On Wednesday, Microsoft launched a chatbot on social media that learns from conversation, and trolls quickly taught it how to be a shameless, Nazi-loving bigot. Oh Internet, an opportunity for a Hitler joke never slips past you, does it? This Is Why We Can't Have Nice Things

If you're entirely new to smartphones, Android's share menu can seem like a foreign concept at first glance. In reality, it's one of Android's most central and unique features, and with a little experience, it can make your smartphone a lot easier to use.
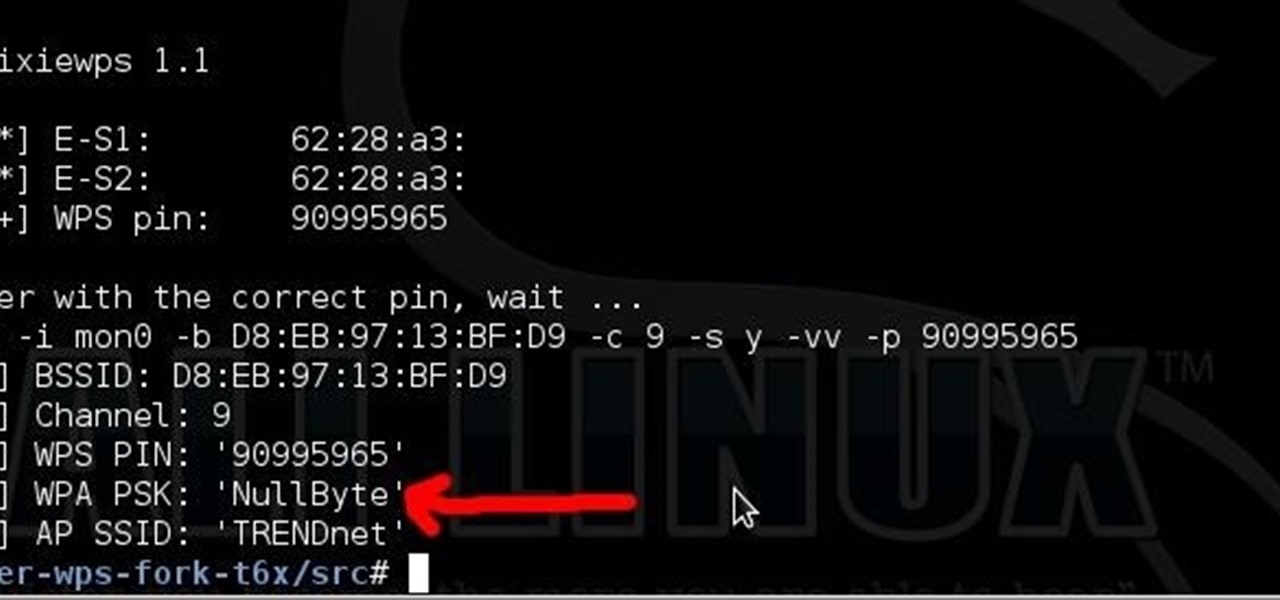
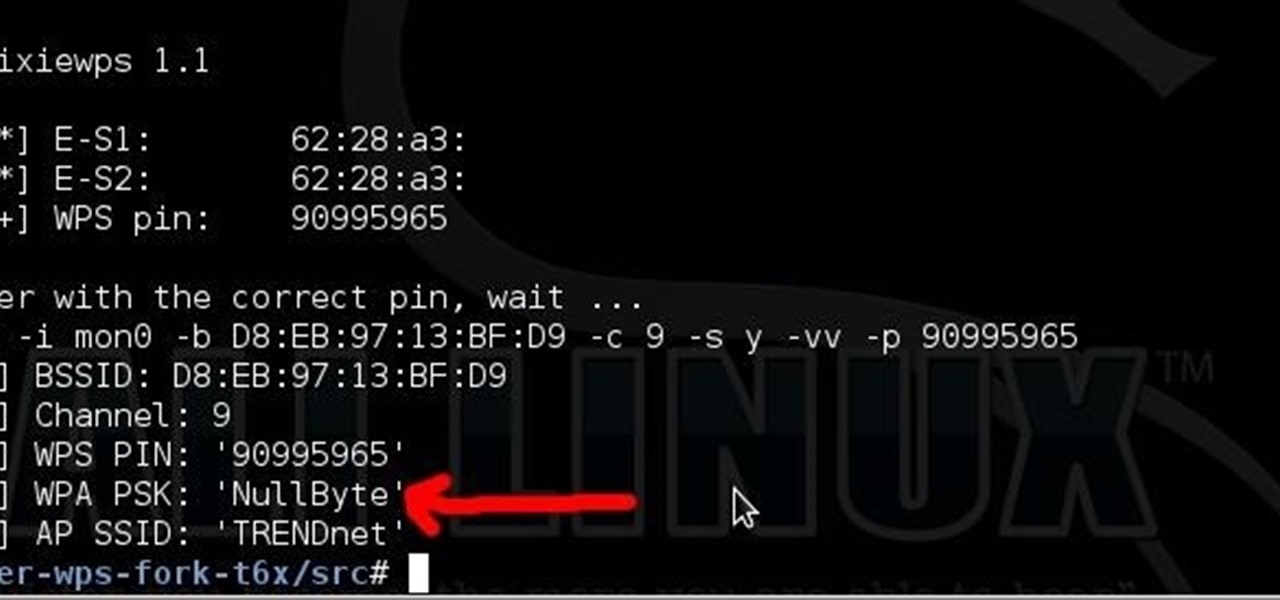
Long time reader, first time 'How To' poster. This tutorial has been highly requested. Here are the steps to perform a Pixie Dust attack to crack a WiFi password that has WPS enabled.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.

