
News: Target Treats Shoppers with Augmented Reality Tricks via Snapchat
Big-box retailer Target has been on a bit of an augmented reality advertising shopping spree via Snapchat lately.


Big-box retailer Target has been on a bit of an augmented reality advertising shopping spree via Snapchat lately.

It's common for IoT devices like Wi-Fi security cameras to host a website for controlling or configuring the camera that uses HTTP instead of the more secure HTTPS. This means anyone with the network password can see traffic to and from the camera, allowing a hacker to intercept security camera footage if anyone is watching the camera's HTTP viewing page.
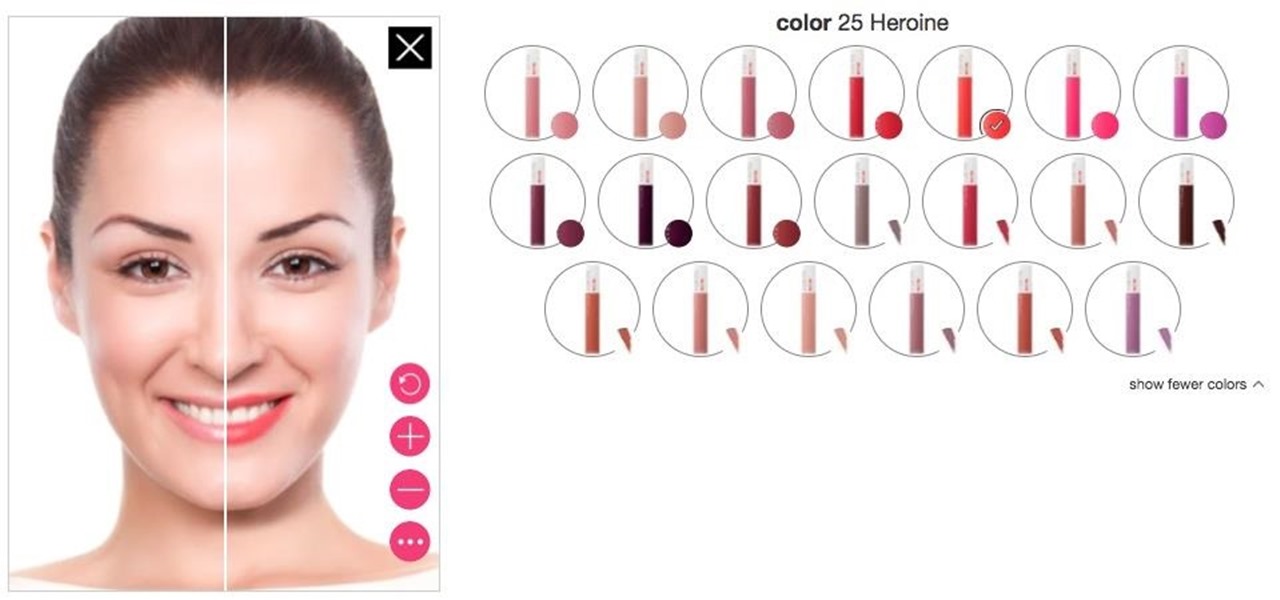
Department store chain Target is the latest retailer to offer an augmented reality cosmetics app for customers to virtually try on lipstick.

Using a keylogger to intercept keys pressed on an infected computer can circumvent encryption used by email and secure chat clients. The collected data can often reveal usernames, passwords, and potentially compromising and private information which hackers abuse for financial gain.

Chrysaor, a zero-day spyware believed to have been created by the Israeli "cyber war" group NSO, is an even greater threat to Android phones than it ever was to iOS.

360world, a Hungary-based tech company involved in motion control and augmented reality, released information today about their latest products, the CLAIRITY HoloTower and CLAIRITY SmartBinocular. These tools are designed to bring augmented reality into the hands of air traffic controllers, via Windows Mixed Reality, to greatly improve their workflow over tools already in use.

It's a real challenge to create exploding targets that can be set off by low velocity projectiles, yet remain safe to handle without risk of ignition during construction.

Excel is great, and if you're a Mac user, Excel 2008 for Mac has a lot of new and useful great features you can use to maximize efficiency in your spreadsheets. Excel doesn't have to be the boss anymore, you can! The Microsoft Office for Mac team shows you all the great features in this how-to video.

