In this series you will learn how to use PHP to perform attacks, gather information, and setup backdoors. Along with performing attacks you will learn how to protect yourself from them. In this part you will learn about PHP as well as install Apache and PHP. What you'll need for this series

When performing something such as a mass mailer attack on a company, sending executables usually isn't the best option. That's why, in this tutorial, I'll be teaching you how to code a VBA script macro into a Word document in order to compromise a system. Combined with a little social engineering, this can be a very effective technique.
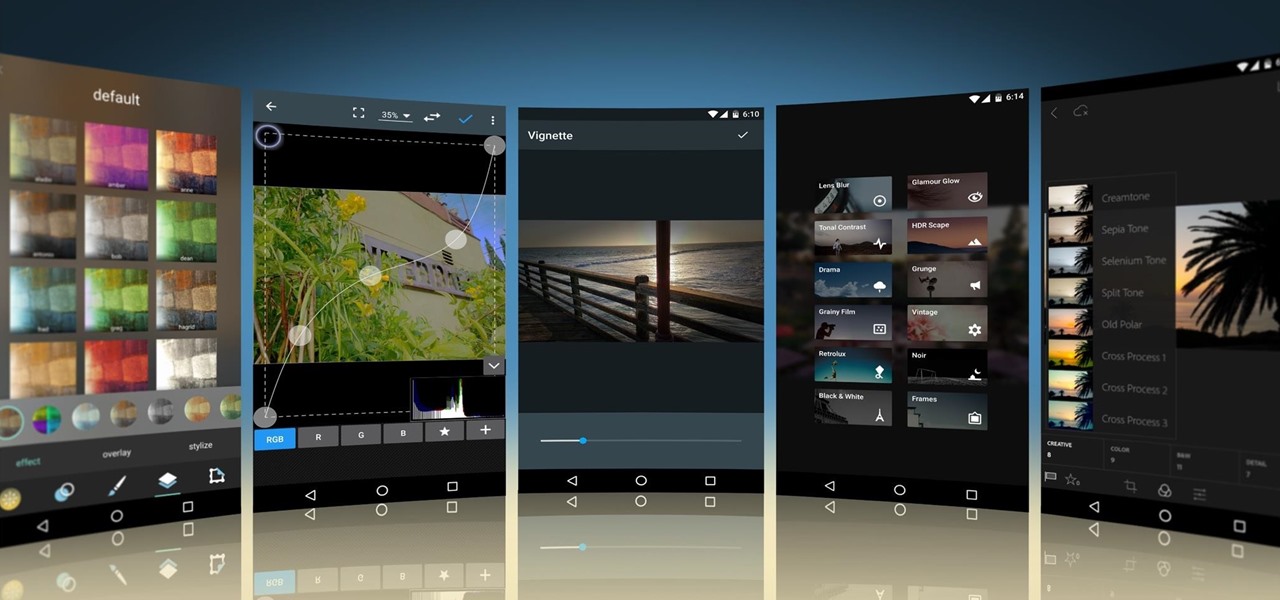
Smartphone cameras are so good nowadays that there's almost no reason to own a point and shoot. Once the megapixel spec race was finally settled (hint: more isn't always better), manufacturers started focusing on the quality of their camera sensors, which has led to a huge jump in color accuracy, dynamic range, and image clarity.

A lot of people think that TOR services are unhackable because they are on a "secure environment", but the truth is that those services are exactly the same that run on any normal server, and can be hacked with the same tools (metasploit,hydra,sqlmap...), the only thing you have to do is launch a transparent proxy that pass all your packets through the TOR network to the hidden service.

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

Crochet Weave with Xpression Hair takes some proper care. It is just like having your hair relaxed; the hair is that texture.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

While honey is one of the most popular ingredients on kitchen shelves the world over, honeybee pollen is still a relatively rare find in most households. It's not hard to guess why: eating pollen just sounds weird... it would probably sell a lot better if it had a more appetizing name, like honey. Furthermore, it looks unlike any other common ingredient, and the smell can be off-putting to some. But it's good, it's healthy, and it's altogether pretty awesome!

