Party poppers are magnificent. They can be used for a plethora of pranks— basically, any prank where the victim / target has to open something. You can use party poppers on practically any household item, but this video covers the much used dental floss container. The exploding floss prank is easy to do yourself, and requires only the floss container, the party poppers, scissors, and a screwdriver. Once your prank target goes to use their floss, they'll have quite the grin.

In this video tutorial, viewers learn how to shoot a compound bow. It is deeply recommended that users who use a compound bow should have a release. Put your arrow on the string and push it in until you hear a click. Now hook the release into the D-loop. Your feet should be shoulder width apart and the tips of your feet should be on the target line. Now look at the target and pull back the bow. Your hand should be at the point of your jaw, arrow at the corner of your mouth and string on the t...

In this video tutorial, viewers learn how to avoid a bad finish to cure a golf push shot. Usually, when players make a swing for the ball, their arm separates from their body. This will take the club to the right of the target and as a result, pushes the shot. To correct this, connect your left arm to your left side as you make a swing. This will allow the club to stay with your turn and go down the target line. This video will benefit those viewers who enjoy playing golf and would like to le...

In this video tutorial, viewers learn how to burn fat with a cable workout. These exercises will require a cable machine. There are four exercises in this workout. These four exercises are: cable wood chop, reverse wood chop, one arm cable row and exercise ball cable crunches. When performing these exercises, do not use a heavy weight. These exercises mainly target the abdominal and core muscles. They also target biceps, obliques and back muscles. This video tutorial will benefit those viewer...

How to aim your shot in World Golf Tour in four easy steps. When aiming for a shot, simply click the target and drag it on your desired location. The Yardage Indicator will change as you move the target closer or further. If it turns red that means that you positioned it outside the maximum carry distance for that club. You can also consider changing your club. Hit the Space Bar or click on Zoom to give you the aerial view to get a closer look and adjust for a precise aim. Be sure to take the...

Kathy Kaehler, author, celebrity trainer, spokesperson and mother, gives us a rundown of the best exercises for fellow women and moms on how to target their belly fat and love handles, and specifically the best ways to tighten these areas. Kathy first does advise us that if you're going to be targeting like this the most important thing first will be cardio and general fitness. Then, she offers us first the side plank, where you place one elbow to the ground, lying on your side, and then elev...

The obliques exercise is a classical pilates exercise which targets the abdominal muscles to flatten the stomach and strengthen the core. Keeping the elbows wide helps keep the shoulders down and increases the rotation in the trunk, which helps shrink your waist. Be sure to stretch your legs fully each time and stop the knee at 90 degrees of hip flexion to encourage greater strengthening of the abdominal muscles. Watch this how to video and you will be strengthening your obliques with pilates...

If we had the time, we would totally make all of our own Valentine's Day cards. But if you have kids, then you know that crafting 36 individual cards for each student is more than a pain in the behind.

This tutorial assumes you've already set up your Facebook account, and are looking for tips and ideas on how to create a profile. Create a page for yourself, your business, your favorite group or any other organization you want to spotlight.

This tutorial shows you how to make chainmail following the tradition European four in one method. You'll need many small metal rings of uniform size and some metal pliers (work gloves are also recommended!) Afer you make each individual unit, you're also shown how to bring them together in a larger piece.

Access your favorite FM radio station with your Motorola Q! This tutorial also shows you how to load your favorite music onto your cell phone, and then choose segments to turn into ringtones, which you can personalize further by assigning them to individual callers.

The new version of Microsoft Office has a feature which allows you to batch create PDFs. You can easily convert whole folders or specfic selections of Word, Excel or PowerPoint files into PDF files. You also have the option of converting the files into individual PDFs, or turn them into one large file.

Not everyone has the "Sun" or "Apollo" line on their palm. For those lucky enough to have it, such a line indicates many potential gifts and popularity! Watch this video as Jim Winters explains how to identify the Sun line and what it indicates for the individuals who have them.

In this video, learn how to decorate beautiful cupcakes that are perfect for spring or summer parties. These little cakes look exactly like flower pots and in this tutorial, you will get a step by step walkthrough of the decorating process. These unique and delicious cakes will make a great addition to any table.

