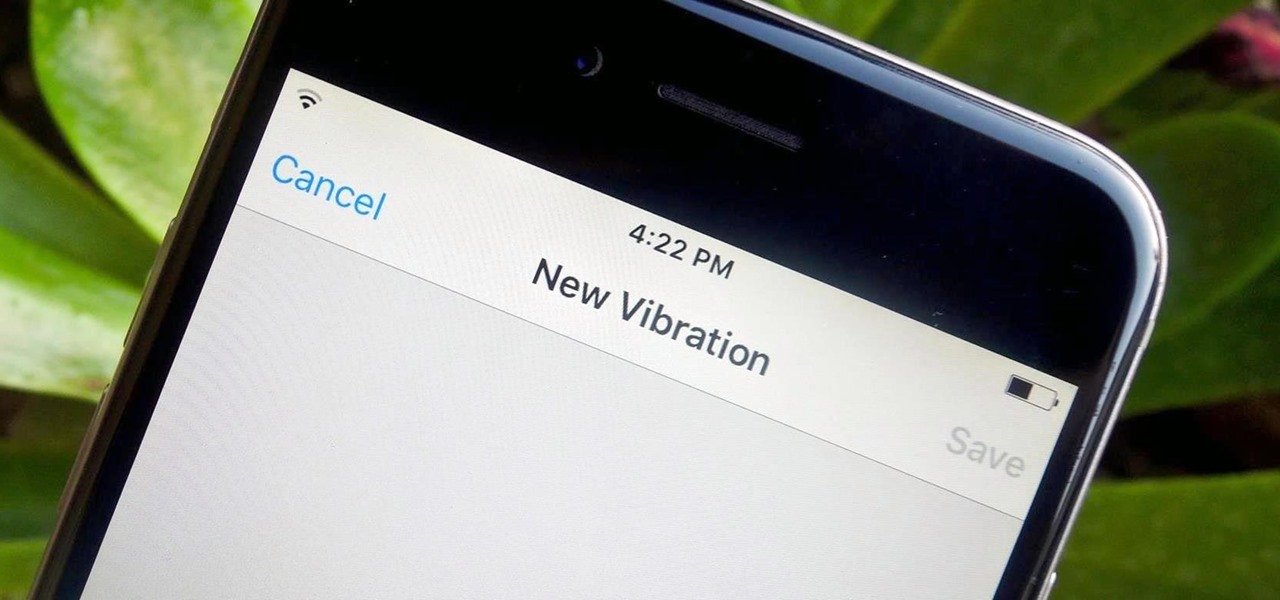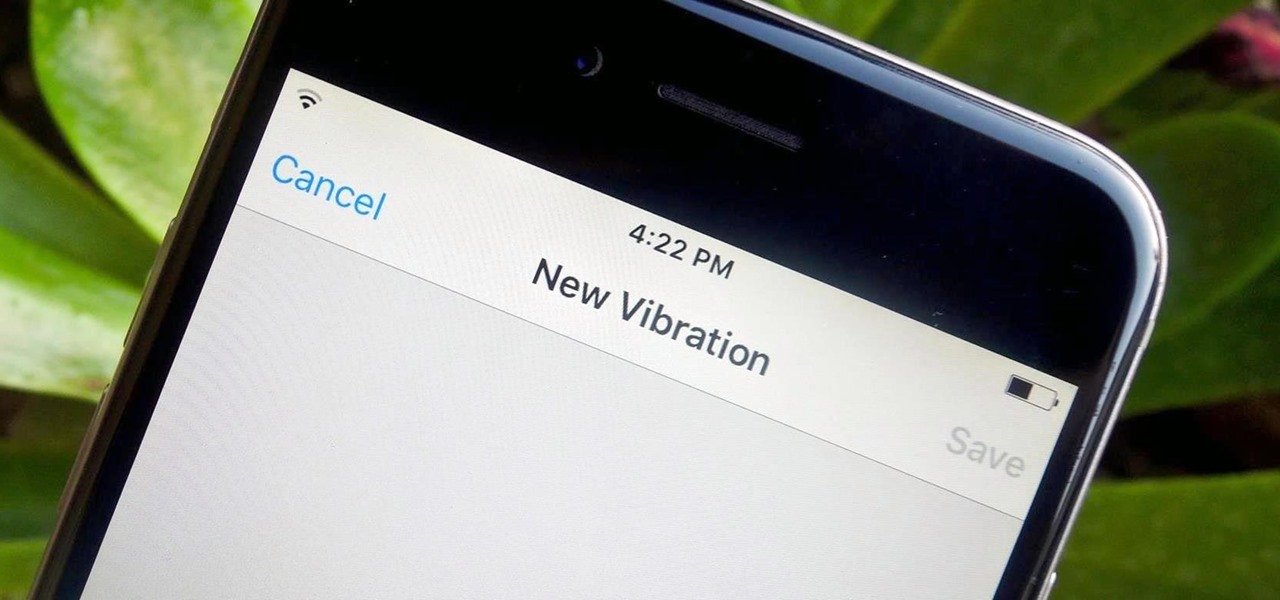
Certain contacts on my iPhone have special ringtones so that I know exactly who's calling or texting without looking at my screen (like Adele's "Hello" for all my exes). But when my phone is silenced and tucked away in my pocket, these contact-specific ringtones can't really help me out. Luckily, there's something else that can—custom vibration patterns.

