Spinach raita is yet another tasty way to prepare the ever popular green vegetable. Spinach is a rich source of vitamin A, vitamin C, tocopherol, vitamin E, vitamin K and magnesium. It also contains several vital antioxidantS and folic acid. Watch this How-to video and try this spinach and yogurt combo with rice or chapattis. It’s a perfect accompaniment to any meal.
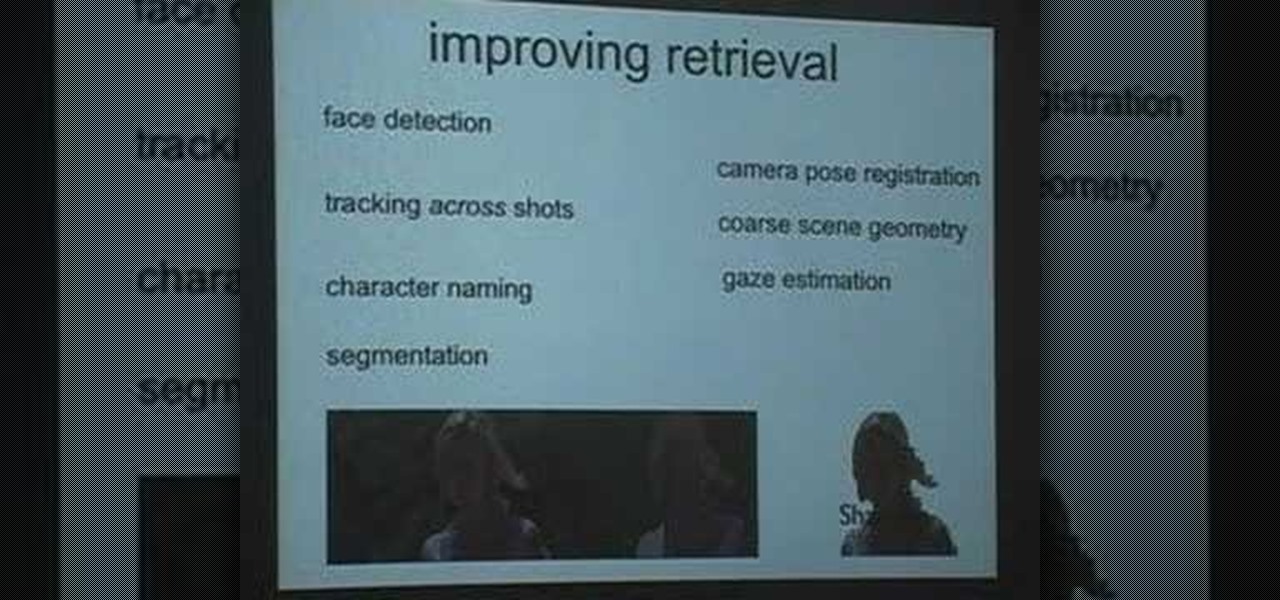
This is a Google Tech Talk from March, 26 2008. Timothee Cour - Research Scientist lectures. Movies and TV are a rich source of highly diverse and complex video of people, objects, actions and locales "in the wild". Harvesting automatically labeled sequences of actions from video would enable creation of large-scale and highly-varied datasets. To enable such collection, we focus on the task of recovering scene structure in movies and TV series for object/person tracking and action retrieval. ...

If you've got an iPhone with firmware version 3.0 and you want to figure out how to use Cydia on it, check out this video. You are shown how to download and update your Cydia sources.

Check out this video tutorial on Blender. You'll see how to successfully create a modeled skull in Blender.

The amount of information we see on a daily basis is overwhelming. Then there's all the data we never even see. If your career depends on making sense of all of this information, you need to understand the programs that do the heavy lifting.

The term "hacker" often has negative associations attached to it, yet the world is in dire need of professionals with hacking skills. White hat hackers are ethical computer hackers that use their hacking skills to pinpoint network vulnerabilities and patch them up before they can be exploited by the bad guys.

Producing professional video can be expensive and time-consuming. Green screens are cumbersome and require a lot of space, whereas dialing in the perfect lighting comes with its own challenges. For people working on a budget and space constraints, achieving the ideal background can be a nightmare.