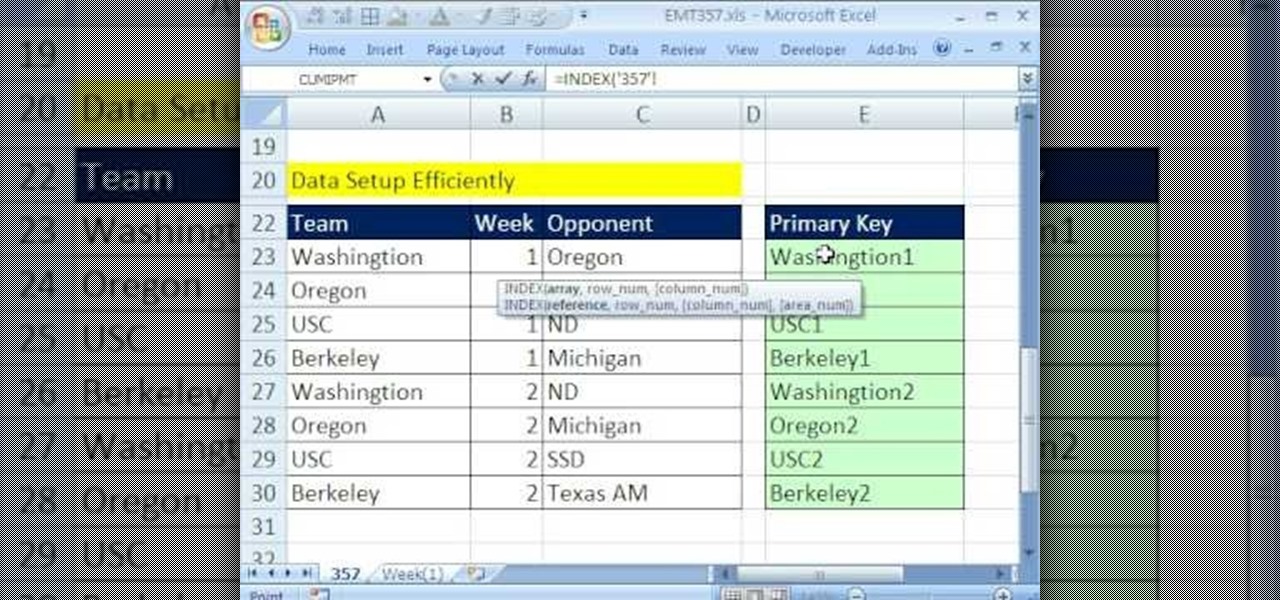
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 357th installment in their series of digital spreadsheet magic tricks, you'll learn how to pull data from individual sheets to a single master sheet given improper data setup.

Every new pair of ballet shoes needs their elastics sewn on to fit the individual personally. In this video, learn a few tips on sewing in the elastic and satin ribbons with help from a ballet expert: Lynda DeChane-Audette is the founding artistic director of the South Florida Ballet Theater and was born in Boston. Learn more ballet from this expert by searching WonderHowTo! You're only practice time away from ruling the dance floor!

Veronica Belmont from Tekzilla shares a tip for finding lost podcasts without unsubscribing and resubscribing to the feed. To do this by a simple keyboard combo fist close the disclosure triangle so that the individual episodes are hidden, then hold down the 'Option key' in Mac or 'Shift' in Windows and toggle the disclosure triangle as shown. The iTunes feed will refresh and all the past episodes will reappear. Combine this with the "Get All" button to find lost podcasts.

A below elbow arm amputee demonstrates how to put on a dress shirt, fold the collar and tie a tie with his prosthetic hook. This is an adaptive equipment tutorial for handicapped, disabled or individuals that have lost limbs to amputation. The prosthetic arm outfitted with a hook or hand can be body powered or myoelectric. The operation is important to ensure healthy living and daily tasks like dressing yourself.

A below elbow arm amputee demonstrates how to open a jar with his prosthetic hook. This is an adaptive equipment tutorial for handicapped, disabled or individuals that have lost limbs to amputation. The prosthetic arm outfitted with a hook or hand can be body powered or myoelectric. The operation is important to ensure healthy living and daily tasks like opening jars, bottles and lids in the kitchen.

