Introduction In this post we will look at how to access a PosgreSQL database in your C/C++ application. It's not as hard as you might think, but you need to understand the procedure and the functions used.

If you tried visiting the Apple Store online this morning, you were probably prompted with the same notice as the one below, which lasted a good portion of the a.m. What could Apple have been doing to shut down their online store for so long?

Body hacks. So simple, so ingenious. They're the shortcuts in life. We love them, the internet loves them. Back in 2008, somebody named Alicia Goh wrote a friendster blog post that has been passed along far and wide. Her tricks of the body include quick solutions for an itchy throat, a stuffy nose, a dire need to pee, and more. My favorites:
You know it's crazy out there when governments start blocking social websites like Facebook, Twitter and even YouTube. But that's what happened in Egypt, when tens of thousands of anti-government protesters took to the streets on Tuesday (January 25th) in hopes of ending President Hosni Mubarak's 30 years of authoritarian power.

There's three types of animal lovers in the world. The first are your basic pet owners. The ones with a

In a recent survey of more than 5000 UK jobseekers by TotalJobs.com, it was found that 60% spend less than two hours working on each application following a job search, all inclusive of the time it takes to write a CV and covering letter, and to prepare for an interview.

Via Sports Game News By the time you finish reading this, you’ll agree with me on the thought that a coach will always be at the center of change. How to coach soccer is a feeling that is innate in a coach and he or she is a natural in it. But, a coach still needs to learn and become accustomed to so many other things if he or she has to shine in the field of coaching.

Life has always been complex and challenging. The challenges today are just different than what they were in the past. Nowadays instead of hunting and scavaging for food and living in the elements we’re bombarded with suggestions and demands from our highly sophisticated societies. How is it possible to find harmony amidst what are often contradictory messages?!

Good commentary can make anything interesting.

Make My Mondays Meatless! One day a week join in on cutting out the meat! This Presidential initiative revived by The Monday Campaigns in association with Johns Hopkins, rolled out this program to the Baltimore public schools, then San Francisco went meatless and now celebrity chef extraordinaire Mario Batali and his fleet of fabulous restaurants said I'll play too! Now you too can help fuel this fire!

DVice posts six of the world's most powerful telescopes and, man, they are HUGE. Check it out. The Keck I and Keck II

Watch this first 'tutorial'.FauxTo! Hoax! Con! May 28, 2008, this video was uploaded to YouTube illustrating the popcorn popping power of a circle of ringing mobile phones. Radiation. Amazing. Viral. Millions viewed.

A First Timer's Guide When some new guitarists break their first string they stash it in the closet and forget about it. Me, I put the sweaty axe back in its case and asked my parents to take me to the local music store. After a morning full of senseless racket emanating from my bedroom, my mom welcomed the drive.

Plastic Jungle.com offers an awesome service in which you can sell your unused gift cards for cash, other gift cards, and even Facebook credits!

In this video you will see how to heel toe shift and double clutch shift while auto racing with Gary Sheehan. Both methods are used in racing but can be applied to regular street driving as well. There is no verbal instruction, but you can get the idea just from watching Gary's feet. More experienced drivers will pick up how to heel toe and double clutch from this video better than beginners. Heel toe and double clutch with Gary Sheehan.

Wall studs are both critical for maintaining the structure of your home and supporting items of weight and function on the interior walls (e.g. cabinets, shelves, plasma TVs, etc.). With wall studs playing such a critical role, consistently being able to find them is important. The problem with finding them is that drywall and wallboard isn't exactly see-through.

I was looking around on this site and this article caught my eye. It was about hiding text in ADS or Alternate Data Streams. While this is nothing new in the tech world, it seems that more and more people are looking at ADS for one reason or another.

Want a face lift? Scared to go under the knife? Then, your solution is dimethylaminoethanol. Um... what is dimethylaminoethanol?

