Ready to edit your footage in Windows Live Movie Maker? First, you'll need to move the individual clips from your camera to your computer. This installment in Vimeo's excellent Video 101 series of covers all of the basics—connecting your camera, copying the files over and, finally, importing them into your video editor of choice.

Enhance your visual skills and demonstrate your manual dexterity as a magician by incorporating the "Synapse" card fluorish by Ayres into your repertoire. Playing card fluorishes are typically performed as part of larger magic performances and can also be shown on their own as individual exhibitions of skill.

Isolation is an important part of hip-hop dancing. It involves moving individual parts of your body without moving the rest, either quickly or slowly depending on the dance. This video will show you some ways that you can use isolation to improve your dancing and get better moves.

If you have a circular or semicircular protractor like the one used in this video, making a pie chart is as easy as – well — pie. This will teach you how to use your protractor to measure out each individual slice in your pie chart. Learn how to visualize statistical data through hand-drawn pie charts with this free video math lesson.

This video tutorial from Foreclosureresearch presents how to burn video files to a playable DVD using DVD Flick application.First you need to download and install free software called DVD Flick.You can find it at DVD Flick.Once it's installed, run the program. First thing to do is to set your Project Settings. Click Project Settings from top menu. From Project Settings window you can name the project, select Target size (size of your DVD), Encoder, Thread count, DVD format, bitrate, playback ...

Fantasize about role playing? One of the most popular venues for role playing medieval fantasy is the board game, Dungeons and Dragons. Get a group of three or four together and have a blast!

Check out this video tutorial to show you how to use a Marantz digital audio recorder. This video was made by the equipment room at CUNY Journalism School in New York.

A below elbow arm amputee shows how to open bottles one handed, without a prosthetic device. This technique is also great for people with arthritis pain, cerebral palsy, weak joints, stroke, and people who want to be ready for the worst-case-scenario that they suddenly have only one free hand and have to dismantle a bomb that is hidden inside a bottle! This is a great tutorial for handicapped, disabled or individuals that have lost a limb to amputation.

The oyster stitch is an isolated stitch. It is a combination stitch using the twisted detached chain stitch which is "surrounded" by an "open" chain stitch, or even a fly stitch. The oyster stitch makes a filled oval shape, suitable for flower petals or individual buds and accents. Watch this video from Needle 'n Thread to see how it's done.

In Jiu Jitsu the standard goose neck wrist lock may not work of very stong individuals. That means that your level of force must go up in order to deal with the increased resistance.

Childcareland demonstrates how to make a Thanksgiving book of thanks with kids in this video. A book of thanks can be done by a group or an individual. It begins a title page which can be labeled to reflect whether it is an individual book called "My Book of Thanks" or an group book called "Our Book of Thanks" or a general book called "Book of Thanks". The back page is a blank match of the cover page. In the middle are five pages labeled "I'm thankful for" with a line for older children to wr...

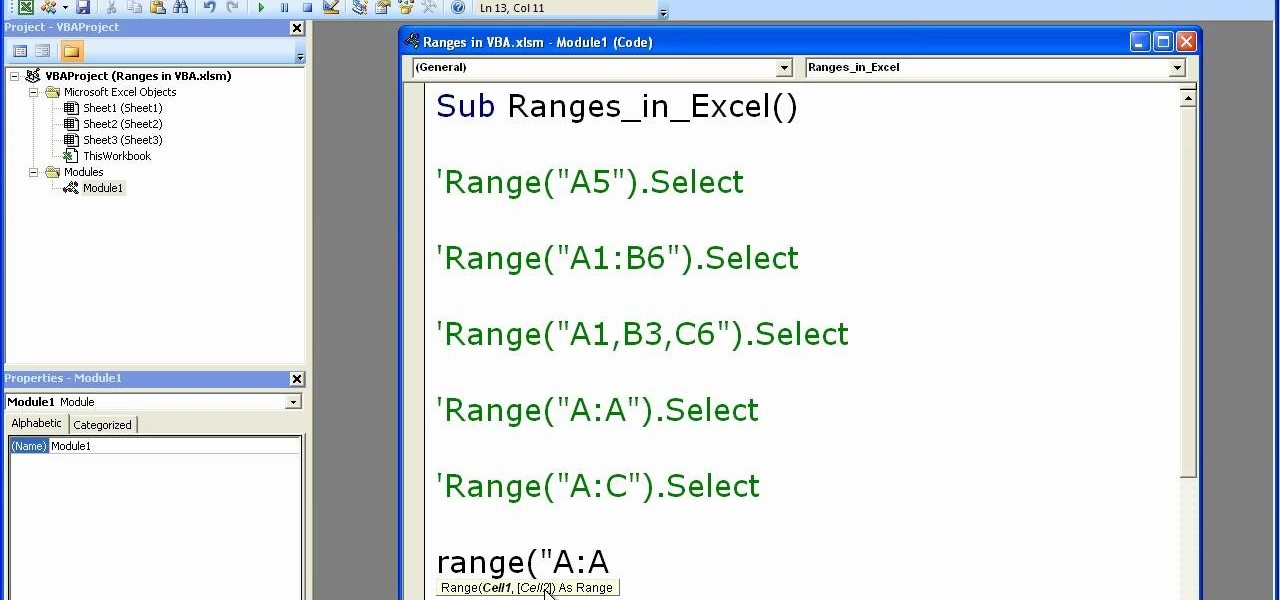
Microsoft excel is a powerful tool used to work with numbers and data by filling them down in rows and columns of a table. Excels also supports macros, which are small scripts to automate certain functions. In Microsoft Excel you can select entire rows and columns using the range property. You can also use macros to select individual rows and columns as well as multiple variations of rows, columns, and individual cells all at once. In Excel a horizontal line of data is called as row and a ver...

