There are a couple of limitations that Microsoft put in to Windows 7 upgrades that can prevent users from upgrading and ultimately force them to do a clean install. First limitation is that they won't let you to upgrade Windows 7 if you run Windows 7 release candidate that was released earlier this year, which they won't let you to upgrade to a download Windows edition. If you are running Windows vista ultimate you cannot upgrade windows 7 professional. We have to buy an ultimate edition then...

Take a look at some vectored hearts… it's fully vectored. Older versions of Illustrator should be able to handle this project just fine. Watch this Illustrator video tutorial to learn this heart-shape design. A vector heart is great for Valentine's Day. No source files are needed. Just Adobe Illustrator and some time. Learn about using the grid, the basic pen tool, gradients, swatches, blend modes, masking, and so much more.

Everyone can agree on one thing: mashed potatoes are delicious. But they can be kind of ticky to make perfectly. You can end up with gluey mashed potatoes, potatoes that don't taste quite right, or you could forget the cream. CHOW is here to help with their You're Doing It All Wrong series to help you rectify your mashed potatoes issues.
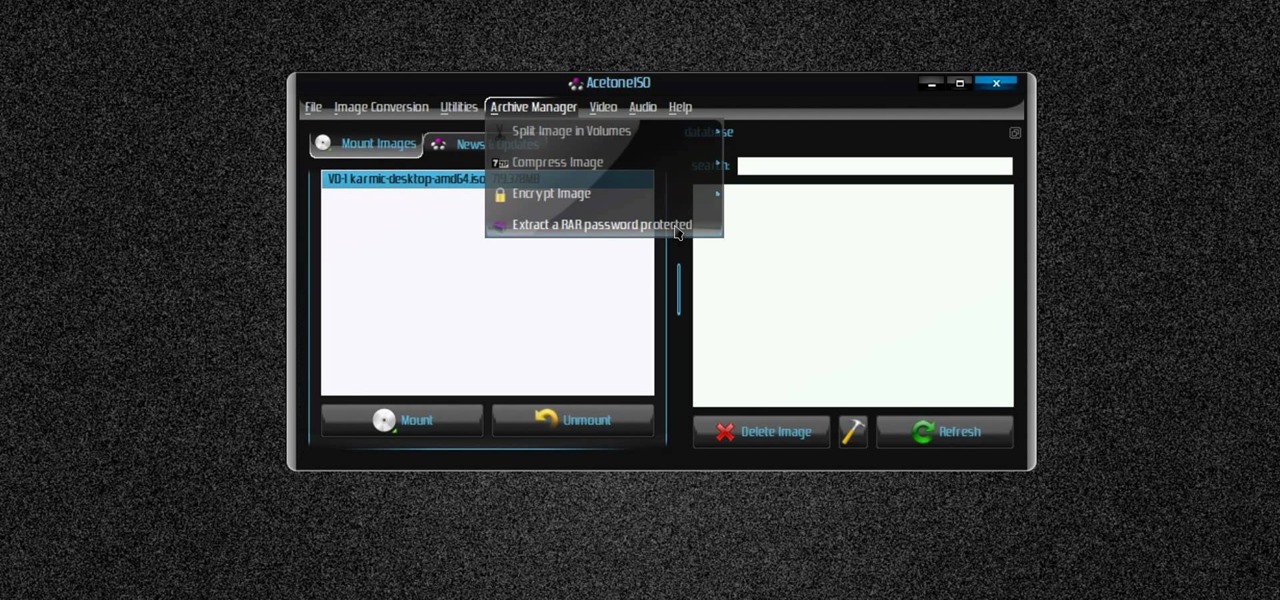
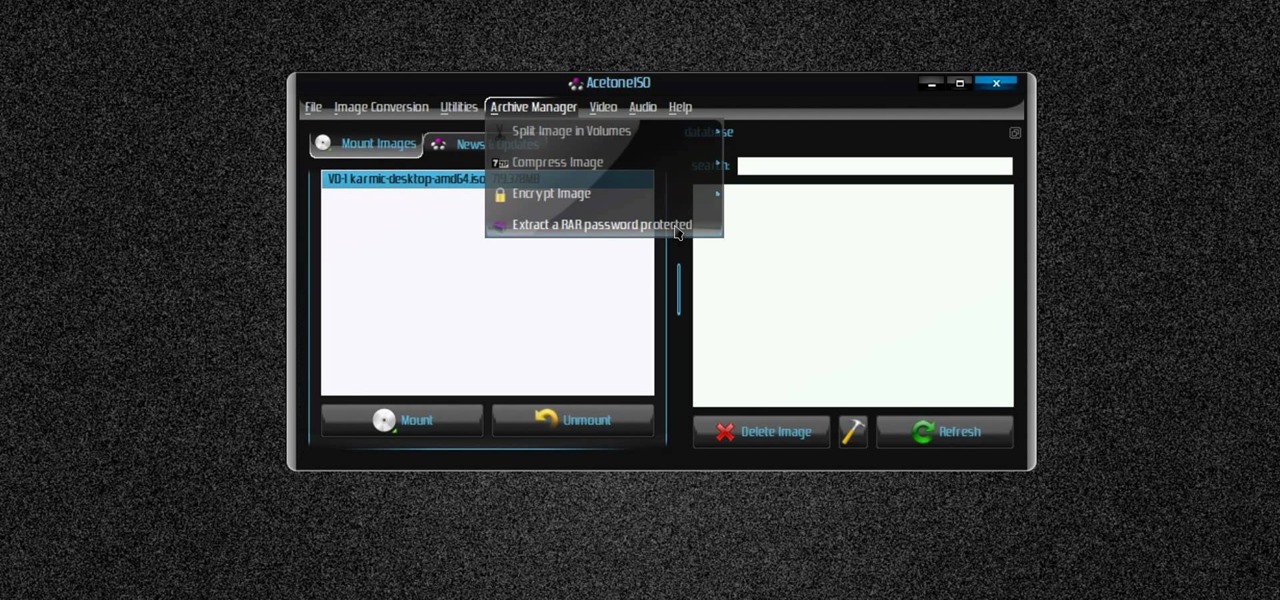
New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to manage CD/DVD images with ease on Ubuntu Linux.