A below elbow arm amputee demonstrates how to don and operate his myoelectric prosthetic hook and hand. This is a first hand account of what goes into using prosthetic hands and hooks for individuals with arm amputations. This video is an overview of adaptive equipment for handicapped or disabled persons to assist them. The myoelectric hook and hand are very helpful in assisting persons with arm amputations or otherwise missing limbs.

A below elbow arm amputee demonstrates the device he uses in the gym. He shows you how to use a prosthetic for working out at the gym when you've suffer a limb amputation. This video is very helpful in describing utilities available for enabling individuals with amputations to workout or get around and function in a gymnasium setting. This is a video that addresses adaptive equipment for handicapped or disabled people.

This is the first drum editing video in Pro Tools from thestudiofiles.com.

Watch this video to learn how you can use folders to better organize your Mac dock. Group together applications in folders and add the folders to your dock instead of each individual app.

Looking for a little extra flair? You could get eyelash extensions, or even eyelash transplants; but applying false eyelashes is a lot easier and you can do it all by yourself.

In this video tutorial you are told how to use the Wagon Wheel Cue Ball Control training method. This is called Wagon Wheel because each target ball is aligned to RESEMBEL the spokes of a wagon wheel. Set your cue ball and your object ball in the same position each time. The objective is getting the cue ball to one balls width of the target ball. Using THE FOLLOWING cue ball, direction and speed. By using a piece of chalk the instructor helps line up the balls. By using either a quarter stick...

Component 1. Frame And Posture. The benefits of dance shoes never outweigh the benefits of proper spin technique. Your body should be straight lower abs and stomach should be tight. Your arms are in proper position. If you lift your hand it should be in 90 degree angle.

So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit makes it easy to perform local privilege escalation and get root with its exploit suggester module.

SMB (Server Message Block) is a protocol that allows resources on the same network to share files, browse the network, and print over the network. It was initially used on Windows, but Unix systems can use SMB through Samba. Today, we will be using a tool called Enum4linux to extract information from a target, as well as smbclient to connect to an SMB share and transfer files.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

Open-source intelligence researchers and hackers alike love social media for reconnaissance. Websites like Twitter offer vast, searchable databases updated in real time by millions of users, but it can be incredibly time-consuming to sift through manually. Thankfully, tools like Twint can crawl through years of Twitter data to dig up any information with a single terminal command.

The most essential part of a healthy lifestyle is managing your diet — after all, what would be the point of a daily workout regimen if you were eating junk food? Thankfully, Samsung Health makes it easy to record your calorie and nutrient intake to get a clear picture of your dietary habits and how you can make them better.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

Using Hydra, Ncrack, and other brute-forcing tools to crack passwords for the first time can be frustrating and confusing. To ease into the process, let's discuss automating and optimizing brute-force attacks for potentially vulnerable services such as SMTP, SSH, IMAP, and FTP discovered by Nmap, a popular network scanning utility.

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

Facebook really wants your phone number, nagging you for one as soon as you join. This isn't all bad since it can help secure your account with two-factor authentication. On the flipside, this makes it easy to reveal the private phone numbers of virtually anyone on Facebook, including celebrities and politicians. We're going to look at how a hacker would do this and how to protect yourself.

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.

With the release of the Mirai source code, botnets are back in a big way. In the early days of botnets, zombies (infected hosts) would report to IRC (Internet Relay Chat) channels for CNC (command and control) instructions. Modern botnets have evolved, but they continue to use the same concepts as their predecessors.

Welcome back, my neophyte hackers! Metasploit is such a powerful tool that I can only scratch the surface of its capabilities here. As it has developed over the years, it is now possible to use Metasploit for nearly everything from recon to post exploitation to covering your tracks. Given its versatility, every aspiring hacker should have at least a tentative grasp of Metasploit.

Although this century is still young, with little fanfare we may have just witnessed the "Hack of the Century." AV software developer Kaspersky of Russia recently announced that they found that some hackers have stolen over $1 billion from banks around the world!

Seldom in recent history has a cyber security event caused so much media stir (maybe because it happened to a media company?) and international relations upheaval. Cyber security breaches seem to take place daily of major corporations, but the Sony hack seems to have captured the American imagination and, for that matter, the whole world's attention.