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

Featured on MTV's Catfish TV series, in season 7, episode 8, Grabify is a tracking link generator that makes it easy to catch an online catfish in a lie. With the ability to identify the IP address, location, make, and model of any device that opens on a cleverly disguised tracking link, Grabify can even identify information leaked from behind a VPN.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

The macOS 10.14 security update tried to make parts of the operating system difficult for hackers to access. Let's take a closer look at how its new feature works and what we can do to spoof the origin of an application attempting to access protected data.

Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

There's now more reasons to make sick workers stay home—a new game theory study suggests adequate hand washing and other illness-aversion tactics aren't as useful as we thought to keep you from getting infected when a virus or bacteria is circulating.

Welcome back, my fledgling hackers! As nearly everyone has heard, Target Corporation, one of the largest retailers in the U.S. and Canada, was hacked late last year and potentially 100 million credit cards have been compromised. Happening just before Christmas, it severely dampened Target's Christmas sales, reputation, and stock price (the company's value has fallen by $5B).

In Studio One, you can drag and drop workflow. Open a song in Studio One. Here, you can isolate particular instruments. Alt + click, will allow you to isolate. You can search a list of plug-ins in the mixer or press F7 to open the effects browser. You can also drag and drop the gate onto a mix.

In this video tutorial, viewers learn how to build a movie from individual clips in iMovie. Using clips in iMovie will easily allow users to create a movie. On the right side of the screen in iMovie, there will be a library of all the clips and images that you have imported. Click on the Clips Viewer to arrange the clips in an order that you would like. Just drag them to the clip viewer. You can change the position by dragging a clip over another. Click on the time line viewer to see how long...

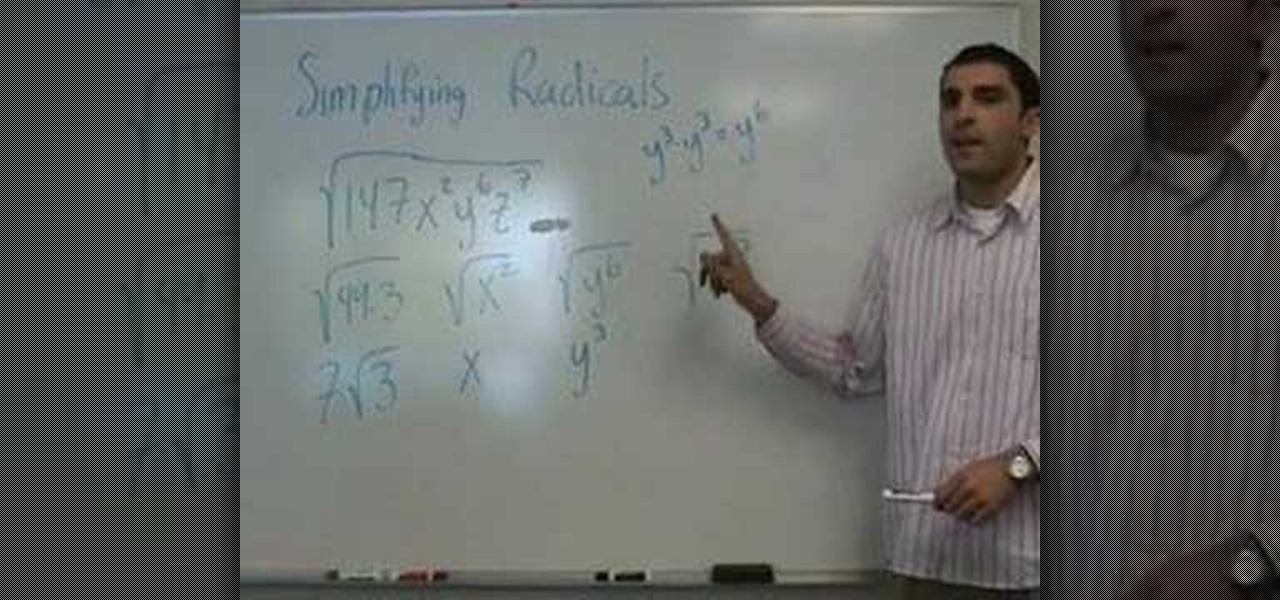
In this video the instructor shows who to simplify radicals. If you have a term inside a square root the first thing you need to do is try to factorize it. First factorize the numerical term. Write down the numerical terms as a product of any perfect squares. Now split the original radical expression in the form of individual terms of different variables. Now you can pull out the perfect square numerical factors out of the radical. Similarly for the variable terms write the variables as power...

