The freezer section at your local grocery store may have plenty of popsicle flavors, but they're mostly going to be the same old fruit-flavored varities you've been shoving in your mouths for years. None of those will truly get your tastebuds rolling like some creative homemade versions will. We've already shown you some crazy sounding ones made with Oreos, veggies, and coconut flakes, but now we're back with some more chilling ideas. Just wait until you get down to the corn one!

Greetings my fellow hackers, In the previous article, I discussed briefly about ransomwares and their devastating capabilities. Devastating in a way that ransomwares are not only known to encrypt files but to also lockout some specific functions of the system and hold it up for a ransom.

Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics series, I showed you how to acquire a forensically sound, bit-by-bit image of a storage device such as a hard drive or flash drive, but now let's dive into live memory.

Of course, if it were a perfect form of currency, it would have become the standard by now. But it hasn't. Wanna know why? The story begins with the advent of agriculture, when humans had settled down under groups as units called villages, over 10,000 years ago.

Let's say you're flush with Google Opinion Rewards credits, or you just got a Google Play gift card for your birthday. This is a perfect opportunity to remove ads and unlock new features by upgrading some of your free apps to their paid counterparts, or to finally purchase that app you've been lusting after that doesn't offer a free version.

Welcome back, my fledgling hackers! In this series, I am trying to develop your knowledge of digital forensics, which is valuable whether you're choosing a career in it or just want to know how your hacker activity can be traced. Few professional digital forensic investigators have a hacking background, but the best ones do.

Have you ever been using your computer when a friend randomly decides it's time to start up a text message conversation? You usually have to stop what you're doing on the desktop, then go pick up your smartphone and respond to the text. Then, if your buddy replies with another message, you have to juggle back and forth between your mouse and keyboard and your handheld device.

Welcome back, my novice hackers! This new series on Bluetooth hacking was inspired by a recent episode of Mr. Robot (my favorite TV show). In episode 6, Eliot hacked the bluetooth keyboard of the police office in order to hack the prison and release his nemesis, Vera. This is just one of the many hacks we will explore in the series.

Whether you are sending your phone in for repairs or finally selling it to upgrade to a new flagship, you are going to need to make sure all of your personal data is removed from your device.

Developing GUI apps in python is really cool. I ask those who understand the language to help convert some of the command-line or console programs or apps ( I mean programs that are useful to a hacker ) to GUI. I know GUI makes us lazy and not wanna learn but we should all know its fast. Today's tutorial is on p2p chat app I developed last week and decided to share it with the community since its kinda cool.

The desktop Start menu is finally back! After receiving a lot of negative user feedback, Microsoft ditched the touchscreen-first approach of Windows 8 and went with a more traditional setup for mouse-and-keyboard users in Windows 10.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.

At last, what you all finally waited for! Hi! Fire Crackers,

Welcome back, my tenderfoot hackers! Have you ever wondered where the physical location of an IP address is? Maybe you want to know if that proxy server you are using is actually out of your local legal jurisdiction. Or, maybe you have the IP address of someone you are corresponding with and want to make certain they are where they say they are. Or, maybe you are a forensic investigator tracking down a suspect who wrote a threatening email or hacked someone's company.

Welcome back, my rookie hackers! "How can I travel and communicate over the Internet without being tracked or spied on by anyone?" It's a question many Null Byteans have asked me, so I have decided to write a comprehensive article addressing this issue.

If you've ever wiped your computer without having a proper backup of your operating system, or just wanted to cause some havoc online, chances are you've had to rely on Linux to help you out, specifically the Ubuntu distro.