YouTube, the popular video streaming website owned by Google, announced on October 21st that it will be launching a new subscription service titled "YouTube Red" for $9.99 a month. Under the membership, subscribers will be able to watch videos without ads. Yup, all videos—from music to trailers to gaming and everything in-between—completely ad-free. Additionally, individuals can save videos to watch offline on their mobile devices as well as play videos in the background.

Your brain holds a lot of precious information and is capable of great feats. However, there's one quality that doesn't lie among its strengths—memory security. Yes, that's right, your brain can be hacked, and it doesn't take a psychologist to do it. Anyone with the right know-how can change your memories for their own personal benefit, and you can do so to others, too.

Ant-Man isn't one of the most famous Marvel superheroes. In fact, with the news of his individual movie came great doubt that the comic book legends could succeed in telling the tiny story of an oddball hero on the big screen. Yet with its humor and unique story, Ant-Man has become a hit movie in its own right—and the hero will most certainly make a hit Halloween costume.

If your iPhone can't last a full day without being recharged multiple times, something's wrong—but it might just be working harder than it needs to.
Welcome back Hackers\Newbies!

Welcome back, rookie hackers! We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).

In recent weeks, major bank websites around the world have experienced outages after being have been hit with Distributed Denial of Service (DDoS) attacks. Although few, if any, of these banks have been totally knocked offline, these DoS attacks have dramatically slowed the response time of their websites to legitimate customers. The most recent victim was the Royal Bank of Scotland. Due to this attack, RBS customers were unable to access their accounts for about an hour last week.

Linux and Mac users have long enjoyed the use of multiple virtual desktops to free up clutter on their home screen and keep individual workflow environments separated, but Windows users have always been stuck with one solitary desktop.

Sometimes just drinking your alcohol can feel a little dull and boring. Eating your alcohol, however, is always a party.
Hello I have now asked for help a few times, so I figured I should contribute with what I can offer as of right now, which is many valuable sites if you need to look someone up.

