Pretty Little Liars is the newest part of the increasingly puzzling lineup of shows on ABC Family that seem to be creating a new demographic to target as they go along. The girls on it are very pretty, and this video will show you how to create a makeup look inspired by the show's star Alison DiLaurentis.

THis video from accredited 3D art instructor Andrew Klein covers how to create symmetrical and asymmetrical blendshapes using the 3D sculpting program Zbrush. This is a fairly complex process, utilizing transpose masking features, move brush, smart resym, and morph target tools to accomplish its goal of creating a really cool animated 3D mask.

In this video tutorial, viewers learn how to properly shoot and sight in a compound bow. It is recommended that users use a release. Your body should be perpendicular to the target. Hold the bow vertically, and hold it with a relaxed and secure grip. When you are ready to begin shooting, learn a technique that will help you relax and steady the bow. When you draw the bow string back, you should be looking through the peephole on the bow string and where the target and pins come into view. Thi...

In this video, Tom Leese, Director of Instruction at Angel Park Golf Club, gives pointers for your pre-shot routine in golf. Important in the transition from the practice range to real games, your pre-shot routine helps you get situated and ready to play real competitive golf. Tom explains, first, how to set your lines, taking a straight and purposeful line down course where you want your ball to go, and remaining fixed on it, as you approach your tee. Then, when positioned at your ball, he t...
In this Photoshop CS3 tutorial you will learn how to use the knockout feature. This advanced masking technique allows you to move a targeted layer around, revealing the layer underneath. This video will show you how to reveal a creepy skeleton under a monster werewolf right in Photoshop. This classic technique lives again! Learn the subtle qualities of the Deep, and Shallow, Knockout feature in Photoshop.

Hip flexors are important muscles to target when weight training to build functional strength in the legs. Learn how to do hip flexor exercises in this strength training video. Take action: knees to chest exercise targets core, hold weight between feet, raise knees as high as you can, start in push up position and bring alternate knees to elbows, and work for quick reps and endurance. Tom Clifford, the instructor in this how-to video, has a degree in physical education, fitness and health fro...

Katherine and Kimberly Corp show you how to do a ten-minute (1o min) pilates arm workout using stretch bands. This workout targets every major muscle group in the arms and helps maintain alignment and ab strength.

In this video tutorial you are told how to use the Wagon Wheel Cue Ball Control training method. This is called Wagon Wheel because each target ball is aligned to RESEMBEL the spokes of a wagon wheel. Set your cue ball and your object ball in the same position each time. The objective is getting the cue ball to one balls width of the target ball. Using THE FOLLOWING cue ball, direction and speed. By using a piece of chalk the instructor helps line up the balls. By using either a quarter stick...

Component 1. Frame And Posture. The benefits of dance shoes never outweigh the benefits of proper spin technique. Your body should be straight lower abs and stomach should be tight. Your arms are in proper position. If you lift your hand it should be in 90 degree angle.

Want to be able to hack into a computer remotely? This method takes a little extra time and cunning to set up, since you will need to first install the ShowMyPc program on your target computer. Once you have installed this program, however, you will be able to go to the website ShowMyPc.com and be able to see what your target has been up to. Even better, you can use that computer and the files on it as if it were your own desktop!

What's in a name? Quite a lot. Learn how to choose a good one that targets your desired demographic. Whether you're considering the possibility of starting your own Pilates studio or already have one and just need a little help tackling a particular pedagogical problem, you're sure to be well served by this free video lesson from the folks at Balanced Body Pilates. For more information, including a comprehensive overview, watch this video guide.

Party poppers are magnificent. They can be used for a plethora of pranks— basically, any prank where the victim / target has to open something. You can use party poppers on practically any household item, but this video covers the much used dental floss container. The exploding floss prank is easy to do yourself, and requires only the floss container, the party poppers, scissors, and a screwdriver. Once your prank target goes to use their floss, they'll have quite the grin.

In this video tutorial, viewers learn how to shoot a compound bow. It is deeply recommended that users who use a compound bow should have a release. Put your arrow on the string and push it in until you hear a click. Now hook the release into the D-loop. Your feet should be shoulder width apart and the tips of your feet should be on the target line. Now look at the target and pull back the bow. Your hand should be at the point of your jaw, arrow at the corner of your mouth and string on the t...

