Ever since high school, I've been preparing my own taxes. Each year it gets more and more complicated, which results in me filing later and later, avoiding it until I have the time or just can't wait any longer. I even resorted to using TurboTax online to help do some of the grunt work for me these past couple years, but that hasn't stopped me from being lazy about it. I have yet to file my 2010 taxes, but I will very soon. Tomorrow, in fact—before TurboTax raises their prices.

Tired of touch-tone hell? Get human with our cool phone hacks and cheats with the tips from this how-to video. Become a life hacker - we'll show you how to find phone numbers, cheat the computer and hack the call center system with our hacking tools. Watch this video tutorial and learn how to hack a call center telephone system. Hack a call center telephone system.
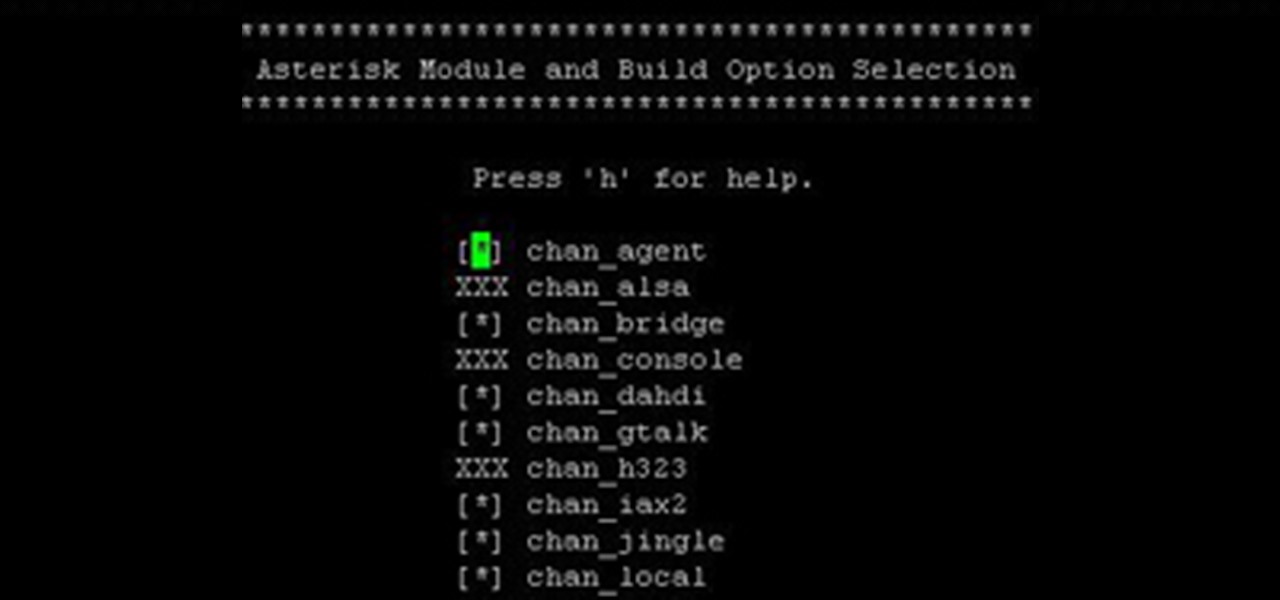
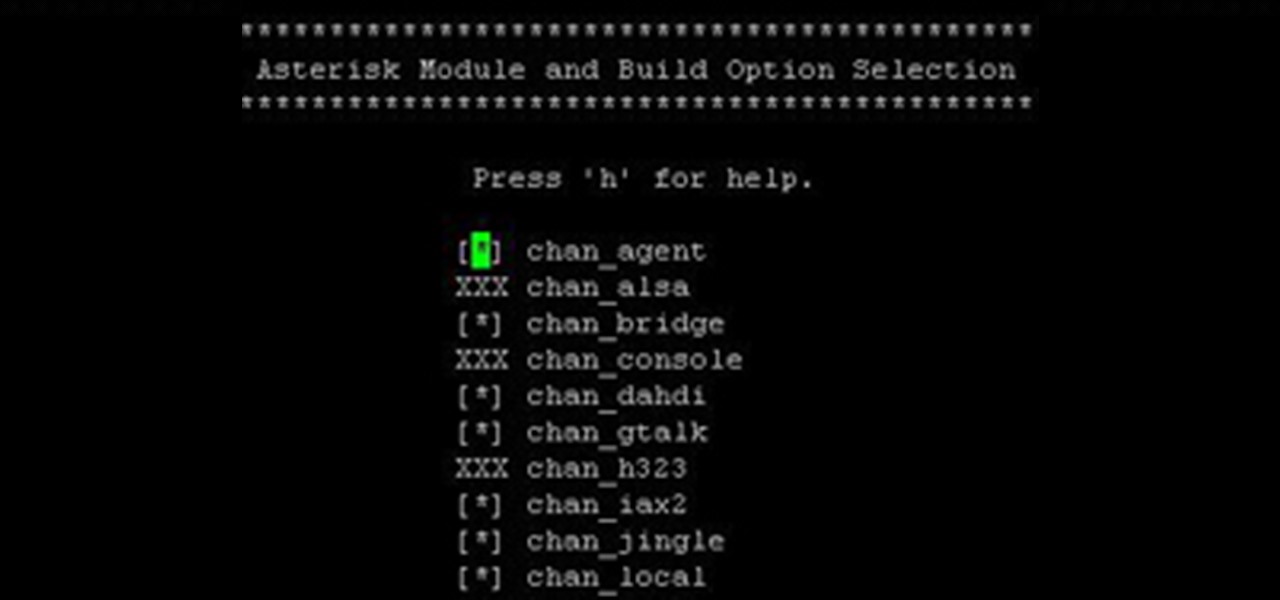
Over the years, I have enjoyed playing with Asterisk. I have found Asterisk to be extremely powerful and fun to play with. There are several books and many scattered how to articles out there, but most are outdated and the information required to build Asterisk from beginning to end can be a bit daunting. I wanted to combine all the steps into a single article and share my experience with everyone. If I have left out any steps please let me know.

