
News: Unreal Engine 4 Now Available for Microsoft HoloLens 2
A major software tool first promised during the reveal of the HoloLens 2 earlier this year is finally available.


A major software tool first promised during the reveal of the HoloLens 2 earlier this year is finally available.

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

If you're an iOS developer, welcome back to beta testing. Apple just released the first iOS 12.4 developer beta today, Wednesday, May 15, just two days after the public release of iOS 12.3. While Apple has not shared any release notes, we know this latest version of iOS will support Apple Card, Apple's upcoming credit card.

Over the past two years, Apple's Worldwide Developers Conference (WWDC) has become a showcase for new ARKit capabilities. This year, it could offer more information related to Apple's long rumored augmented reality wearable.

Auditing websites and discovering vulnerabilities can be a challenge. With RapidScan and UserLAnd combined, anyone with an unrooted Android phone can start hacking websites with a few simple commands.

When we reviewed the best file managers on Android, MiXplorer easily topped our list with its abundance of features, including tabbed browsing, support for up to 19 different cloud services, file and folder encryption, and much more. The only major complaint we had was the fact it couldn't be installed from the Play Store, but now, that is no longer the case.

While Unity is already the leading 3D engine for augmented reality content in terms of volume, the announcement of Project MARS, a new augmented reality authoring tool, at Unite Berlin in June promised to expand AR development to a whole new audience of designers and other non-coders this fall.

This year's holiday shopping season is shaping up to be fertile ground for augmented reality to show its worth, as both Walmart and Target have crafted immersive experiences designed to engage shoppers in the coming weeks.

It's always a good idea to know how an attack works at the very basic level. Manual techniques for exploitation often find holes that even the most sophisticated tool cannot. Sometimes, though, using one of these tools can make things so much easier, especially if one has a solid foundation of how it works. One such tool can help us perform a cross-site request forgery with minimal difficulty.

MacOS isn't known as an ideal operating system for hacking without customization, but it includes native tools that allow easy control of the Wi-Fi radio for packet sniffing. Changing channels, scanning for access points, and even capturing packets all can be done from the command line. We'll use aliasing to set some simple commands for easy native packet capture on a macOS system.

Net neutrality is dead and your internet service providers can collect all the data they want. While VPNs are a great way to protect some of that privacy, they're not perfect. There is another option, though, called Noisy, which was created by Itay Hury. It floods your ISP with so much random HTTP/DNS noise that your data is useless to anyone even if they do get it.

Google's Pixel smartphone had a decent head start as one of the first devices to offer ARCore, but that early exclusivity has been frustrating for some Android device owners. Some of that frustration was relieved when Google added more Android devices to the ARCore list in February.

A very low-key update to the ARCore developer's site has expanded the universe of officially-supported devices for Google's augmented reality toolkit to include the Samsung Galaxy S7, S8+, and Note 8 handsets.

When it comes to media players, few are more capable than VLC. With its extensive codec support, VLC is able to play almost any video file. Partly due to its open-source nature, features are constantly added. This trend has continued with a new update that added native Chromecast support.

In 2017, after purchasing a majority of the 600 MHz frequency, T-Mobile began a massive rollout of the new LTE Bands across the US. However, there are currently only two devices that support the frequency, also known as LTE Band 71. Thanks to a recent FCC listing, we've learned this number will double when the Galaxy S9 and S9+ debut next month.

Rooting has a long and storied history in the Android community. As OEMs push out more refined software, the need to root has diminished — still, the number of incredible things you can do with a rooted phone is enough to tempt many enthusiasts. Luckily, some manufacturers are still putting out root-friendly devices.

In a highly exciting but ultimately disappointing turn of events, Google released the ARCore Preview 2 today. While the new preview does bring with it new versions of the application programming interface (API) for the C language, pause and resume functionality, as well as increased accuracy, one thing it seems to be missing is a bigger compatibility list.

If you own a Porsche, there's a good chance you're interested in two things: speed and quality. Porsche Cars North America wants to extend that experience from the driver's seat to the service center.

Networking is built largely on trust. Most devices do not verify that another device is what it identifies itself to be, so long as it functions as expected. In the case of a man-in-the-middle attack, we can abuse this trust by impersonating a wireless access point, allowing us to intercept and modify network data. This can be dangerous for private data, but also be fun for pranking your friends.

If you're in the market for a new smartphone, you'll likely scan spec sheets and read reviews of the top phones, compare display size and technology, RAM amount, and processors. But one factor that is often overlooked is cell reception — and for T-Mobile subscribers, there's only one device that has flagship specs and an exclusive antenna that will actually improve your signal.