This is a tutorial on Rerooting Blythe Doll Hair from the CRAFT Video Podcast. Blythe dolls are great for making three-dimensional self portraits. There is an enormous community of customizers working with the Blythe Doll. One of the main online sources for customization is Puchi Collective, which houses oodles of tops for changing her eyechips, face makeup, and clothes.

Citizen Engineer is an online video series about open source hardware, electronics, art and hacking by Limor (`Ladyada') Fried of Adafruit Industries & Phillip (`pt') Torrone of MAKE magazine.

Want to break free from the confines of DVR land? If you're tired of spending all the money to download program listings from your DVR, then it's time for a change. If you don't want to mess with DRM files anymore, but want to backup your system, then MythTV is the way to go. You'll need to build your own PVR (personal video recorder) with thanks to MythTV, and it will end up costing you less than $500. Well worth the investment. The MythTv software is free and open source, so you just need t...

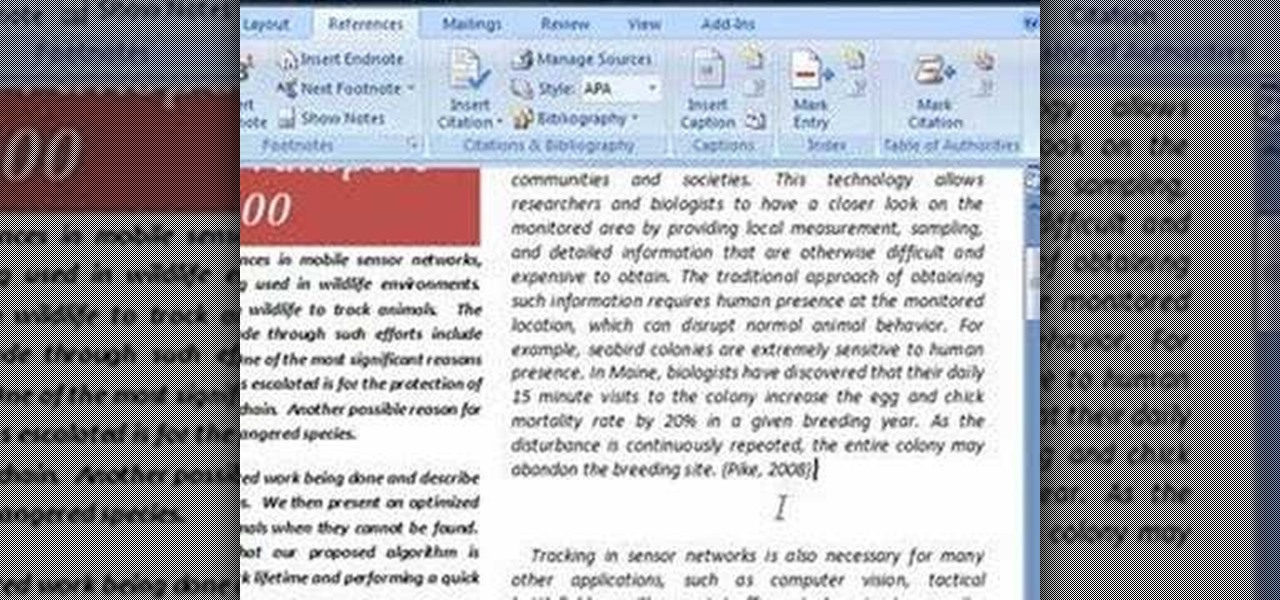
In order to use the bibliography feature in Microsoft Word 2007, you will need to begin by opening your document in Word. Find the place where you would like to add a reference. Place your cursor in that spot. Then, go to the tool bar. Click on "Insert Citation". Click on "Add New Source". When the pop-up opens, enter the information about the periodical or book that you are citing. Fill it in completely. Make sure you choose the type of material you are referencing in the top drop down menu....

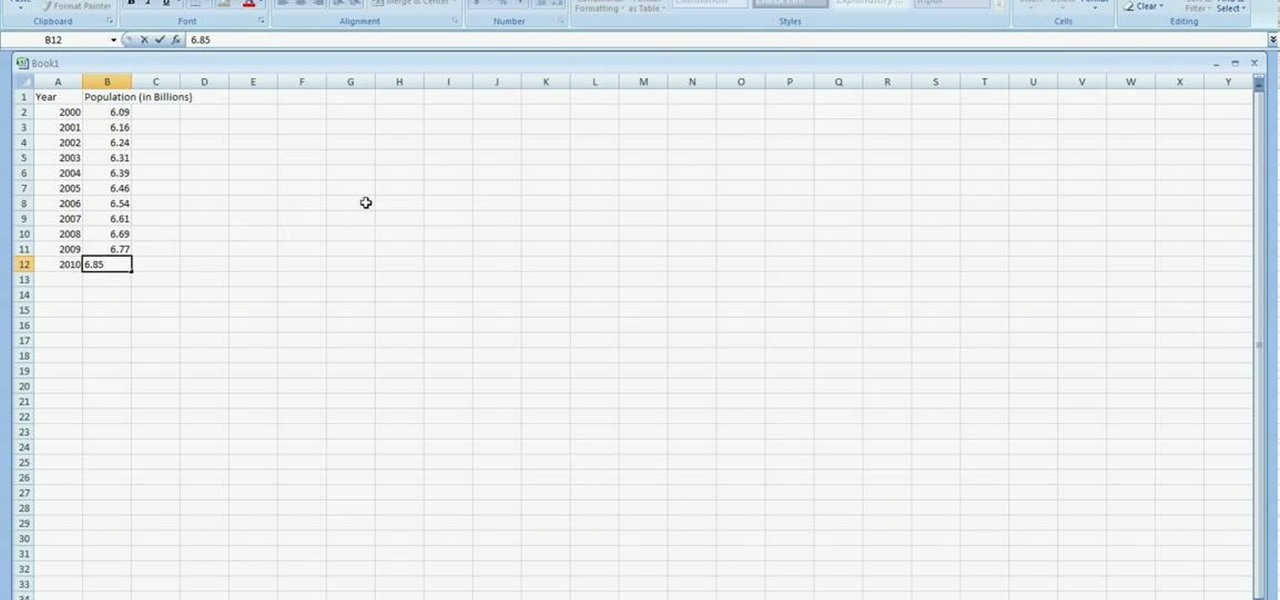
In excel a left click is made on box A1 and the X title is typed in as year. In A2 the year 2001 is typed and in A3 the year 2002. Both A2 and 3 boxes are highlighted and the bottom right hand corner is used to drag the work into a copied sequence down to A12. In B1 "population in billions" is typed. From the web site the data is copied and typed in as it appeared and the numbers are rounded off. A click is made on the "insert" tab and line is selected from the menu which appears. The upper l...

