Welcome back, my fledgling hackers! The database is the hacker's "pot-of-gold," as it contains information that is very valuable to both the business and the hacker. In this, the second of my series on hacking databases, we're on the "hunt" for Microsoft's SQL Server. Although far from the most commonly used database (Oracle hold's that title), Microsoft's SQL Server is very often found in small-to-medium sized businesses. Even a few big businesses use it.

If I were a math major, I'd probably be rolling in dough somewhere in Silicon Valley right now, but since multiplying numbers and figuring out tangents gives me panic attacks, I went the English route... pays much better.

The NSA's massive internet spying efforts will continue. In President Obama's latest press conference, he went public to (in so many words) say that the NSA's spying efforts will continue uninterrupted. This, coming just weeks after the Amash Amendment which would have defunded the program, was narrowly defeated in the House (you can check if your congressmen voted against it here).

Whether or not you believe that the government is snooping around in our private emails, texts, and phone calls, it wouldn't hurt to protect ourselves a little better in the digital realm.
Arcades, Nintendo, Sega, and 16-bit graphics ushered in a new level of gaming that was leaps and bounds ahead of the early Pong days. I remember loading quarters into the machines and playing 2D fighting games until all my money ran out. When I wasn’t in school, you could usually find me at the arcade playing Street Fighter, The King of Fighters and Marvel vs. Capcom. At home, I had my Super Nintendo and Super Mario World keeping me glued to the television until the next boss stage.
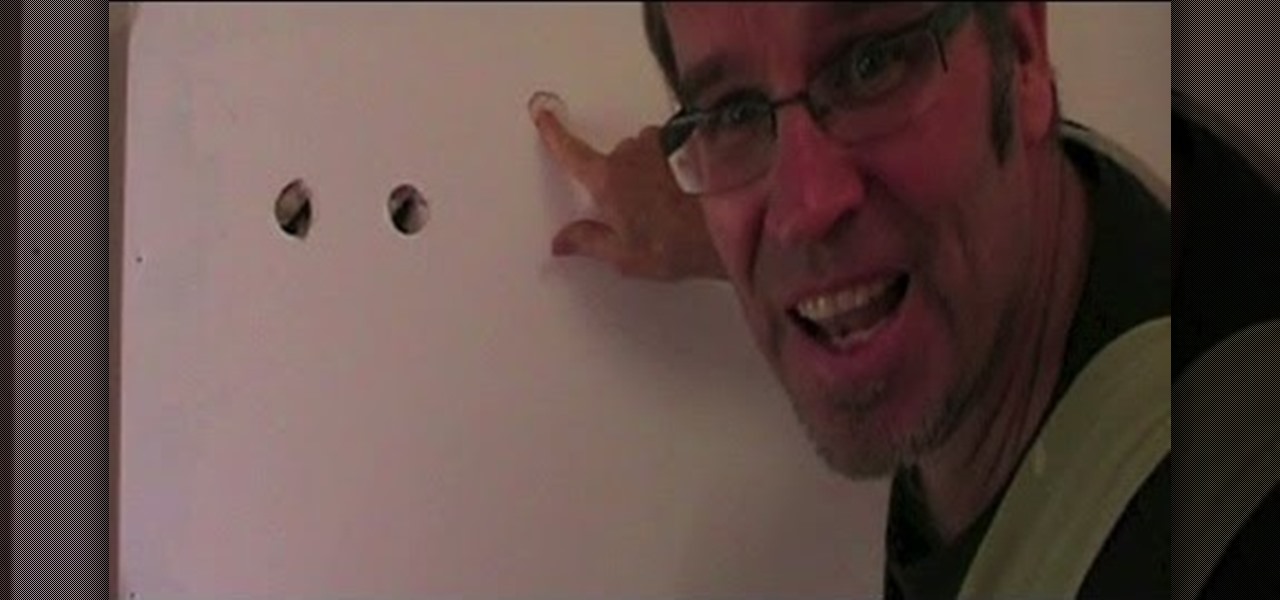
How to find a stud in the wall. How would you like to be able to find a stud in a plaster wall / drywall wall, easily and every time without an expensive stud finder? Let's look at how to find a wall stud using three conventional methods then l'll explain my foolproof method of how to find a stud in the wall without a stud finder.

The advantages of rooting have been covered before, and with rooting comes flashing ROMs and mods to your device. The easiest method for flashing anything is to do it through recovery.

