
How To: Boot Windows XP from a CD
The following are the steps to be followed to boot Windows XP from a CD: 1. The first thing to do is switch on your computer. Before your computer starts loading windows, you need to hit the F12 key.


The following are the steps to be followed to boot Windows XP from a CD: 1. The first thing to do is switch on your computer. Before your computer starts loading windows, you need to hit the F12 key.

Have you ever wondered how to open a .ISO file without the need for the disk? Well with Daemon Tools, and this tutorial, you can learn just that. What you will end up doing is creating a virtual drive on your computer, and mounting the .ISO image onto that virtual drive. It's as simple as loading up the program, right clicking on the icon in your task bar tray, clicking on the empty drive, and mounting any .ISO image you like! In no time you'll be playing your favorite game, or program withou...

This video is a report by Terry from Good housing keeping. She reports that women of any age should be thinking of bone health and one of the best ways to strengthen your bones experts say is to follow low fat Mediterranean diet.

How to Install Installous on any iPhone or iPod Touch? Learn about it in this video tutorial in the Electronics category. For this purpose you will need a jailbroken iPod Touch or iPhone. First go to Cydia and open it. It takes a little time to load. Go to manage -> source -> edit -> add. Then type in this source: Cydia.touch-mania.com. Download and install it. Now you go to search and type in Installous in the search box. Download it and go back to your springboard. Open it up, search for an...

First make sure that you have a boot able disc and insert it to your optical drive. Shut down your PC And start it up again making sure to press the special key to enter the setup dialog. Go to the boot sequence and select the CD ROM as the first bot device as shown. Save the settings and exit the setup console. Wait for the PC to boot up and during the loading hit any key to boot from the CD.

The video shows users how to change the boot sequence in a computer with an older AMI (American Megatrends, Inc.) BIOS to boot from the CD/DVD drive. This is required, for instance, if you need to reinstall an operating system, or fix a corrupted windows installation by running Windows Setup from the installation CD. Users should first enter the BIOS setup by pressing the delete key when prompted shortly after powering the computer on. Once the Bios Setup screen has loaded, users may navigate...

This video shows you how to easily access blocked website like MySpace or YouTube at school. The first thing you have to do is open the web browser and surf to Unfilter Me . Then, type your desired web site URL in the "Enter Address" field. Hit the "Start Browsing" button and wait for the site to load. Note that the URL in the address bar is different. This is the easiest way to access blocked websites at school. That's it! Good Luck!

The tarbuck knot is a non-jamming knot, great for when the rope will be bearing a heavy load, and shocked with sudden weight. Form the loop around the winch then make a serises of turns around the standing part in a clockwise direction. Bring the running end down to the base of the runs and make another clockwise turn finishing off with a figure eight through the exiting strand from the top turn. Watch this video knot-tying tutorial and learn how to tie a tarbuck knot.

ACMG Ski Guide Cliff Umpleby discusses how to build a T-Slot anchor using ice axe and skis. Once you have your anchor, learn how to use it to rescue someone from a crevasse. Part two demonstrates transferring the load onto the anchor and escaping the system. Part three demonstrates checking the victim and droppping a loop for a 2:1 pulley system. Part 4 demonstrates creating a Z Pulley for 6:1 advantage.

Post-exploitation information gathering can be a long and drawn-out process, but it is an essential step when trying to pivot or establish advanced persistence. Every hacker should know how to enumerate a target manually, but sometimes it is worth it to automate the process. Metasploit contains post modules that can quickly gather valuable information about a target, saving both time and effort.

Koji is a culture made up of a certain fungus (mold) called Aspergillus oryzae, which has been used to ferment rice and soybeans in Japanese, Chinese, and Korean kitchens for centuries. Koji can actually have other involved fungi, but Aspergillus oryzae is the most common, and therefore the names can be used interchangeably. Its end purpose is to enhance the flavor of items like soy sauce, sake, and miso.

You probably don't give much thought to buying yogurt in the store. You have your favorite brand, or maybe you like trying new varieties each week; either way, you just grab it and go.

