Prying into people's lives without them putting up their guard can be difficult, unless you can convince them that you already know them very well. Most people don't have many friends they can be honest with, and this can be exploited. Once they're convinced you already know their secrets, they'll start to fill you in on the little details.
Particles, such as electrons, have a property called spin which can be measured at any angle, but when measured always results in one of two answers—up or down.

This may seem like an odd subject, because what do Steampunks and iPhones even have to do with each other? Actually, more than you might think!

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

We've all been there. Stranded in a large lot or parking garage, braving the rows upon rows of identical cars in an endless concrete landscape because, for the very life of us, we can't remember where we stashed the very ride that brought us there.

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

The key to becoming a competent white hat is knowing how the technology that you are trying to exploit actually works. SQL injection is one of the most common methods of attack used today and also one of the easiest to learn. In order to understand how this attack works, you need to have a solid grasp of ... you've guessed it ... SQL.

Yes, I understand some people may consider this a repost. However, I have been searching for this answer for 3 weeks and after reading numerous reddit post, Kali Forums post and Null byte post I finally have gotten it to work for me. I would like to compile and share this information with you guys.

hello hackers,newbies and followers of this great community, after some research here in our community, I noticed that there is not even one tutorial that teach Web Development. We have a lot of tutorials on how to hack web site but many do not know exactly how a web site is composed, then I decided, meeting the community's needs, begin to teach people how to develop web sites.

Common knowledge is a funny thing: it represents a majority's opinion on a particular subject and somehow makes that opinion fact. If that 'fact' goes unopposed and unchallenged, then it is passed on and preserved from one generation to the next—regardless of whether it is true or not.

I've tried my hand in the past at defining Steampunk, but as anyone else who has made a similar attempt will tell you, there's a significant backlash from the community against working to create a real definition of what Steampunk is. That may sound ridiculous to some, but it's a very serious matter to others. With the recent announcement that TeslaCon 4 will be called the Congress of Steam, I think it's appropriate to talk about why all of this stuff is worth it. In this article, I'm going t...

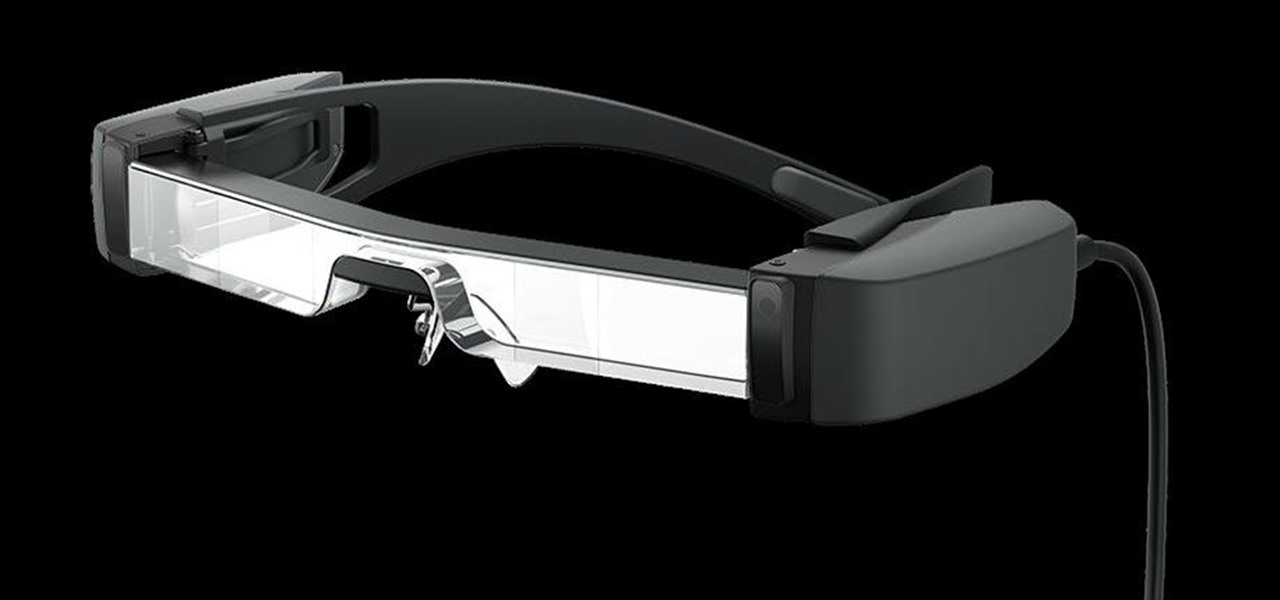
The average business person likely recognizes Epson for its printers or even its projectors, not the futuristic AR wearables.

