Using Shazam has quite literally spared me hours of searching the internet for the name of a song I briefly heard for a few seconds. At WWDC, it was announced that iOS 8 now has Shazam technology integrated into Siri. What makes it even cooler is that you don't even need the Shazam app on your device.

Welcome back, my neophyte hackers! Many newbie hackers seem to be confused regarding the process or methodology to employ a successful hack. Most want to simply go straight to the exploit without doing the due diligence to make certain that the hack will work and you won't get caught.

The term "selfie" is taking the world by storm. Having been around since 2002, the slang word for "self-portrait" went into hyperdrive thanks to the addition of front-facing cameras on mobile devices. It's even popular enough to have been included in the Oxford Dictionary, and to have broken Twitter (thanks to the Oscars selfie taken by Ellen DeGeneres).

The internet was ablaze this week after it was found out that evasi0n's newest jailbreak for iOS 7 secretly came bundled with a highly obfuscated Chinese app store. The application, called Taig, was filled with pirated software and was rumored to have permissions capable of tracking your information and sending it elsewhere. It was reported that the team at evad3rs financially benefited from this move, netting them a very high six-figure number close to a million dollars. The controversy incr...

Hey dolls! I love my new infrared hair straightening iron by MUK. I thought it was a gimmick but really, the technology makes sense. I love that you can adjust the temperature unlike GHD straighteners. So if you if have fine hair you can turn it down and if you have thick crazy hair like me you can turn the bad boy up!

Every single year technology companies have a little bit of fun on April Fool's Day by releasing absurd, yet almost believable stories of some new product or feature. Yesterday, Google publicized the release of Google Nose—a new project in beta—that supposedly allowed users to sniff a variety of smells through their smartphone screens.

Google Glass, the augmented reality head-mounted display, has sent ripples through the technology world ever since its inception in 2012—even warranting Time Magazine to recognize it as one of the "Best Inventions of the Year 2012". Today, Google announced that it’s now opening up an exclusive opportunity to become a Glass Explorer. What this entails is that if you're chosen to be a Glass Explorer, you'll have the opportunity to purchase one Glass device, long before it becomes available to t...

It's a controversial headline, I know, but bear with me and I'll explain in due course. Disclaimer: I was once a child, and I played lots of video games. I didn't look anything like this child.

No matter how advanced technology gets, there will always be room for classic video games in the hearts of nerds everywhere. Mini arcades became very popular, as they allowed users to take arcade games on the go. As Game Boys and other mobile gaming devices appeared, the mini arcade slowly disappeared. Well, believe it or not you can combine the best of both worlds! Metku user Japala wanted to make his old Game Boy Advance SP "look cool again," so he turned it into a mini arcade cabinet.

While graffiti may never be fully accepted by the masses, it has already become a very large medium for creative artists across the globe, who make mundane and austere cityscapes a little more interesting for the rest of us. Walking past this Banksy stencil on my way to class (at UCLA) made my day. Art like this can cause people to stop and appreciate the otherwise boring and blank walls that surround the city. It can stir up artistic feelings, pensive thoughts, and other emotions stored insi...

Keys are on the way out. They're clunky, take up precious space, and slow you down when you have tons of identical-looking gold ones on your keyring. Everything we can open with keys can now also be opened with wireless technology in just a click—so why use keys anymore? Sure, you can pay hundreds of dollars for an automated lock system on your house—but why do that when you can build it yourself!

Ever since the mid-2000s, there's been a lot of bandying back and forth on the Internet over what exactly Steampunk is. Some people think it's one thing, others another thing, and some think that it shouldn't be defined at all.

As a technology writer, phone screenshots can pile up on your computer in no time. Testing out different apps, showing buggy software, and doing step-by-steps can lead to a plethora of mobile screenshots piling up on your computer's desktop. The problem with my screenshots is that they save as photo.png or photo.jpeg, as do many of my other photos. If I haven't finished a project or article, I tend to move them to different folders to save them for later. After a while, the screenshots begin ...

Thanks to Flutter, it's now possible to control the music on your computer simply by making a few hand gestures. The app is available for both Windows and Mac and uses your computer's webcam to monitor your hand movements. Through the use of a few simple hand movements, you can play, pause, forward or replay your music. Flutter works with iTunes, Spotify, Quicktime, MPlayerX and a few other programs.

We've all played with bubbles as kids, but I think most would agree that they're not exactly the most functional of objects. An international team of researchers made up of Yoichi Ochiai, Alexis Oyama and Keisuke Toyoshima wants to change that. They've figured out how to project both 2D and 3D images onto a micro membrane (soap bubble) using ultrasonic sound waves and a standard projector. The bubble is made of a solution of sugar, glycerin, soap, surfactant, water and milk. The glycerin and ...