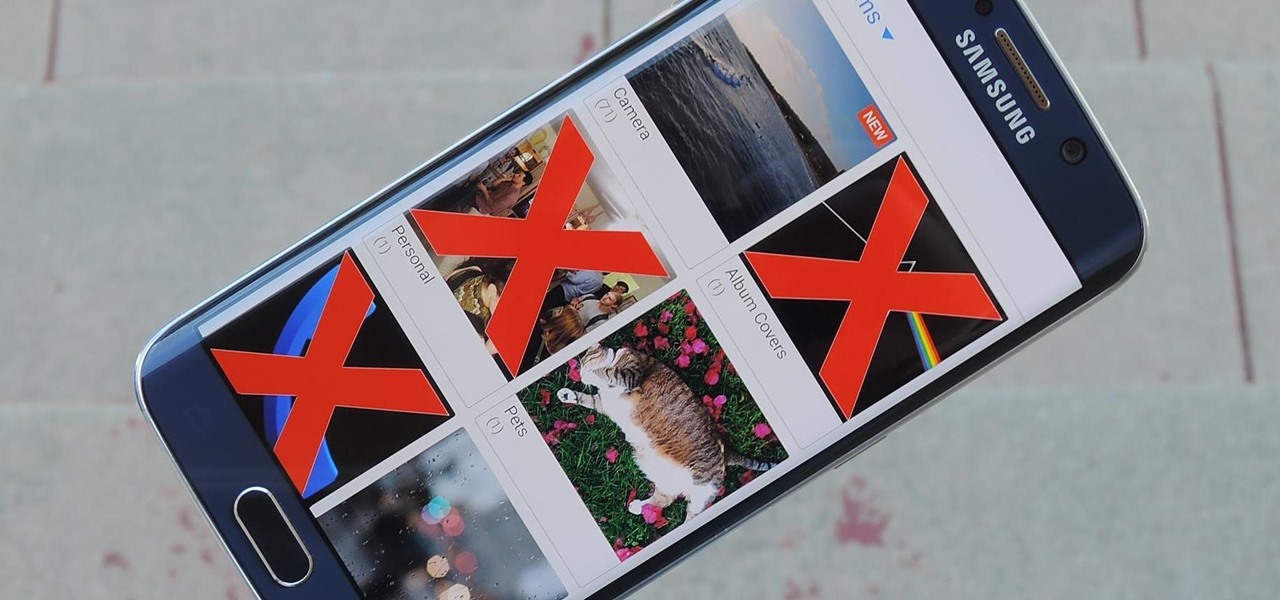
Have you ever noticed that some Android gallery apps display every last photo that you have stored on your device? This is particularly annoying when most stock gallery apps don't provide an option for hiding certain folders from your filmstrip view. Then there are music players that load up ringtones and video players that queue every video on your device, regardless of whether you want them there or not.

Welcome back, my tenderfoot hackers! Now that we have begun this trip down web app hacking lane, we need to first address target reconnaissance. Like any hack, reconnaissance is critical. (Are you tired of me saying that yet?)

Using spaghetti squash "noodles" for a healthy, low-carb meal seems like such a great idea, but as many of us know, turning this vegetable into a decent pasta facsimile usually has less-than-satisfying results. The usual method is to cut the squash lengthwise and roast, microwave, or steam it. Often, it comes out overcooked and underwhelming.

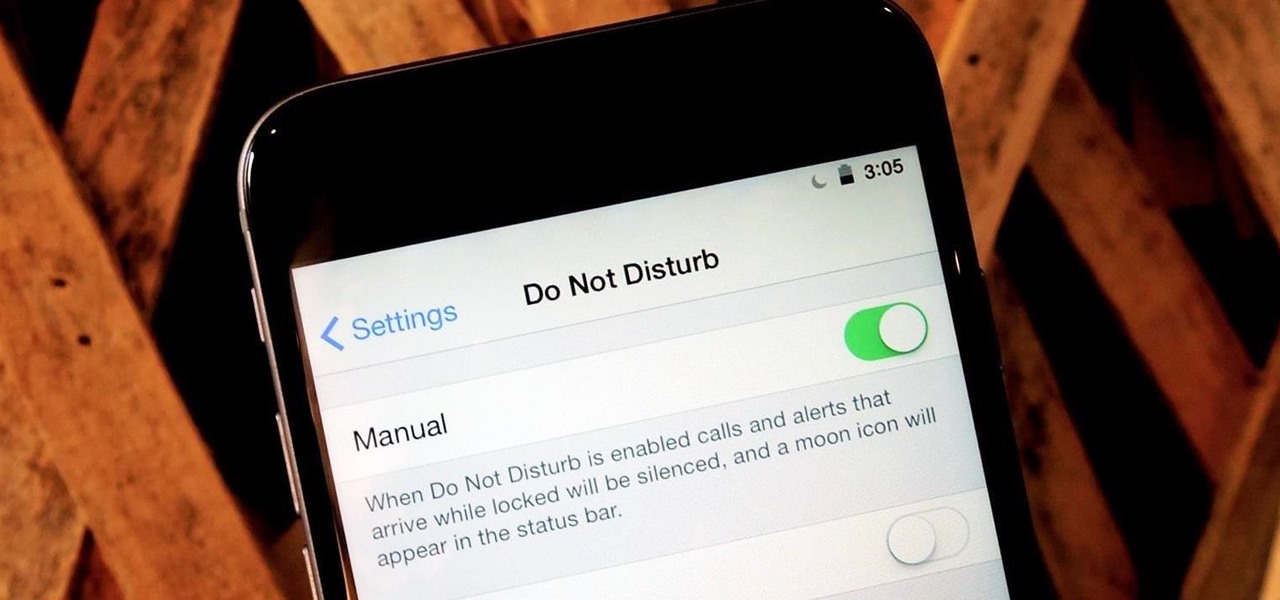
At certain times of the day, like when I finally get home after sitting through aggravating traffic, the last thing I need is the sound of my phone irritating me any further. So, I toggle on the "Do Not Disturb" feature (introduced in iOS 6) on my iPhone and get to enjoy a little peace of mind.