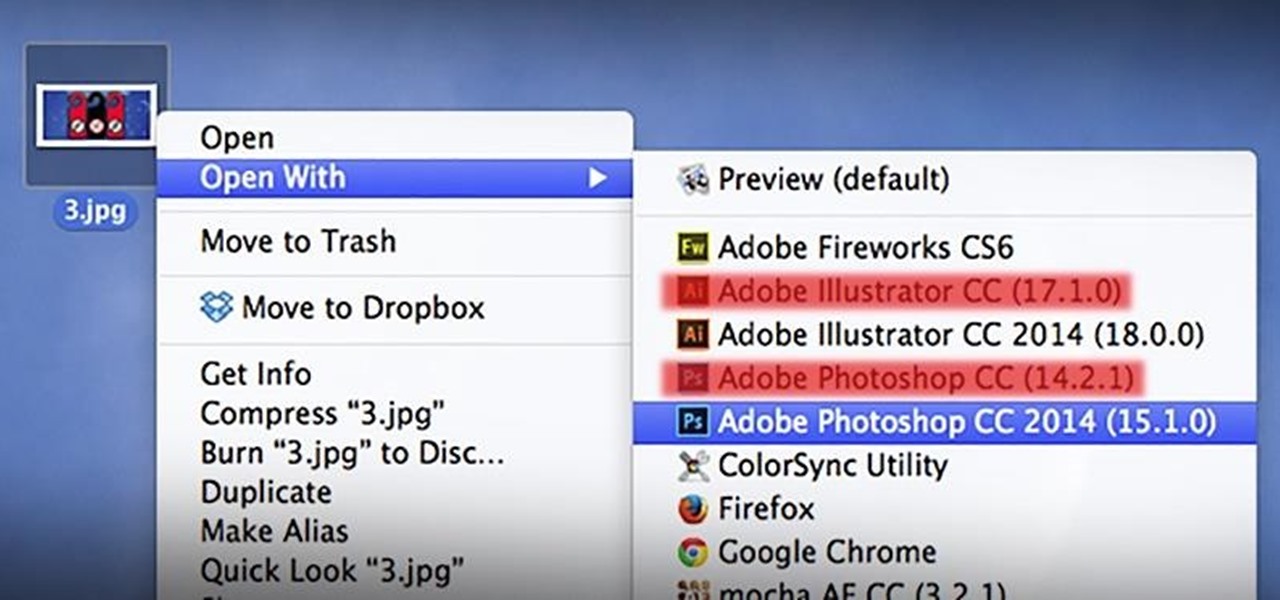
As a regular Mac OS X user, I have a love/hate relationship with the "Open With" contextual menu. Sometimes, it has just what I need. Other times, it's often packed with unnecessary or duplicate items, or missing the app I want to open the file up with the most.

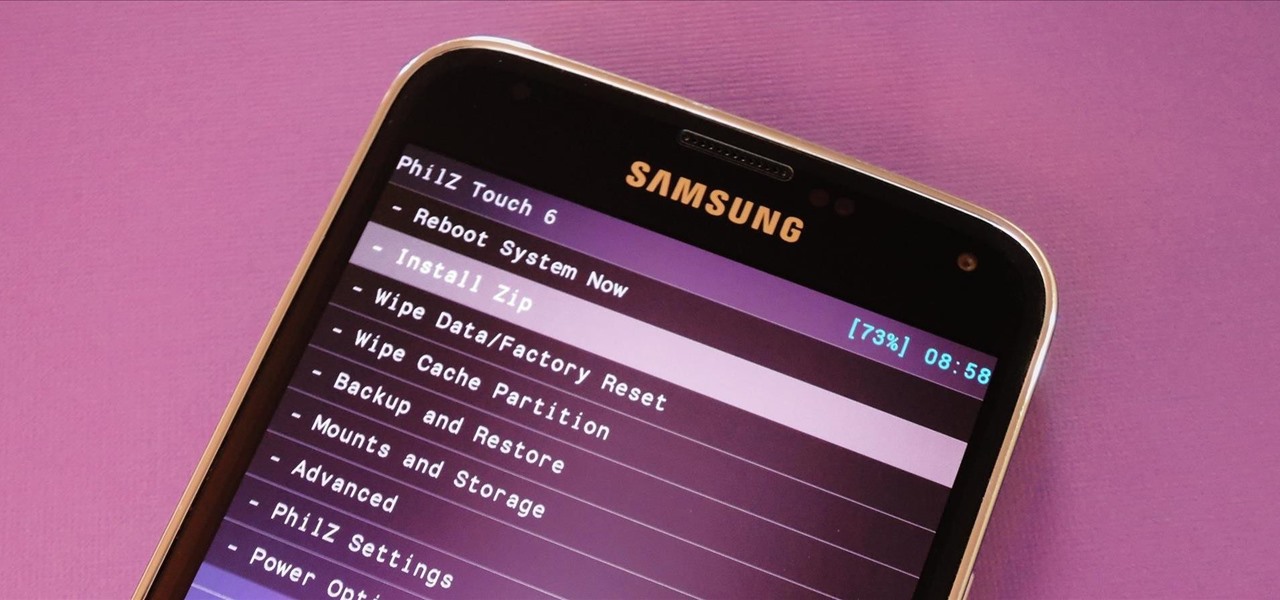
With Safestrap bringing custom recovery functionality to the AT&T and Verizon Wireless variants of the Samsung Galaxy S5, it's high time we covered this process for all other versions of the GS5.