For SQL injection, the next step after performing reconnaissance and gathering information about a database is launching an attack. But something seems off .. in the real world, it's usually not quite as simple as passing in a few fragments of SQL code to an input field and seeing all that glorious data displayed right in the browser. This is when more advanced techniques are needed.

I'm an Android user. Over the course of the past seven years, I've owned ten different smartphones—all of them powered by Android. This isn't due to some blind trust in Google or some unfounded hate for Apple, either, because I've always made sure to get my hands on each iPhone iteration along the way to see what it had to offer.

Hello, everyone! Many of you don't even know about my existence here on Null Byte, so I thought of contributing something rather interesting. Recently, someone asked how to make your own "Bad USB," and I promised to make a how-to on this topic. In addition, it would be nice to have something related on our WonderHowTo world. So here it is!

Probably SSH is not as clean and fast as other useful tools like netcat, but it has some features which are very useful, and when you'll need them, here's how to behave with that huge amount of computers all over your house.

I love cryptography. It is like a great gigantic puzzle for me to solve. However, it is more important than that. It is also how we keep secrets safe. Not just sorta safe either, but really safe.

When you start up your new Google Pixel 6 or 6 Pro, one of the first things you should do is unlock the hidden "Developer options" menu. Don't let the word "developer" scare you because there are little-known features in this secret Android 12 menu that every Android user can enjoy.

Group chats, particularly ones with many active participants, could bombard your iPhone with hundreds of texts in a single day. It can get overwhelming real quick unless you take precautions to hide all notifications for that conversation. But there's another option now, one that'll make sure you only get alerts for the messages that matter to you most in the thread.

What if the code you are trying to reverse engineer is obfuscated or somehow corrupted? What if no way is left? Here comes what I like to call (wrongly and ironically) the "brute force of reverse engineering".

I've been playing around with iOS 7 for a while now, and for the most part, I dig it. It's a nice update for a stale OS, and there are a lot of great new features. But like any good piece of tech, there are a few things to be disliked. Some of these are big issues, and some could be considered nitpicking, but given that I'm fairly used to the older iOS 6 version, they feel big to me. Paper cuts always hurt worse than gashes.

There are many ways to open up the media account settings for your Apple ID on your iPhone, but they all require two or more steps. However, there is a hidden trick Apple hasn't told anybody about that can get there in one, and it's not Siri.

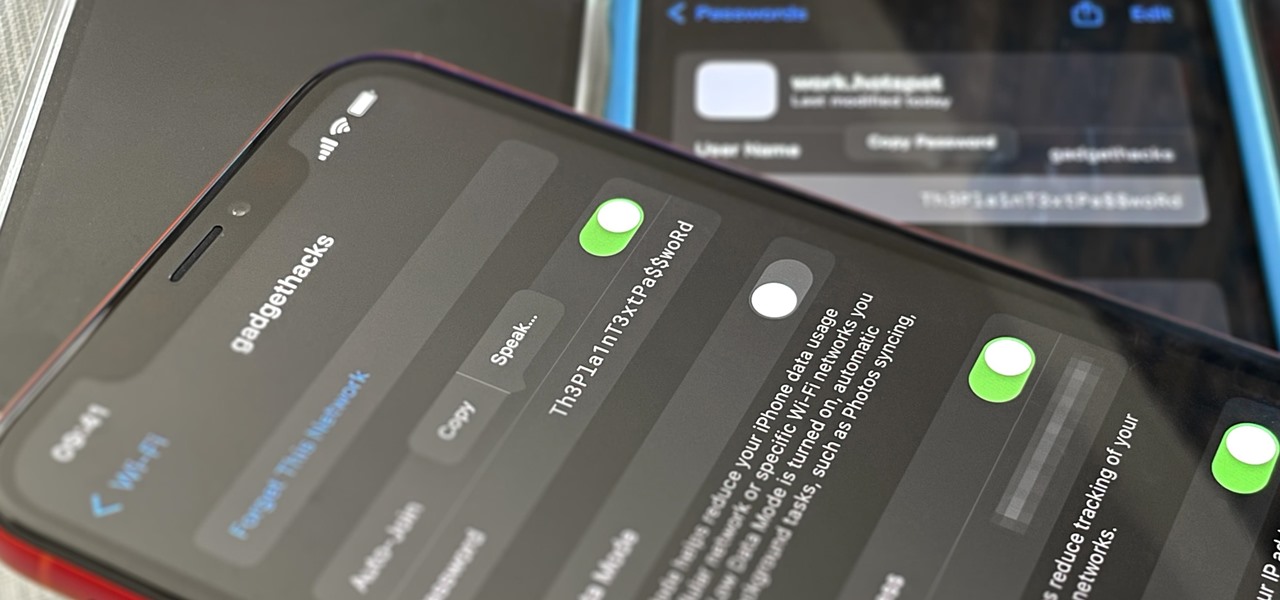
Your iPhone goes with you pretty much everywhere you go, and unless you have unlimited data on your cellular plan, you've probably connected to dozens of Wi-Fi hotspots over the years. Wi-Fi passwords are saved to your iPhone so you can auto-connect to the router or personal hotspot again, but finding the plain text password for a network hasn't always been easy.