Cool, refreshing fruit, ice-cold margaritas (or beergaritas), and popsicles... this combination of food and drink just screams summer. Turn up the chill jams on the stereo, fire up the grill, and throw on your shades—you're just one pool away from the best summer party ever.
To be twentysomething is an awkward time for entertaining. As we graduate college and begin to work in “the real world,” there is a yearning to transition from keg parties into dinner soirées. However, though the desire is there, often the bank account is not. Here are some ways to do in the kitchen what twentysomethings do best: fake it until you make it. (In other words, host a fabulous dinner party for four and still be able to make rent this month!)

When you think of bivalves, such as manila clams and oysters, you tend to think of the meat as being nicely tucked in the shell. Anything else would be scary, right?

In my family, if a food could be made instead of bought, it was made. It wasn't until I went to college and started eating dorm food that I tasted the store-bought versions of many kitchen staples. I quickly learned that there is an enormous quality difference between homemade dressing and the kind that comes in a bottle at the supermarket.

Those ordinary green zucchini you see in the market are hiding a lovely, delicious secret: Actually, all summer squashes produce these delightful blooms, but the zucchini's are most frequently used for eating since they taste the best: fresh, clean, and zucchini-like, but with a little something extra. They used to be a rarity at supermarkets, so you had to have a garden or a gardener friend who would generously share the bounty with you.

Our workdays are typically filled with one thought: get as much completed as possible. Whether you face an inbox filled with tasks or just a project or two, both our bosses and our inner workhorses encourage us to knock out as many tasks as we can each day. But is being super-productive the best course of action for our minds and our employers?

Beef aficionados love a medium-rare burger, but many people are wary of meat that's on the pink or red side since it might contain bacteria. Is it possible to enjoy a burger that's perfectly juicy and yet also cooked thoroughly enough to destroy all traces of salmonella, E. coli, and other microbes that cause foodborne illness? Absolutely! You just need to know a trick (or three).

There is very little in this world that tastes as good as a glass of fresh-pressed juice. The flavors in fruit and vegetables are more clean and immediate on your palate, while the chlorophyll and nutrients seem to zip right into your bloodstream. A really great glass of fresh juice makes you feel more alive and the pasteurized versions on supermarket shelves just can't compare. However, as much as I love a glass of fresh juice, if I had to do it all over again, I wouldn't buy a juicer. The o...
Your smartphone has a ton of ringtone options built in, but ringtones haven't really changed much in the past decade, and it's definitely not cool to hear someone in the supermarket with the same lame ringer. While replacing the stock sounds with a song of your choosing is the best way to keep your phone personalized, why not go a step further using a video?
In this video you will learn how to make a gel like liner using Rallye Balm and Eyeshadow. Just swipe some Rallye Balm on the back of your hand, mix some eyeshadow into the Rallye Balm with a liner brush and then line your eyes. It's super simple to do, longer lasting and moisturizing at the same time!

The following video is the result of months of viewer requests to create a single-shot airsoft rifle. The design I decided to film the video around ended up being quite durable, and very capable of being loaded with single pellets, or multiple pellets to operate as a shotgun.

RonyaSoft Poster Designer software includes lots of different ready-to-use templates. You can freely change anything you want in the template or you can just print it as it is, if you don’t want to puzzle over it. Moreover, you can create your own poster from scratch.