T-Mobile's "Uncarrier" initiative has done wonders for my wallet and my data usage. Before I had to deal with being throttled down to 2G speeds after passing my data limit, but thanks to their unlimited data plans, I'm free to use as much LTE data as I possibly can. The only downside is, when sharing data through a mobile hotspot (tethering), T-Mobile imposes a 5 GB limit (which was recently upped to 7 GB for some).

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

Snapchat developers insist that the app stay true to what its always been: a service for snapping and sharing self-destructing images. This belief is further hit home with their strict 31-character text limit, which some people refuse to abide by. Namely, Snapchatter Shayne Skellett.

Welcome back, my novice hackers! Reconnaissance is one of the most important preparatory steps to hacking. As I have emphasized many times before here on Null Byte, you must know the operating system, the ports, the services, the applications, and sometimes even the language of the target to be effective. If you haven't taken the time to gather this info, then you are likely wasting your time.

Welcome back, my rookie hackers! Now that nearly everyone and everyplace has a computer, you can use those remote computers for some good old "cloak and dagger" spying. No longer is spying something that only the CIA, NSA, KGB, and other intelligence agencies can do—you can learn to spy, too.

Welcome to this short and easy tutorial on hacking and DDosing (is that even a word I don't know) anyways lets get started

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

As if you needed another reason to lock down your Facebook profile, the company's sketchy new partnership with data mining firm Datalogix is geared towards giving advertisers more information on what you're doing—even when you're not online. It's just not enough that they can target ads based on your preferences, now they want to know how those ads are influencing your buying habits in the real world.

In this video, we learn how to calculate a limit at infinity with a radical. The idea is to take out the higher power of 'x' in the denominator first. If the x squared is under a radical, take that out so you're left with just 'x'. After this, divide every term by 'x'. Once you are finished with this, you can rewrite the equation. Next, you will use the rules of math to find the answer of the equation. This is hard math to do if you aren't used to it! Make sure you practice with the samples i...

