There's nothing better than real, homemade tomato sauce, but to really develop the flavors, it usually has to simmer for a few hours. And while it's totally worth doing if you have the time, some nights it's just not an option. That's where the pre-made stuff comes in. Jarred pasta sauce certainly doesn't taste the same, but it's really easy to dress up when you need something quick. If you don't want anyone to know your "secret recipe," here are 10 ways to make store-bought spaghetti or mari...

The use of smart phones is not limited only as a mode of communication now-a-days. There are many things that can be done with the help of a smart phone.

The @DesignGears guys have been busy today, leaking an unofficial KitKat build (Android version 4.4.2) for the AT&T Samsung Galaxy Note 3. The latest is a peek into what the international variants are beginning to see, although this build is far from official. Still, if you want to give it a shot, I'll show you how to install it, but make sure to check out the details below the how-to to see what you can expect, good or bad.

It's time. You've experimented with apps from the Play Store, you've switched your lock screen, and maybe you've taken different launchers out for a spin. If, throughout your tinkering, you've found yourself chanting, "More. More. Give me more!" then now is the time. It's time to root.

The Nexus 7 is a huge jump in screen size when coming from a phone, but obviously this tablet is still smaller than some of the major players such as the Nexus 10, Galaxy Tab, etc. One way to squeeze out a little more space is to eliminate the navigation and status bars.

How to easily build a raised garden bed out of wooden pallets for free! …Well almost free. Building a raised vegetable garden with pallets or reclaimed wood is a really rewarding experience. The garden bed idea out of pallets came about from the fact that l wanted to build a rustic looking raised garden bed. A vegetable garden bed that not only provides delicious food, but looks good at the same time. The recycled wood has come from hardwood timber pallets that have been sourced totally FREE ...

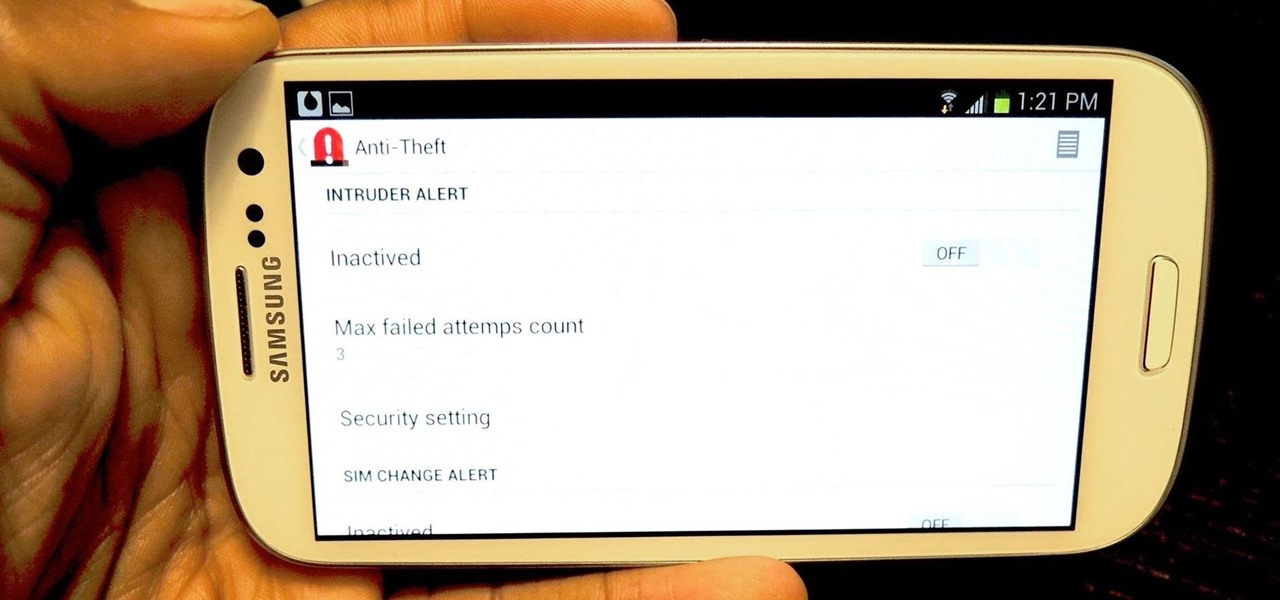
I love surprises. Surprise parties, surprise visits, surprise Patrick... But there are times when a surprise is the last thing you want, like reaching into your pocket to find that your Samsung Galaxy S3 is not where it should be.

Welcome back, my greenhorn hackers! Continuing with my Wi-Fi hacking series, this article will focus on creating an invisible rogue access point, which is an access point that's not authorized by the information technology staff and may be a significant security vulnerability for any particular firm.

