Hello all! In this tutorial, I'd like to show you one way of getting root on OS X. Check out this GitHub page for a recent privilege escalation exploit that was recently discovered. I've tested it and it works on both OS X 10.9 Mavericks and OS X 10.10 Yosemite, but appears to have been patched with OS X 10.11 El Capitan. If you check out the file main.m you can see where most of the magic is happening. This source code can very easily be changed to make it do more than just the system("/bin/...
Did you know Kali 1.0.8? You probably did, and you probably know about the EFI boot option that has been added.

My first encounter with a phablet was late last year with the AT&T version of the Samsung Galaxy Note 2, having never touched or even seen its highly-acclaimed and pioneering predecessor. Initially, I was a bit overwhelmed by the enormous screen and taken aback by the dated stylus, which brought up ugly memories of my dad using his ten pound PalmPilot.

First of all you shall need a program called "Disk Inventory X". You can download this program from the link Once you have downloaded you have to install this program. Now launch "Disk Inventory X". This shall take some time to load because it processes your hard drive and looks at all the files and folders. This program provides you a visual representation of the files that are there in your hard drive. Therefore for every folder that is shown in this application it shows...

For anyone who lives in a space that may frown upon making holes in the walls, or for anyone who may not want to take on such a task, there's a simple alternative to hanging curtains or drapes. And the answer is brilliantly simple.

FireworksTutorial shows you how to restore your recycle bin files that you've already deleted. Go to Google and search "Restoration." Click on the first link that pops up from the list (the one from Snapfiles that's free) and download it. Once it's downloaded, run it and unzip it to somewhere you can easily access. Organize it by creating a new folder and putting the files into the folder. Double-click on the application Restoration with the trash can icon to load up the program (If you're on...

Tired of static cling? You can make your very own dryer balls that will prevent your clothes from having static clean and it only takes some yarn and pantyhose. You can even make scented dryer balls using this method.

Removing the gunk from a gutter but with proper methodically will ensure a clean job and keep you safe while doing activity on top of a ladder. Don’t let this chore get you down, with a little work you’ll have free flowing gutters all season.

In this tutorial video, learn how to get started using the Akai MPC 4000 drum machine. Our expert music producer will give you a tour of the basic interface for the MPC, and then show you how to load, chop, and slice samples, layer a beat, use the sequencer, and create a basic hip-hop beat of your own.

In this video series, learn how to operate one of those tools. Our expert will demonstrate how to use and maintain an electric sander. He'll demonstrate how to load various types of sandpaper, how to empty the bag, and how to properly store the tool.

In this how-to video series, learn how to use a cordless nailer from certified building contractor Matthew Christian. Matthew will demonstrate how to load nails in a cordless nailer, how to unjam a cordless nailer, how to change air cartridges and air filters in a cordless nailer, how to properly handle a cordless nailer, how to change the battery in a cordless nailer, how to charge cordless nailer batteries, how to oil cordless nailers, how to flush a cordless nailer.

Whatever your particular bent on the art of photography may be, learn how to use the darkroom as one of your tools for developing and printing beautiful pictures. Our expert will walk you through the step-by-step process for developing film, including removing the film from the cassette, loading it on a spool, using the proper agitation method, prewetting, and the push-pull process.

In this tutorial video, learn how to get started using the Akai MPC 2000XL drum machine. Our expert music producer, Amir Tauheed, will give you a tour of the basic interface for the MPC, and then show you how to load, chop, and slice samples, layer a beat, use the sequencer, and create a basic hip-hop beat of your own.

In this video series our expert, Fred Norwood, will not only show you the different components of a 35mm camera and how to use it but he will also show you how to load the film and when and how to use certain types of other cameras. Certain cameras are used for certain things in certain places and you will learn when it is best to use a tripod as well as the benefits to disposable cameras.

On Monday, the social media giant Facebook suffered a massive outage that, as of this writing, is still in effect.

Between all the streaming services you have to contend with, it's hard to want to go through the trouble of plugging in an adapter and loading up a DVD when you could find another movie without needing to move.