How to speed up your internet connection

Are you slightly rusty on your math skills? This video demonstrates how to find the volume of a sphere with a given radius. The first step is to sketch a solid and cross-sectional view of your sphere to get an understanding of the process to come. Next, find a formula for the area of this cross-section. Third, find the limits of integration. This will allow you to take the area of each cross-section in the sphere, not just the singular one you are viewing. Lastly, integrate this formula from ...

tasktutorial shows you how to create a limited offer button, using Photoshop with this high resolution and informative video. You can learn how to create these buttons, using step-by-step instructions. You never have to leave the comfort of your home, and it's free to learn. This button is a must when you need to bring attention to a customer on your web site, to show a special offer that you may be having. With a variety of layers that must be used, this tutorial still makes it easy.

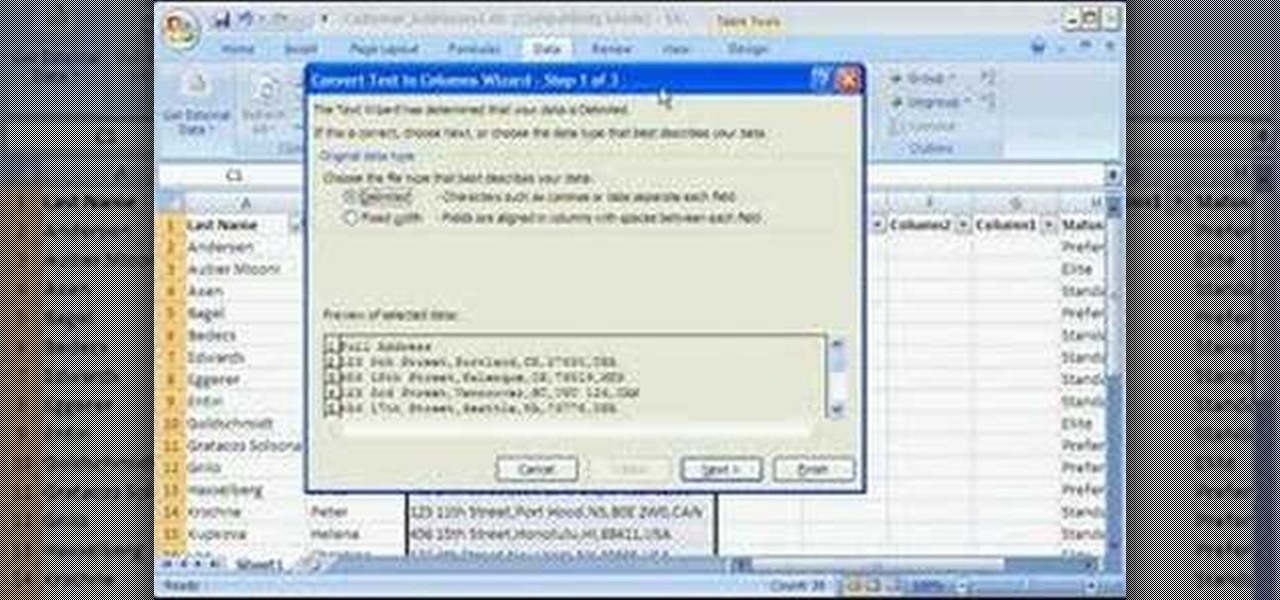
Storing information, such as a full address, in one column can limit what you can do with that information. For example, you can't easily filter or sort by part of the address, such as country/region or city. However, if you break up the address into its parts — street address, city, state/province, postal code, country/region — one for each column, you can remove those limits. Watch this instructional video to see how to use the Convert Text to Columns Wizard to automatically break up a sing...

With a cheap computer, smaller than the Raspberry Pi, an attacker can create a remote hacking device. The device can be attached to a target router without anyone's knowledge and enable the hacker to perform a variety of network-based attacks from anywhere in the world.

Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

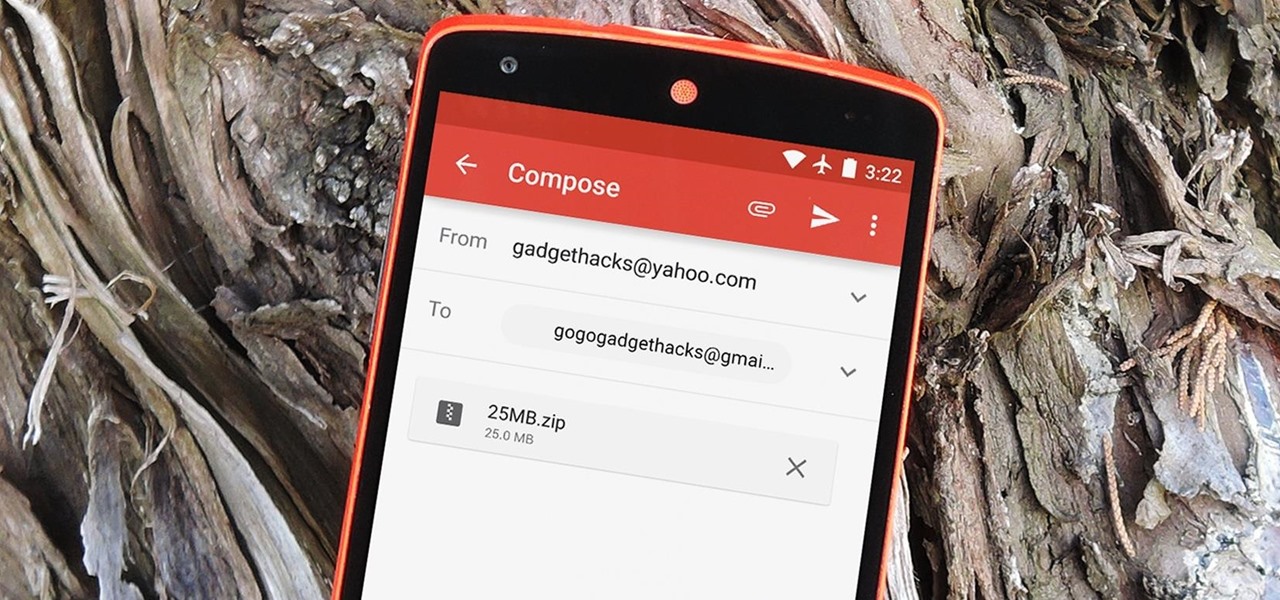
The Gmail app recently became stock Android's central hub for all of your email accounts. Instead of being limited to just Gmail accounts, the app can now handle POP3, IMAP, and exchange service email accounts, making it a one-stop shop for all of your emailing needs.

Urgot is a unique champion who can deal out high amounts of damage early in his game, and eventually evolves into a tank/assassin hybrid who can be sent after important enemy targets. Here's a guide for building and leveling Urgot to take advantage of his capabilities to help your whole team.

Lady Gaga is definitely in shape. No one can deny that. But how does she do it? How does pop music's most popular artist stay in perfect shape? How does she get those great looking abs?!?

Shane goes into detail on a specific type of boof in which the paddler comes across the drop with angle and boofs into an eddy.

They are after you from all over the globe. Looking for ways to exploit you. Ways to hurt you. Not political terrorists, but rather "info terrorists." Each month thousands of websites get hacked into and have hidden links inserted into the pages by people wanting their spam sites to rank highly in the search engines.

Suspect that your bovine (bull, cow) is pregnant. Well, there's only one way to be sure. Put on a plastic glove and insert your hand into the rectum, with your fingers together. See how to find out if your cattle is pregnant with help of this video tutorial.

Don't hide in a cave when the market is down. Find stocks that will pay off when the bull makes its return.

The Capra Demon boss fight in Dark Souls is incredibly frustrating. You're limited on space and you have to deal with the dogs as well as the demon. If you want to find out how to defeat the Capra Demon, this IGN guide should help.