Welcome back, my neophyte hackers! As part of my series on Wi-Fi hacking, I want to next look at denial-of-service (DoS) attacks, and DoSing a wireless access point (AP). There are a variety of ways to do this, but in this tutorial we'll be sending repeated deauthentication frames to the AP with aircrack-ng's aireplay. Remember, hacking wireless networks isn't all just cracking Wi-Fi passwords! Our Problem Scenario

Give me a paintbrush and easel and you'll be sorely disappointed, but give me a Samsung Galaxy S3 and a new app called Let's 8-Bit Art and you might call me the next Picasso.

Navigating through row after row of plants, my tiny fingers would reach into the leaves to pluck all the vile little creatures from their homes and deposit them into a can of gasoline. Potato bug duty, my least favorite gardening chore. Growing up, my family had a small garden every year. And every year, I was recruited to help plant, maintain, and eventually harvest the vegetables from it. There were some tasks I didn't mind, but the ones I hated most usually involved bugs (have you ever see...

There are two options when it comes to a dent in your car — live with it, cringing each time it enters your view, or get rid of it. While the latter is obviously the best option, most of us will probably just live with dents and dings since spare money is better spent on the actual functionality of the vehicle. However, there is a way to knock out automobile dents yourself with relatively little cash in the bank.

Welcome back, my newbie hackers! Hackers often are associated with clandestine and illegal activity, but that is not necessarily always the case. Hackers are increasingly being used and employed for law enforcement, national security, and other legitimate purposes. In this installment, we will look at how a single hacker could save the world from nuclear annihilation.

It's always a good idea to have a pack of mints on hand, especially right after a cup of coffee or a lunch made with loads of garlic. Whether you're going on a date, to the dentist, or to an interview, bad breath is a major faux pas and totally avoidable. Simply pop a mint! But not just any old mint — homemade ones not only freshen your breath but can give you a sense of pride every time you need one.

I'm sure that there are plenty of people out there who have no idea what a plague doctor is/was, so I'll start with an explanation.

The art of persuasion is a very crucial characteristic that anyone can learn, and it has countless benefits. Whether it's at work, home, or in social situations, the ability to be veritably persuasive can have an unheralded impact on your daily life.

This guide will explain how to configure a USB Flash Drive / Memory Stick so that you can run a keylogger within just a few seconds of plugging it in any computer.

While there are countless ways to welcome in the new year, many of them involve imbibing copious amounts of delightfully spirited libations. If you're anything like me, I know you're fearing the monster hangover on New Year's Day.

In my last hack blog on crashing your roommates Win7 system, we started looking at client- side attacks. As promised, we will be looking at some more client-side attacks.

Thanksgiving is pretty much the only day out of the year when you can be a complete fatass. It's totally expected, if not encouraged. In fact, if you aren't stuffing your face with a bunch of delicious and unhealthy food, people start to look at you funny.

As the holidays approach, so does that wonderful Autumn day where loads of people happily camp out in freezing weather in front of their favorite stores to save a few bucks on their favorite electronics. And yes, that day is near... Black Friday brings the biggest markdowns of the year, and that includes slashed prices on many of our favorite touchscreen devices, including the Kindle Fire HD, Samsung Galaxy Tab 2, and Nexus 7. Want to get your hands on an Android tablet for cheap? Below are a...

The Dark Knight Rises. The Amazing Spider-Man. The Avengers. Halloween is a few weeks away and all we're going to see are these same ol' superhero costumes. It's like that every year, due to the immense popularity of comic book films by DC and Marvel.

Since it's October and Halloween is fast approaching, it's time for a series of articles on how to make the coolest Steampunk Halloween decorations for your home! In this installment, we'll look at some jack-o'-lanterns, skulls, and a few other things that are easy to Steampunk, but will still keep that "spooky" Halloween feeling.

There's only three weeks left until the spookiest holiday of the year, which means stores and costume shops everywhere are bringing out their Halloween inventory full force. So now's a good time to start prepping your Halloween costume—because you really don't want to do it last-minute again, do you?

For those who don't know, LEGO recently came out with a new line called Monster Fighters. This set is about fighting monsters, sure, but it's about fighting classic monsters in a Steampunk universe. Just look at this promotional picture from the LEGO site: That LEGO dude (properly called a minifig) is wearing a vest, pocket watch, bowler hat, and a mean smirk. Not to mention that he has a robotic leg. You won't find the word "steampunk" anywhere in this marketing campaign, but I call Steampun...

If you want to make clothes for your cat, you're on your own. As I recently said in this article, cats will just totally flip out if you make them wear things. Your dog may also flip out, but I've found them to be more tolerant, personally.