In this video the instructor shows how to graph a piecewise defined function. A piecewise defined function is a function that is defined in separate pieces. In these kind of functions, for different ranges of the value of x, you are given different small functions, all of which together make the whole function. This means your equation of the function is given in the form of smaller functions. Now to graph these kind of equations all you have to do is graph the individual equations in the sam...

Learn to cook like a professional chef from the comfort of your own home with this fun and entertaining video on creating individual meringue shells. Don't throw away your money by buying store bought finished products and create this tasty treat at home. Beat together all your ingredients as outlined in the step by step video, pop them in the oven, top with your favorite fruit and whipped or lemon cream and you're ready to eat. You're friends will think you spent hours on these delicious des...

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you to select targets in range and let the script choose the best strategy for each network.

This year's holiday shopping season is shaping up to be fertile ground for augmented reality to show its worth, as both Walmart and Target have crafted immersive experiences designed to engage shoppers in the coming weeks.

If you need to hack an Android device, try a remote administration tool. Known more familiarly as a RAT, there are open-source RATs that are barebones and exorbitantly priced RATs that are more polished. There are also low-cost and polished RATs that aren't intended to be RATs at all, such as Cerberus, an anti-theft solution available right on Google Play.

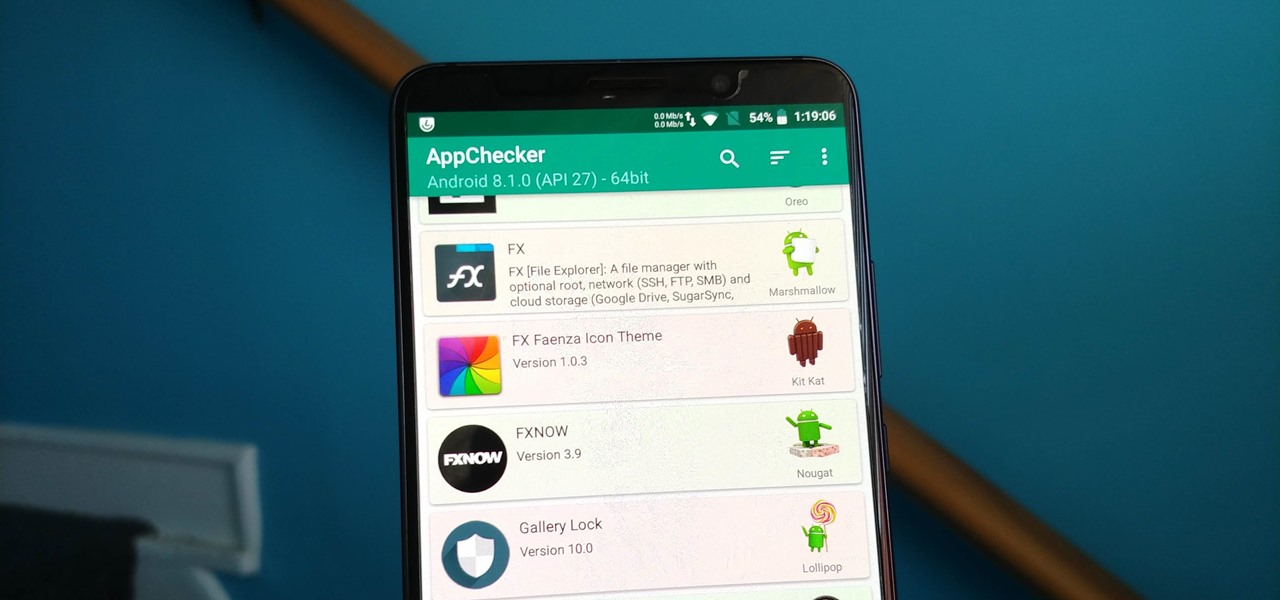
On August 1, Google Play started requiring new app submissions to target at least Android 8.0 Oreo's API. Then, as of November 1, all updates to existing apps were required target the same API. While at first glance, this change may mean little to you, it will have a profound impact on Android. Now, your favorite apps will be getting better.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

After Vuzix's scorching hot week at CES, the future of AR is so bright, we have to wear (smart) shades. Luckily, Vuzix is making it easier for consumers to grab a pair.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Looking for a way to speed up the boot time on your favorite programs in Windows? This video will show you a little tweak to make your most-used applications start up in no time. Basically, you just go to the "Shortcut" tab in the program's properties menu. Then add " /prefetch:1" to the end of the target location in the "Target" box. This tweak works on PCs running Windows 7, XP or Vista.