With the whirlwind of noise surrounding the COVID-19 virus sweeping the nation, it's not hard to default to panic mode. One of the best ways to avoid panicking, however, is to follow trusted sources of information and avoid all of the opinions and trolls that don't reflect reality.

It's pretty much a given at this point that Facebook has a lot of data on us. While you might be conscious of the data you share with Facebook when you post, upload photos, or chat with friends on Messenger, you might not be thinking about all the data it receives from websites and apps you use outside the social media giant. Now, you can actually do something about it.

Songs new and old are given a fresh purpose through the TikTok meme machine, but it can be tricky to figure out where a track originally comes from. Sure, you can tap the name of the song to see the source on TikTok, but if it were a snippet uploaded by someone other than the track's creator, the song title likely wouldn't be listed. Luckily, there is an easy way to figure it out.

Folders are great for organizing apps and removing clutter from your home screen. But once they become overfull, it's not as easy to find and launch an app. If you have a jailbroken device, however, there's a tweak that will lessen the hassle of rummaging through folders and make it easier to open the apps they contain.

Rumors are what Apple dreams are made, so most of the time it's best to ignore the juicy ones -- but some Apple rumors demand a least a little attention.

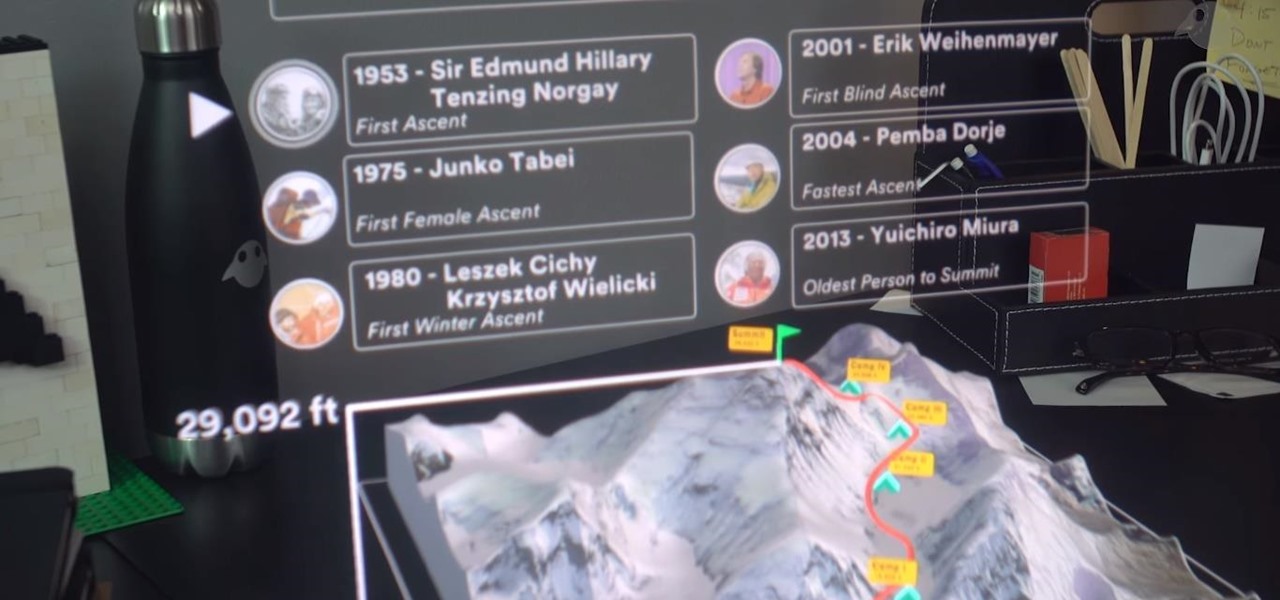
Prior to this year, Time primarily relied on image markers in the magazine to trigger its special augmented reality features

Beyond spotlight-grabbing features like Dark Mode and computer mice support that iOS 13 contains, Apple has also made its mobile platform more user-friendly for people that exhibit sensitivity to on-screen animations. If you've always found the transitional effects between app pages jarring, your iPhone now has a setting to help with that, preventing possible motion sickness and anxiety.