You've been there. Those precarious few seconds between dropping your expensive smartphone right on its face and reaching down to survey the damage. Or maybe you got thrown in a pool while your device was in your pocket, or you dropped that sucker right into the toilet bowl. Heck, I've managed to accidentally wash two devices by leaving them in my pants pocket when throwing in a load of laundry.

It was only a matter of time before the apps from the new Samsung Galaxy S5 leaked for everyone to download and install, and today we've got one that takes advantage of the IR blaster on your Galaxy Note 3.

The launch of Android 4.4 KitKat alongside the Nexus 5 was met with much fanfare from Android enthusiasts. Unfortunately, if you don't have a Nexus device or are still awaiting the 4.4 update, you may feel a bit left behind.

Welcome back, my budding hackers! One of the keys to becoming a professional and successful hacker is to think creatively. There is always a way to get into any network or system, if you think creatively. In previous tutorials, I have demonstrated ways to crack passwords on both Linux and Windows systems, but in this case, I will show you a way to get the sysadmin password by intercepting it from a Remote Desktop session.

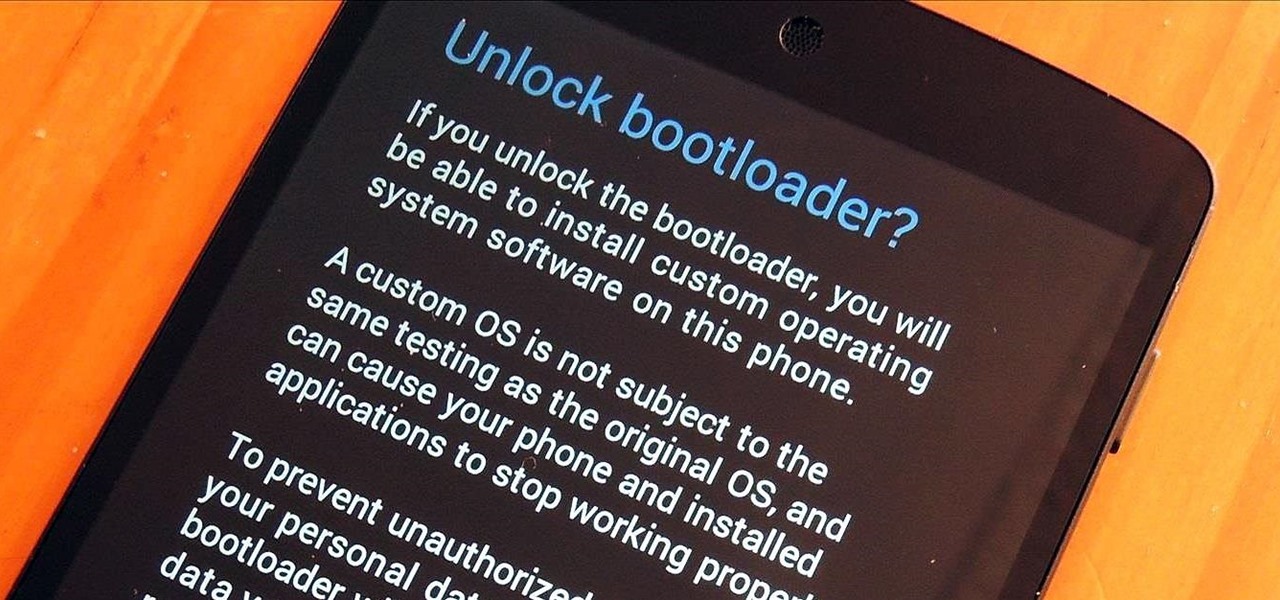
You know what's awesome? You own a Nexus. That means, with Google's blessing, you have easier access and control over your device than other manufacturers allow. You can really dig in and do some interesting things if you root.