Back in 2008, media artist Kyle McDonald created a 3D interface that could track movement, which he turned into a virtual Tic-tac-toe game.

Technology is awesome. You can use your iPad to record music or even turn your tunes into a solar system, but sometimes being plugged in all of the time can leave you nostalgic for simpler times. This new concept by Joelle Aeschlimann brings together the best of both worlds by turning your iPad into an old-fashioned, hand-cranked music box. The artist created three different music boxes, each one with its own unique song and visualization. The music boxes were made using wooden cylinders with...

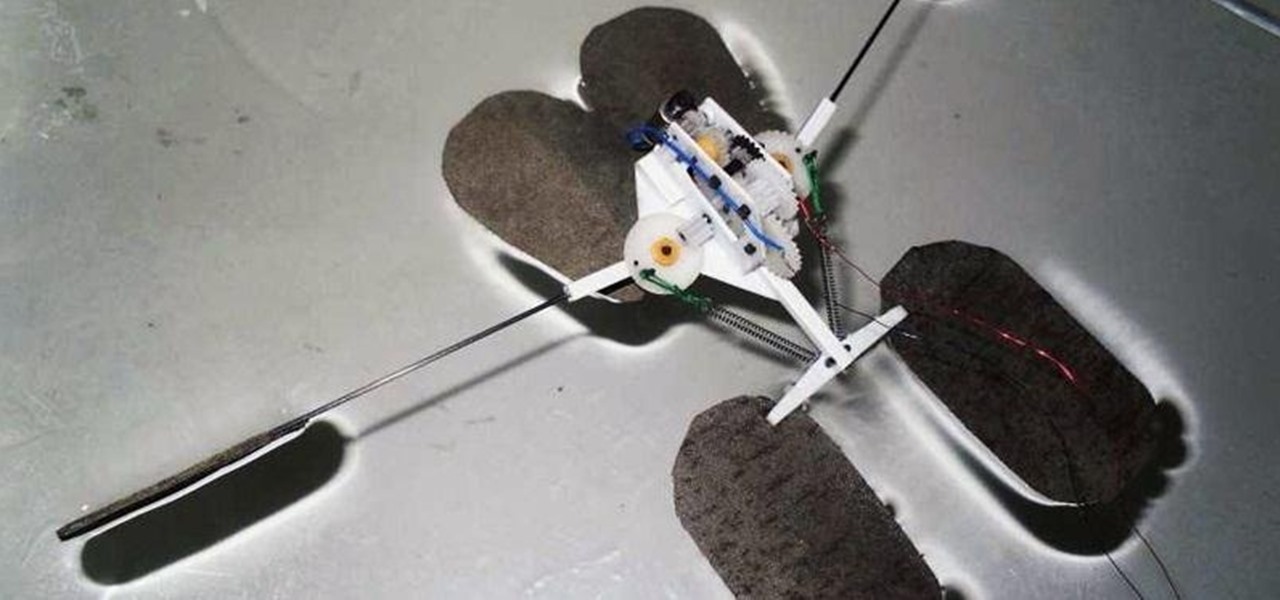
Gerridae—you've probably seen these weird bugs gliding across the surface of the water when you're out swimming or fishing. These insects are commonly referred to as water striders, or more cleverly, Jesus bugs, for their ability to "walk on water". It's a pretty cool trick, but what could it do for science, right? Turns out, quite a bit. Photo by felixtsao

Some of us use our smartphones for almost everything. Manufacturers know this, so they try to make their devices as convenient as possible to use, but sometimes that convenience comes with a cost to security. The very same technology that allows you to easily share music with friends and make purchases can also put you at risk. Photo by sam_churchill

Since the days of Archytas, rocket propulsion has been the Holy Grail of aeronautics. Thanks to Galileo's inertia, Newton's laws of motion, and the "father of modern rocketry," Goddard, space is not a complete mystery anymore. Rocket-powered aircrafts have evolved from the first liquid fuel rocket in 1926, to the Soviet R-7 which launched Sputnik, to NASA's Saturn V that propelled Apollo 11 to the moon. Today, even billionaire tourists can enjoy space, like Microsoft's Charles Simonyi and Cir...

Learn how to wait tables and do it well with expert tips and advice on customer service in this free waiter related video series.

In this two part Photoshop tutorial, Richard Harrington takes a look at the camera raw files and the camera raw interface. Many video professionals do not know much about the camera raw interface because it is a technology mainly used by digital photographers. The key advantage to using with a camera raw file is that the data is usually stored in the picture more than you can normally see in a single exposure.