There's nothing like buying an awesome new gadget, but it leaves you with one problem (besides an empty wallet)—what do you do with the ones you already have? There are plenty of ways to put your old gadgets to use, but if you'd rather get rid of them, you may as well get something out of it, right? Here are five places where you can recycle your electronics and replenish your cash stash.

Stand out from the high street fashion clones with stuff you’ve fashioned yourself. It’s easy to take old pieces of electronic junk and transform them into all sorts of fun ‘n’ funky geeky accessories. Like a totally useful tote bag, a what-on-earth-is-that wallet and a bedazzling belt. It’s terribly geeky but chicy too. Here’s how…

We use smartphones for just about everything, and while that may be beneficial to us in our day-to-day lives, it can also be used against us in the court of law.

It's no secret that there's a lot of surveillance going on these days. It's easier than ever to end up in a database, and even former government agents are speaking out about the atrocious amount of spying being done against our own citizens. They've targeted our laptops, cars, IP addresses, and now they're coming for our iPhones. AntiSec hackers managed to get their hands on a list of over 12 million Apple UDIDs (Universal Device IDs) from an FBI computer, and they published 1,000,001 of the...

RFID chips are everywhere. They're in passports, credit cards, and tons of items you've bought in the last 5 years or so. Big retailers like Walmart started using tracking products with RFID as early as 2004, and today, they're used in everything from mobile payments to hospital record systems. Chances are, unless you're a hermit (in which case you wouldn't be reading this anyway), there's an RFID tag within a few feet of you. Photo by sridgway

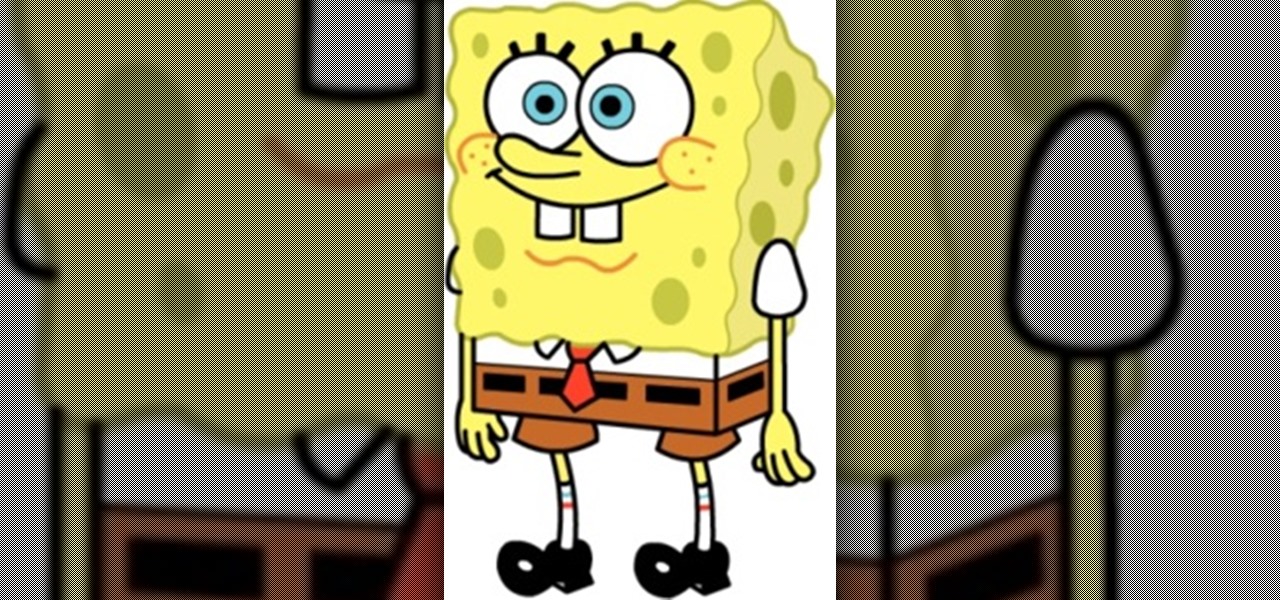
Today we're going to draw Spongebob! He's going to be facing forward, so even beginners should find drawing this guy to be a piece of cake! 1) Begin by sketching out a rectangle with a broader top and a narrow bottom, make sure it's not too skinny though. This will be the base of Spongebob's body.

AdSense. It's a beautiful thing, isn't it? Google AdSense is something every website owner or blogger should use… it's what every blog needs… if you plan on making any money and surviving. So, how much traffic do you need to actually start making money via AdSense? This video will try and answer that question for you. You must have targeted traffic to drive your blog.