Welcome back, my fledgling hackers! In the first part of my series on Wi-Fi hacking, we discussed the basic terms and technologies associated with Wi-Fi. Now that you have a firm grip on what Wi-Fi is exactly and how it works, we can start diving into more advance topics on how to hack Wi-Fi.

An internet connection has become a basic necessity in our modern lives. Wireless hotspots (commonly known as Wi-Fi) can be found everywhere!

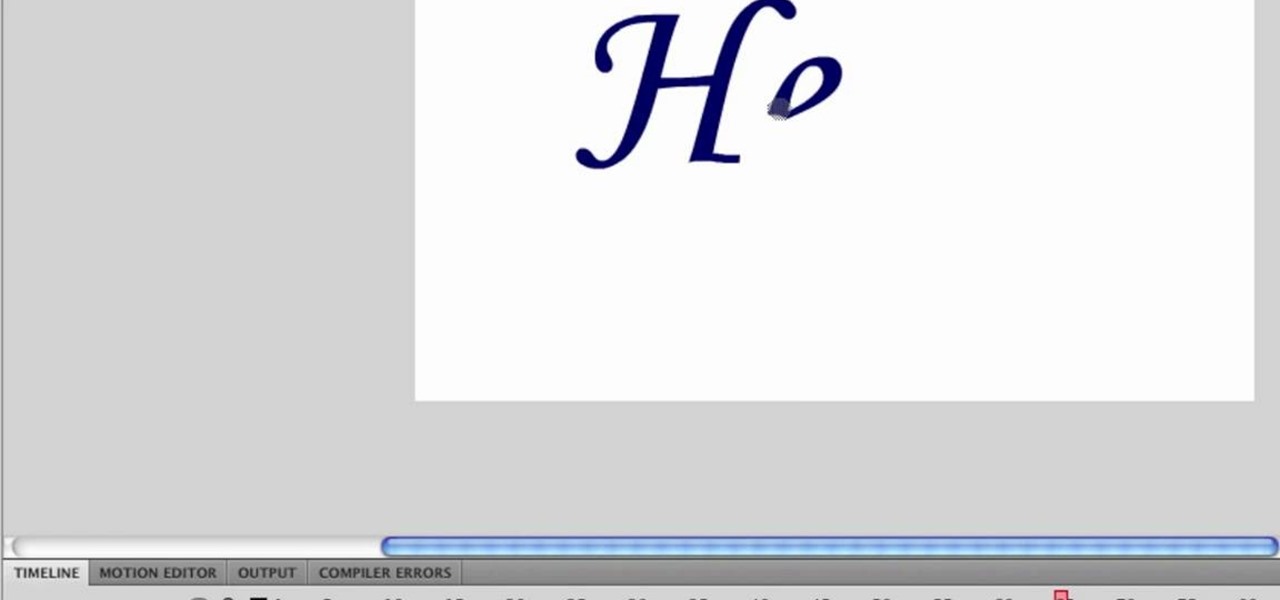
First type your word and set the font. Now select the word and break it apart by pressing the ctrl+B twice. Now select the erasing tool and erase the letters in reverse order like when you write that word, you write it in a order but you need to erase it just reversal of it as you can see in the video. Now press the F6 button, it will create a keyframe, select

What is it about Parisian women that makes them so effortlessly chic and timelessly beautiful? Whether we're talking about Charlotte Gainsbourg, AKA Jane Birkin's daughter, or an older lady like Juliette Binoche, Parisian women really take it easy when it comes to applying makeup, emphasizing skincare instead. And they look gorgeous doing it.