Data can be troubling, especially if there's a ton of it plaguing your Excel worksheet. But Excel 2008 for Mac makes life a little easier and less confusing thanks to a few worksheet tips and features you can utilize to work with your data in worksheet cells. The Microsoft Office for Mac team shows you just how to work with worksheets in this how-to video.

Not every client or coworker likes to mine through a spreadsheet to find all the important data. So, with Excel 2008 for Mac, you can easily share that data without sending the entire Excel spreadsheet. To do this, all you need to do is to use the "copy as picture" option. The Microsoft Office for Mac team shows you just how to insert a spreadsheet snippet in this how-to video.
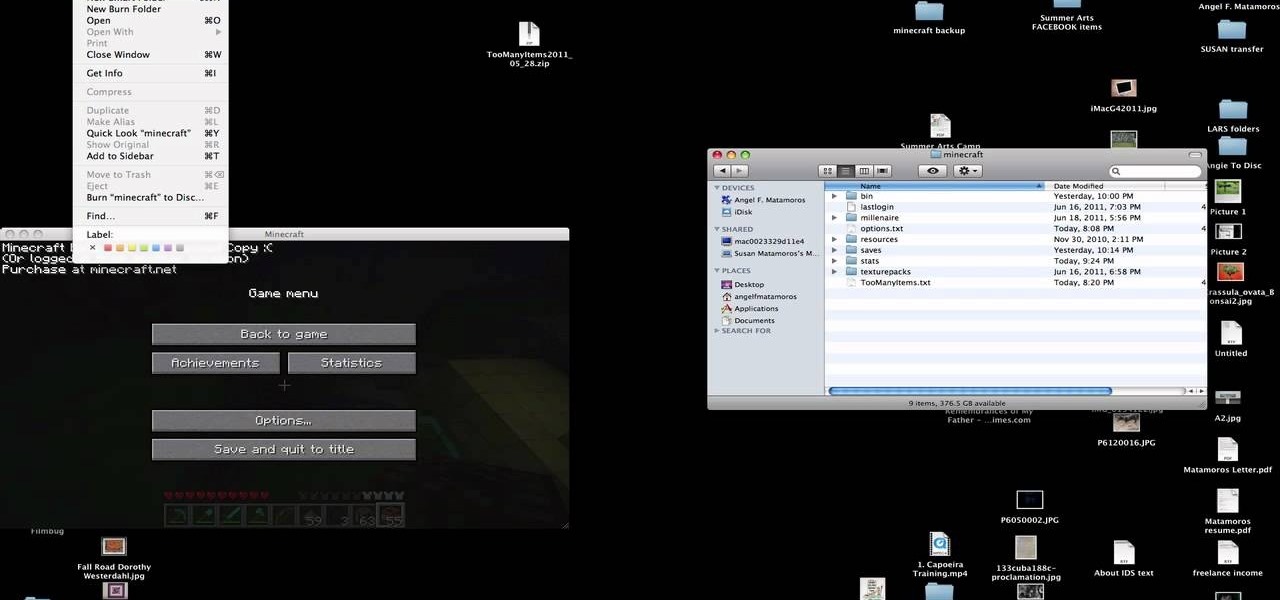
You have worked long and hard creating an entire world of Minecraft data. Make sure you have all of that saved data backed up. Watch this video to learn how to backup your Minecraft data. You will be glad that you did.

