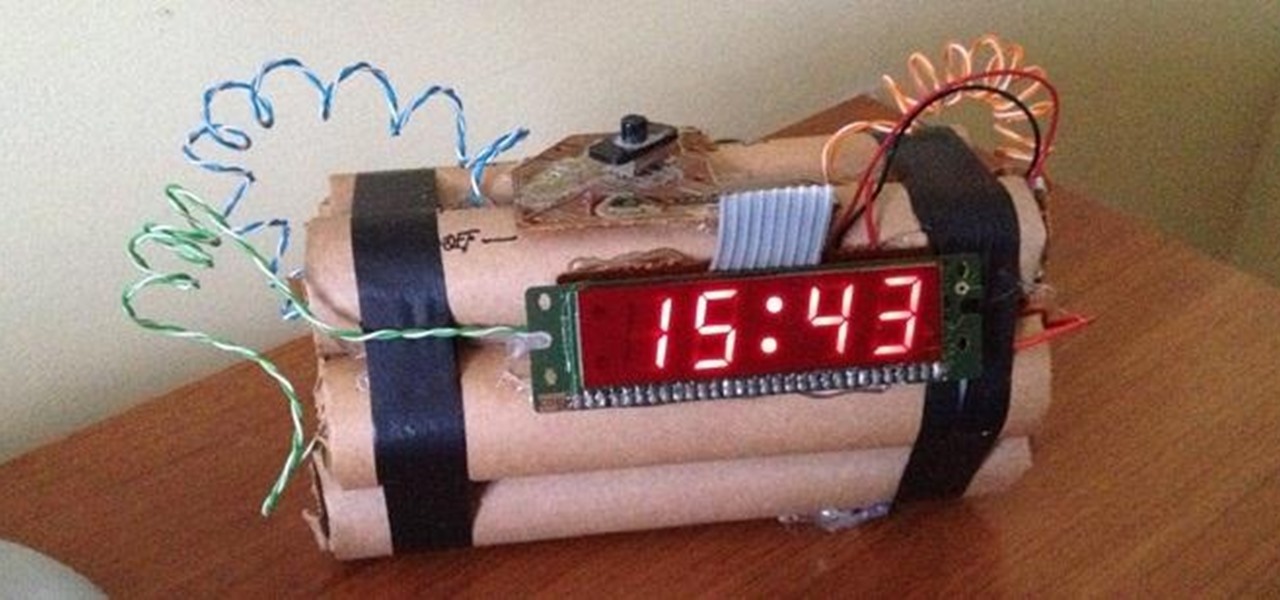
The first alarm clock in recorded history can be traced back to ancient Greek philosopher Plato, known for laying the foundations of Western philosophy and science. Plato was said to possess a very large water clock with an alarm signal similar to that of a water organ.

PGA golf professional Frank Ganley explains how to hit a golf ball with an iron. In golf, a player has a variety of clubs to choose from, but should only have one type of swing. Frank emphasizes that in order to learn how to hit a golf ball with an iron, the player needs to use the same swing that he uses when hitting the ball with a wooden club. The key to a successful hit is in the players ability to adjust for the difference in the lengths of shafts of the clubs. This because a wooden golf...

This video shows how to do a 'kick flip' on a skateboard. The man instructing begins by getting the things he will need, which are a skateboard and a pair of shoes. He demonstrates where to place your feet, with the left foot on the middle of the board and the right foot on the end. The next step is to kick the board up with your right foot and flick your left foot up and off, then quickly jump back on after the board flips. He shows a real life example of a successful 'kick flip', and then g...

This video gives instructions on how to cite sources when giving a speech. When giving a speech, you want to appear persuasive and credible to the audience. In order to do this, you must cite the sources of your speech's content. Prior to giving your speech, research materials relevant to your topic. In the course of giving the speech, mention where you got your data. In this case, the speech is about Emotional Intelligence in the Workplace. While making your first main point, mention that "a...

Accidents will happen. This brief how-to will guide you through the process of disassembling your HP iPAQ hx2100, hx2190, hx2400 or hx2700 series pocket PC quickly and efficiently without damaging any of the components, the first necessary step of any successful repair. This tutorial will also be of use to those who wish to learn more about the guts of their iPAQ PDAs without actually disassembling their units.

Accidents will happen. This brief how-to will guide you through the process of disassembling your HP iPAQ rw6815, rw6818, rw6828 series pocket PC quickly and efficiently without damaging any of the components, the first necessary step of any successful repair. This tutorial will also be of use to those who wish to learn more about the guts of their iPAQs without actually disassembling their units.

Accidents will happen. This brief how-to will guide you through the process of disassembling your HP iPAQ hx2000, hx2100, hx2110,hx2115, hx2141s, hx2190 (hx2190a, hx2190b), hx2400, hx2410, hx2490 (hx2490b, hx2490c), hx2495b, hx2700, hx2750, hx2755, hx2790 (hx2790b, hx2790c) or hx2795b series pocket PC quickly and efficiently without damaging any of the components, the first necessary step of any successful repair. This tutorial will also be of use to those who wish to learn more about the gut...

Accidents will happen. This brief how-to will guide you through the process of disassembling your Hewlett Packard iPAQ h3870, h3875, h3835, h3860 or h3830 series pocket PC quickly and efficiently without damaging any of the components, the first necessary step of any successful repair. This tutorial will also be of use to those who wish to learn more about the guts of their iPAQs without actually disassembling their units.

Accidents will happen. This brief how-to will guide you through the process of disassembling your HP iPAQ h2210 or h2215 series pocket PC quickly and efficiently without damaging any of the components, the first necessary step of any successful repair. This tutorial will also be of use to those who wish to learn more about the guts of their iPAQs without actually disassembling their units.

In this video series for puppeteers, learn how to start your own puppet company home business, with tips on where to get puppets, what equipment you need and how to train puppeteers to put on a successful puppet show. Also learn how to market your company to schools and corporations, and how incorporate yourself.

Not only has Google released a completely new Google Pay app for US users on both iPhone and Android, but the've also minted a new mobile banking service. Called Plex, it provides online bank accounts at one of 11 partner banks and credit unions, with no minimum balance requirements, overdraft charges, or monthly fees.

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.