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

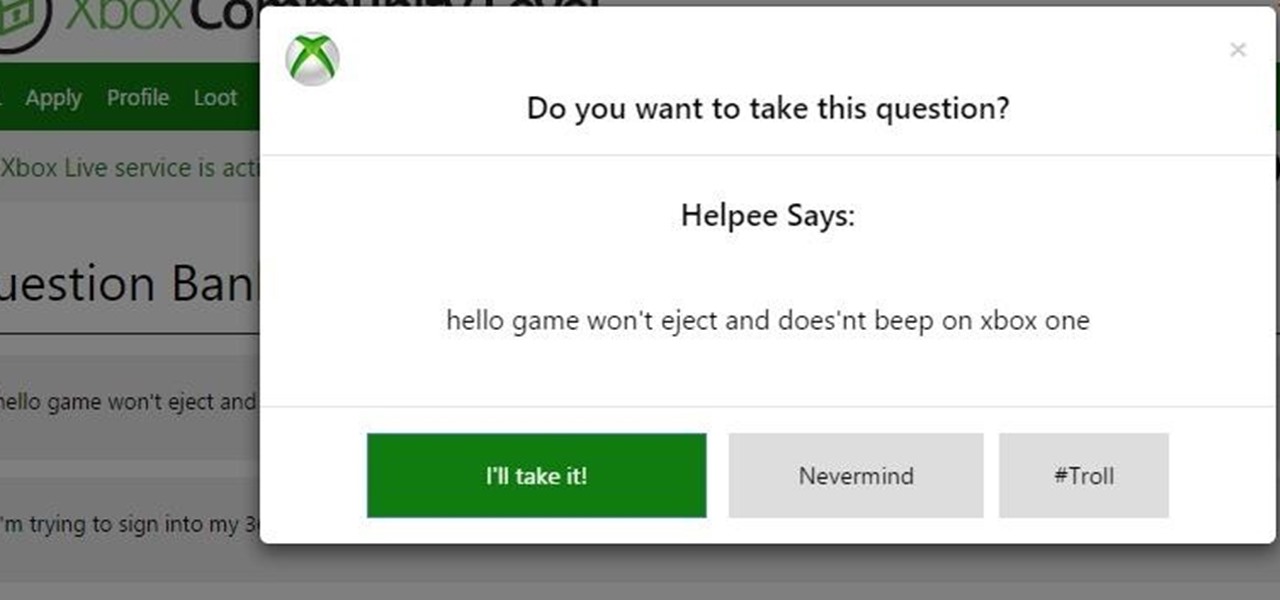
If you're a regular reader of this site, there's a good chance friends and family turn to you as their volunteer technical support staff.

To hack a Wi-Fi network using Kali Linux, you need your wireless card to support monitor mode and packet injection. Not all wireless cards can do this, so I've rounded up this list of 2019's best wireless network adapters for hacking on Kali Linux to get you started hacking both WEP and WPA Wi-Fi networks.

One of the biggest features of Android Oreo is a picture-in-picture mode that lets you watch videos in a floating window while you're using other apps. Honestly, it's fantastic and intuitive, but there are a few ground rules you'll need to learn to master the new feature.

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.