In this Pets & Animals video tutorial you will learn how to train your dog to perform the "cop-cop" trick. In this trick the dog learns to put its feet on your feet. Step 1 – teach the dog to target a book or a mat with their feet by offering them some treat. You can do this either by appreciating or clicking when both the feet touch the book. The next step is getting the dog to target the book with their feet while they are between your legs. You have to continually reinforce the dog to ma...

Looking to work on your form? Try this free video golfing lesson for size. In short: When putting, to be able to release the putter down the line to your target, the club must travel slightly inside the target line. For a complete overview of how to become a better putter, watch this video guide.

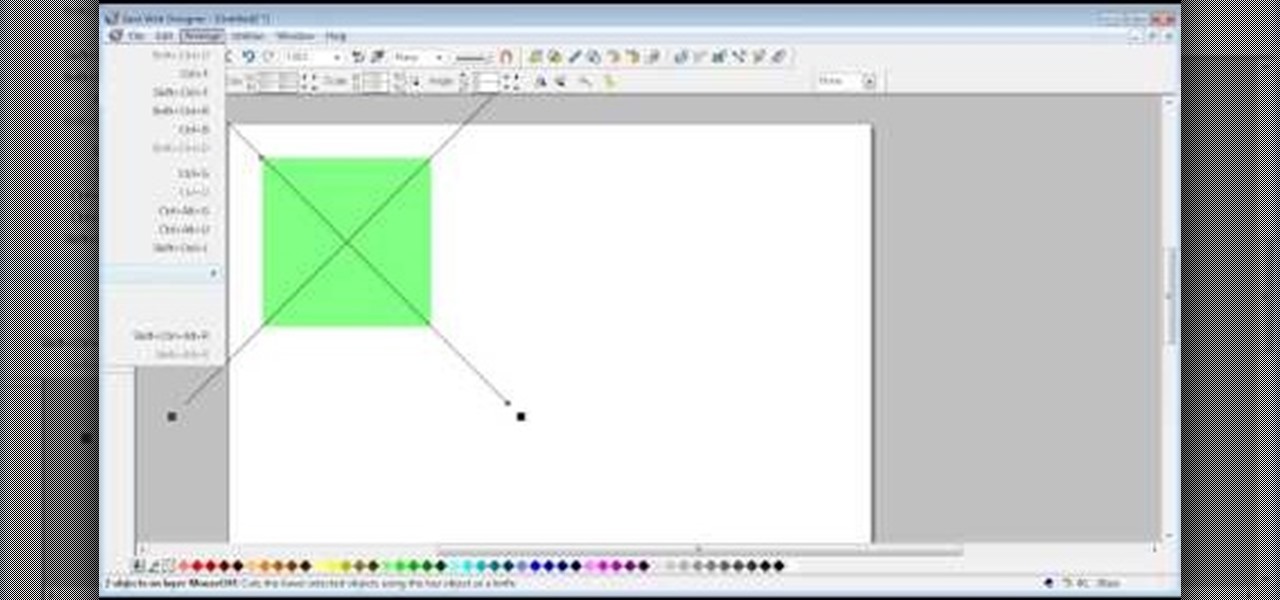
The video shows us how to create bevels in Xara web designer. Firstly using the rectangle tool hold down the Ctrl key to create a square. The problem with the Xara web designer is that it hasn't got a convert to edit the shape features which actually means that you cant select individual nodes with the shape editor tool which may create some other line. However you can select individual nodes by going to arrange/combine shapes/add shapes with selecting the rectangle. And by doing changes the ...

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

Gmail conversations, Facebook private messages, and personal photos can all be viewed by a hacker who has backdoor access to a target's Mac. By livestreaming the desktop or exfiltrating screenshots, this information can be used for blackmail and targeted social engineering attacks to further compromise the mark.

Consumers are chomping at the bit for augmented reality smartglasses from Cupertino's finest, but one market analyst is saying not so fast, Apple fans. Meanwhile, automotive AR is gaining speed, with the latest milestone coming courtesy of a major investment in waveguides by Continental. And although mobile AR apps have already arrived, retailer Target is taking a different approach. So why is Target tinkering with web-based AR? Answers below...

Dating websites allow you to see a person in a very intimate context, framing their successes and accomplishments in life to an important audience. The information contained in these profiles often can't be found elsewhere, offering a unique look into the personal life of the user.