Most ab workouts target your upper abdominals only. Sit ups and crunches, for instance, only work on that upper part of your abs without even touching the lower portion, where most of us have muffin tops and really need the work.

Google is the biggest and best search engine on Earth, and if you are a webmaster and want your website to be a big success it would really behoove you to know as much about how it works as possible. The Google Webmasters series of videos and website were created to teach webmasters, SEO professionals, and others how Google works by answering their questions and giving them insights into how they can best integrate and utilize Google's functionality to improve their business. This video will ...

Have you ever wondered what it would taste and feel like to take a bit fat bite out of a supersized Twix bar? No, we're not talking about the King Size Twix bars you can get at Target. We're talking a goddamn cake-sized Twix bar.

The arms are the part of the body most used by Westerners in fighting. As a result, targeting and disabling an opponents arms is a great way to end a fight quickly without the risk involved in hitting an opponent's head. This three-part video details pressure points all over the arms and various ways of striking them in order to hurt and disable your opponent, ending your engagement with limited damage to both yourself and them.

A poker face is sharp, beautiful, and intimidating, giving your target a peak at the cow without giving away the milk. Bring out your inner card-dealing bovine by watching this professional makeup tutorial by makeup artist Reiva Cruze.

Need to color correct your photos and you're not sure how? In this video, the basics of RGB and CMYK colors are discussed as well as how to use them to color correct everything from everyday snapshots to portrait photographs. By using the eyedropper and the info palette to read the colors in the photos, you can then color correct. Based on the CMYK read out of the color sample targets, you can then adjust the color channels using a curves adjustment to achieve the kind of colors you'd like. A...

First, you have to lay down your net and bundle up the rope in one hand like an extension cord all the way up to the net. Hold the net in the same hand, and grasp the rim of the net with the other hand. When you want to throw the net, grab the net midway with the rim in the other hand, and throw it towards your target with some spin, so the net lands flat on the water. If the net landed properly, it should sink slowly to the bottom, trapping some fish underneath it. To retract the net, simply...

In this video tutorial, viewers learn how to perform a sumo squat. It is the same as a regular squat, except the legs are extended more wider. The bar should be setup a little bit below your shoulder level. Go into a split stance when picking up the bar. Keep your core muscles tight and keep the bar stabilized. Spread the legs wide, pass the shoulder width. This exercise target the leg muscles and helps strengthen them. Inhale when going up and exhale when going down. This video will benefit ...

In this video tutorial, viewers learn how to perform the Siva count sleight card trick. This sleight card trick is very similar to the Elmsley, except it is a reversal. It reveals the cards instead of facing them down. This sleight uses 5 cards, but only reveal 4 of them. It hides the target card. The card that you want to hide needs to be in he middle (3rd card). When going through each card, users have to double drop the card and not allow the spectator to see the hidden card. This video wi...

A lot of the available shooting benches on the market today are well-made, but it's really hard to find one that you're completely comfortable with. That's why it's best to make your own custom shooting bench, made especially for you, how you want it.

Samba can be configured to allow any user with write access the ability to create a link to the root filesystem. Once an attacker has this level of access, it's only a matter of time before the system gets owned. Although this configuration isn't that common in the wild, it does happen, and Metasploit has a module to easily exploit this security flaw.

Apple's Gatekeeper security software for macOS (Mac OS X) is vulnerable to remote attacks up to version 10.14.5. An attacker that's anywhere in the world can exploit MacBooks and other Mac computers by sharing a single ZIP file.

With an inconspicuous Android phone and USB flash drive, an attacker can compromise a Windows 10 computer in less than 15 seconds. Once a root shell has been established, long-term persistence to the backdoor can be configured with just two simple commands — all while bypassing antivirus software and Windows Defender.

Many apps, including Facebook, Twitter, and Facebook, do not let you download videos, even if they are living on your own account. Saving these videos usually requires a third-party app or screen recorder, which is inconvenient and can result in loss of quality. However, TikTok, the newish popular short-form video platform, makes it easy to download videos — even if they're not yours.

Many online users worry about their accounts being breached by some master hacker, but the more likely scenario is falling victim to a bot written to use leaked passwords in data breaches from companies like LinkedIn, MySpace, and Tumblr. For instance, a tool called H8mail can search through over 1 billion leaked credentials to discover passwords that might still be in use today.

Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.