Hi Elite Hackers! Welcome! to my 4th post. This tutorial will explain, how to extend a (hacked) AP's range with a wireless adapter. I made this guide because after hacking an AP it was difficult to connect to it (poor connection) and further exploit it. You can also use this:

Revised Version, Gallery pictures of the Ambassabank have been removed since XCL 2.0 has been released.

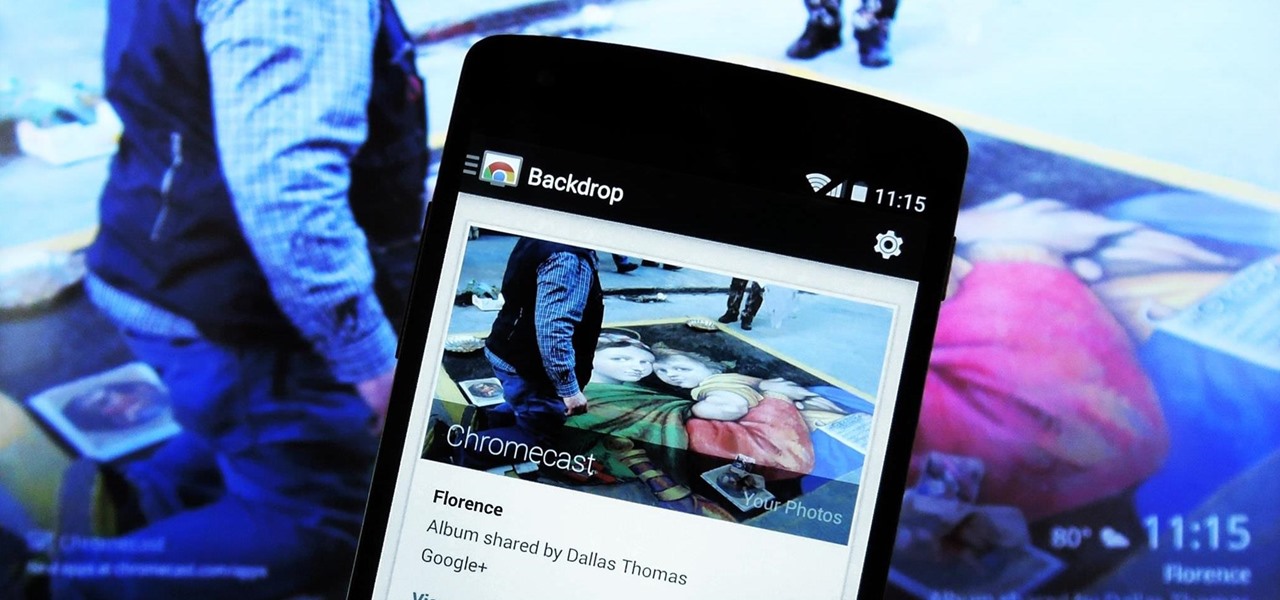
It's been a long-awaited feature since being announced at Google I/O in June, but Backdrop for Chromecast has finally started rolling out. With an update to the Chromecast app for Android and iOS, users will be able to personalize the background images that appear when Chromecast is idle.

In today's world of ordering food from your PC or hailing a cab with an app, it almost seems archaic when we have to actually use our vocal cords to contact a local business. It sure would be nice if we didn't have to use our smartphones as, well, you know...phones.

Video: . How to Make My Famous Spaghetti.

Google, like Apple before them, no longer supports mobile Flash, but clearly there's plenty of Flash content still available on the web. From games to videos, it can be frustrating to get the most out of your mobile browsing experience without Flash functionality.

Apple has acknowledged a problem with the sleep/wake key, better known as the power button, on a certain number of iPhone 5's manufactured through March 2013. As a result, the company has announced the iPhone 5 Sleep/Wake Button Replacement Program, which will replace the power button mechanism, free of charge, for certain iPhone 5 models.