People sometimes ask me about the IT industry here in the states. These folks are usually either trying to get into a certain field, or looking to switch or move into another one. Right now, you may currently be a Computer Science major that will be graduating shortly and are interested in the current state of IT security.

With the mass arrests of 25 anons in Europe and South America, and the rumors of an FBI sweep on the east coast of America floating around, times look dicey for hackers. Over the past few days, a lot of questions have been posed to me about removing sensitive data from hard drives. Ideas seem to range from magnets to microwaves and a lot of things in-between. So, I'd like to explain a little bit about data forensics, how it works, and the steps you can take to be safe.

Carol Baldwin-Moody of Wilmington Trust describes the challenges that are present in her line of work as senior vice president and chief risk officer. There is a strong legal backing to every major issue in today’s society. Baldwin-Moody has come across several scenarios that aren’t covered by the dated constitutional law in effect today. In past years, a risk officer was thought to be a management concept that would be useful, but not worth the investment. Lately, a risk officer career has b...

Lisa Nichols, contributing author of The Secret and one of the great inspirational speakers of our time, believes the best way to stay motivated when continuing your education is to “begin with the end in mind.” Pushing forward through challenges is what makes accomplishment so gratifying. Every accomplishment leads to personal growth. Nichols believes that making the completion of your degree “non-negotiable” means that you will not settle for anything less.

Welcome to the Google+ Insider's Guide to all things Google+. We're dedicated to keeping you updated with all the latest news, tips and tricks on Google+, and this official index will serve as a one-stop catalog of all our How-To articles, as well as all the news & updates we've covered over time.

noob - Short for "newbie." Someone with little to no experience or skill. In some gaming communities, there is fierce debate over the distinction between "noob" and "newb"—one being derogatory while the other simply indicates being a novice. While some may argue the semantic differences, "noob" is the most common spelling seen around the internet, for both purposes.

Description: Admit it, having thousands of valid email Ids give you the power to do anything! Such as adding thousands of friends to your Facebook, MySpace, Twitter, etc profiles or promoting your article or blog in just a single click and much more! But how do we do it? I searched all over the internet in a hope to get a perfect email producing software but ended with just two -

For those not used to it, working from home can be a difficult transition. Everything around you can be a distraction, and distance from your boss and coworkers means less pressure and incentive to get things done. So it's not surprising to see a major drop in productivity during a period of self-quarantine, but your phone can help you stay on track instead of sidetracking you.

If running out of battery while out and about weren't bad enough, the experience is a lot more painful if your iPhone has a semi-untethered jailbreak. With that kind of jailbreak, when the iPhone dies, all of the mods will be disabled after the device powers back up. Fortunately, instead of restoring your jailbreak and tweaks manually after recovering from a critically low battery, you can avoid it altogether.

The last time we heard from Meta, the makers of the Meta 2 augmented reality headset, things looked pretty bleak. Now, as several new facts have come to light, we have confirmation regarding the beleaguered company's fate: Meta is done.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

With the software installation out of the way, it's time to build the framework within which to work when building an augmented reality app for Android devices.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.

Nmap is possibly the most widely used security scanner of its kind, in part because of its appearances in films such as The Matrix Reloaded and Live Free or Die Hard. Still, most of Nmap's best features are under-appreciated by hackers and pentesters, one of which will improve one's abilities to quickly identify exploits and vulnerabilities when scanning servers.