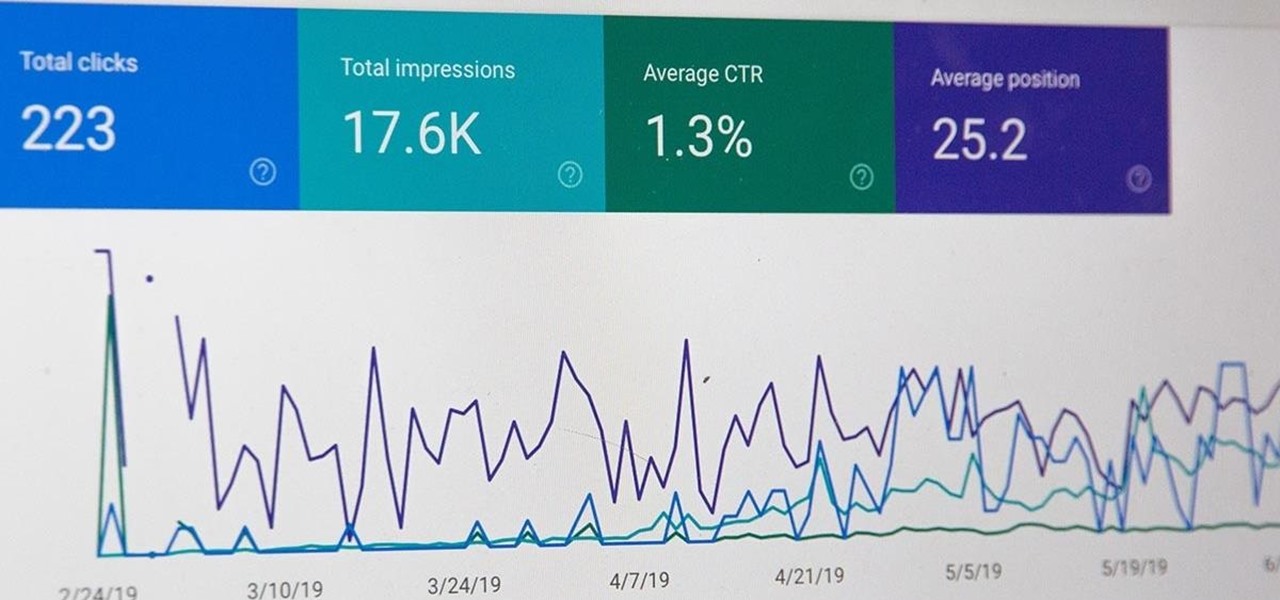
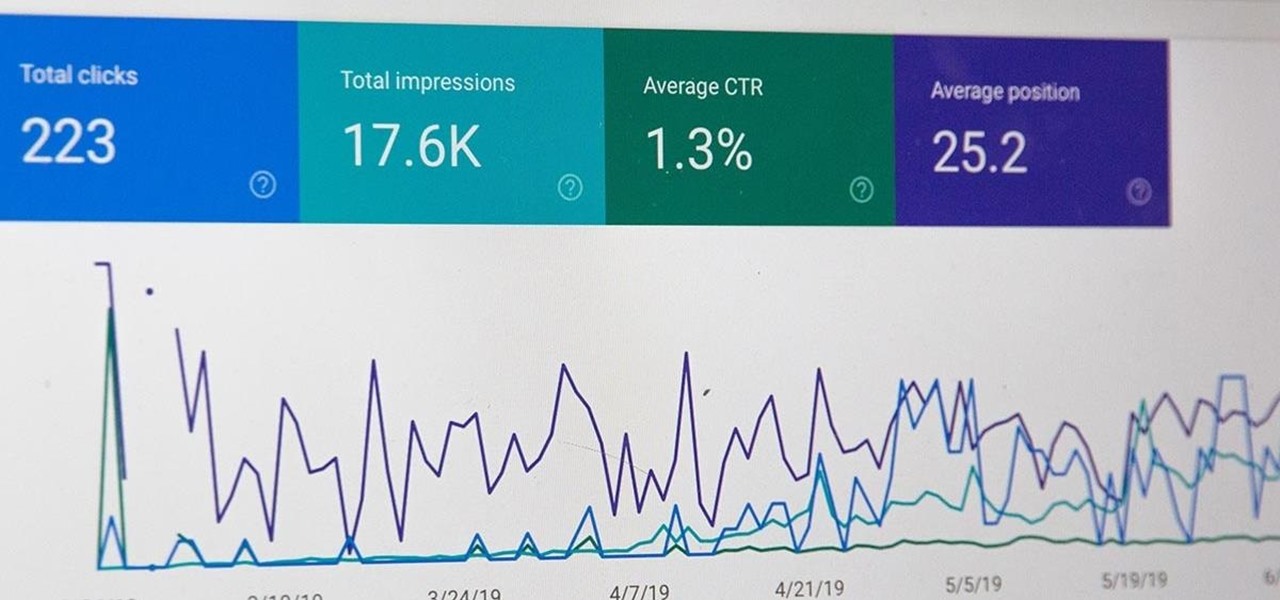
You know just how great your products and services are. Now it's time to let the rest of the world know. Of course, that's easier said than done. You're probably competing with bigger, more established brands that can afford to spend their way to the top. You can make it a fair fight with a little SEO optimization.