With most of HTC's staff working on getting Sense updated to Android Lollipop, their piecemeal approach to individual app updates now comes to their Gallery app. The new update is available for all HTC devices running KitKat, but if you have the HTC Service Pack installed, it will run on any Android device running 4.4 or above.

Third-party keyboard support, introduced earlier this year by Apple with iOS 8, was initially pretty awesome. I loved playing around with all of the different options available in the iOS App Store, including SwiftKey, TouchPal, GIF Keyboard, and Swype.

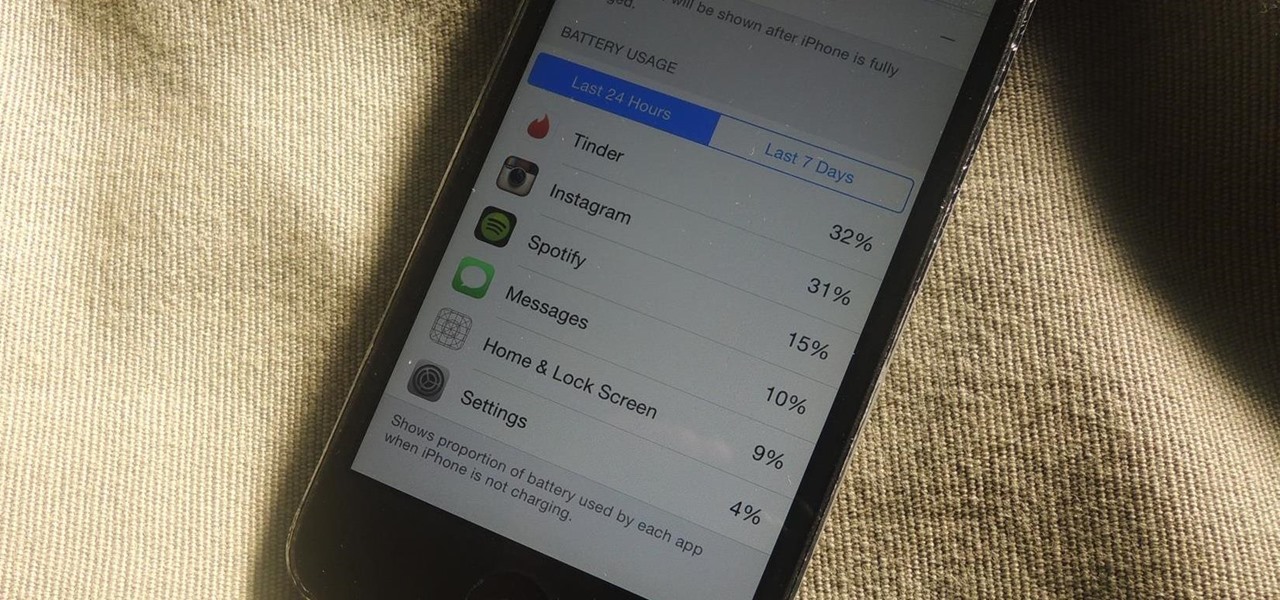
One of my favorite new additions to iOS is the ability to view battery usage stats on a per-app basis, which is helpful in knowing exactly which apps are taking up all of my iPhone's battery life. If you jailbreak iOS 8 on your device, you can take Apple's stock battery stats feature even further to give you details on how those apps are actually using the battery.