PRL, or Preferred Roaming List, basically tells your phone which towers to connect to first. Changing PRLs can improve reception and data speeds, and in some cases even give you access to corporate/test towers.

The beauty of free apps is that, well, they're free. But as we all know, there is no such thing as a free lunch. Sometimes these "free" applications are only feature-limited mini versions, or they're so littered with ads that opting to pay for it is the only way to actually enjoy it.

This is a lengthy, detailed series on iPhone development, for which you'll need an Intel-based Mac computer, running Mac OS X 10.5 (Leopard) or higher. Then, before you actually get started developing for the iPhone, you'll need to register as a developer with Apple. Then, you'll need to download Xcode and the iPhone SDK. Once you have all this, you can start developing iPhone applications!

In this video tutorial, viewers learn how to completely format a hard drive. Begin by downloading the Knoppix Live Boot CD. Then burn the newly download ISO onto a CD as a bootable disc. Use your BIOS to tell your computer to boot from the CD-ROM instead of the hard drive. With the Knoppix CD still in your CD drive, restart your computer to load up Knoppix. Once loaded, use Knoppix to run the “dd” command and reformat your hard drive. This video will benefit those viewers who want to learn ho...

This video will show you how to use a ramp to load a snowmobile in a truck properly. Using this kind of ramp, you can take advantage of leverage to load your snowmobile into the back of your pickup.

Whether you're in an airport, restaurant or waiting room, the insidious grip of televisions on human life is omnipresent. Sometimes it's nice to talk to other human beings while looking at them directly—actually hearing what they have to say.

Don't be too disappointed if you don't have the spiffy new Kindle Touch, there is an up side. The benefit to owning the older (duller) models is that the firmware remains the same throughought generations, so the hacks retain their usefulness. This has given the modding community for Kindle a bunch of time to flourish, with tons of great code, hacks and homebrew. Today's Null Byte is going to show you how you can root, and then remove the crappy original screensavers that come installed on th...

Weapon grouping has become available in the Quantum Rise expansion for EVE Online. This allows you to load ammunition for up to three separate weapons at a time - useful in a dogfight! This tutorial shows you how to group your weapons to take advantage of this new feature.

Hack the hex code in Bejeweled Blitz for a higher score! Everyone wants the top score in this popular web game, but it all comes down to how you get it. Do you have what it takes to come out on top? Check out this video tutorial to learn how to hack Bejeweled Blitz (07/24/10).

In this tutorial, we learn how to jailbreak an iPhone 3g and keep the data. First, plug your phone in and connect it to your computer. Next, go to the website felixbruns iPod firmware. Go to the bottom of the page and find where it says "iPhone 3g 3.0" then download and install this to your computer. Next, go and download this zip file, and download and install this on your computer. Next, turn off your phone, then wait for it to restart. Now, hold the power button off and click on the RedSno...

To hack into Google images follow the following steps. You will first need to open a new internet browser window and go to Google, then load their images website. Next type into the search bar your image query and press search. Once you have gotten your search results paste the following code into your address bar:

Need to know what kind of oil your car needs? How about your vehicle load capacity? What about the standard maintenance procedures for you specific make and model? All of this and more can be located inside your owner's manual. If you don’t have an owner’s manual for your used car, you may still be able to find one even if your car is an antique.

Unlock and jailbreak your iPhone! You can either reinstall the entire operating system, wiping all the data from your phone, or you can wait for Black Snow to come out. In the method shown in the video, you can unlock right away. To restore, hold option (on a Mac) or shift (on a PC) and click restore. After it is done restoring, you should be getting an error message that the phone isn't registered and to insert a SIM card. Insert the SIM card you want to use. Close iTunes and open up www.bla...

This video explains how to send the Text message to any where specifically to mobile using Yahoo mail. To do that first type the "www.yahoo.com" or "www.yahoomail.com" in the browser. And then choose the Mail option from the front page of the yahoo website. From that click the sign in option, and give your Mail id and password in the yahoo sign in page now you will logged into your yahoo account. Into your account you will have the "New" menu option on left to corner. From that you have to ch...

Glass shelves add a elegant beauty to your home, but imagine how much more elegant and sleek they would look if they were simply floating against the wall. Floating glass shelves are the innovative way to create stylish wall arrangements.

This is part 1 of 2 on how to complete the Takedown mission and get the Tag Em And Bag Em achievement. The Tag Em And Bag Em achievement is earned by completing the Takedown mission, so check out this video if you want to see how to complete this level.