In this video tutorial, viewers learn how to avoid a bad finish to cure a golf push shot. Usually, when players make a swing for the ball, their arm separates from their body. This will take the club to the right of the target and as a result, pushes the shot. To correct this, connect your left arm to your left side as you make a swing. This will allow the club to stay with your turn and go down the target line. This video will benefit those viewers who enjoy playing golf and would like to le...

In this video tutorial, viewers learn how to burn fat with a cable workout. These exercises will require a cable machine. There are four exercises in this workout. These four exercises are: cable wood chop, reverse wood chop, one arm cable row and exercise ball cable crunches. When performing these exercises, do not use a heavy weight. These exercises mainly target the abdominal and core muscles. They also target biceps, obliques and back muscles. This video tutorial will benefit those viewer...

How to aim your shot in World Golf Tour in four easy steps. When aiming for a shot, simply click the target and drag it on your desired location. The Yardage Indicator will change as you move the target closer or further. If it turns red that means that you positioned it outside the maximum carry distance for that club. You can also consider changing your club. Hit the Space Bar or click on Zoom to give you the aerial view to get a closer look and adjust for a precise aim. Be sure to take the...

Kathy Kaehler, author, celebrity trainer, spokesperson and mother, gives us a rundown of the best exercises for fellow women and moms on how to target their belly fat and love handles, and specifically the best ways to tighten these areas. Kathy first does advise us that if you're going to be targeting like this the most important thing first will be cardio and general fitness. Then, she offers us first the side plank, where you place one elbow to the ground, lying on your side, and then elev...

The obliques exercise is a classical pilates exercise which targets the abdominal muscles to flatten the stomach and strengthen the core. Keeping the elbows wide helps keep the shoulders down and increases the rotation in the trunk, which helps shrink your waist. Be sure to stretch your legs fully each time and stop the knee at 90 degrees of hip flexion to encourage greater strengthening of the abdominal muscles. Watch this how to video and you will be strengthening your obliques with pilates...

In this video tutorial, Chris Pels will show how to deploy a web site using the Copy Web Site Tool in Visual Studio. First see how to connect to a remote web site and deploy an entire site to the target location. Next, learn how to synchronize an entire source and target web site. In addition, see how to copy and synchronize individual or groups of files including how the Copy Web Site tool provides status indicators of differences between files. As part of this process see how the tool provi...

UAC is something we've all dealt with on Windows, either as a user, administrator, or attacker. It's a core feature of the Windows security model, and for the most part, it does what it's supposed to. But it can be frustrating as a hacker when attempting privilege escalation, but it's easy enough to bypass UAC and obtain System access with Metasploit.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

It's not uncommon for hackers to attempt to move laterally between devices in proximity of a compromised device to maintain a prolonged presence in the network. Malware utilizing USB flash sticks to self-replicate and compromise air-gapped machines isn't a new concept.

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.

With the release of the Mirai source code, botnets are back in a big way. In the early days of botnets, zombies (infected hosts) would report to IRC (Internet Relay Chat) channels for CNC (command and control) instructions. Modern botnets have evolved, but they continue to use the same concepts as their predecessors.

I mentioned in 2015 I wanted to start a 'DoXing' series, and since I havent seen this on Null Byte, I am now going to introduce this to the community.

Since The Guardian published leaked documents exposing the depth of the NSA's spying powers, many people who've never put much effort into protecting their privacy are finally starting to pay attention. Evidence of public opinion concerning PRISM can be seen from the rise in traffic for pro-privacy sites like DuckDuckGo to the petitions demanding that the program be scaled back or done away with altogether. Some would argue that you waive your right to privacy by signing the terms of agreemen...

Welcome back, my nascent Hackers! In my last blog, we looked at a passive way to gather information necessary for a hack. The advantage of using passive recon is that it's totally undetectable, meaning that the target never knows you're scouting them and you leave no tracks. The disadvantage, of course, is that it's limited to only some websites and not entirely reliable.