It's the end of an era. Facebook's WhatsApp just announced that older Android devices equipped with the Gingerbread operating system will no longer be able to use the messaging app as of February 1, 2020.
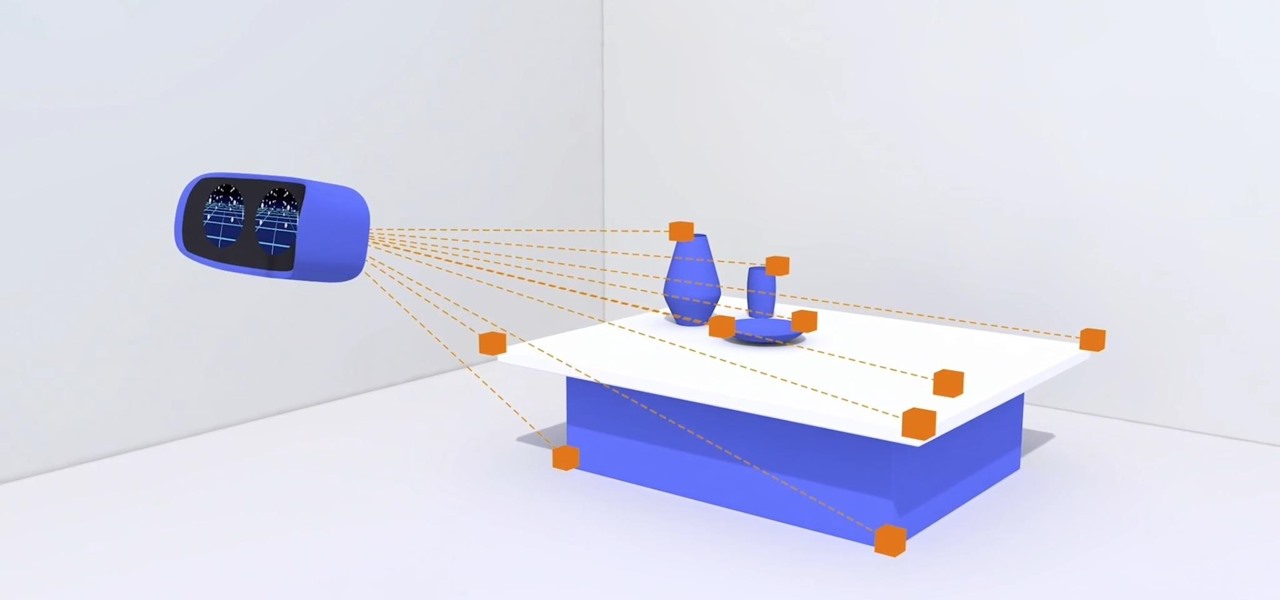
Today in Santa Clara, California, at the Augmented World Expo, Scope AR revealed a major new update that will add markerless tracking for their remote assistance application, Remote AR, on standard devices.
Google announced several new devices (as well as updates to existing devices) that will take advantage of the company's augmented and virtual reality platforms.

It really is a pain getting an Apple device fixed ... What's a gal to do when there's jelly stuck in your Macbook Pro fan and no Apple Store in sight? (Yes, this actually happened to me. Stop laughing.)
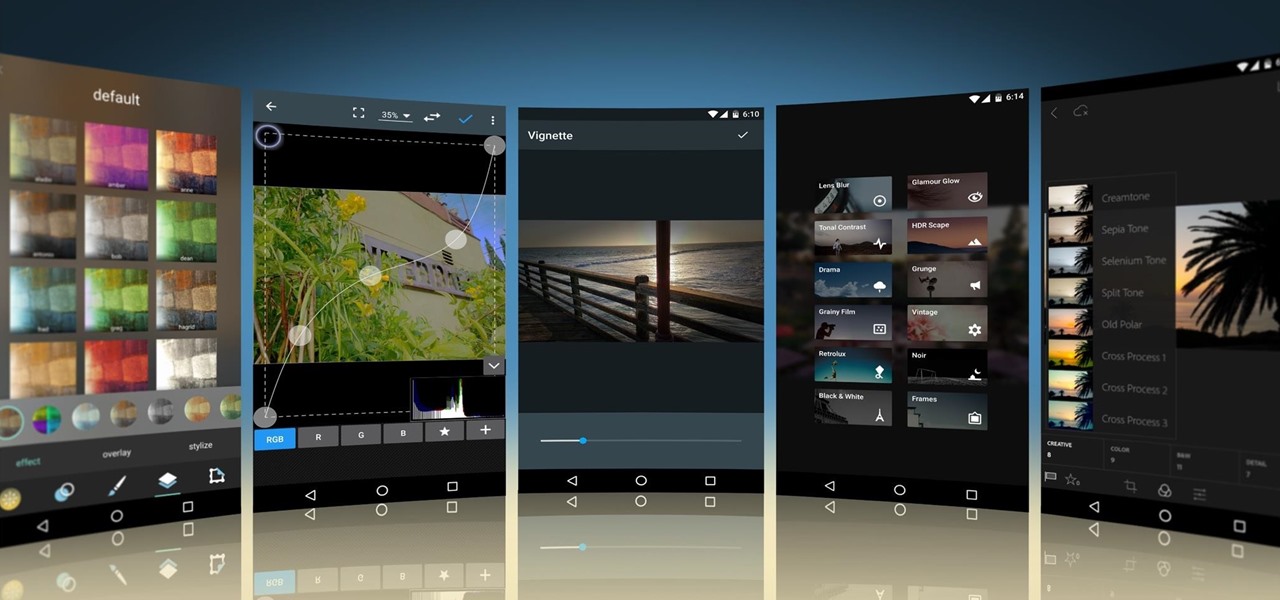
Unity 5.6 was just released on March 31, and it will be the last entry in the Unity 5 cycle. With all of the new features, it looks like Unity 5 is going out with a bang.