Hacking RC is easy with Piaps Restaurant City Hack! Restaurant City is a Facebook game that allows you to create your own restaurant. Watch this video tutorial to learn how to cheat Restaurant City with Piaip's Hack (11/08/09). See how to download, install and run Piap's Restaurant City Hack v.1.13 or 1.12.

The Department of Biological Sciences at the University of Alberta brings you this video tutorial specifically relevant to your student laboratory courses, specifically microbiology. If you're a student at any school of biology, this information will be helpful for learning how to perform agarose gel electrophoresis in the lab.

The Department of Biological Sciences at the University of Alberta brings you this video tutorial specifically relevant to your student laboratory courses, specifically microbiology. If you're a student at any school of biology, this information will be helpful for learning how to use pipetting techniques in the lab.

The tools required for this project are: an electric hand drill, a drill bit of the appropriate size and goggles to protect the eyes from falling debris. You will also need a ceiling hook kit, available in most major home stores. In the kit, there is a hook; a spring-loaded anchor; a threaded shank or screw, which is threaded on both ends; and another threaded shank or screw, which is threaded on one side and has screw thread on the other side for wood installation. To install in a sheetrock ...

If you're a PC gamer, you know the value of performance metrics. These graphs and charts overlaid on top of a game give you real-time information about how well your system performs. And for the first time, Galaxy users running One UI 3.0 will get access to similar information for mobile games.

The Pi-hole project is a popular DNS-level ad blocker, but it can be much more than that. Its DNS-level filtering can also be used as a firewall of sorts to prevent malicious websites from resolving, as well as to keep privacy-killing trackers such as Google Analytics from ever loading in the browser. Let's take a look at setting a Pi-hole up and customizing a blacklist to suit your needs.

SEO is the name of the game. If you want your business or brand to succeed, ranking on the front page of Google is a boon. Getting to the front page of search engines takes work, but it's not impossible when you master SEO best practices.

Your phone is loaded with contacts you've collected over the years. They're an asset, and you should use your library of connections outside the confines of your mobile device. Luckily, your Pixel uses a standardized medium to store contacts that can be used by the likes of LinkedIn, Outlook, Hubspot, iCloud, and more.

It's now standard for websites to have a mobile version. Conveniently, we can browse the web with a mostly mobile-optimized experience. But what if you want the desktop experience on mobile? If you want, you can browse the mobile web and see only the desktop version of websites on Android devices.

While Snapchat augmented reality often embraces pop stars like Drake and Ariana Grande, a couple of bands from the louder side of the music industry have found a home with Facebook.

Newer smartphones usually come with a decent amount of storage, even at the lowest tier, but that doesn't stop items from filling up all that space. Watching movies offline, shooting 4K videos, and other processes can fill up your phone fast, and so can albums and songs in Apple Music.

It's here! Apple just released the latest version of iOS today, Monday, March 25. Version 12.2 has seen six beta releases, spanning the course of fewer than three months. The new update sports 30+ awesome features, including new Animoji, air quality reports in Apple Maps, and AirPlay 2 support for compatible TVs, in addition to a slew of new UI tweaks and redesigns.

In keeping with its focus on loading the Magic Leap One with content at launch, Magic Leap has inked a creative partnership agreement with augmented reality production studio Square Slice Studios.

While Hulu offers users an easy way to catch up on the latest shows, it hasn't always given them the best tools to control that content. Scrubbing — or fast-forwarding and rewinding — had a history of inaccuracy, as well as a general uselessness. Luckily, Hulu has greatly improved this tool, updating it with new features to help you find your place quickly and accurately.

If you want to follow Null Byte tutorials and try out Kali Linux, the Raspberry Pi is a perfect way to start. In 2018, the Raspberry Pi 3 Model B+ was released featuring a better CPU, Wi-Fi, Bluetooth, and Ethernet built in. Our recommended Kali Pi kit for beginners learning ethical hacking on a budget runs the "Re4son" Kali kernel and includes a compatible wireless network adapter and a USB Rubber Ducky.

Koadic allows hackers to monitor and control exploited Windows systems remotely. The tool facilitates remote access to Windows devices via the Windows Script Host, working with practically every version of Windows. Koadic is capable of sitting entirely in memory to evade detection and is able to cryptographically secure its own web command-and-control communications.

From all the demos we've seen, we know for sure that the marketing world is going to change drastically thanks to Apple's ARKit.