Most companies have services like employee login portals, internal-only subdomains, and test servers they would prefer to keep private. Red teams and white hat hackers can find these obscure and often vulnerable services using a tool designed to help protect users from fraudulent certificates.

After backdooring a MacBook not protected by FileVault or using a fake PDF to gain remote access, an attacker may wish to upgrade their Netcat shell to something more fully featured. While a root shell allows attackers to remotely modify most files on the MacBook, Empire features some useful post-exploitation modules which make hacking Macs very easy.

Traditional subdomain enumeration techniques create a lot of noise on the target server and may alert intrusion detection systems to an attacker's intentions. For a stealthier approach, there's a tool with the capability of finding hundreds of subdomains related to the target website without alarming the server administrators.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

During a penetration test, one of the most important aspects of engaging a target is information gathering. The more information you have coming into an attack, the more likely the attack is to succeed. In this article, I'll be looking at SpiderFoot, a modular cross-platform OSINT (open-source intelligence) gathering tool.

So cute, so furry, and so chock full of parasites. While raccoons are fun to watch, they are neither friendly nor clean — and they can make you sick in more ways than one.

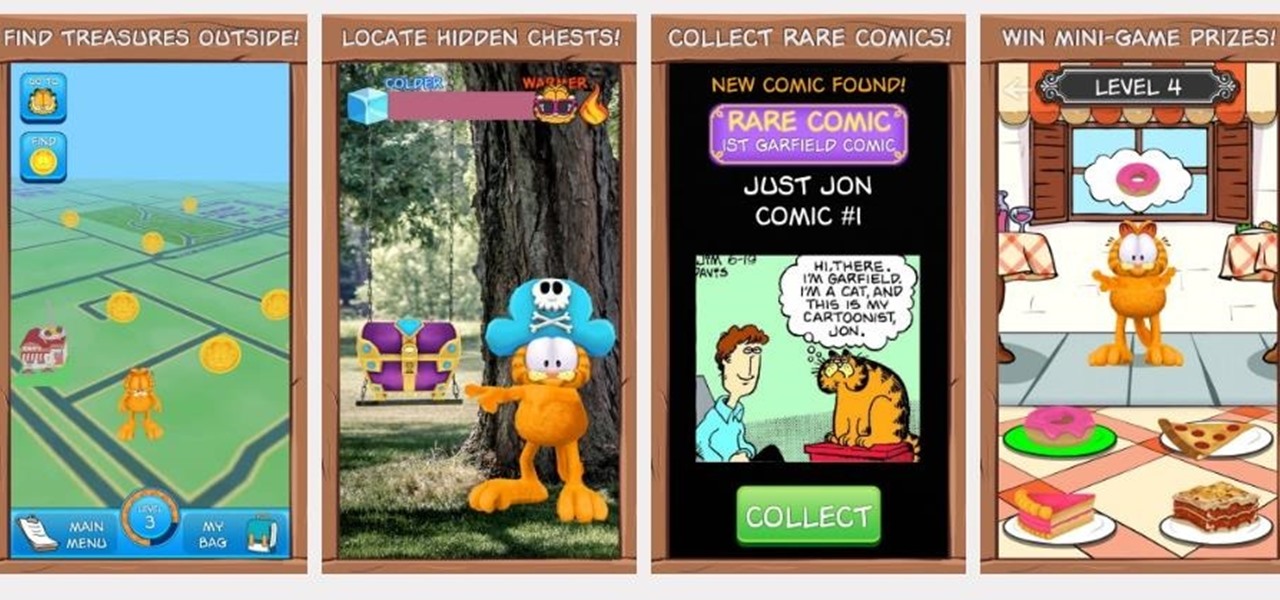
If imitation is the sincerest form of flattery, then Niantic must be blushing constantly, as numerous copies of Pokémon GO have spawned over the past year or so, seeking to capture the same success, often adding the lure of tangible prizes from brand partnerships.

Snapchat is rolling out some awesome new features in their update today. The major update comes just two weeks after the company's premiere of backdrop, snap shopping, and voice clip features. They rolled out two new features this time, Multi-Snaps and the Tint Brush.