Thirty dollars a month may be a little steep for an unlimited data plan for iPad users. To cut down on your data usage, you can download the Offline Pages app to browse articles or blogs offline. InstaPaper is another account you can use as well, and both will cut down on your data usage per month.
In this video we are shown a workout that targets your stomach and helps you to lose belly fat and tighten your lower abs.
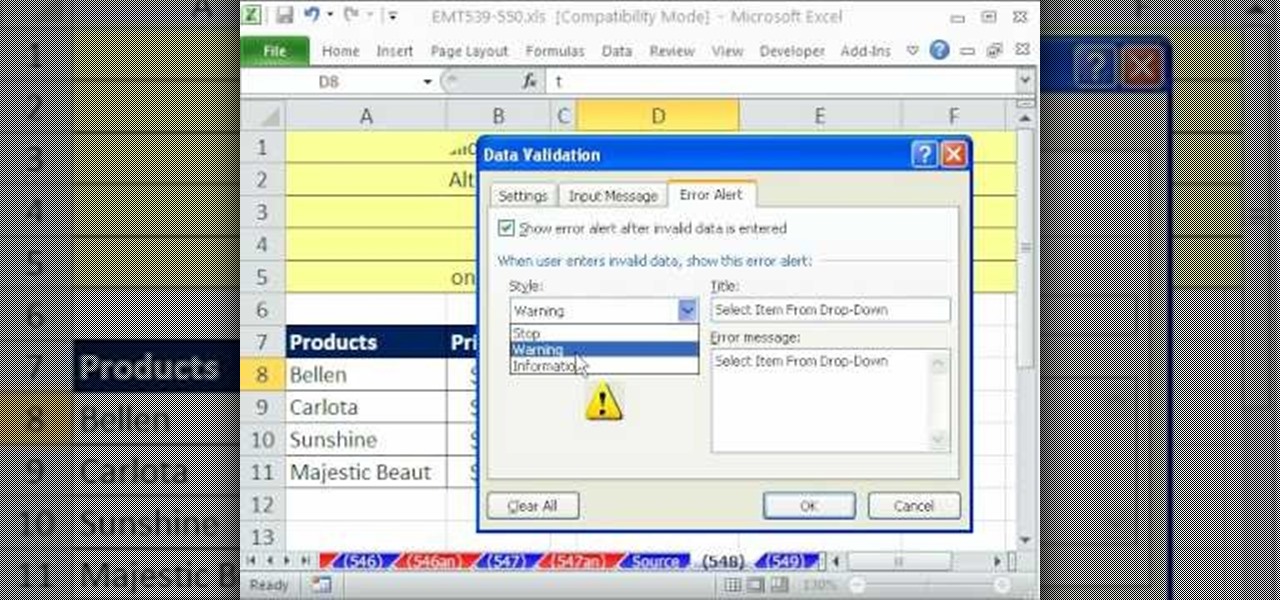
If you want to manage what sort of data is entered into your Excel spreadsheet, data validation will help you to accomplish just that. In this Excel tutorial from ExcelIsFun, the 549th installment in their series of Excel magic tricks, you'll learn how to use data validation to full effect in your Microsoft Office projects.
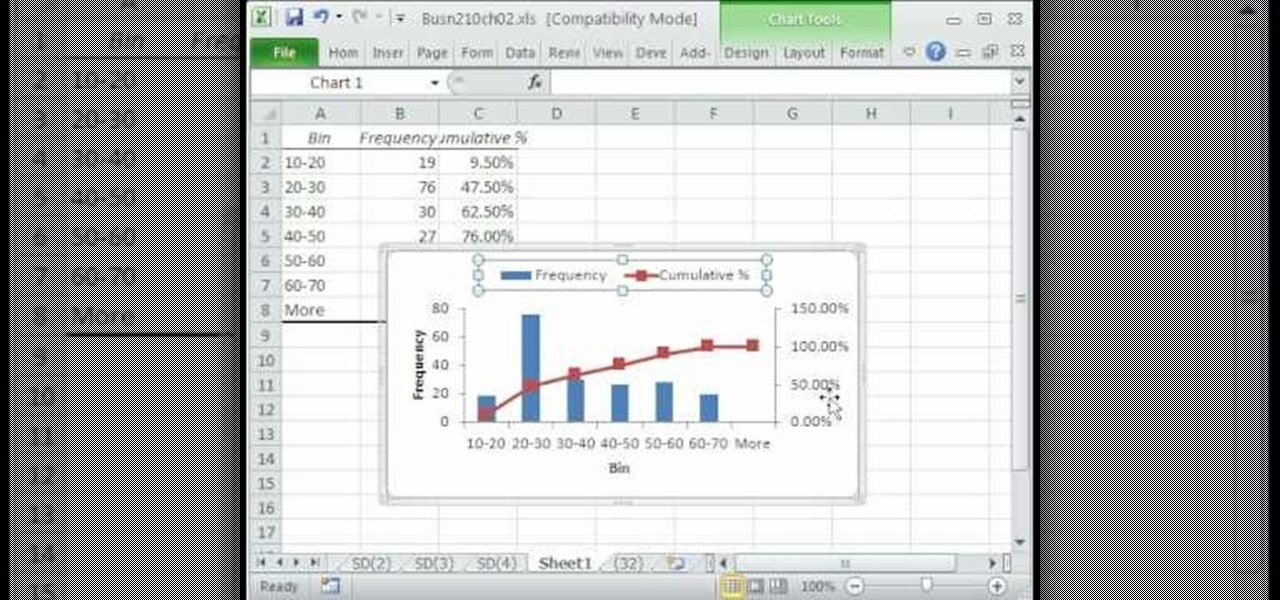
A histogram is a summary graph showing a count of data points that fall in various ranges. Histograms are used in statistics and other forms of mathematics. In this video, learn how to create your own histogram using data analysis on the computer. This tutorial will show you how to create a frequency distribution, a cumulative frequency distribution, a histogram chart and an ogive chart with the data analysis add-in.