This Sports video tutorial shows how to hit the golf ball as a draw. Frank demonstrates in this video how to hit a draw. It is very easy to hit one. What you should aim to achieve is an inside outside swing. He has laid out three clubs on the ground. One club is on target line. The other two clubs are parallel to each other and are on swing path line with the ball placed in their middle. When you swing your club back, go through the two clubs winding up. In the unwind portion, your club shoul...

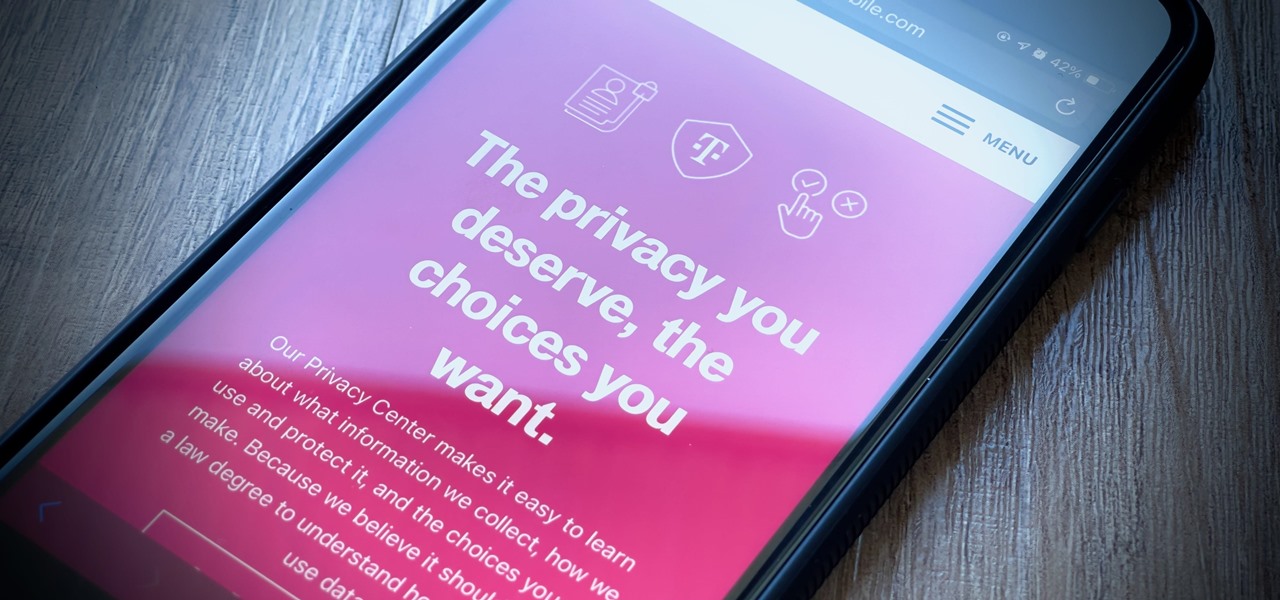
It's getting harder and harder to escape ad tracking by the day. For the latest example, look no further than T-Mobile. The No. 2 carrier updated its privacy policy on Feb. 23, 2021, indicating that it would start sharing customer data with advertisers under the guise of more relevant ads starting April 26. If that's not something you'd like to participate in, there's a way to opt-out.

The team over at Spatial isn't done innovating its way through augmented reality in 2020. Just days after adding a mobile option to its groundbreaking Spatial virtual collaboration product, the company is releasing Tele, a new app geared toward more casual, AR-powered video chats.

Quietly, while the rest of the world was engaged in pandemic and political concerns, a few weeks ago Facebook casually upgraded its Spark AR platform with what it calls Unified Effect Publishing.

Privilege escalation is the technique used to exploit certain flaws to obtain elevated permissions relative to the current user. There are a vast number of methods out there to go from user to root on Linux, and keeping track of them all can be difficult. This is where automation comes into play, and a privilege escalation script called Linux Smart Enumeration is one to take advantage of.

Secure Shell is one of the most common network protocols, typically used to manage remote machines through an encrypted connection. However, SSH is prone to password brute-forcing. Key-based authentication is much more secure, and private keys can even be encrypted for additional security. But even that isn't bulletproof since SSH private key passwords can be cracked using John the Ripper.

Every summer for the last 26 years, hoards of hackers have descended on the Las Vegas Strip for DEFCON, the biggest hacker conference in the US. There's a wealth of talks every season (DEFCON 27 has at least 95 scheduled), and there have been some essential topics to learn from in past discussions. We've dug through the last ten years and found the 15 most popular talks you should watch.