Short hair is a breeze to take care of most of the time. Minimal shower time, minimal styling - you get up out of bed and you're good to go.

If iMovie 11 is what you use for your Mac movie editing, you'll want to check out this how-to and learn to make the most of iMovie 11's titling abilities. While the set of iMovie 11 titles is more limiting than most video editing tools, you can use some simple tricks to place and style titles. Some of the title options allow you to position the text by simply inserting lines and changing font properties.

No matter how desperate they are for work, most actors will not let you crush their heads for your film. The potential for career development afterwards would be limited. This video will teach you how to crush a head with special effects for a film and then how to use three-point lighting to make your films look more professional.

During Thanksgiving, cooks, who are often limited by time and oven capacity, must choose between classic Thanksgiving side dishes like mashed potatoes and more interesting, novel ones like Italian stuffed pasta shells. Have both a classic dish and a new one by checking out this video.

Are you under a backbreaking amount of debt? In this economy, we don't blame you. If credit card bills, mortgages, and bank loans are making you want to crawl into bed and pull the covers over your face, then check out this video to learn how to consolidate debt.

Super Scribblenauts is truly a game only limited by your imagination, but every now and again you may run into a puzzle that you can't quite solve. In this video you'll get all of the solutions to the puzzles in Constellation 9, covering levels 9-1 through 9-10

Chicken is one of our favorite foods because there are an infinite number of ways to prepare it. And making chicken recipes on the go is a cinch.

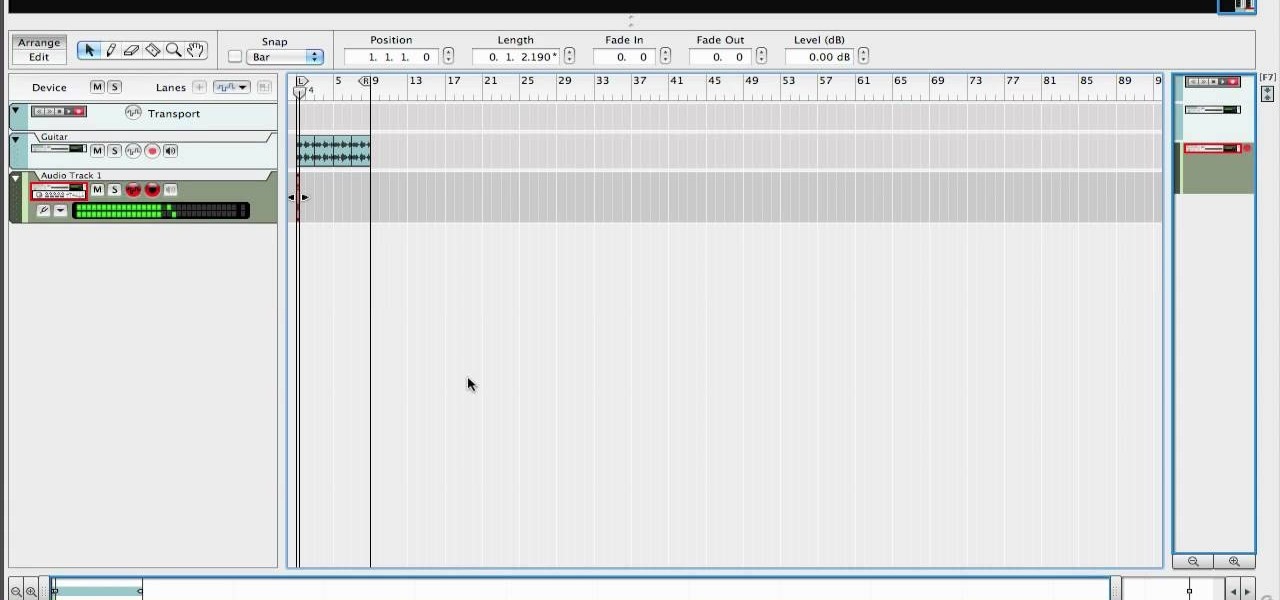
The time stretch feature on Reason's music-editing software can create some very interesting sounds when you push the program to the limits of what it can do. Slow down or speed up your clips dramatically and get an entirely different sound.