When researching a person using open source intelligence, the goal is to find clues that tie information about a target into a bigger picture. Screen names are perfect for this because they are unique and link data together, as people often reuse them in accounts across the internet. With Sherlock, we can instantly hunt down social media accounts created with a unique screen name on many online platforms simultaneously.

Phone numbers often contain clues to the owner's identity and can bring up a lot of data during an OSINT investigation. Starting with a phone number, we can search through a large number of online databases with only a few clicks to discover information about a phone number. It can include the carrier, the owner's name and address, and even connected online accounts.

Despite the recent gut punch of staff layoffs, Canada-based smartglasses startup North and its Focals are likely to be in the game for a while longer.

Open-source intelligence researchers and hackers alike love social media for reconnaissance. Websites like Twitter offer vast, searchable databases updated in real time by millions of users, but it can be incredibly time-consuming to sift through manually. Thankfully, tools like Twint can crawl through years of Twitter data to dig up any information with a single terminal command.

Over the past two years, Apple's Worldwide Developers Conference (WWDC) has become a showcase for new ARKit capabilities. This year, it could offer more information related to Apple's long rumored augmented reality wearable.

We're still weeks away from a probably HoloLens 2 release, but Microsoft's immersive computing team is still hard at work on other aspects of its "mixed reality" ecosystem.

For anyone using open source information to conduct an investigation, a balance between powerful tools and privacy controls are a must. Buscador is a virtual machine packed full of useful OSINT tools and streamlined for online research. This program can easily be set up in VirtualBox, and once that's done, we'll walk you through some of the most useful tools included in it.

Like an overbearing mother, Apple will constantly nag you through annoying red bubble alerts about iOS updates that are ready to install. Fortunately, you don't have to take this issue lying down, as there are ways to prevent your iPhone from receiving OTA updates and their corresponding prompts, regardless of whether your device is jailbroken or not.

The Magic Leap One: Creator Edition has been teased for months now, and while we still don't know exactly when the sales will begin, it can't be long now because we've discovered a couple of new hints that the device's launch is imminent, hiding in plain sight on the company's website.

While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

Before Google Chrome entered the scene and subsequently dominated the market, Firefox trailed only Internet Explorer as the most popular web browser. Now, Mozilla has its sights set on a new opportunity to revive its browser for immersive experiences.

With numerous insider reports, patent awards, acquisitions, and hires over the past few years, augmented reality smartglasses from Apple appear to be an inevitability.

Why would Magic Leap, a company preparing to launch its first augmented reality headset this year, need a developer for iPhone and iPad apps? It's not as crazy as it sounds.

While much of the technical specifications of the Magic Leap One: Creator Edition still remain a mystery, some clues to its internals are hidden among the guides in the now freely-accessible Creator Portal.

Design flaws in many routers can allow hackers to steal Wi-Fi credentials, even if WPA or WPA2 encryption is used with a strong password. While this tactic used to take up to 8 hours, the newer WPS Pixie-Dust attack can crack networks in seconds. To do this, a modern wireless attack framework called Airgeddon is used to find vulnerable networks, and then Bully is used to crack them.

Augmented reality hardware maker Avegant has reportedly laid off between 20 and 30 employees, with founder Edward Tang returning to the CEO role at the company.

This year will be an interesting one for iPhones. With speculation that the expensive iPhone X is underperforming, rumors have circulated that Apple will release three "bezel-less" devices, one of which will cost less by omitting the OLED panel for a traditional, yet large, 6.1" LCD. Now, thanks to the source of this rumor, we have an idea how much that lower-tier iPhone will cost.

In another move that pushes Meta 2 toward becoming a legitimate workplace tool, Meta Company has partnered with Dassault Systèmes to bring augmented reality support to the latter's Solidworks 3D CAD software.

Starting your morning right is an essential first step to a productive day. Whether you're running late, rushing to catch up on the day's news, or lagging behind with early emails, little hiccups like these can have a trickle-down effect and ultimately ruin your day. Like with many problems, though, your smartphone can help.