Take a look at this instructional video and learn how to fit a projected image onto a target surface with Johnny Chung from Carnegie Mellon University. Typically, you'd need to use a screen to be directly in front of the projector and at a very specific orientation to get an undistorted image. What this tutorial is trying to accomplish is to place a screen at any location that is convenient and then calibrate the projector onto the target surface. This technique is used to automatically disco...

See how simple it is to create data-driven web sites using ASP.NET 2.0, Visual Web Developer 2005 Express Edition, and SQL Server 2005 Express Edition. Watch this video tutorial to learn how to create a database, add its data, and display that data on a web page.

The object is to pass to ball between the cones in as few shots as possible, watch and learn how to do this target passing soccer drill.

All-American Skeet Champion Todd Bender explains the safety "does and don'ts" of shooting clay targets. He shows how everyone in the family can enjoy the game and still use proper gun handling techniques.
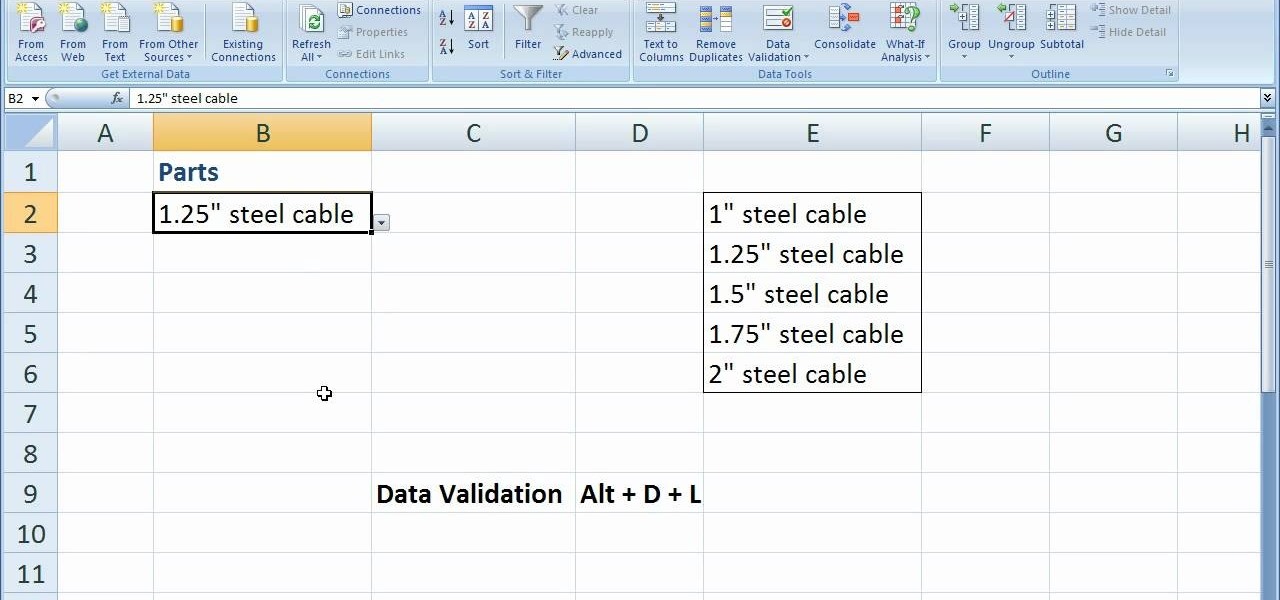
In this software video tutorial you will learn how to create drop down menus in Excel using Data Validation. This example will show you how to display a list of parts in a drop down menu. Create the list of parts somewhere in your worksheet. Then in the cell underneath the one where you want to display the parts, go to the data validation window and enter the data. For this select the cell and then press 'Alt + D + L' to bring up the data validation box. Here you click on 'settings' and selec...