If you've seen ParaNorman or Fantastic Mr. Fox, then you have some kind of idea of what stop-motion animation is. Basically, these artists make objects, or small figures, appear to be moving on their own by manipulating and repositioning them in the smallest increments, then capturing each frame after doing so. When all the frames are compiled together, the final product is something spectacular like The Nightmare Before Christmas, which took roughly 109,440 frames in all.

It's been a great week for Chromecast owners. First, Google released the development kit, allowing devs to install the casting code into their apps. Then, CyanogenMod dev Koush updated his AllCast app to support the Chromecast. That means you can shoot personal movies, music, and photos directly from your Android device over to a Chromecast-connected display.

The Chromecast may be slowly weaving its way into the smartphone ecosystem, but the amount of supported Android apps that are available for the streaming media player are still severely limited.

Assuming that you're not going to knit a sweater and celebrate New Year's Eve with Ryan Seacrest and Jenny McCarthy on ABC's “New Year's Rockin' Eve," it's a pretty safe bet to say that you're probably going to consume alcohol—a considerable amount of alcohol.

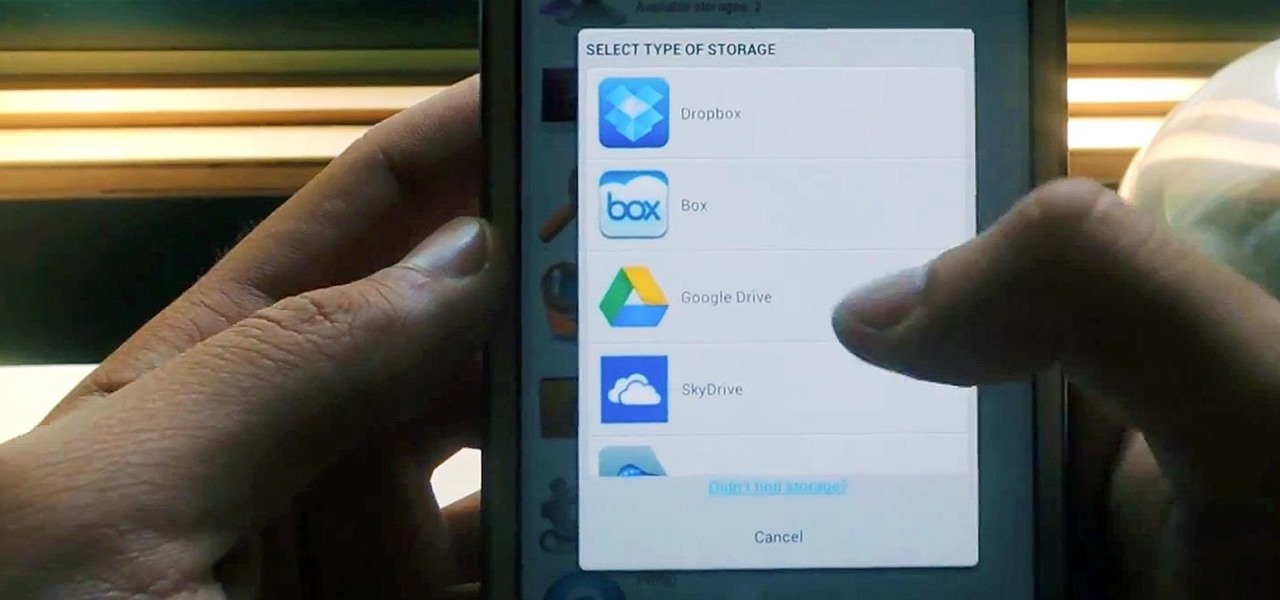
Cloud storage looks pretty good compared to the heavy restrictions that hard drives and other types of external memory carry. The cloud is not only limitless in what it can hold, but it can also easily be accessed from any device that has Internet—your smartphone, work computer, personal laptop, tablet, and more. While accessing a specific cloud storage system like Dropbox or Google Drive may be easy on your Samsung Galaxy Note 2, managing all of them individually can not only get confusing, ...

If you haven't walked into a department store or seen one of those millions of jewelry commercials airing over the last month, you might not know that February 14th is Valentine's Day.