Although sleep mode and screen savers contribute to the security and energy preservation of my MacBook, it can become a nuisance when they initiate unwelcomely. Yes, I could just change these settings in System Preferences, but to do this every time I momentarily leave my Mac unattended would be tedious, to say the least.

Apple doesn't make it very easy to delete things quickly from your Photos library, mainly for two reasons. First of all, if you delete multiple pictures at once, it's difficult to know the full details of each individual one you're selecting because the tiny thumbnails don't show very much detail. Secondly, if you delete the pictures one-by-one, you'll be able to view them in full screen, but it will take forever. And dealing with a delete confirmation each time is enough to drive anyone crazy.

Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective.

Video: . Extraterrestrial life is life that does not originate from Earth. It is also called alien life, or, if it is a sentient and/or relatively complex individual, an "extraterrestrial" or "alien" (or, to avoid confusion with the legal sense of "alien," a "space alien"). These as yet hypothetical forms of life range from simple bacteria-like organisms to beings far more complex than humans. The possibility that viruses might exist extraterrestrially has also been proposed.

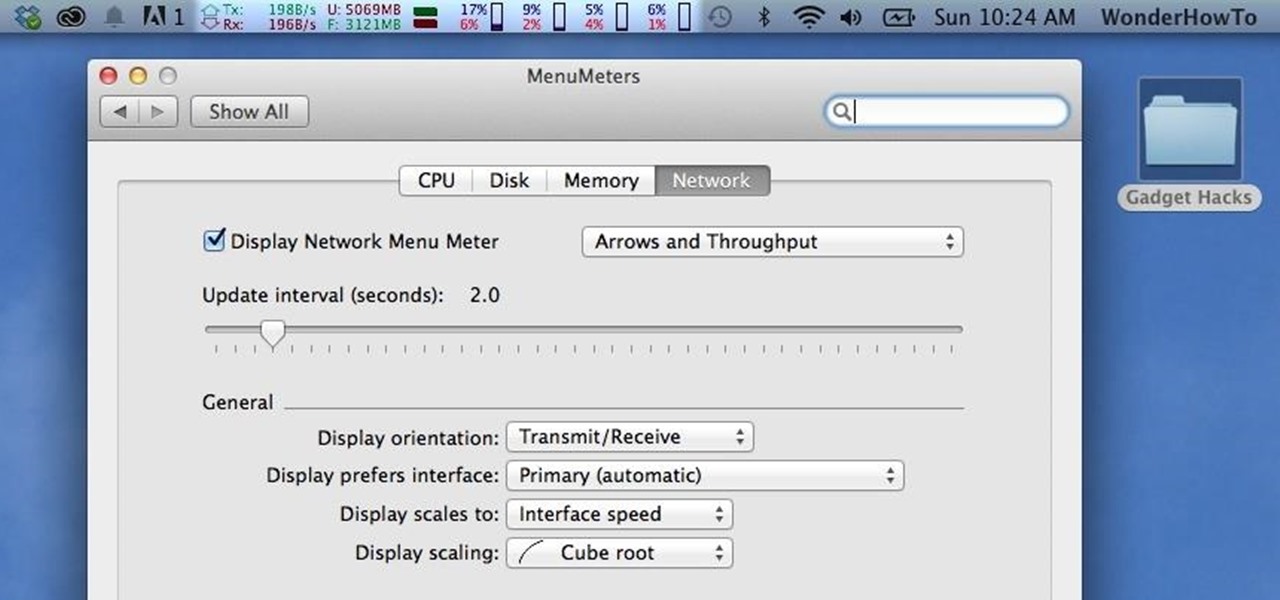
Like a car, your Mac needs to be monitored and cared for to keep it running as smoothly as possible. While your vehicle comes with a ton of gauges to keep track of your oil, temperature, and in some cases, even tire pressure, your Mac has no easy way to watch for low memory or high disk usage. Normally you would have to open up Activity Monitor to take a look at your usage stats, but now there is something better.

Welcome back, my hacker novitiates! When we are trying to find vulnerabilities in a website to attack, we need a solid web server vulnerability scanner. Internet-facing web apps can open enormous opportunities for us as they are often riven with vulnerabilities and can often offer an entire point to the internal network and resources.