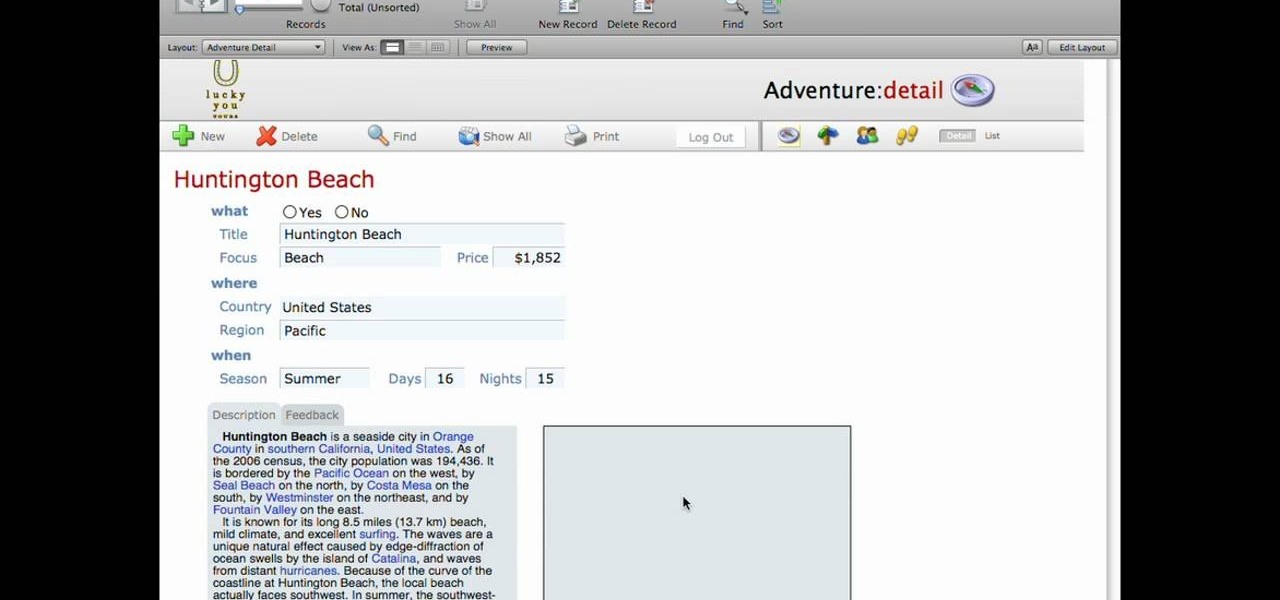
This lynda.com video tutorial shows how to use container fields with FileMaker Pro 10. When you want to create fields in FileMaker database you have the choice on what kind of fields you want to make. Many general fields are self explanatory like text, date etc., but there is a special kind of field called the container field. FileMaker Pro container field is a versatile data type in that it can store any kind of binary data. Container fields can be used to hold binary data in four broad clas...

This tutorial on the companion Tech Ease for Mac site shows you how to use Inspiredata to collect, organize, and visualize data using several types of diagrams supported by the program. The movies were recorded on a Mac, but Inspiredata is a cross-platform program so the steps shown should work on the Windows version of the program as well. Inspiredata works like a database system that allows you to add notes and more.

This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol works by encapsulates your data into an encrypted payload and transmitting it to the SSH Server which is setup on a trusted LAN.

In Halo: Reach for the Xbox 360, there is so much to do! The campaign, the multiplayer, the achievements! But One tough one to get is all 19 hidden data pads. Luckily for you, the first nine can be acquired on any difficulty, and in this video you will learn the locations of all nine of the initial data pads on levels such as Winter Contingency and Pillar of Autumn!