Starting a business has to involve a desire to benefit someone else other than you. If all your reasons for starting a business are to benefit you, chances are good that you have missed the big picture. At least one reason you have to want to stat a business needs to be to help someone else. Either use proceeds from the business to help a charity of your choice or to solve a problem or provide a solution to a need for the target group that your business serves. Focus on one issue to start wit...

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

A lot of time can be wasted performing trivial tasks over and over again, and it's especially true when it comes to hacking and penetration testing. Trying different shells to own a target, and testing out privilege escalation commands afterward, can eat up a lot of time. Fortunately, there is a tool called One-Lin3r that can quickly generate shells, privesc commands, and more.

So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit makes it easy to perform local privilege escalation and get root with its exploit suggester module.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

Websites and web applications power the internet as we know it, representing a juicy target for any hacker or red team. TIDoS is a framework of modules brought together for their usefulness in hacking web apps, organized into a common sense workflow. With an impressive array of active and passive OSINT modules, TIDoS has the right instrument for any web app audit.

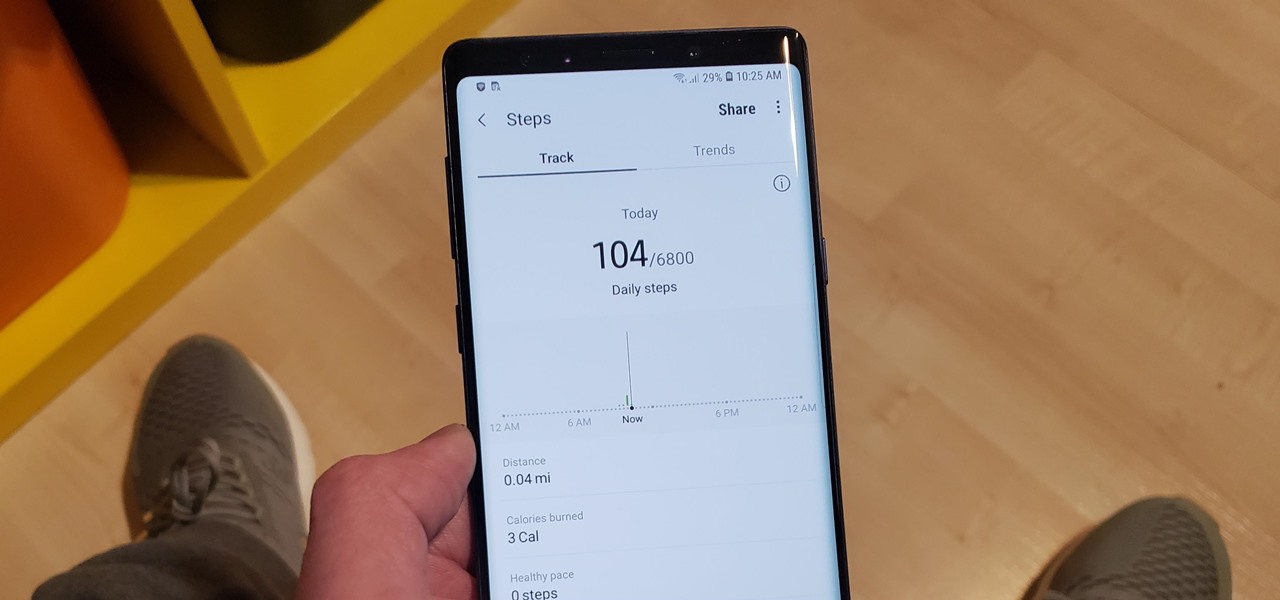
The quality and length of your sleep will almost always dictate how the rest of your day unfolds. Sleeping fewer hours increases your chances of spending the day in a tired and cranky state, while having a restful night's sleep contributes greatly to being alert and productive. Luckily, if you want to track your sleep patterns to figure out how you can improve your circadian rhythm, Samsung Health has you covered.

Once known as S Health, Samsung Health has become one of the most comprehensive health apps available for Android. In fact, we all can benefit from the features the app brings to the table — whether you're a marathon runner or a couch potato. If you're in the latter category, the app has a simple feature that can nudge you towards becoming more active.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.