All modern entrepreneurs know that your business is as strong as its SEO. Whether you want to Rank #1 on Google to increase your personal branding, traffic to your online storefront, or to add the skills to your resume, you can now get a Complete SEO Training course for just $14.99, in the Gadget Hacks Shop, 92% off the regular cost of $199.

If you're interested in joining the increasingly popular and lucrative world of ethical or "white hat" hacking, you're far from alone. More and more coding and programming pros are turning to this field thanks to the high pay, countless opportunities, and exciting work environment.

Everyone knows that app updates on iOS are found in the App Store. What you might not have known, however, is that you don't need to manually open the App Store app to manage your updates and downloads. In fact, that work can be started or completed directly from the first place you interact with on your iPhone — the home screen.

There are many considerations to make when choosing a web hosting plan. Storage space, performance, security, and reliability all matter. The cheapest option isn't always the best idea.

3D printers allow hackers and makers alike to create something from nothing. They're an incredible technology that lets you build protective cases and covers for gear such as a wardriving phone and Raspberry Pi-Hole. 3D printers can even help you out in a bind when something breaks, and it's impossible to get the part, since you can just print one out yourself.

Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there that cater to particular needs. For auditing web applications and servers, Tishna comes in handy.

Snapchat popularized personalized stickers for social media and messaging with Bitmoji, followed by walled-garden versions from Apple with Memojis and Samsung with AR Emojis. Even Google has gotten into the game, integrating an emoji generator for Gboard.

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

If you haven't used a Samsung device in a few years, the Galaxy S20 series will be your first taste of One UI 2, the skin running on top of Android 10. Although One UI is on the heavier side, it has loads of exciting features that go beyond what's offered in stock Android.

It's OK to want an extended break when you're working or learning from home. Maybe you want to play a video game, spend more time with your family, hang out with your dog, or FaceTime with friends. But how can you do that when you're supposed to be in a Zoom video conference or class? Thanks to one Zoom feature on your iPhone, it may be easier than you think.

There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture handshakes from both attended and unattended Wi-Fi networks, we'll use two of Bettercap's modules to help us search for weak Wi-Fi passwords.

Pyrit is one of the most powerful WPA/WPA2 cracking tools in a hacker's arsenal, with the ability to benchmark a computer's CPU speeds, analyze capture files for crackable handshakes, and even tap into GPU password-cracking power. To demonstrate how quickly it can hack a WPA/WPA2 password, we'll use it to play a Wi-Fi hacking CTF game anyone can practice for less than $10.