Battery life is and most likely always will be an issue with iPhones and other smartphones and tablets, but Apple is making it easier for us to save juice when we need to. To help monitor per-app battery usage, iOS 8 now lets us view battery usage stats for individual apps.

Welcome back, my tenderfoot hackers! Not too long ago, I showed how to find various online devices using Shodan. As you remember, Shodan is a different type of search engine. Instead of indexing the content of websites, it pulls the banner of web servers on all types of online devices and then indexes the content of those banners.

Peeling apples is pure grunt work, especially if you have a recipe that calls for a lot of 'em, like apple pie. You can make this task go by much more quickly if you use something from your tool box—your literal tool box, that is.

If rapid battery drain is something that's been an issue for you in the past, Apple is now making it easier to monitor what might be the problem. In the new iOS 8, you can now check battery usage for every app on your device.

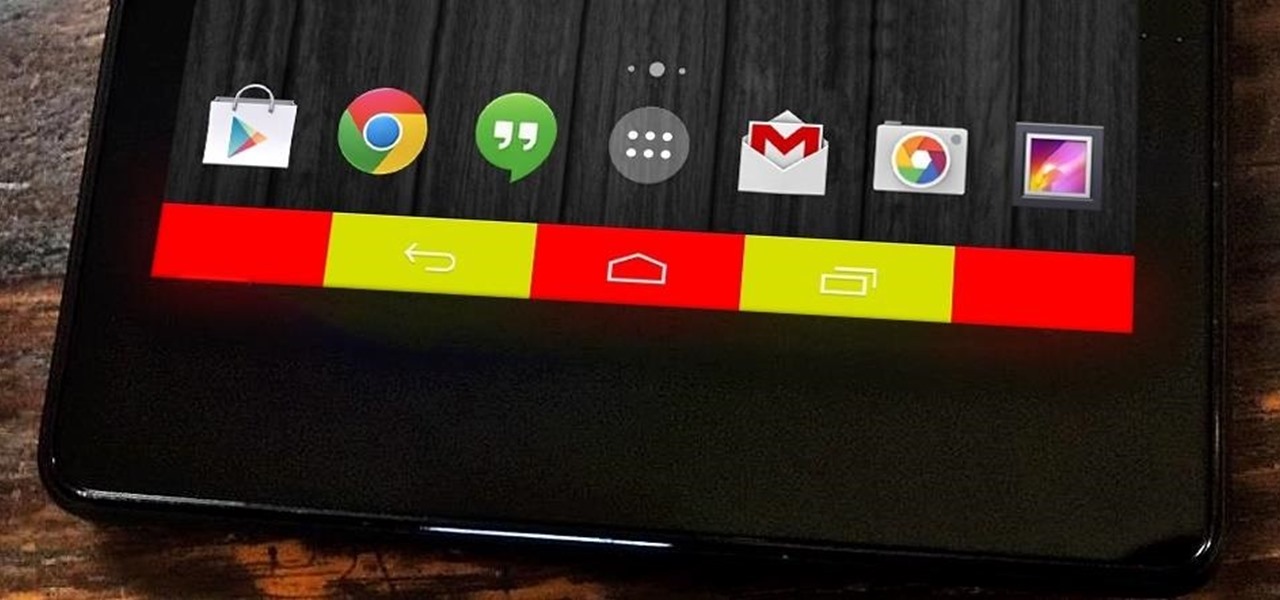
When I first used the Google Now Launcher, I appreciated the transparency that came with it, and how it made the real look larger than it did before. But now that I'm used to it, that transparent navigation bar is beginning to look a little stale.

Android devices are awesome, let me just state that now, but when iOS 7 came out, the new flat theme caught my eye. Yes, we can easily apply new themes on our Nexus 7 tablets to make it look more like iOS 7, but they won't actually change the individual look and feel of apps like Instagram.

Welcome back, my hackers apprentices! To own a network and retrieve the key data, we only need to find ONE weak link in the network. It makes little sense to beat our heads against heavily fortified systems like the file and database server when we can take advantage of the biggest weak link of all—humans.