Baidu's self-driving car unit has had a tough week. Today, the company's leading artificial intelligence (AI) expert, Andrew Ng, announced in an optimistic blog post that he would be leaving the Chinese search engine company to pursue AI research on his own.

A lot more people are about to be able to use Android Auto. Google announced at I/O 2016 that you'll soon be able to use the app with only your phone, so you won't need a compatible car or third-party display unit. And if (or more likely, when) Google brings the app to iOS, Apple may lose the precious "infotainment" system battle very early in the game. The update isn't coming until later this year, but once it arrives, you'll be able to mount your phone and use Android Auto the same way that...
It has been a while since my last Raspberry Pi tutorial , but now I am back with another tutorial. This one I should note isn't your typical tutorial, but as always lets boot up our Pi and wreck havoc.

Greetings my fellow hackers.
Smartphone cameras are so good nowadays that there's almost no reason to own a point and shoot. Once the megapixel spec race was finally settled (hint: more isn't always better), manufacturers started focusing on the quality of their camera sensors, which has led to a huge jump in color accuracy, dynamic range, and image clarity.

In this day and age, maintaining your privacy is a perpetual battle, and doing so with an internet-connected device like your smartphone is even more of a struggle. Every website you visit, every app you install, every message you send, and every call you make is a potential vulnerability that could expose you to prying eyes.
Remember portable MP3 players like the classic iPod? Seems like forever ago that they were all the rage, and I don't think I've seen a real one in the wild for a good 5 years now. These devices died out so quickly as a direct result of the onset of smartphones, which allow us to do everything that an MP3 player could do and then some.
Revised Version, Gallery pictures of the Ambassabank have been removed since XCL 2.0 has been released.
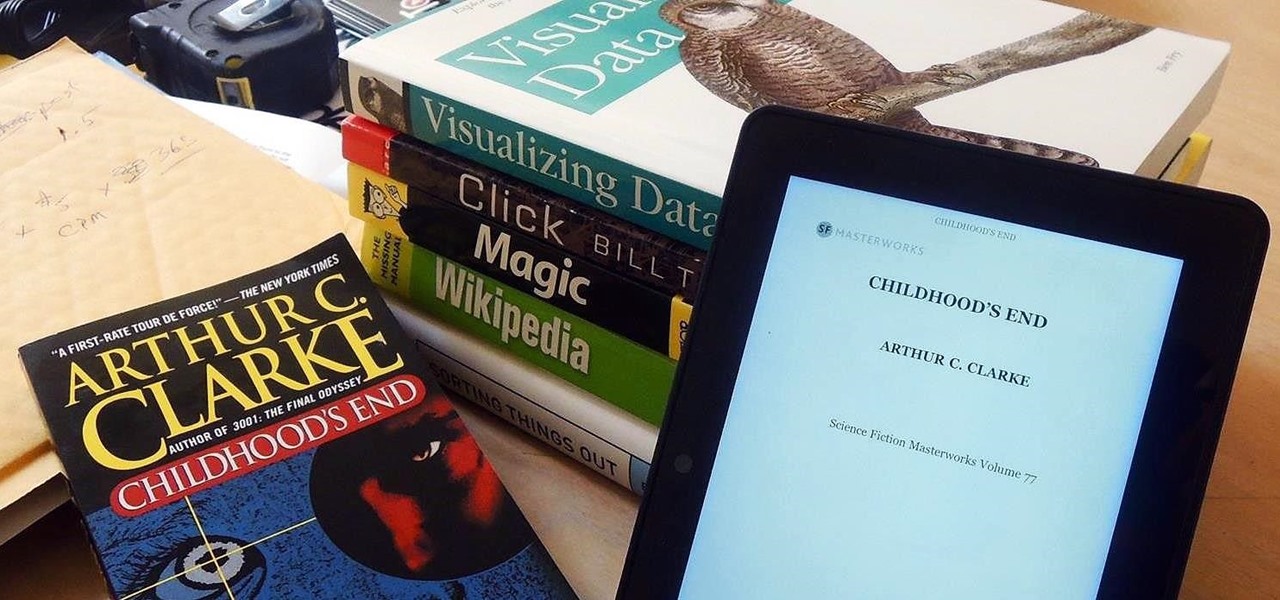
Loaded with a gorgeous display and a powerful processor, the Kindle Fire HDX is an impressive all-around tablet, especially when it's used for what Amazon Kindles were built for—reading electronic versions of novels, textbooks, and other printed works.