If you've read my darknet series, you've probably got a pretty good idea of what I2P actually is and is capable of. One of the features of I2P is that it's designed with P2P file sharing in mind. Using a built-in service called I2PSnark, you can host and seed torrents quickly and easily!

Want to stick it to your mobile carrier by porting your cell number to Google Voice? Now you can! On Wednesday, January 19th, Google Voice began allowing select users to transfer their personal numbers to Google Voice for a one-time fee of $20. Though the feature is still in limited release, Google has stated that they intend to make the feature available to all Google Voice users "in the near future." Terrific, right? Not entirely!

No Time To Explain is the first game by two man indie developer tiny Build Games. It's a fun and very stylish platformer in it's own right, available for $10 from the tiny Build website. Articles about the game on RockPaperShotgun, Destructoid, and other prominent PC sites helped it develop substantial hype and raise more than $26,000 via Kickstarter to fund development.

Every key on a telephone keypad has its own sonic signature, a sort of calling card composed of two distinct tones: one high, one low. While it's easy to tell the difference between the individual pitches in a single row—see, for example, this article on using your cell phone as a musical instrument—, it's often difficult to differentiate between notes within the same column. Unless, of course, you outsource the work to a computer! Which is what Uruguayan hacker [Charlie X-Ray] recently set o...
HoloDecon Tecnology directly afects our perceptive capacity, influencing the construction of the oniric sourronding , built in the alternate hyperrealist narratives

Centerfold Hope Dworaczyk Will Jump Off Page Via AP

Texas based photographer Adam Voorhes takes four objects (telephone, frog, gun, etch-a-sketch) and dissects them for his photo essay entitled Exploded. The frog in particular looks like an illustration, but is indeed a photograph.

Have you been caught eating the cookies that were left for Santa? That's easy to explain, but what do you do when the doubt begins to rise in your child, rendering them dubious about the authenticity of everyone's favorite childhood lie?

According to the UK's Daily Mail, a group of ladies have lovingly knitted their entire village. "...A small group of very twinkly ladies started 23 years ago with a couple of cottages and some pigs, and ended up creating more than 60 properties, complete with wheelie bins, outdoor loos, gas tanks, cars in the driveways and even a smart red telephone box."

Hot Sauce Take water and hot sauce and cover your hands.

So, you just bought Photoshop. It's time to familiarize yourself with the rudimentary tools. Let's start at the very beginning!

Remember what life was like before your iPhone? Before there were palm-sized smartphones with seemingly endless features, there were phones like Motorola's RAZR that peaked with its embedded camera. Before that, there were simple flip phones with texting capabilities, bulky two-pound Gordon Gekkos—even briefcase phones.

If you're a diehard Apple fan, chances are the new iPad 2 caught your eye, stole your heart and emptied your wallet. Who couldn't resist the sophisticated slim-body design or its fascinating new Smart Cover? Well—it seems nobody could. And if you were late to jump on the bandwagon, you're still probably cleaning that dust out of your mouth because it took off without you—leaving the latest and greatest Apple gadget out of your reach.

Are you the expert hacker we're looking for? Do you have a great idea for an article on Null Byte? Do you have a passion to write, and more importantly... teach?

Lost the product key for your game? If you have to reinstall the game and don't have that key anymore, you're out of luck, especially if you didn't "buy" the game. But never be in fear of losing product keys again with today's Null Byte, where we'll be practicing a little bit of mind-kung fu.