Quickness and efficiency should always be a fundamental aspect of the experience when using any Android device. Anything less, and we've got a problem. As app development continually progresses, these adjectives become much more refined and polished, making the use of a smartphone a flawless affair of swipes and gestures.

Halloween is only a few short weeks away, and most people are scrambling to get their costumes together before the big night. The secret to a great getup is all in the details, and including your pet in the fun can be exactly what you need to take your costume to the next level.

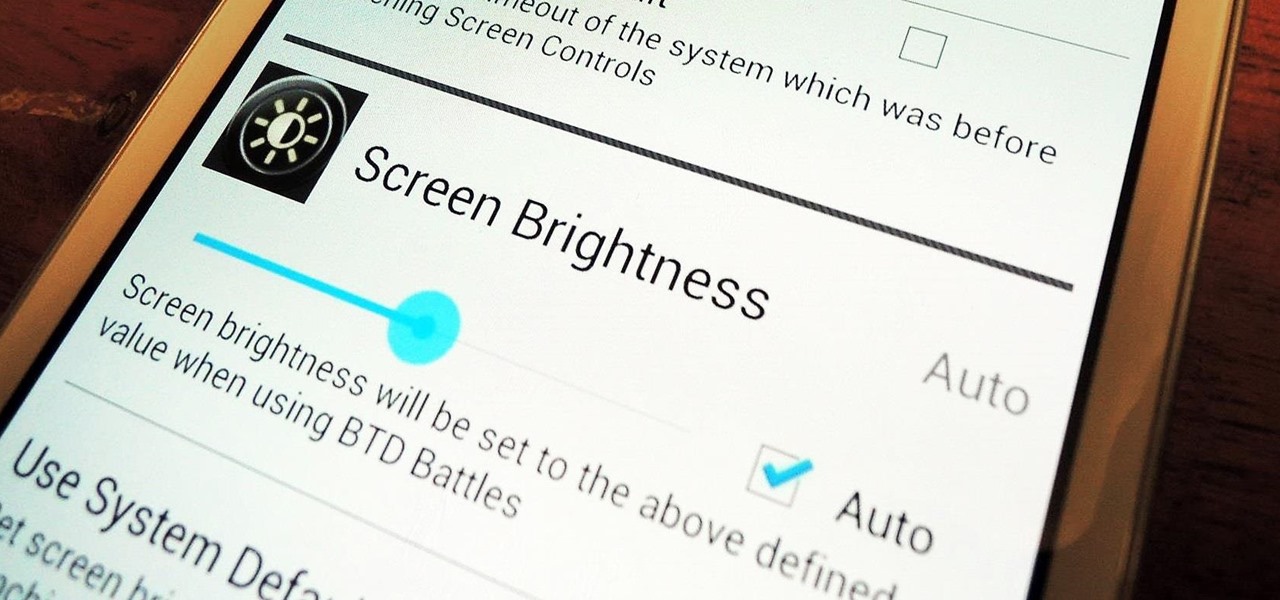
Adjusting the brightness on your Samsung Galaxy S3 can be a real pain sometimes. Each app you open may need a different amount of light to better optimize its use of the screen, and then you have to worry about it potentially eating up your battery life if it's too bright.

Welcome back, my budding hackers! Previous to this tutorial, we've focused mostly on hacking the target system. If we're successful in owning the target system, we'll then want to make certain that the system administrator doesn't know we were there, and that he or she cannot track us.

Welcome back, my nascent hackers! Earlier, I wrote a guide on finding operating system and application vulnerabilities in Microsoft's own security bulletins/vulnerability database. In this tutorial, I will demonstrate another invaluable resource for finding vulnerabilities and exploits by using the SecurityFocus database.

With the majority of smartphone carriers no longer offering unlimited data plans for the iPhone, monitoring how much mobile data you use is a key element to saving money on your phone bill.

Every Windows system includes command prompt; and while a lot of people on Null Byte and WonderHowTo in general know how to use it, some people don't know anything about it, even how to access it.

When it comes to melee combat, two swords can definitely be better than one. Throw a stun gun on top of that and you've got a seriously terrifying weapon. That's exactly what YouTuber jonathanj9969 did with his homemade double-bladed stun sword.