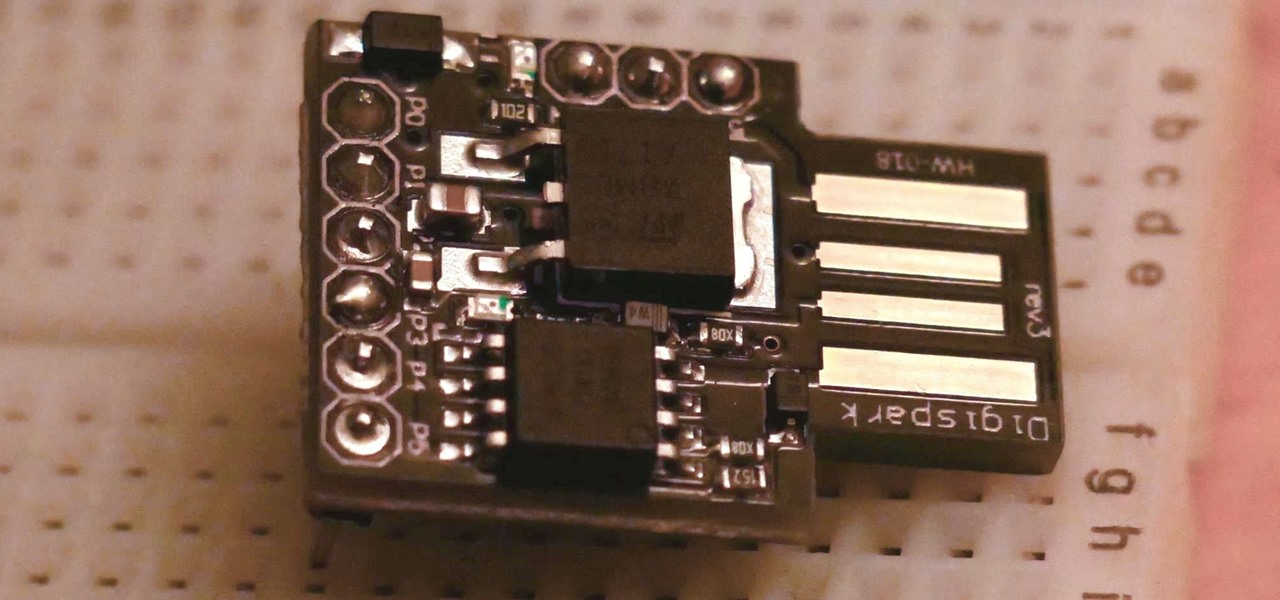
The USB Rubber Ducky is a famous attack tool that looks like a USB flash drive but acts like a keyboard when plugged into any unlocked device. The Ducky Script language used to control it is simple and powerful, and it works with Arduino and can run on boards like the ultra-cheap Digispark board.

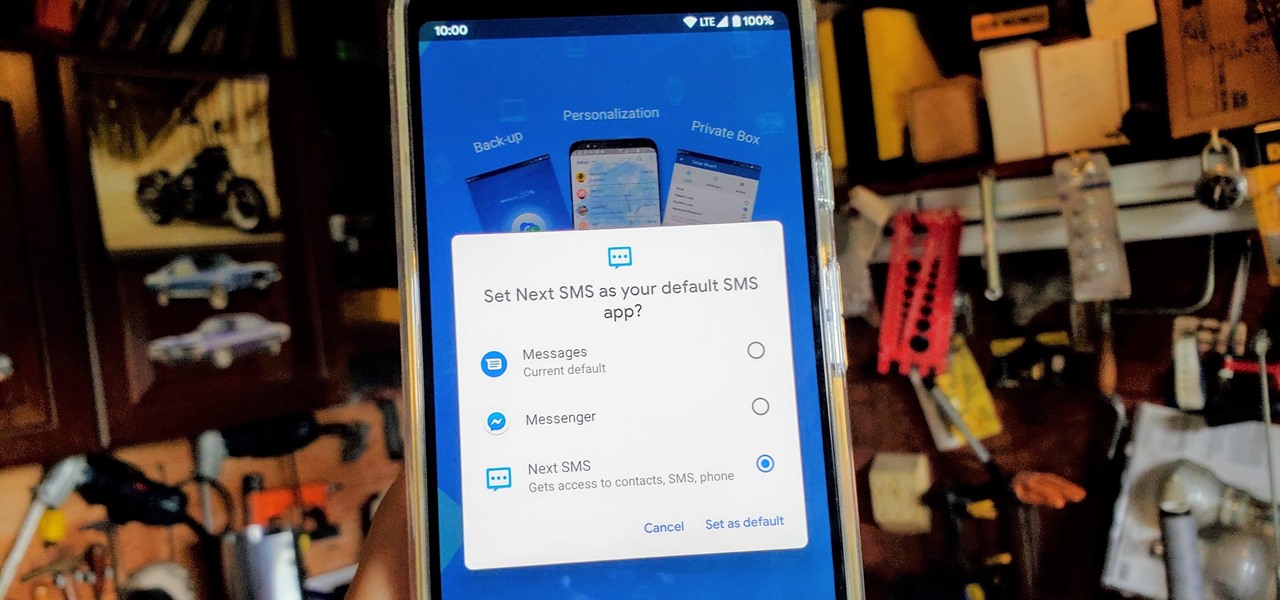
One of the best things about Android is being able to control everything you want, from your wallpaper down to the default apps you use for every action. Changing the default SMS app from the one that came with your device can drastically alter your messaging experience. Many SMS apps have loads of themes to pick from while also offering other features you can't find anywhere else.