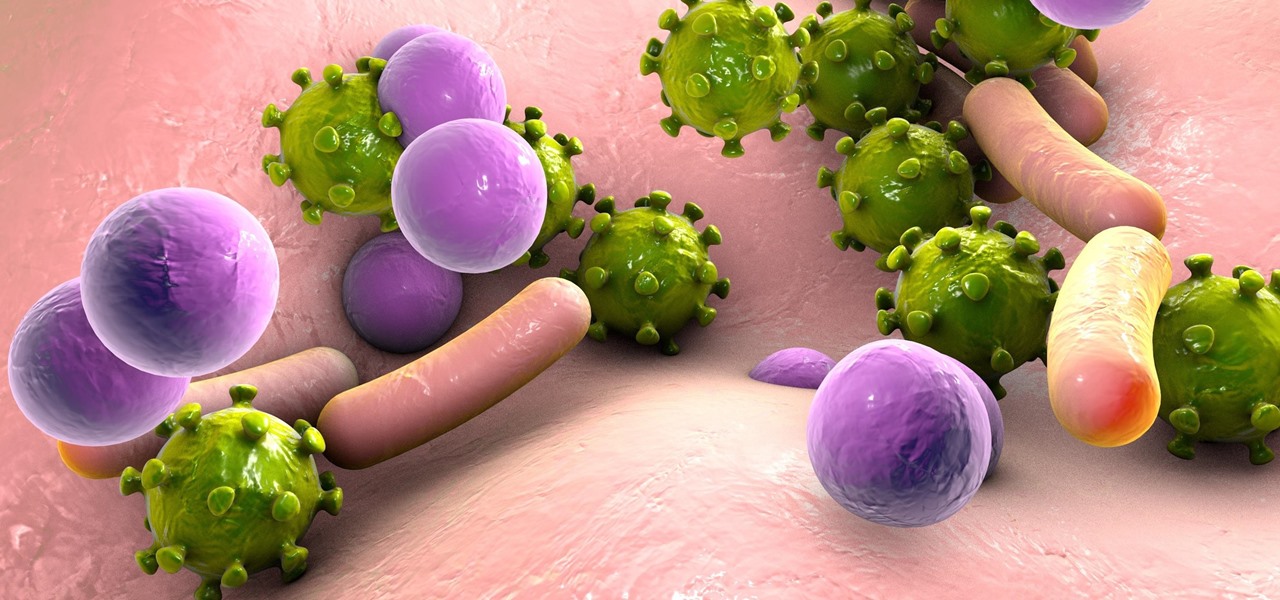
A new study just out reveals that HIV takes hold in the human body with the help of cells that usually work to heal, not kill.

Welcome back, my greenhorn hackers! A few years back, Microsoft implicitly recognized the superiority of the Linux terminal over the GUI-based operating system by developing PowerShell. Since Windows 7, every Windows operating system has had PowerShell installed by default, and they even made PowerShell capable of running Linux commands on Windows!

Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photography, payment services, and so on.

When attempting to compromise a target, we want as much control as possible over the victim. Metasploit's meterpreter allows us to have immense control over the victim, the only issue is that sometimes we can't land a meterpreter. We may only be able to land a standard shell, but fear not, there is a way to upgrade our shell into the all powerful meterpreter!

As we're all aware, recon is vital to a successful hack. We need to know everything we can about the target in order to perform the best possible attack. Port scanning is a basic recon concept that is introduced very early in learning proper reconnoissance. The issue with port scanning is that is makes a lot of noise. Every connection to every port will be logged. This is where stealth scanning comes in. Also known as SYN or half-open scanning, stealth port scanning is a bit quieter, and is l...

Welcome back, my novice hackers! In my series on cracking passwords, I began by showing off some basic password-cracking principles; developed an efficient password-cracking strategy; demonstrated how to use Hashcat, one of the most powerful password-cracking programs; and showed how to create a custom wordlist using Crunch. In this tutorial, I will show you how to create a custom wordlist based upon the industry or business of the targets using CeWL.

Welcome back, my rookie hackers! I recently began a series on using Metasploit, and my goal with it is to teach you the very basics the incredibly powerful hacking tool has to offer while progressively moving on to the more advanced features.

When it's most important for me to browse the web incognito, I always seem to forget to enable private browsing. If that sounds like you, it's time you stop making that mistake for good. Manually deleting the cache and browser history is a thing of the past, and as it turns out, so is manually switching to incognito mode.