Amazon really wants to make itself at home in your home. Like, everywhere in your home, from your doorstep to your kitchen, your kids' rooms, and everywhere in between.

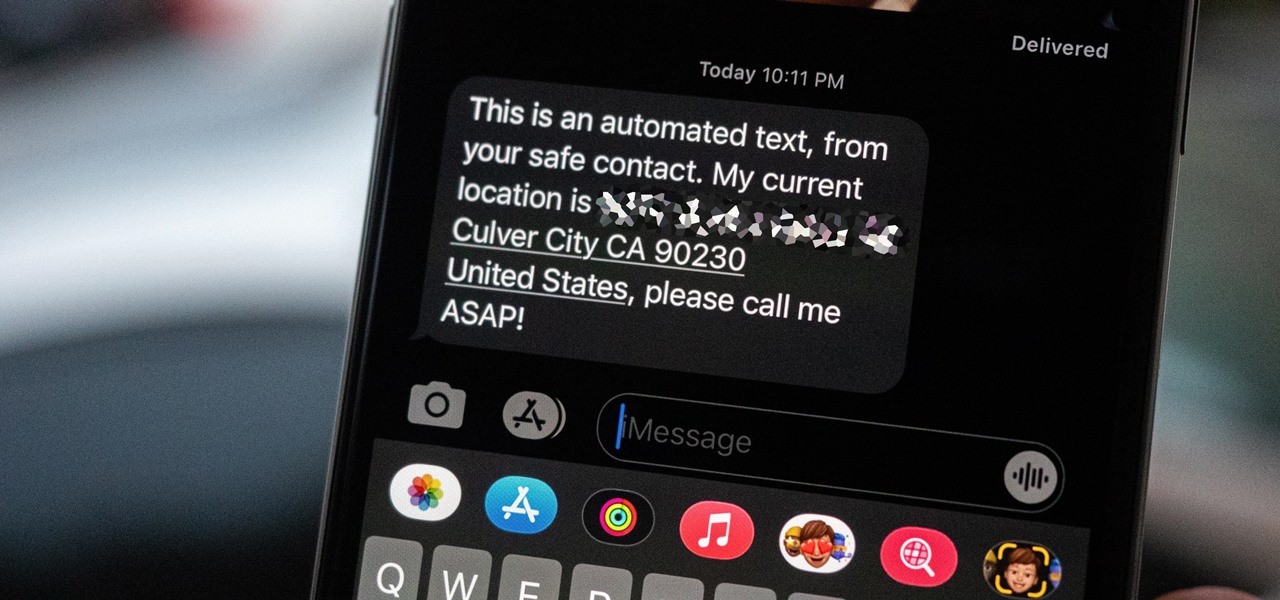
Strange or uncomfortable encounters can be difficult to get away from sometimes if you're overly polite and don't want to hurt anybody's feelings. Thankfully, your iPhone can help save the day, providing you with a plausible excuse to exit the scene without having to conjure up some last-minute reason on the spot.

Silence spreads over these mountains like nothing I've ever felt. If I didn't have Moby blasting in my earphones, there'd probably be no other sounds around. Well, except for someone, Phil probably, murmuring in a nearby tent just low enough to make his words indiscernible.

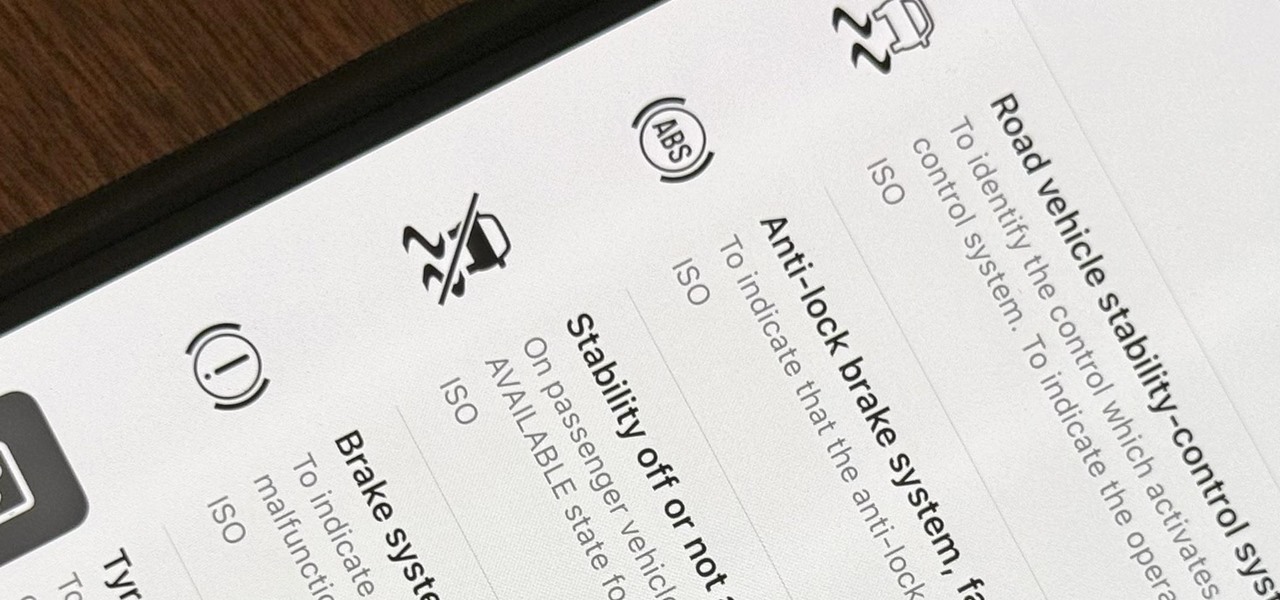
When you encounter a mysterious laundry care symbol or alarming vehicle indicator light, you might just ignore it rather than ask somebody, search online, or open a user manual for the answer. If you have an iPhone, there's an easier way to decipher the meanings behind perplexing symbols and signs—and it only takes a few seconds.

If it has an internet connection, it's got a huge attack surface for hackers. But what makes your phone even more dangerous is its portability and the collection of sensors it houses that can be just as good at tracking you as the camera and mic.

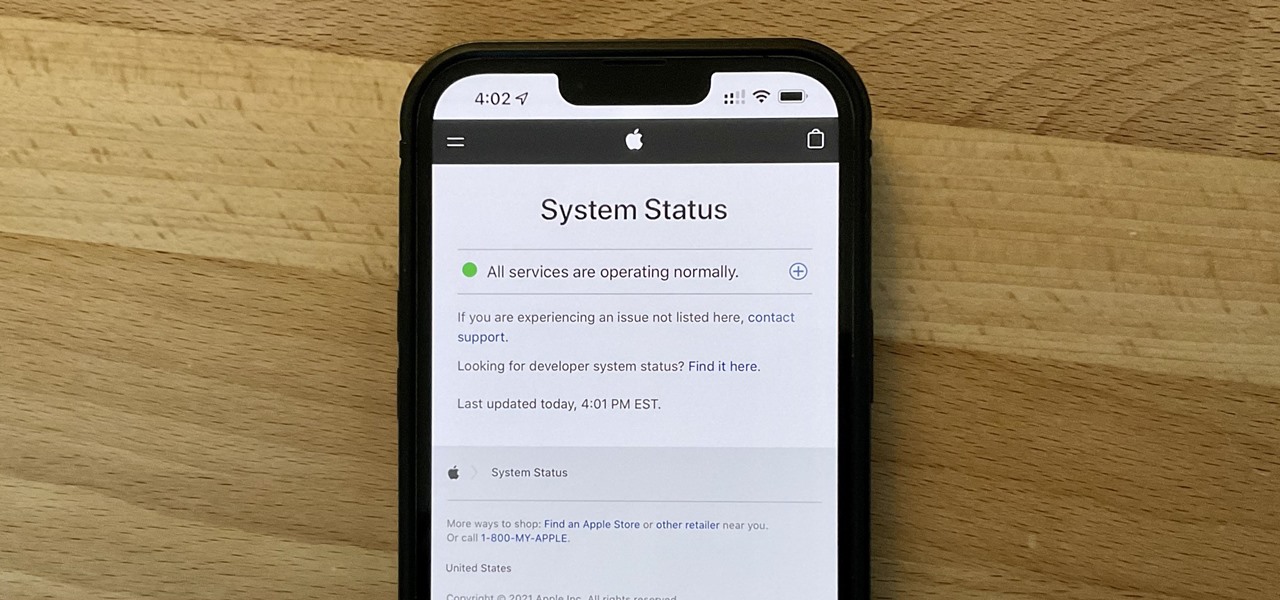
It can be very frustrating: You open your Messages app, send an iMessage, and then see that dreaded red exclamation point or horrible green SMS bubble. At this point, you may be curious whether it's just your iPhone or whether iMessage is broken for everyone, but how do you find out?

Flight disruptions can cost billions of dollars, but most modern commercial flights rely on air traffic control systems that harbor serious vulnerabilities. The Federal Aviation Administration uses an infrastructure called NextGen, which relies on Automatic Dependent Surveillance – Broadcast, or ADS-B for short.

The iPhone doesn't stop at last year's excellent iPhone 12 lineup. Apple's been developing its iPhone 13 models for a while now, and there are a lot of rumors already with eight or nine months still to go until a release. This year, we're expecting four new models with similar sizes and features to 2020's offerings. If you want to know what makes the 2021 iPhones so different, we've got answers.

Looking for another Angry Birds fix? Well, drop the lame birds and pick up the zombies—Stupid Zombies, that is. You'd think that killing "stupid" undead beings would be easier than knocking off a few "angry" vertebrates, but it's actually more challenging—and more fun! Who wouldn't enjoy killing zombies with a shotgun blast and watching their heads roll? Armed with a shotgun and a strategic mind, your goal is to take out all the living dead with as few bullets as possible, trying to achieve t...

As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm sure you want to know how to protect against it. Well, here it is! In this article, you will find out what SQL Injection is, what you can do to protect against it, and additional recommendations that are easy to do and onl...

The idea is to trick your roommate into opening a can of oatmeal that will be booby-trapped. The outcome will be hilarious, considering your roommate doesn't punch you in the face.

Illustrator's gradient mesh tool is a powerful one for vector artists... if you know how to use it. This tool can help create beautiful and vivid mesh-based vector portraits, as long as your skills are up to par. If not, try out some of the beginner tutorials on WonderHowTo for using the mesh gradient tool in Adobe Illustrator, then move onto mastery...

Watch this video tutorial to see how to cook homemade southern biscuits. We suppose biscuits are considered a side dish, but we could make a meal out of these. You will never forget Chef Ashbell's techniques, in particular to fold the dough 3 times only, once you hear him say so. Who are we to argue with perfection? These biscuits are easy and fast to make! Bake homemade southern biscuits.

Definition Declare is a card game played by 3 or more people. If 4 people are playing the game, then one pack of 52 cards (without the jokers) is sufficient. For 4 to 8 people, two packs of cards are required, without jokers.

Definition Judgment is a game where you have to predict the number of hands you'll make and try to make those number of hands that you predict. It is a game usually for 3 or more players. Even 2 players can play but then the game won't be that interesting. 5 players can play the game using one deck of 52 cards. Jokers have no role here.

For the purpose of simplicity, we shall consider the Windows version to be used as Windows XP. How to start the calculator in Windows XP?

After years of being a PC technician and Windows System administrator, I had the blind hatred for Apple that I thought I was suppose to have. I swore that I'd never even touch an iPod, let alone buy an Apple product. But I found a new career that drug me out of the Windows server/PC tech room dungeon, and into the bright modern office of a web development firm. Then it happened. After a couple weeks with all this Apple stuff around me, my love for gadgets and (closet) Apple curiosity got the ...