If you have friends who aren't privacy-conscious, you've surely heard the old "What do I have to hide?" excuse. Despite the fact that billions of people are using the internet each day, many of them don't know the dangers that can find them. And many don't know the tools to combat them.

Another year, another battle between Samsung and Apple. We recently saw what Samsung is bringing to the table this year with the release of the Galaxy Note 10+, and now it's Apple's turn. For those who want a truly large device, Apple is offering the iPhone 11 Pro Max. Let's see how they match up.

One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.

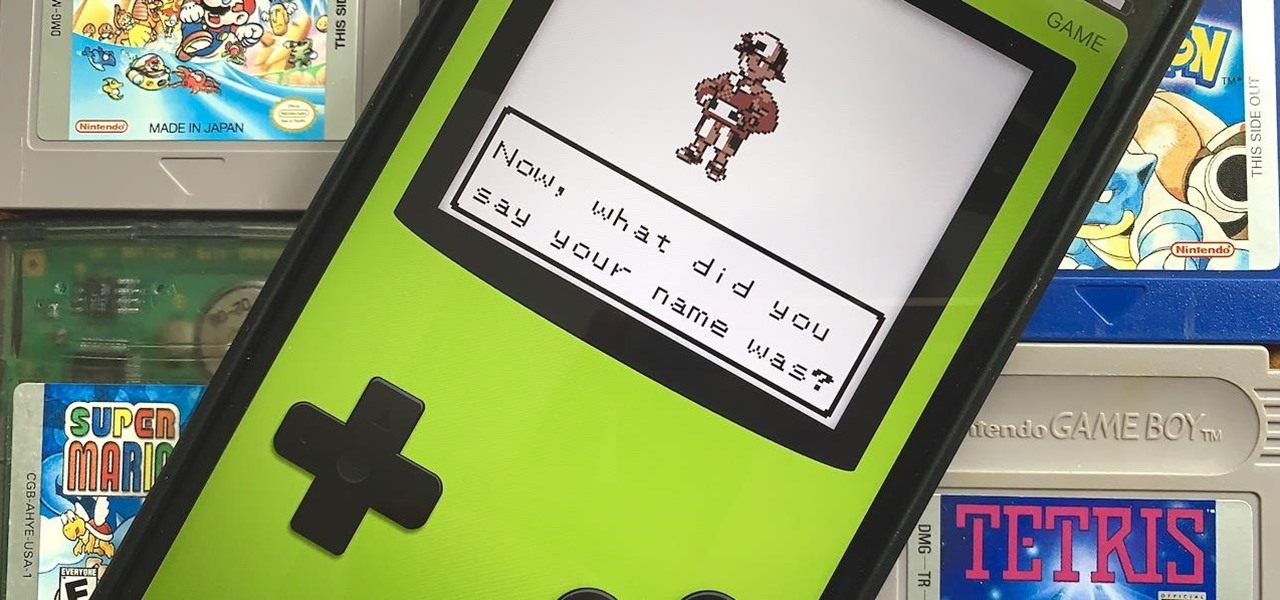
Nintendo may be developing cases that'll turn your iPhone into a gaming device like the Game Boy, but until something materializes there, you're stuck with cheap knockoffs on Amazon or a real Game Boy or Game Boy Color. But there's something else you can do to play eight-bit Nintendo games on your iPhone right now.