Boxing a table doesn't mean getting into the ring, but it does require a certain degree of skill to successfully complete. Boxing the tablecloth is a great technique for any occasion or party, and every caterer should know these moves.

It's amazing what you can create with a few, everyday household and office supplies. Most of these items are already sitting in your junk drawers, so there's no need to spend money! Kipkay shows you 4 awesome hacks you can make in this "household hack pack" video.

In this how to video, you will learn how to use the fawn feeding bleat. This is very effective for bow hunters. The call is easy to use. The key is when you make the sound, make it low and desperate. The fawn is hungry and calling to a doe to be fed. Make sure there is a sense of concern to it. Cuff it to create resonance when you make the call. You can make two or three of these calls. Hesitate for ten to fifteen minutes before making the call again. A doe should respond to feed the fawn. A ...

If you want to learn how to play Eleanor Rigby by the Beatles on the ukulele in key g this might be for you. There are only two chords with some variations throughout this song. The first chord you need to play is B minor. The B minor chord consists of a bar on the second fret on the bottom 3 strings and the fourth fret on the fourth string. The next chord in the progression is B minor7. To play B minor7 use the formation for the B chord; however, in this variation you must put your finger on...

Ukulele Mike shows his viewers how simple it can be to play "Oh, Susannah" on the ukulele. According to Mike, "Oh, Susannah" is an old classic story song. This means that it is a song that has been handed down that tells a story and doesn't just throw words together because they sound nice.

In this how-to video, you will learn how to fertilize and deadhead roses. Late summer fertilization is okay for these roses. Make sure to water them in well, as this is key. Deadheading in late summer will give you a fall bloom cycle with the roses. Deadheading will mean cutting off dead blooms. Hips are dead blooms that have fertilized. These make seeds and some are either sterile or will actually grow. To properly deadhead, go down to the second or third five-leaf. Cut at a 45 degree angle ...

ZurplusFaction shows viewers how to pick a lock easily using 2 paper clips. First, you need to take your first paper clip and fold one end out. Fold it out again and straighten this out. Next, take the folded out in and fold in again so it forms boomerang shape with the paper clip. Now, take your pliers and squeeze this folded part together tightly. With a bigger paperclip, and use wire cutters to cut of a straight piece of the paper clip with a curve at the top. Now, you are ready to pick yo...

Begin playing the first measure in Claude Debussy's "Clair de lune" masterpiece. This song has stood the test of time, and influenced musicians around the world. This makes it a really good piece to begin learning piano with. This video covers Measure 1.

This video on typhoon preparedness comes from Andersen Air Force Base in Guam, where typhoons are common. The key to surviving a typhoon or other disaster is preparation. Stock up on enough food and supplies to last your family for about a week. Routinely check expiration dates on food, water and batteries and rotate your stock. Be sure window screens are in place and in good condition in the event the power is off for several days.

This video shows you how to draw a dog house in Adobe Illustrator. In this video, first the scale is selected, and with the help of a air brush tool, a square is being made as a front of the house, then a top is drawn and then the back. Then the entrance is drawn. This is done by selecting this object, then select the paint bucket tool, select color and then this object is filled with color. Then secondly, using marquee tool, two large spots are made in the middle of the door object to make i...

There are a variety of substances that you can use to clean your LCD screen. The one thing you don't want to use is anything that has alcohol in it. Alcohol will damage your LCD. Any LCD cleaning liquid will work to safely clean your LCD. It is also good to use a microfiber cloth also so that they don't put any scratches in the screen. You should never use napkins, paper towels, or Kleenex. The primary ingredient in most LCD cleaners is water. The key is that they remove the impurities and ch...

The video explains how to hack the game Agony: The portal. First he clicked the start game and created new character by entering the name as test dummy and set the difficulty level as normal. The he clicked the start campaign. While entering the game he skipped the tutorial and directly he went into the game.