So you want to do Kendrick Lamar's "HUMBLE." in Animoji Karaoke, but you need the lyrics. Well, now you can see those rhymes spit out in augmented reality.

You love augmented reality (that's why you're here!), but some of you also love cryptocurrencies, most popularly known in one of its forms as Bitcoin. So you might be wondering why you can't you find two of your favorite emerging technologies together in one app. Take heart, early adopter — now you can.

Apple rarely changes the ringtones on its iPhones. In fact, the last addition was all the way back in iOS 7. However, it appears they wanted to do something special with the 10th-anniversary edition iPhone, so Apple included a unique ringtone called "Reflection" on the iPhone X.

As expected, Magic Leap closed a Series D round of equity funding, raising $502 million from new and existing investors. Less expected, however, were a fresh set of rumors that the company's first devices could ship within six months.

Tor is an excellent obfuscation network for web traffic, and while instant messaging over the network is very useful, it can be relatively difficult to configure. In this guide, we'll look at two synchronous communications platforms (instant messengers) which can be routed over the Tor network, Ricochet and XMPP.

If you have a taste for sweets, you have at least one thing in common with mosquitoes. While too much sugar is unhealthy for humans, a new product makes sweets deadly to mosquitoes.

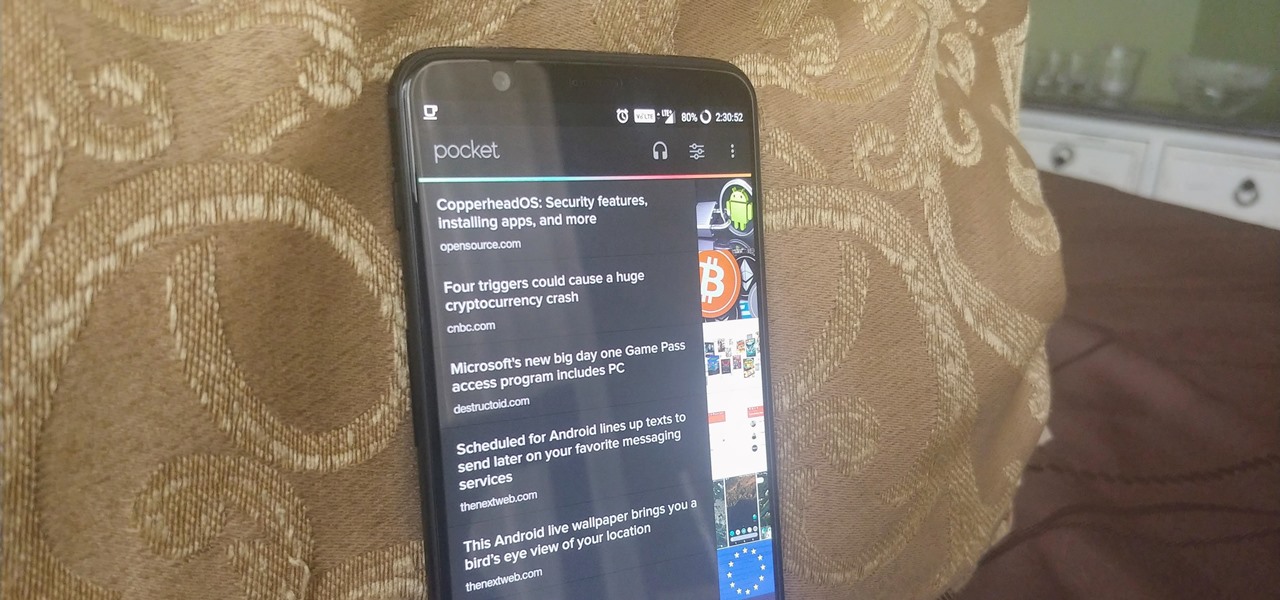
Android Oreo may not be the flashiest release, but it's got tons of under-the-hood changes. We recently discovered documentation in the AOSP source code that outlines one of these understated features, which has been dubbed "Rescue Party."