Okay, it's not actually cake-powered, but it does use cake! Owing to the fact that cake and trapdoors are less than half a block tall, we can use fenceposts (which are a block and a half tall) attached to pistons to push people along, because the tops of the fenceposts will invisibly pop up through cake and trapdoors.
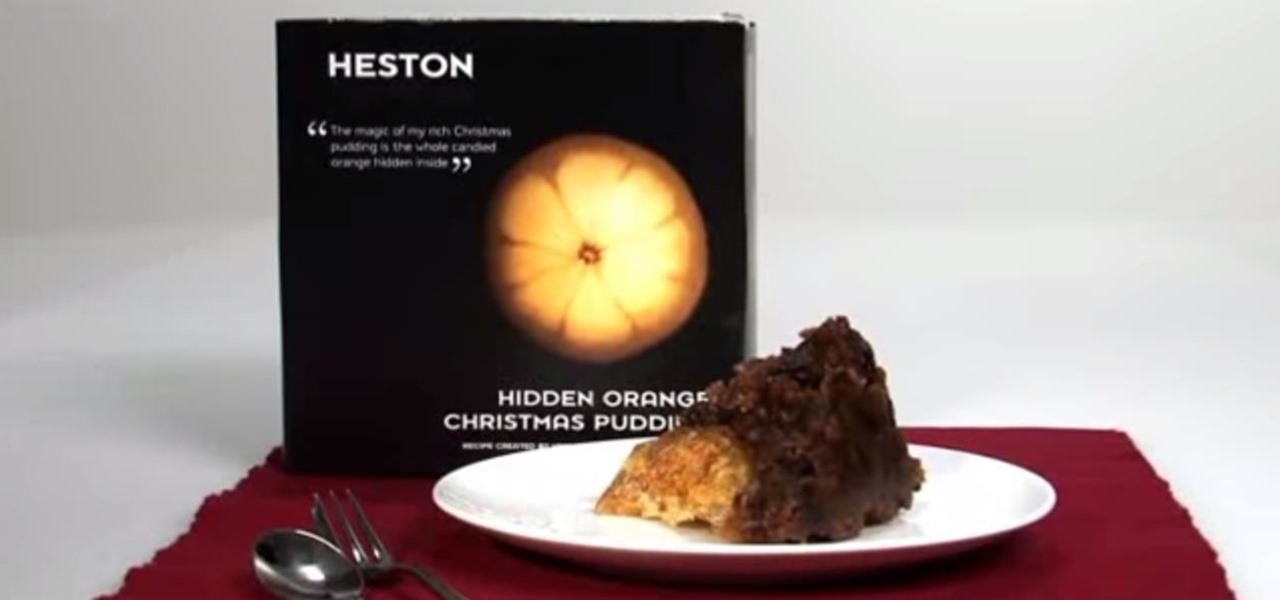
No, not Charlton Heston. The only pudding he ever made was steak and kidney. I'm talking about Heston Blumenthal, world famous chef and pudding lover, and the man behind the "Heston"— a plum pudding with an orange hidden within, brought to you by Waitrose (see video below).

At one point in time, Tesla coils were actually used for things like wireless telegraphy and electrotherapy, but as technology advanced, they shifted to a slightly more enjoyable purpose—entertainment. What's even more entertaining than using a Tesla coil? Building your own. One of the best portable Tesla coils out there is this mini acrylic version by Daniel Eindhoven, aka TeslaCommander. It's made almost entirely of acrylic plastic, minus the steel sphere, and copper wire and tubing. When t...

Apparently it is possible to reduce 64,000 possible Master Lock padlock combinations down to just 100. The entire process is clearly illustrated in the below how-to from Mark Edward Campos. For an enlarged version, click here. Looking for something a little more interactive? We have loads of lock-picking tutorial videos. Here's one that demonstrates the same method (math as opposed to shim) outlined in the above illustration.

Commercial hair conditioners aren’t just expensive, they’re loaded with chemicals. Why don’t you whip up something more natural at home?