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

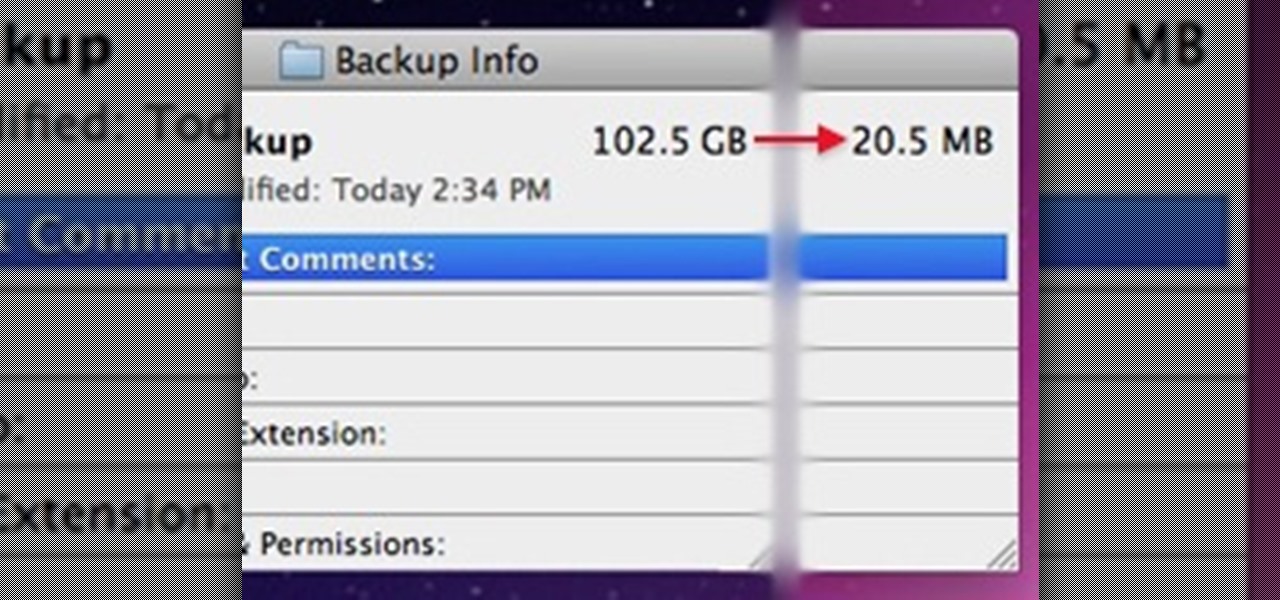
By now, you probably know that your iPhone secretly tracks and stores the locations you've visited in a backup folder on your computer's hard drive. The files are unencrypted, which means anyone with access to your computer or device can retrieve the information, which is downright scary. But Pete Warden and Alasdair Allan are making it fun with their iPhone Tracker application, which lets you map out everywhere you've been with your smartphone.

Sounds like a false promise à la infomercial or typical spammy web headline—how can a 4.8 ounce gadget aid in weight loss? But, in truth, "who" better to act as a dedicated personal trainer and nutritionalist than the iPhone? The smartphone is completely and utterly tethered to the daily life of the average middle to upper class American. It's reliable and exact. All it needs is a charged battery, the right app, and of course, as with every diet and fitness regime, a user with unwavering self...

Outside the realm of politics, where opposing sides are quite passionate and quite disagreeable, there are few areas in our society quite as divisive as Twitter. People who like Twitter love Twitter and are relentless in trying to co-opt the people they know into joining (this is both altruistic and an unsubtle attempt to boost followers).

Back in the eighties, I used to hate television commercials, but I eventually got used to them. Had to, in order to enjoy my favorite shows. Then, the increasing number of billboard ads annoyed me in the nineties. They followed me everywhere I went—no escape—persuading me to buy the newest whatever. It seemed like Big Brotherism—like They Live. But, I got used to it. When I finally entered the digital age and became a web addict, I was peeved at the constant sight of online ads everywhere I v...

With FarmVille being one of the hottest Facebook games on the market, it's no wonder it's the primary target for scams and virus downloads. Anyone playing FarmVille is at risk, but the primary targets are those looking to improve their gameplay and build their farms and neighbors up. These "farmers" are the ones seeking quick hacks and cheats.

You walk over to your laptop, wiggle your mouse to wake up the screen, then fire up your browser to come visit Null Byte. Catching the article about Anonymous and how they presumably will not take down the Internet, you find yourself wondering... how would someone take down the Internet? Could they even do it?

Social engineering is described as the clever manipulation of the natural tendency of human trust. All of the passwords, locks, and encryption in the entire world are useless against a good social engineer who can charm or trick you into giving it up.

If you're interested in bypassing Windows and Linux passwords, there is a great tool from the good people at Kryptoslogic. Have you ever forgotten your administrator password? Have you ever bought a used computer with a password on it? Well, Kryptoslogic have created a boot-disc call 'Kon-Boot', which allows you to bypass any Windows 32 or 64 bit OS, as well as Linux passwords. There is both a paid and freeware version available.

We have no control on the weather yet it is a part of our lives which influence what we do, what we eat, what we wear and many times where we live. How did people predict the weather before there was the Internet, television, radio or the weatherperson with all of their gadgets?

So, you scratched up your $500 Adobe CD and now it's unreadable. You could go buy a new one, but you already purchased it! Searching The Pirate Bay and downloading some Adobe software can usually be easy enough, but what should you watch out for?
International Pet Travel: Taking Your Pet Animal to a Foreign Country If you are taking a pet to another country (permanently or for a visit), contact that country's consulate or embassy for information about any requirements that you must meet. A list of consulates can be found at Foreign Consular Offices in the United States