If you use Microsoft Excel on a regular basis, odds are you work with numbers. Put those numbers to work. Statistical analysis allows you to find patterns, trends and probabilities within your data. In this MS Excel tutorial from everyone's favorite Excel guru, YouTube's ExcelsFun, the 27th installment in his "Excel Statistics" series of free video lessons, you'll learn how to create a quantitative data dot plot chart using the REPT and COUNTIF functions.
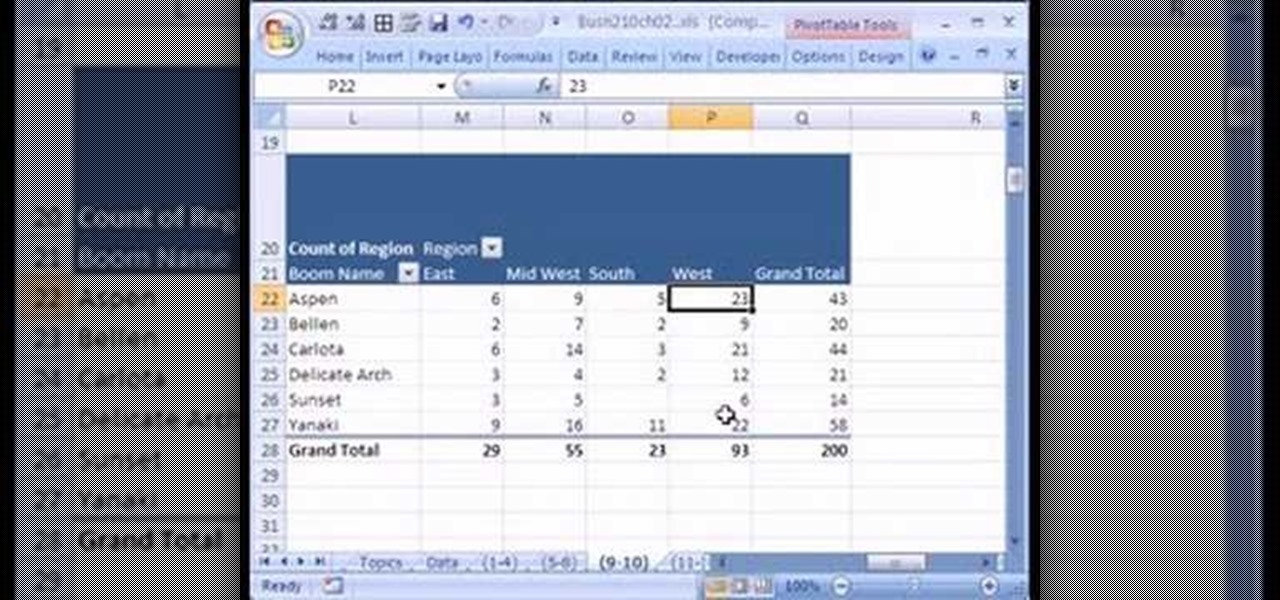
If you use Microsoft Excel on a regular basis, odds are you work with numbers. Put those numbers to work. Statistical analysis allows you to find patterns, trends and probabilities within your data. In this MS Excel tutorial from everyone's favorite Excel guru, YouTube's ExcelsFun, the 16th installment in his "Excel Statistics" series of free video lessons, you'll learn how to cross tabulate & do percentage cross tabulation for categorical data using a pivot table (PivotTable).

If you use Microsoft Excel on a regular basis, odds are you work with numbers. Put those numbers to work. Statistical analysis allows you to find patterns, trends and probabilities within your data. In this MS Excel tutorial from everyone's favorite Excel guru, YouTube's ExcelsFun, the 17th installment in his "Excel Statistics" series of free video lessons, you'll learn how to cross tabulate & do percentage cross tabulation for categorical data using formulas rather than pivot tables.

We're living in the age of Big Data. As the primary force behind everything from targeted marketing campaigns and online search algorithms to self-driving cars and even space exploration, massive sets of complex data stand at the heart of today's most exciting and important innovations.

Before the internet, acquiring enough data to analyze was challenging. Now we have the opposite problem: a deluge of data makes trying to sort through it nearly impossible. That's where data science comes in.

There is so much information in the world that trying to make sense of it all can be daunting. That's where data analytics comes in. By learning how to inspect and model data, you can take large data sets and transform them into highly valuable information that can take any business further.