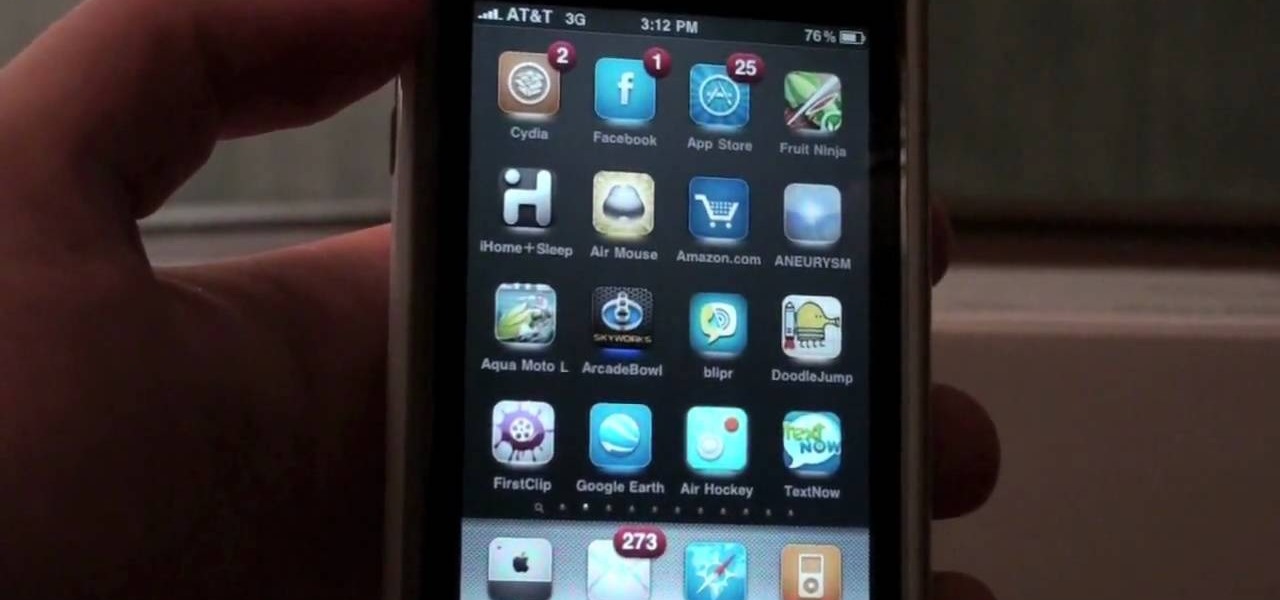
TextNow is a great App for the iPhone that allows you to, for a $1 initial fee, send unlimited text messages to any other TextNow user without using any of the precious limited texts on your AT&T plan. The App is very easy to use, requires only a modest amount of additional money to keep using it forever, and will probably wind up saving you money in the long run by cutting down your monthly billed texts.

Google Voice is the newest release from the experts at Google. Google Voice is a low-cost Internet phone service that redirects calls to your home phone and works over your WiFi connection. This service is very exciting and useful for those that are looking to save some money on long distance. Google Voice was in limited use for a while and is now available to everyone, so check out this clip and learn how to use it!

Are you trying to make it in Hollywood? You won't get very far as an actor without an agent. Most auditions are limited to those with agents only, so how do you get one? In this clip, actor Shaun Pilkington tells you about the various ways to find representation in Los Angeles. Follow these tips and you will be heading out on auditions in no time.

Cooking with a budget can be a challenge. But just because money is limited, that doesn't have to be true for flavor. This eggplant parmesan can be made for only six dollars but it will taste like it came straight out of a fine restaurant. This video will show you how to cook a low budget eggplant parmesan.