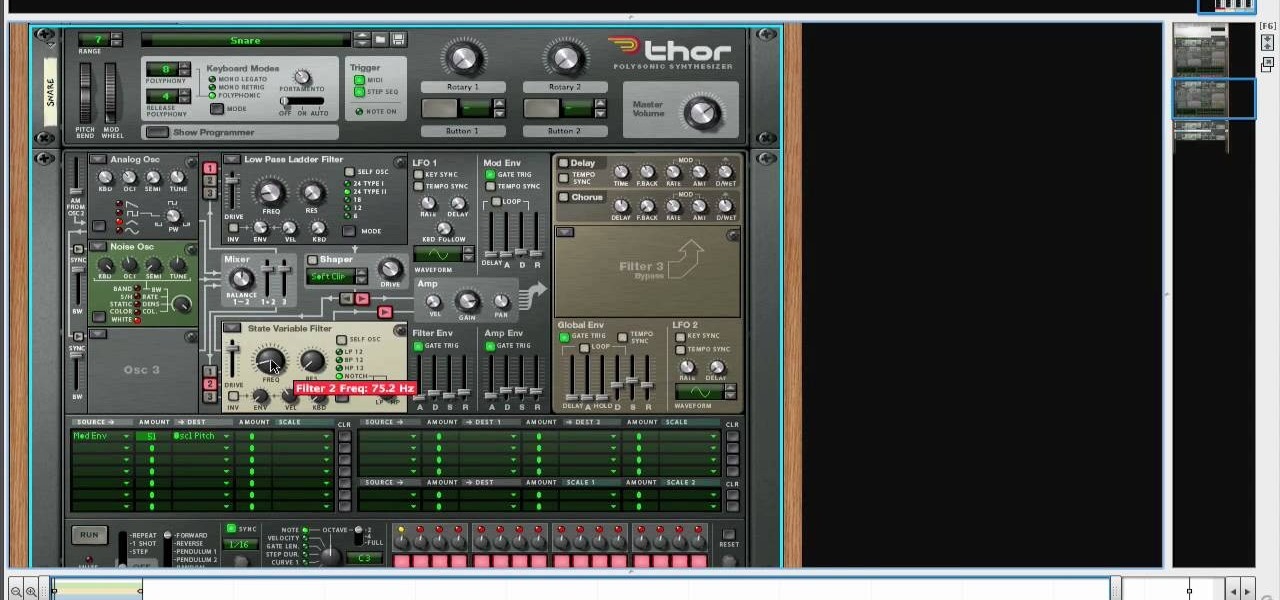
Create drums sounds using Reason's Thor synthesizerYou can use the Thor synthesizer to make a kick, snare, hat and clap sound.Kick:Use the analog oscillator with triple wave form octave3. Set the source to mod envelope 45 destination oscillator 1.Use a very short attack to K and release time. You get the short effect of pitch. Try different oscillator types to get different textures.Snare: Use the same basic patch that we created for the kick. We will keep it as the basis for most patches for...

Video demonstrates how to synchronize two folders on windows without doing much of copy pasting and does the job easily. This is a free wear, “FlagSync”.