Data is king. Nearly every carrier and MVNO offers unlimited talk and text with their cellular plans. Where they differ is the amount of data available, so that's the part that can save or cost you the most money.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

SMB (Server Message Block) is a protocol that allows resources on the same network to share files, browse the network, and print over the network. It was initially used on Windows, but Unix systems can use SMB through Samba. Today, we will be using a tool called Enum4linux to extract information from a target, as well as smbclient to connect to an SMB share and transfer files.
Featured on MTV's Catfish TV series, in season 7, episode 8, Grabify is a tracking link generator that makes it easy to catch an online catfish in a lie. With the ability to identify the IP address, location, make, and model of any device that opens on a cleverly disguised tracking link, Grabify can even identify information leaked from behind a VPN.

Wi-Fi devices are continually emitting "probe frames," calling out for nearby Wi-Fi networks to connect to. Beyond being a privacy risk, probe frames can also be used to track or take over the data connection of nearby devices. We'll explain how to see nearby devices emitting probe frames using Probequest and what can be done with this information.
Your email inbox is a treasure trove of personal data. The people you contact, your writing style, which messages you flag as spam — all of this information and more can be used to paint a clear picture of you. Google knows this as well as anybody, so they use this data to constantly improve your experience in Gmail.

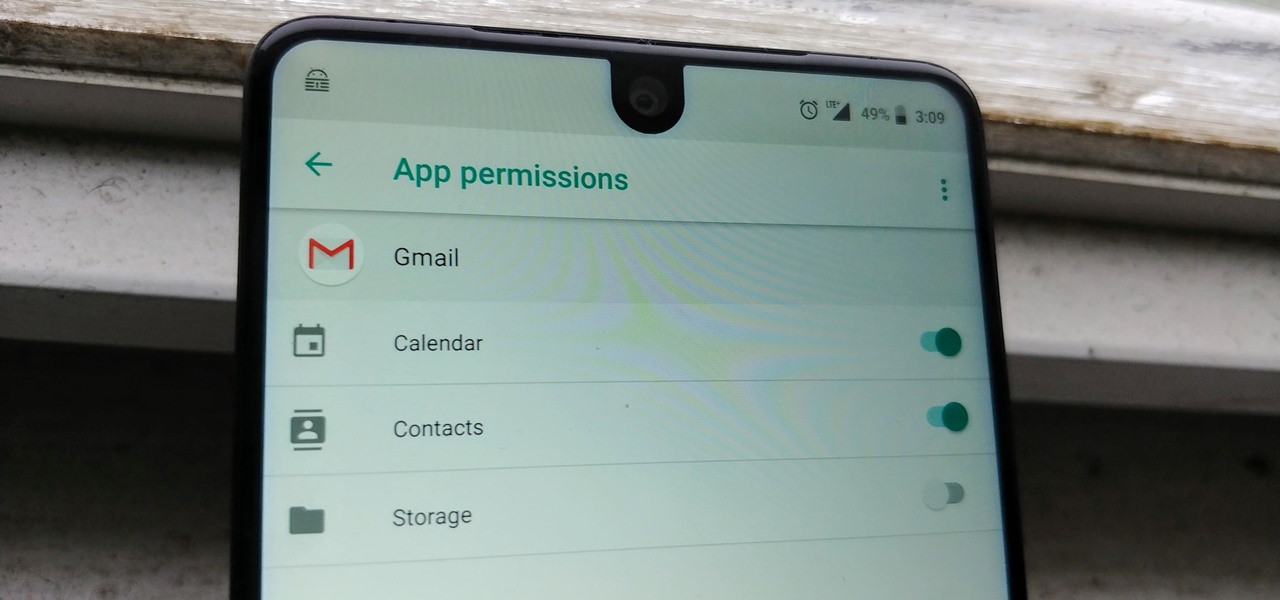
After setting up your phone, there are a number of things you should do immediately before download your favorite apps. Specifically, now that your data is on the device, you need to take steps now to ensure it's both protected and retained. Fortunately, most of these steps are a one-time process.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

A few months ago, it was discovered that Verizon was installing an extremely shady app called "DT Ignite" on some of its smartphones—most notably, the Galaxy S7 and S7 Edge. The app, created by Digital Turbine, monitors your smartphone usage, then uses the data it collects to silently install "recommended" apps without notifying you.