All of my hacks up to this point have been operating system hacks. In other words, we have exploited a vulnerability usually in an operating system service (SMB, RPC, etc.) that all allow us to install a command shell or other code in the target system.

The convenience of storing things on the cloud can definitely make life easier, but if you're storing sensitive files, it could be a total disaster if anyone hacked your account. Some encryption services can be expensive, but if you just need it for personal use, there are some really great ones that don't cost anything. Here are three programs that let you encrypt your cloud storage for free. BoxCryptor

New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to enable USB support in VirtualBox on Ubuntu Linux.

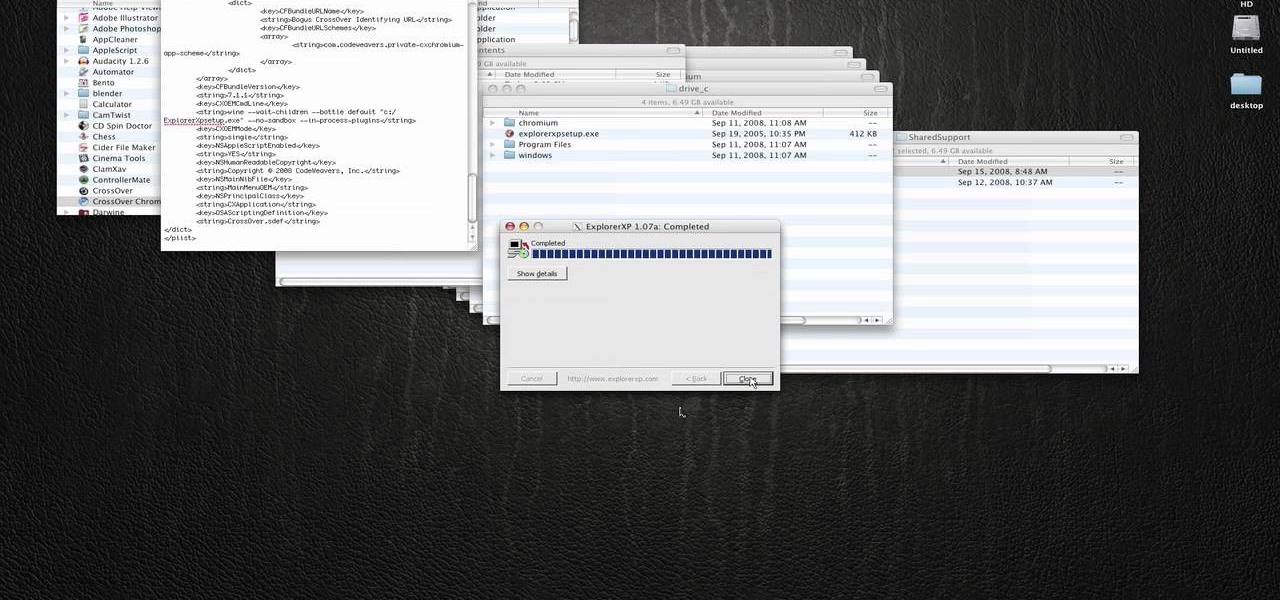
In this how to video, you will learn how to run Windows programs for free on a Mac using Crossover Chromium. You will need to download Crossover and install it by downloading it and dragging it into the applications folder. You will also need Explorer XP. Go to the applications folder and show the package content of Crossover. Go to shared support as you will need a file here later. Open Chromium, go to support, Chromium, and Drive, and then drop Explorer XP into the folder. Open the info fil...

Spotify is a free, ad-supported program that allows you to listen to music online for free. The music is everything from indie labels to the top 100 charts. This guide will help you learn how to listen to music using a Spotify account.

The iPhone supports conference calling capabilities with up to six people. You can even transition from a single-person call to a conference call, or transition from call to call. This tutorial shows you how to make the most of your multi-line call functions in your iPhone.

Looking for freeware alternatives to Photoshop? If you don't need all the bells and whistles of a huge program like Photoshop, this video shows you where to get free photo editing software with good developer support, like Paint.net, FotoFlexer or the GIMP.