Purchase the necessary equipment for this project. Pumice stones can be purchased at any beauty supply store. Chlorine can be purchased from any household supply store. Sodium bisulfite can usually be found at hobby stores. Obtaining the industrial washing machines for personal use is the hardest step. Call local cleaners to see if they will allow you to use their machines. Soak the pumice stones in chlorine overnight. This will allow them to soak up the bleach and create a good absorbency fo...
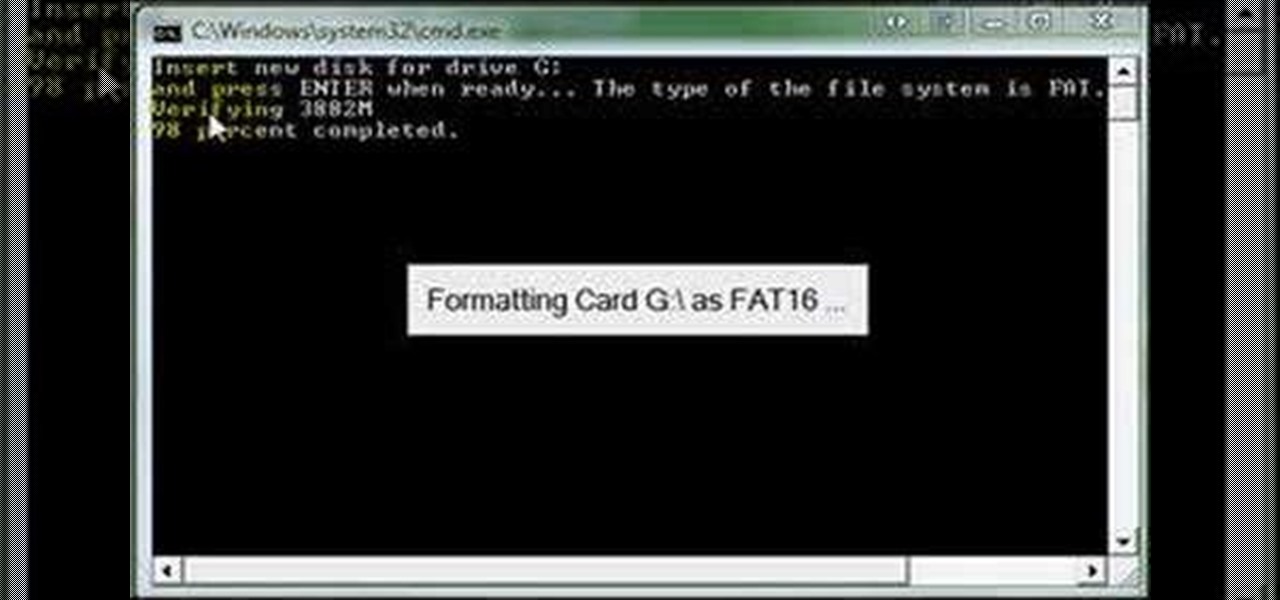
This step-by-step video tutorial shows you how to install CHDK onto your Canon digital camera. CHDK is a firmware enhancement that operates on a number of Canon cameras. CHDK gets loaded into your camera's memory upon bootup (either manually or automatically). It provides additional functionality beyond that currently provided by the native camera firmware.

After the lackluster update that was iOS 13.3.1, we beta testers were in need of some excitement. Thankfully, Apple delivered the goods with iOS 13.4 developer beta 1, introducing fun new features like fresh Memoji stickers and a new Mail toolbar. Of course, that update was for developers only, so we public testers are thrilled that Apple just released the first public beta today.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.
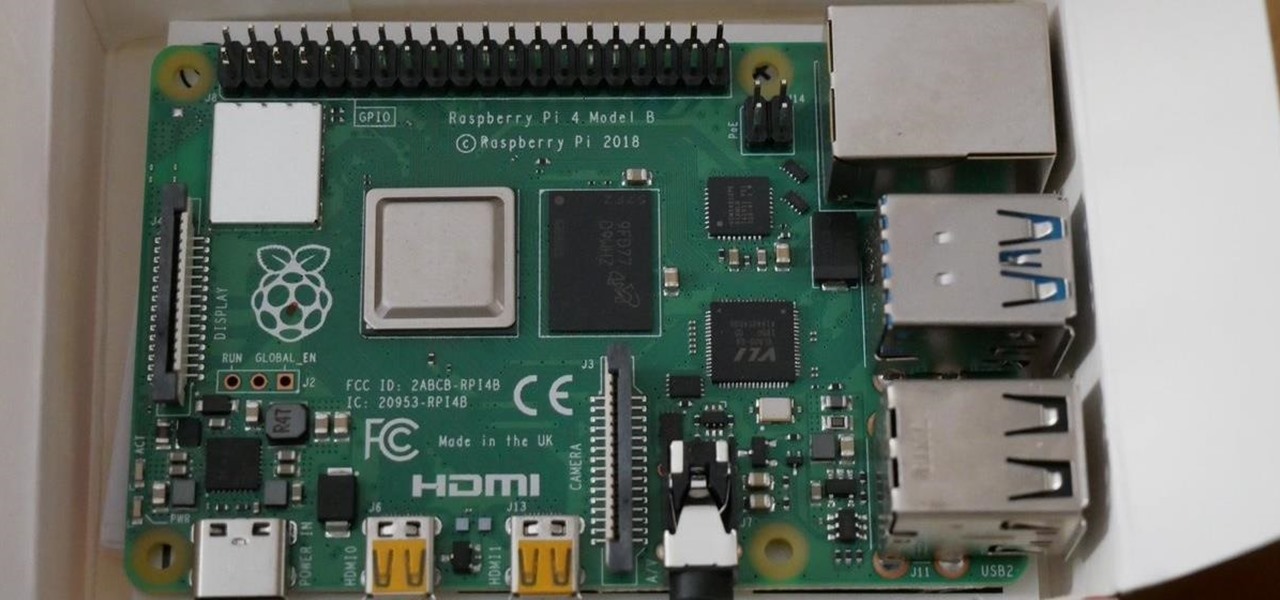
In 2019, the Raspberry Pi 4 was released with specs including either 1 GB, 2 GB, or 4 GB of memory, a Broadcom BCM2711B0 quad-core A72 SoC, a USB Type-C power supply, and dual Micro-HDMI outputs. Performance and hardware changes aside, the Pi 4 Model B runs Kali Linux just as well, if not better, than its predecessors. It also includes support for Wi-Fi hacking on its internal wireless card.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