There are a lot of songs out there, so it's tough to remember all of the words to every song you like. If you're like me and have a less-than-perfect memory, visual aids will ensure your Apple Music jams aren't interrupted with incorrect or forgotten lyrics. That's why Apple's update with time-synced lyrics is so cool, essentially turning your iPhone into a portable karaoke machine.

The first thing you'll always have to do before getting your customization game on with most phones is to unlock the bootloader. Doing so opens the true potential of the device, allowing you to root, install TWRP, Magisk, custom ROMs, and other mods. No matter your wants or needs, there's no way around it — the bootloader must be unlocked to modify the system.

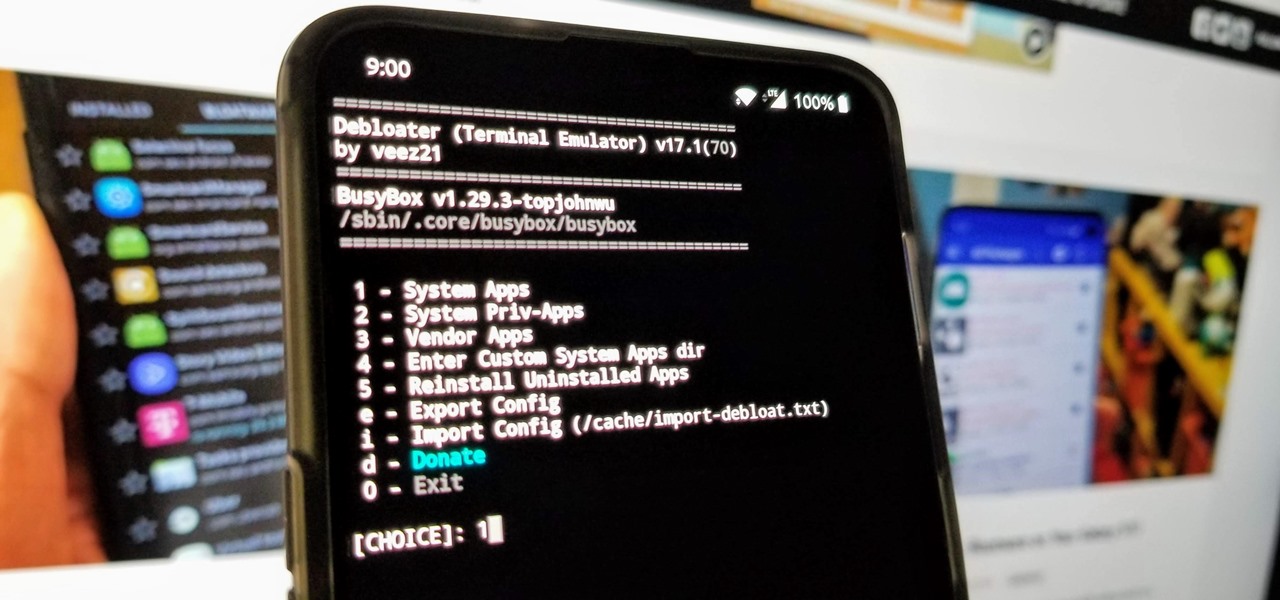
When you get a new phone, the last thing you want to deal with is a ton of preinstalled programs staring back at you. They not only clutter your home screen with apps you'll probably never use, but they're also wasting space on your internal storage and potentially draining battery. To truly uninstall them, you'll need root — but even then, it can be hard to pin down all the apps that should be removed.

With any password manager, the only password you need to remember is the master password that locks the vault from both hackers and the company. This makes the master password very important. But what happens if you forget this password? Well, LastPass has you covered.

In a world of seemingly endless streaming services, podcasts continue to offer free, unlimited entertainment for all. When you find a podcast that's just too good to keep to yourself, sharing it with family and friends is inevitable, but how you share may determine whether or not they listen to it or not. Links alone aren't enough. Audio and video clips are how you get them sucked in.