Welcome back, my novice hackers! I have tried to emphasize throughout this "Hack Like a Pro" series that good reconnaissance is critical to effective hacking. As you have seen in many of these hacks, the techniques that we use are VERY specific to the:

Welcome back, my budding hackers! One of the keys to becoming a professional and successful hacker is to think creatively. There is always a way to get into any network or system, if you think creatively. In previous tutorials, I have demonstrated ways to crack passwords on both Linux and Windows systems, but in this case, I will show you a way to get the sysadmin password by intercepting it from a Remote Desktop session.

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

Welcome back, my budding hackers! One of the most time-consuming, but necessary, activities in hacking is reconnaissance. Before we can hack a system, we need to know what operating system it's running, what ports are open, what services are running, and hopefully, what applications are installed and running.

Do you ever wonder how all these celebrities continue to have their private photos spread all over the internet? While celebrities' phones and computers are forever vulnerable to attacks, the common folk must also be wary. No matter how careful you think you were went you sent those "candid" photos to your ex, with a little effort and access to public information, your pictures can be snagged, too. Here's how.

In today's world of social media, there's really only two powerhouses—Facebook and Twitter. And those of you with Twitter accounts know the power of a Tweet. Getting more followers means reaching more people, but the vast majority of Tweeters are following only a handful of Twitterers themselves. Do you ever wonder why them? What's so special about these selected followed users? Is it worth it to follow them, too? That's up to you, but if you're searching for more people to follow, then it's ...

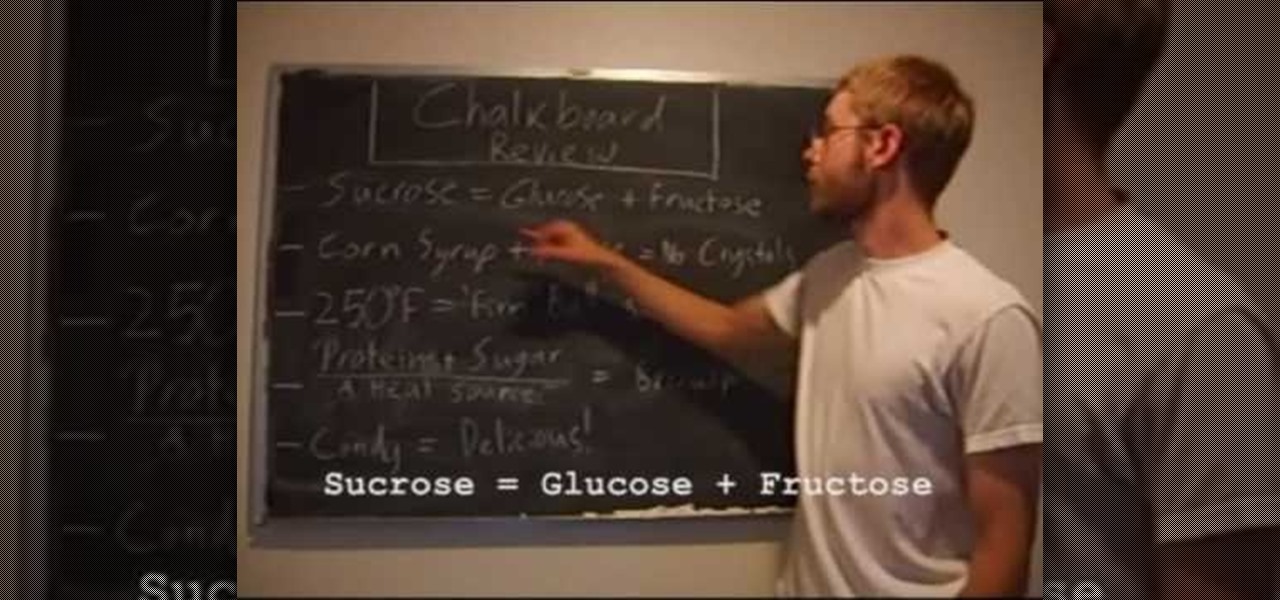
In this tutorial, we learn how to make caramel candies. Ingredients include: 1 cup granulated sugar, 1/4 c light corn syrup, 4 tbsp salted butter, 1 c heavy cream, and 1 tsp vanilla. To create this, you will combine all your ingredients in a large pot, stirring a little bit. Once the mixture has turned into caramel, stick a thermometer to make sure it's reached 250 degrees. When it is finished, pour this into a baking dish. Once you do this, smooth it out to cover the surface, then wait for i...