If you ever want to root your OnePlus 6, install TWRP, get Magisk and Xposed, or flash a custom ROM, the first thing you'll need to do is unlock your bootloader.

Whether due to spotty cellular reception or just data that you want to save, popular navigation apps like Google Maps and Waze offer an offline feature that lets you navigate from one location to another in the absence of internet service. Apple Maps also lets you use its service offline on your iPhone, though the feature is not as straightforward as it is on its competitors.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.
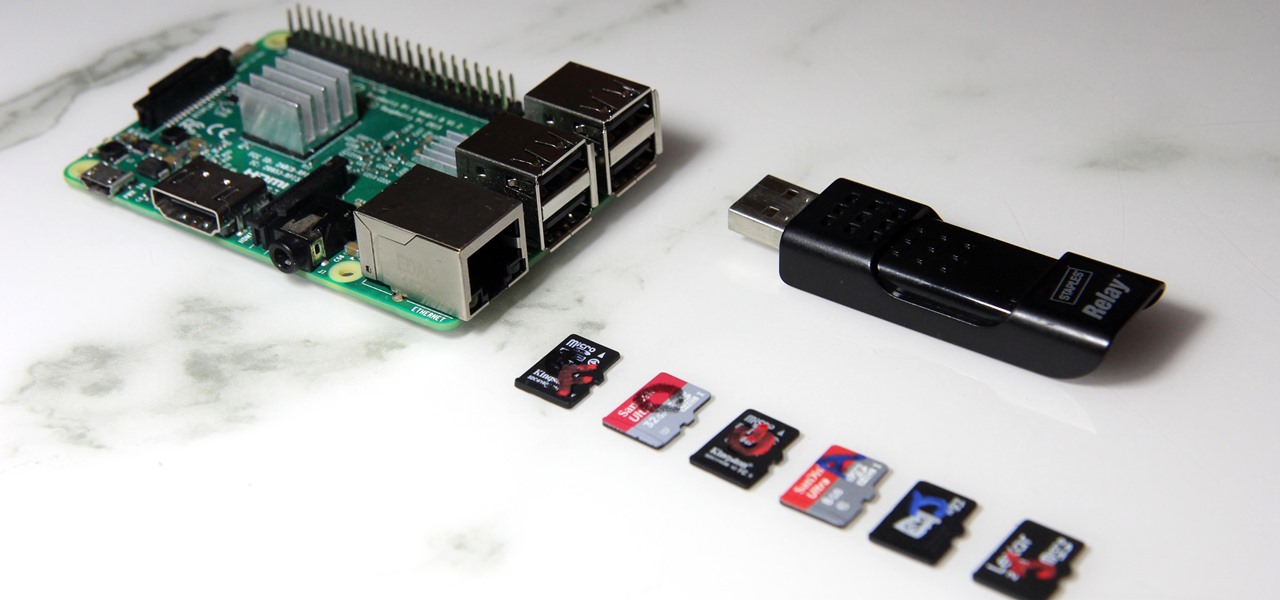
The Raspberry Pi loads an operating system from whatever SD card you insert, allowing you to keep different operating systems on separate SD cards depending on which OS you wish to run. A tool called BerryBoot cuts down on the number of SD cards needed by providing the ability to boot multiple operating systems from a single SD card, similar to Boot Camp for Mac computers.

Microsoft's HoloLens comes with helpful features for capturing video and photos, but sharing whatever you record isn't as straightforward as you might expect. So here are the many ways to get your media off the device to share with the world.