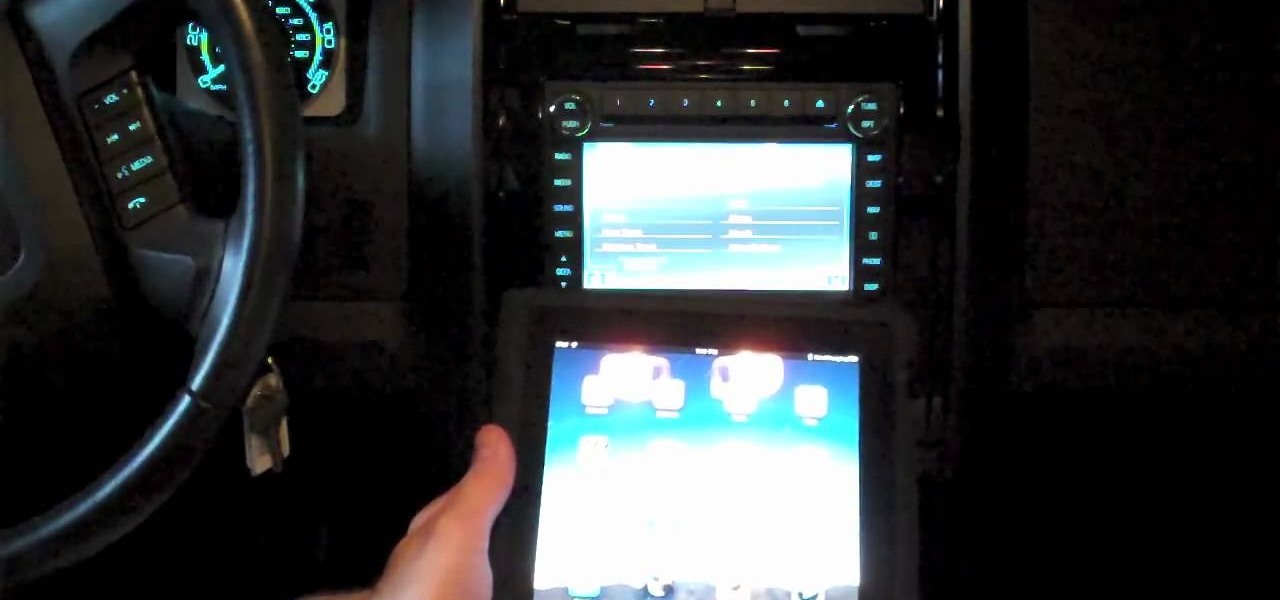
While technically the iPad isn't a supported device with Ford Sync, you can get around that by going to the head unit. Add your iPad as a Bluetooth device, then select the 'sync' option. You can now control your iPad's audio features through Bluetooth.

With version 5.0.1, Safari joins the ranks of web browsers that support user extensions. In this home-computing how-to, you'll learn how to install and make use of extensions in your own web browser. For more information, including detailed, step-by-step instructions, and to get started using browser extensions in Safari yourself, take a look.

The flamingo is a somewhat obscure flatlands skateboarding trick in which the skater swings the board around their leg and stands in a flamingo-like pose for a moment, supporting the board at an angle with their legs, and then drops back into skating from there. No fancy ramps or rails needed for this trick, get practicing!

Parents and coaches are the two most important part of most young athlete's support systems that allow them to excel in their chosen sports. Unfortunately, friction often occurs between these two groups when their opinions of what is best for the young athletes in their charge differ. This video features a high school baseball coach explaining some strategies for parents to maintain a proper, courteous, effective relationship with their child's coaches and improve the skills and well-being of...