If the grill is going hot then it’s a perfect time to throw on a big t-bone steak. You can cook some potatoes right along with your stake. With this professional advice you can get really succulent and perfectly cooked t-bone with minimal effort.

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

Video: . Recycle your hard drive into a hidden flash memory device that only you know how to turn on and use in secret. This DIY hack project allows you to recycle your broken hard drives back to life and turn them into something useful.

While Apple and Google have paved the way for developers to create web-based AR experiences through their respective mobile toolkits, an open source option has entered the space.

Historically, patents have never been a rock-solid source for uncovering the future of a company's product pipeline. However, sometimes, the images you find in the patent application search archives are so convincing you have to pay attention.

In the current state of the augmented reality space, Leap Motion is the only well known name in DIY AR headset kits with its Project North Star design, which gives makers the blueprints to build their own headsets.

Cracking the password for WPA2 networks has been roughly the same for many years, but a newer attack requires less interaction and info than previous techniques and has the added advantage of being able to target access points with no one connected. The latest attack against the PMKID uses Hashcat to crack WPA passwords and allows hackers to find networks with weak passwords more easily.

In recent years, Apple has assembled its augmented reality team and supply chain through a series of acquisitions, high-profile hires, and strategic investments, but at least one potentially major deal was recently ditched.

Hand tracking technology company Leap Motion has built a stunningly fluid augmented reality ping-pong game that not only showcases the capabilities of its open source Project North Star augmented reality headset, but also demonstrates how artificial intelligence can elevate immersive experiences.

Less than two months since unveiling Project North Star, Leap Motion has released the reference design that will allow developers, makers, and even manufacturers to build their own augmented reality headsets based on Leap Motion's work.

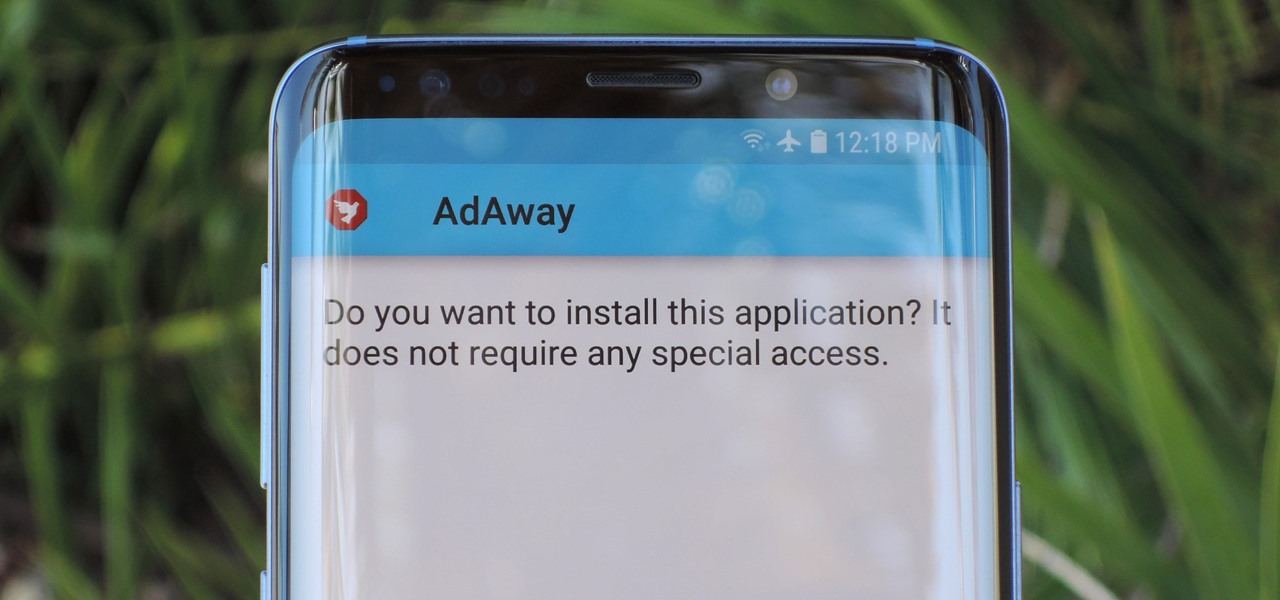
Starting with Android 8.0 Oreo, the process of sideloading apps has changed dramatically. Google removed the old "Unknown Sources" setting and replaced it with a permission that you have to grant to individual apps. It's really an interesting security feature.