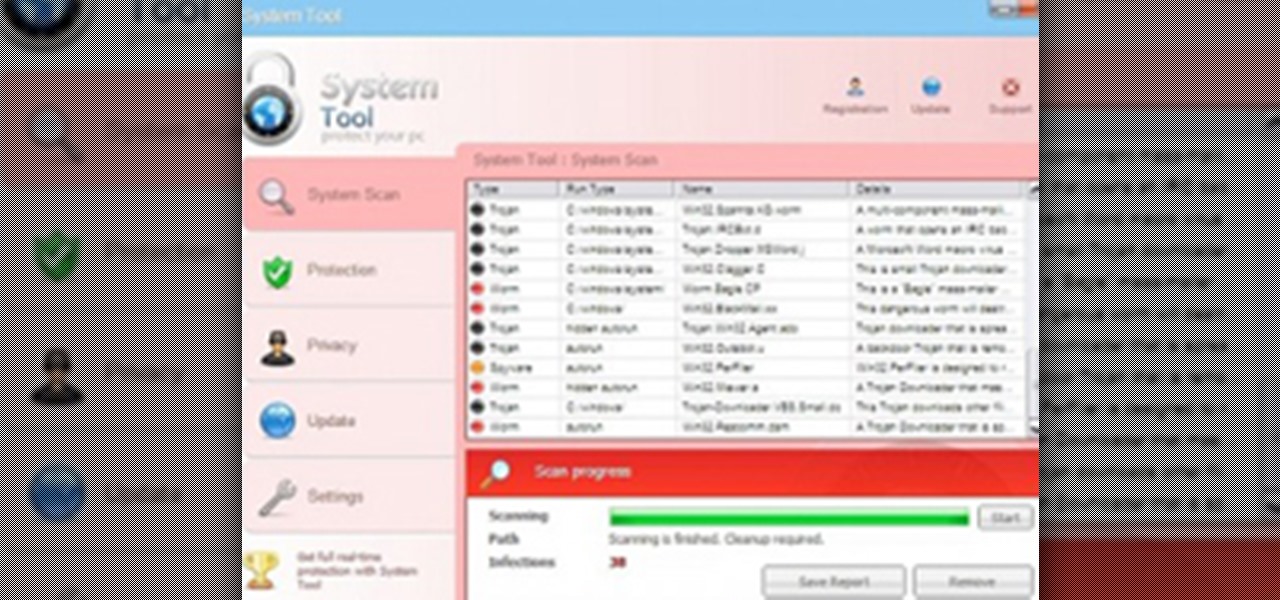
System Tool. It sounds like something your Windows computer might need, but it's the exact opposite.

What is Indirect Care? Does it affect the CNA's exam result? Indirect Care entails your behavior in terms of how you communicate with the resident, valuing residents' rights and residents' safety and security. Indirect Care is absolutely important because: (1) it is a graded performance, (2) it has separate score ratings, and (3 )it greatly affects the testees' overall performance during the clinical skills exam.

In this math made simple series of tutorials the author shows how to find a percent of a number. He shows that to compute x percentage of something we need to movie decimal point in the percentage number two places to the left. There fore to compute the percentage of a number we multiply it with the modified percentage number which has its decimal moved two places to the left. He goes and demonstrates this method by solving many sample problems. If you are looking to find out the percentage o...

Addison's disease is an endocrine disorder where your body is unable to produce adequate amounts of steroid hormones. As such, patients with Addison's disease require hormone replacement therapy.

An insertion pin allows you to stretch the size of your piercing one size at a time. The tapered shape allow you to increase the size of your piercing in a gentler manner. This how to video teaches the method on inserting the pin easily and comfortably. Watch this tutorial and you will be able to stretch your piercing in no time. Use an insertion pin to stretch your piercing.

The Replace Color tool lets you select one color and paint over it with a different color. To use the Replace Color tool, choose whether you want to select replacement colors from the swatches or from the image itself using the From drop-down. This is not always the best method to do this, but it's one of the fastest and worth knowing. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Repl...