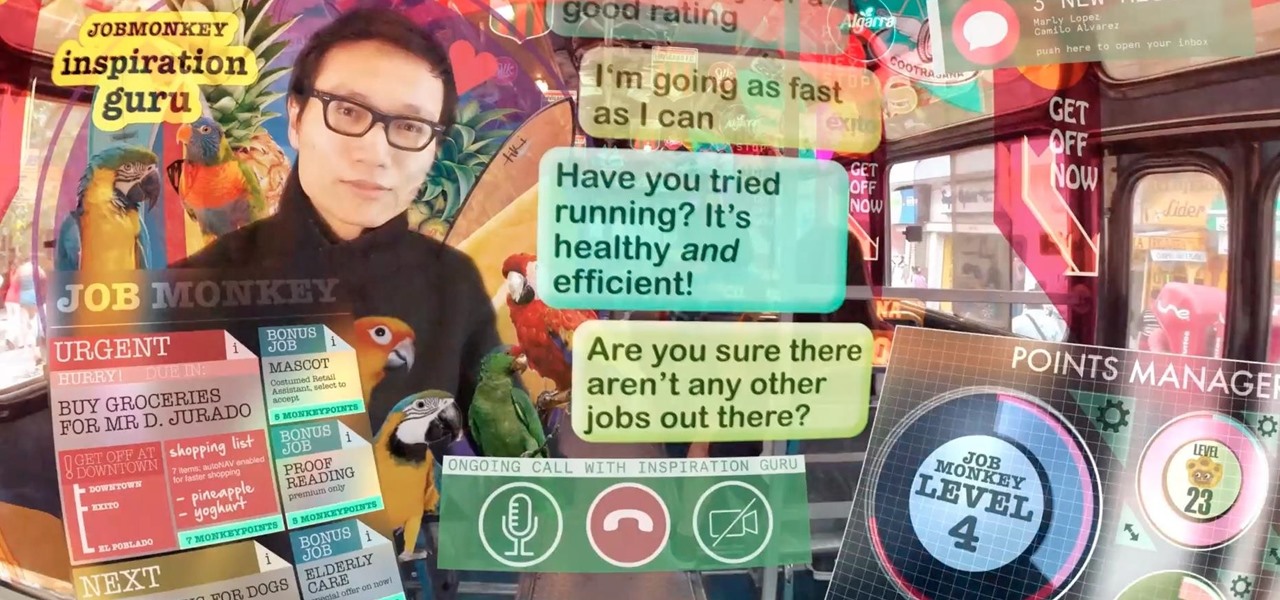
As augmented reality becomes more and more integrated into the mainstream, people have been wondering the future of AR is going to look like. Jay Samit has a pretty clear idea.

Whenever I went to the grocery store on a mission for blueberries, I'd inevitably find myself staring at these weird little tomato-looking berries... and wondering what the hell they really were. Tomatoes? Berries? A weird science experiment? Then, I'd set a pint of blueberries in my cart and carry on, forgetting about them for the time being.

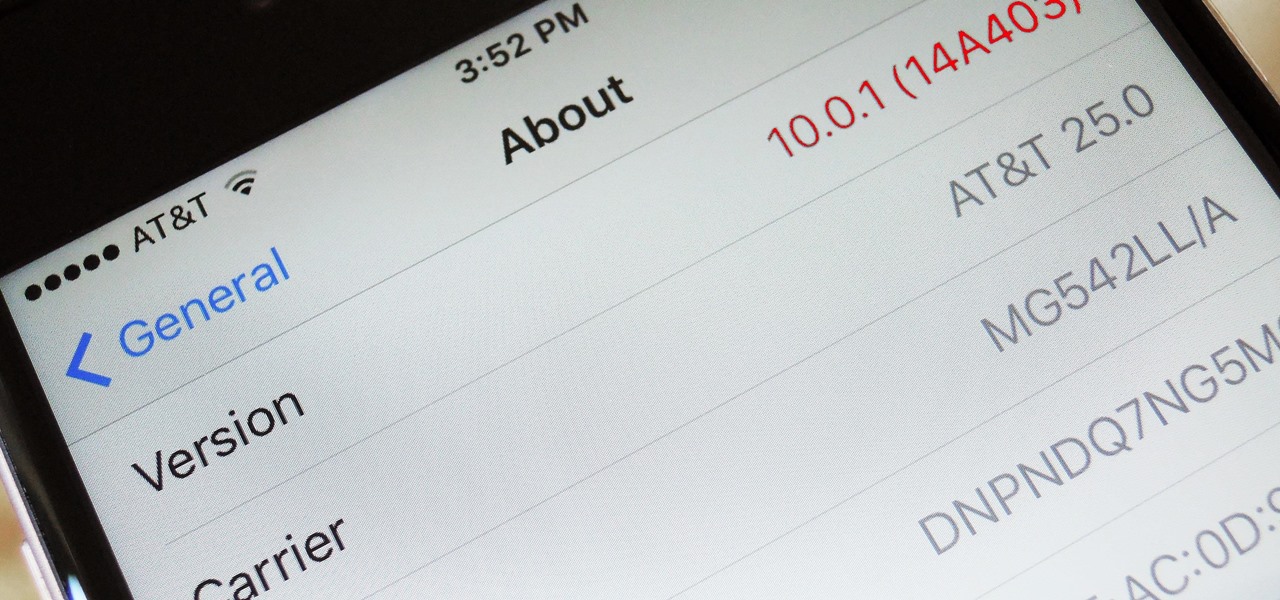
When a new version of iOS comes out, everybody gets caught up in the craze of finding features and playing around with new functionality. But this generally leads to a lack of coverage on the finer aspects of the update—things like bugs, minor tweaks, and pain points that users discover along the way.