If it had come out just a week earlier, around April 1, no one would have believed it. But it's true, Leap Motion has developed its own prototype augmented reality headset, and it looks pretty wild.

Just days after Bose did its best to frame a pair of glasses frames with spatial audio as "augmented reality," a patent application from Magic Leap, surfaced on Thursday, March 15, offers a similar idea, but with real AR included.

Venmo makes it incredibly convenient to send money to friends and family, and it all happens instantly from the comfort of your smartphone. Even better, if you have an iPhone, Venmo lets you conduct transactions straight from the default Messages app, giving you more flexibility and convenience over Android users.

There are more than 2 billion Android devices active each month, any of which can be hacked with the use of a remote administration tool, more commonly known as a RAT. AhMyth, one of these powerful tools, can help outsiders monitor a device's location, see SMS messages, take camera snapshots, and even record with the microphone without the user knowing.

Like gas on an open flame, rumors and whispers have flared up in recent months around hopes of augmented reality smartglasses from Apple. But among all the false leads and unsubstantiated chatter, we finally have a credible report that some sort of Apple AR smartglasses are actually in development.

As we have seen previously with the likes of SethBling's Mar I/O videos and other examples, video games seem to be a great source for training AI neural networks. Augmented reality and machine learning are part of a collection of technologies that seem to be growing toward a point of maturity, and that will likely cause them to be intertwined for the foreseeable future. As developers, machine learning will definitely change the way we create software in the coming future. Instead of going lin...

When it comes to watching movies and TV shows in Amazon's Prime Video service on an iPhone, it's as simple as installing the Amazon Prime Video app, signing into it, then playing content. However, on an Android phone, it's a lot more complicated.

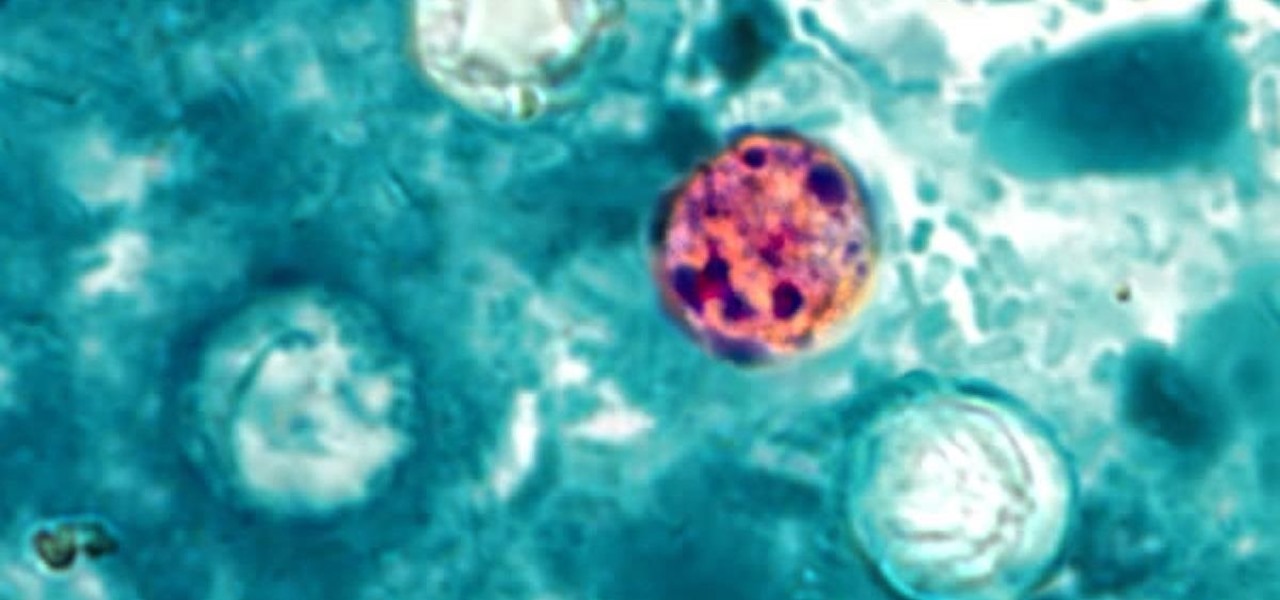
The intestinal parasite Cyclospora cayetanensis has a dramatically increased infection rate this summer, and the source is still unknown, the CDC advised today. 2017 is a good year for Cyclospora looking for homes to start their families and a bad year for those of us who don't like food-stealing tenants living in our bodies.