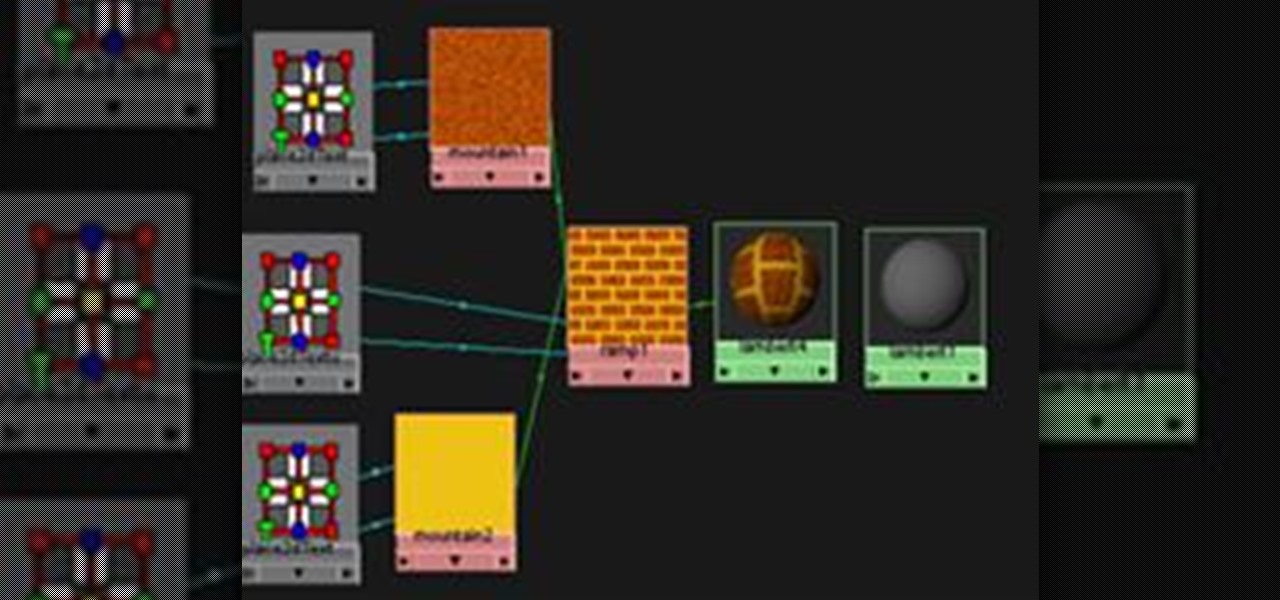
This is a guide to making a very simple procedural texture for Maya. As with all procedural textures, the basic texture can be refined and added to.

Polymer clay is an exciting arts & crafts medium. Actually, "clay" is a misnomer; it contains no true clay, but rather consists of tiny particles of polyvinyl chloride (PVC) combined with plasticizer, which is what makes it malleable like clay.

The Customizable timer Ever wanted to make a simple timer that ranged from 5 minues to whatever you wanted? It's actually fairly simple! In this tutorial I walk you through every step of the way and have a video to show you it in more detail.

When I was attending college, my friends had a phantom thief in their dormitory. Almost every night, a different item of food would go missing, never to be seen again. There was constant speculation as to whom the thief was and how to catch them. Security cameras were deemed too invasive, but none could think of another method of surveillance... until today.

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

How to play Spy, my personal favorite class What do Spies do?

Cryptography is a quintessential part of computer security in the modern world. Whenever you buy something on eBay or log into Facebook, that data is encrypted before it's sent to the server in order to prevent third parties from eavesdropping and stealing your sensitive information.

Today's guide is on creating a password protected folder on Windows 7 without any additional software. Yes, you heard that right. No extra software at all! This guide is intended for beginners. But please note, this method should not be used to store financial or otherwise highly confidential material. It might be a good place to hide a planning document for a family member's birthday party or similar occasion where you need to keep something secret temporarily.

In the first part of this series, we learned about darknets, as well as how they came about. But these patches of forgotten Internet are not the oasis of free information you might think. Despite being hidden—or just harder to come across—these networks are no more safe then anywhere else on the 'clear' Internet. The nature of networking and routing means your location is always known in server logs. It only takes one phone call to your ISP with your IP address to obtain both your physical ad...

Snapshot: 12w08a brings us a few nice things a few things I'm not so sure about and a few things I just hope Mojang doesn't incorporate into the next official update.

Accounting and Finance Degree

Here is my investigation on Teen Stress Base on FTA. QR/ER on Stress

Lock picking is defined by locksmiths as "the art of opening a lock without the key". There's many ways to accomplish this, but I'm specifically interested in using a lock pick set. Since locks vary in shapes and size, it's better to stick with just one kind of lock at first. Most locks are based on fairly similar concepts, so sharing methods across locks is possible.

I'm sure we've all heard about MSN and Yahoo! Messenger, right? They can be useful, but the setup can be quite time consuming for those who need to use it just once or twice—and the privacy statements are a real bother. For example, we must provide our real details. You could use Fake Name Generator, but if you get caught, you will have your account suspended. I don't have a law degree, but to my understanding the United States recently passed legislation that gives the authorities the power ...

VNC is a great protocol that you can use on Windows and Linux machines to remotely control computers. This is useful if you need to control your computer when away from home, help your grandma check her email, or help a client with a disk cleanup. VNC is secure in the sense that it requires authentication in order to make the connection, but after that, the data is sent over the internet unencrypted. This means that an attacker could sniff your traffic and snoop everything that's going on. Th...

If you've ever wondered how software pirates can take software and crack it time and time again, even with security in place, this small series is for you. Even with today's most advanced methods of defeating piracy in place, it is still relatively easy to crack almost any program in the world. This is mainly due to computer processes' ability to be completely manipulated by an assembly debugger. Using this, you can completely bypass the registration process by making it skip the application'...