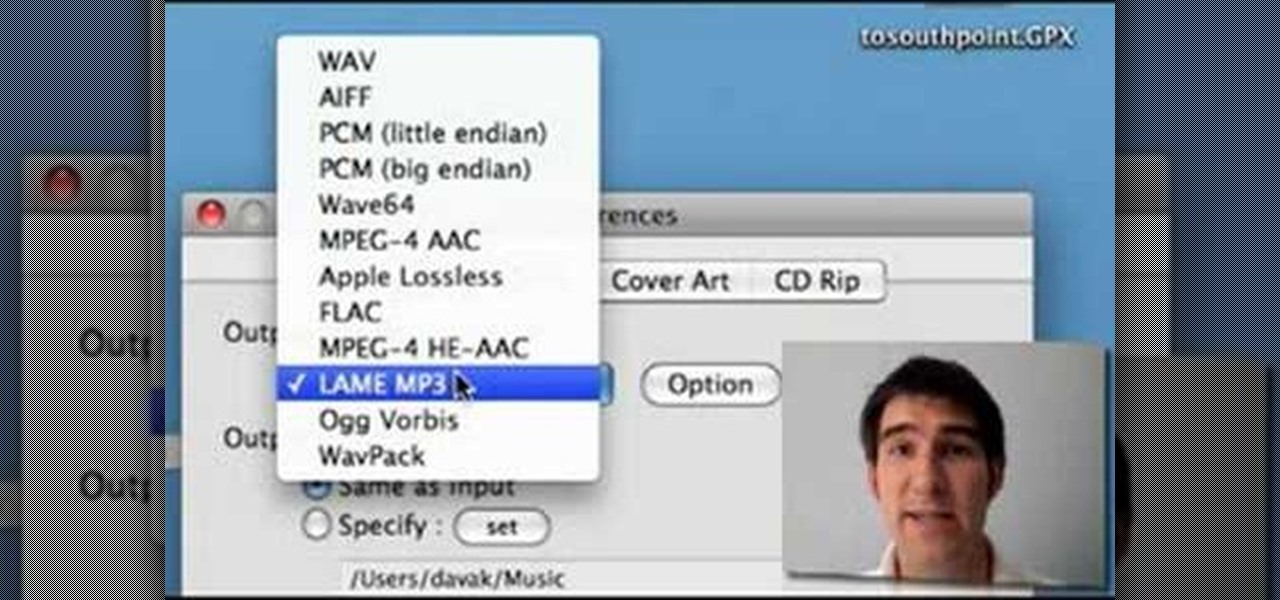
FLAC files are a great way to compress audi files. Unfortunately, iTunes does not support these files outright. But don't worry, you can make those files work on your Mac. This video will show you how make FLAC files compatible wiht iTunes.

Whether you're new to Adobe's Bridge or a seasoned graphic design professional after a general overview of CS5's Mini Bridge, you're sure to be well served by this official video tutorial from the folks at Adobe TV. In it, you'll learn how to manage your media visually with Adobe Bridge CS5 software, which now offers more flexible batch renaming, support for drag and drop between Creative Suite components, and the ability to access files in the context of what you’re working on by using the c...

In this short tutorial, learn how to create videos made for iPods in Premiere CS3. Chad Perkins of Chadd and Todd Podcast shows how to export video from Premiere straight into your iPod, or to YouTube, MySpace, and other Inernet sites that support video.

This software tutorial shows you how to use the Knoll Light Factory Pro plug-in for After Effects. Knoll Light Factory Pro is the industry's favorite tool for creating lens flares, sunsets, photon torpedoes, stars and other effects. It offers a custom lens editor, auto tracking, alpha channel support, and pinpoint control over dozens of settings. If you haven't used the Knoll Light Factory Pro plug-in yet, watch this After Effects tutorial and get started.

Check out this highly educational science video tutorial on how to stand an egg on end during the spring equinox, but wait... does it have anything to do with the spring equinox... no, it doesn't, standing an egg upright has nothing to do with the first day of spring. A lot of eggs have little bumps on the bottom of the egg, so the bumps actually help support the chicken egg when standing upright.

If you want to include lots of movies on one DVD, consider creating sub-menus to better organize the DVD for your audience. Besides support for standard or widescreen menus, iDVD includes families of menus.

This video is for educational purposes only! Cheating is bad and it is not recommended. If you get caught, you support the consequences! If you "steal" want to cheat (ha ha, get it?), you can at least see a good way to do it.

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.