Open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital fingerprints into giant neon signs. The problem is no longer whether the right data exists, it's filtering it down to the exact answer you want. TheHarvester is a Python email scraper which does just that by searching open-source data for target email addresses.

According to a source at TechCrunch, a new version of Snap's 'Spectacles' could include augmented reality.

We've worked hard to reduce the flow of toxic chemicals into our waterways, which means no more DDT and other bad actors to pollute or destroy wildlife and our health. But one observation has been plaguing scientists for decades: Why are large quantities of one toxic chemical still found in the world's oceans?

AR.js is a new JavaScript solution that offers highly efficient augmented reality features to mobile developers. With HoloJS released back in December, there is a potential that the free AR.js, developed by Jerome Etienne, one of Next Reality's 50 people to watch in augmented and mixed reality, could work with the Microsoft HoloLens as well.

A company known as Cyanogen, Inc. has been in the news numerous times over the past year, and almost every time their name is brought up, it's amid reports of an impending doom. The writing is on the wall for the makers of Cyanogen OS, as it appears that there is little that can be done to prevent the company from going belly-up in the near future.

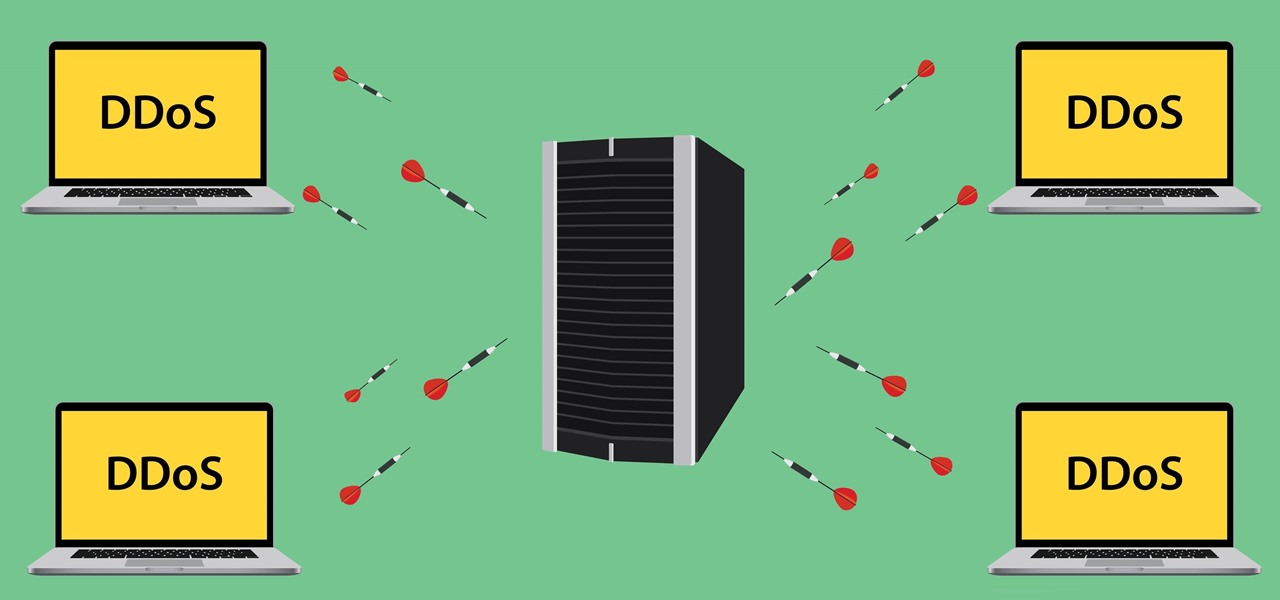
Security journalist Brian Krebs recently suffered a record-breaking DDoS attack to his his website, clocking in at or near a whopping 620 Gbps of traffic. Krebs' site was down for over 24 hours, and it resulted in him having to leave his CDN behind.

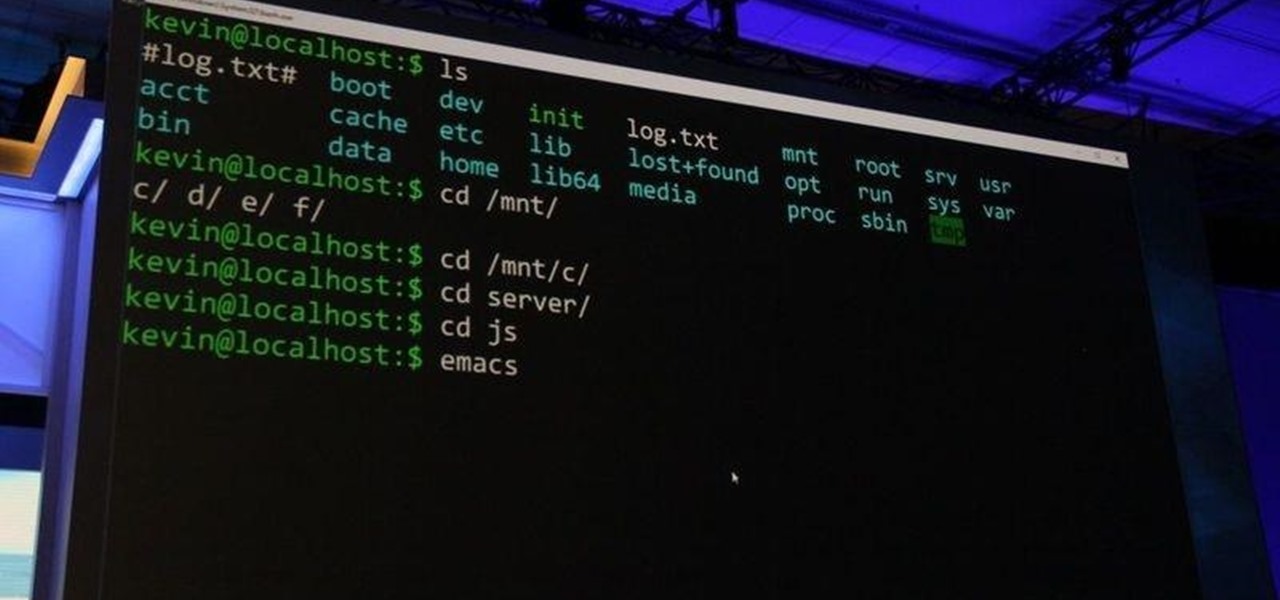
As most of you know, I am a strong advocate for using Linux for hacking. In fact, I would go so far as to say that you cannot be a hacker without knowing Linux well. I laid out various reasons for this in my "Why Every Hacker Should Know & Use Linux" article, and I even have a lengthy, continuing series on Linux Basics to help those new to Linux master it.

Although lots of the bigger hotel chains are lessening the restrictions they put on their room TVs, some smaller ones are still taking measures to prevent you from plugging in computers or streaming devices into an HDMI port. However, there are a few steps you can take to bypass these restrictions and watch your own media in a hotel that has restricted TVs.

It has been a while since my last Raspberry Pi tutorial , but now I am back with another tutorial. This one I should note isn't your typical tutorial, but as always lets boot up our Pi and wreck havoc.

Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic