Apple shipped their first batch of iPhone X's with an outdated and unpatched version of iOS. Be sure to check for updates and install iOS 11.1 first thing after you open your new iPhone or it'll be susceptible to the KRACK vulnerability for wireless connectivity.
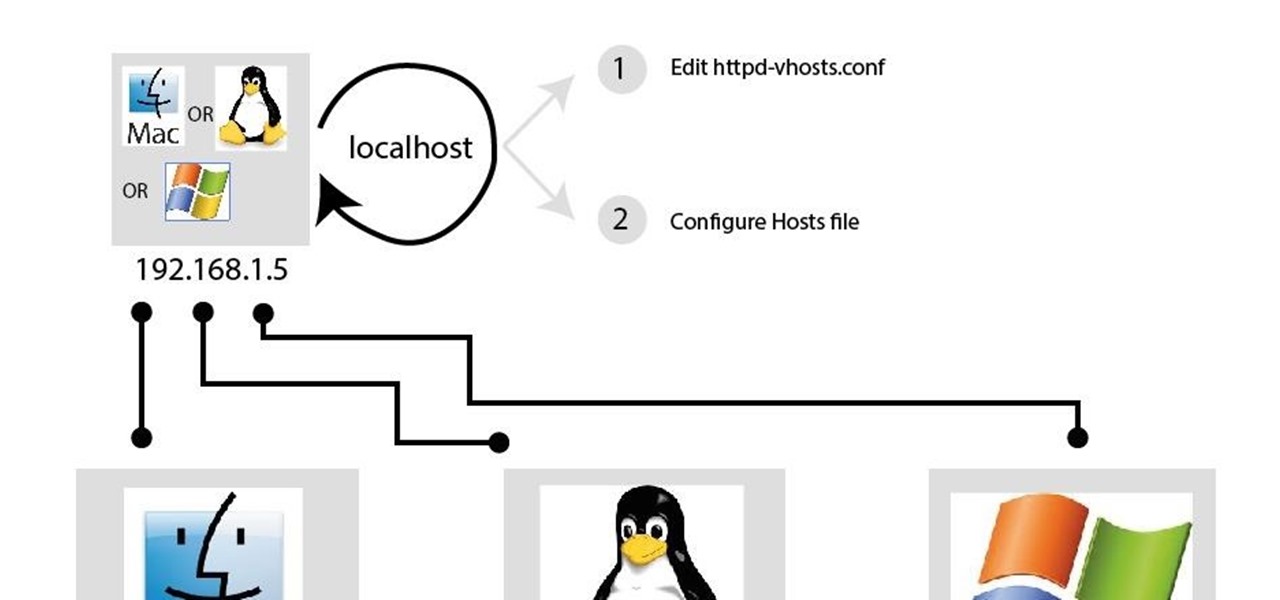
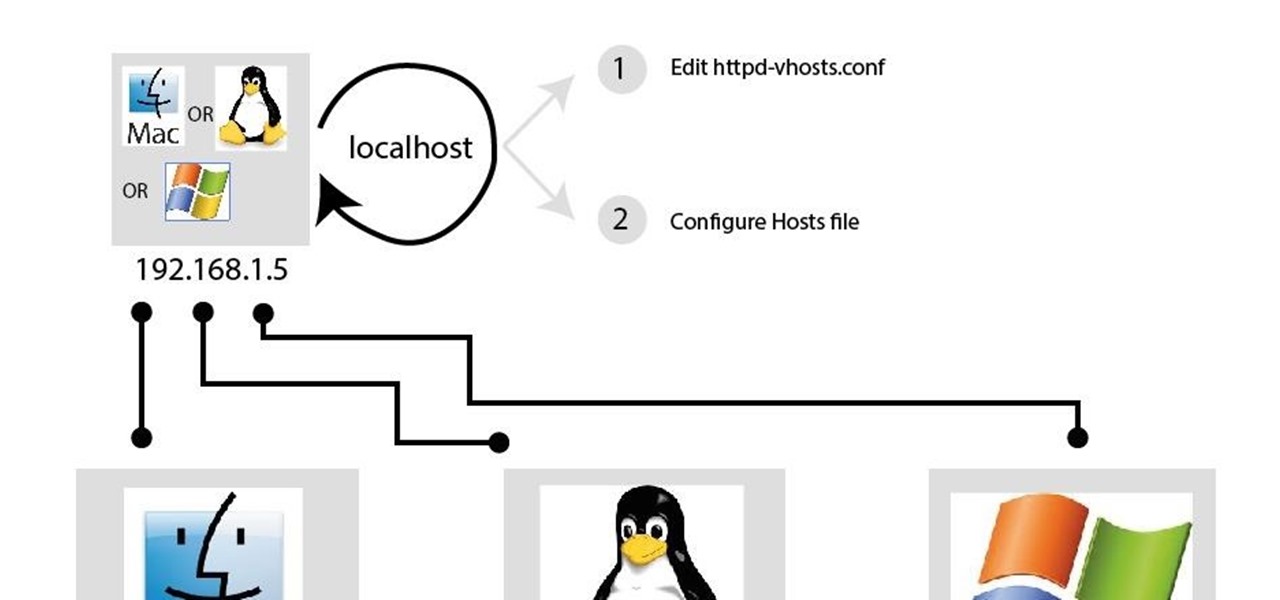
In my last article, I discussed: How to install xampp
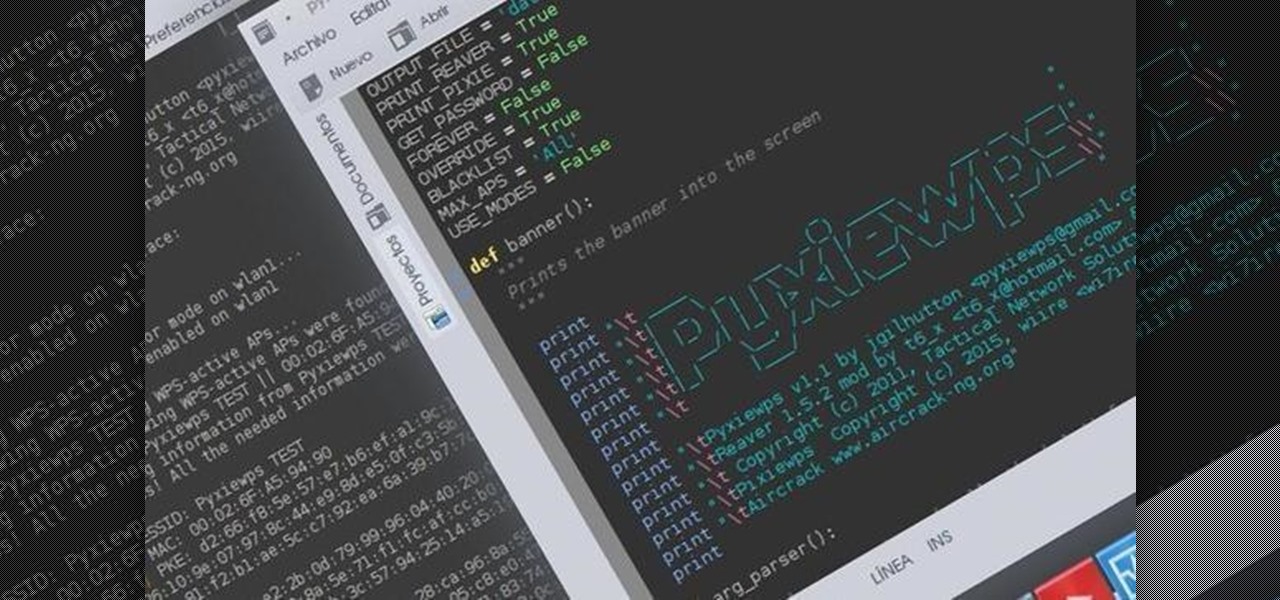
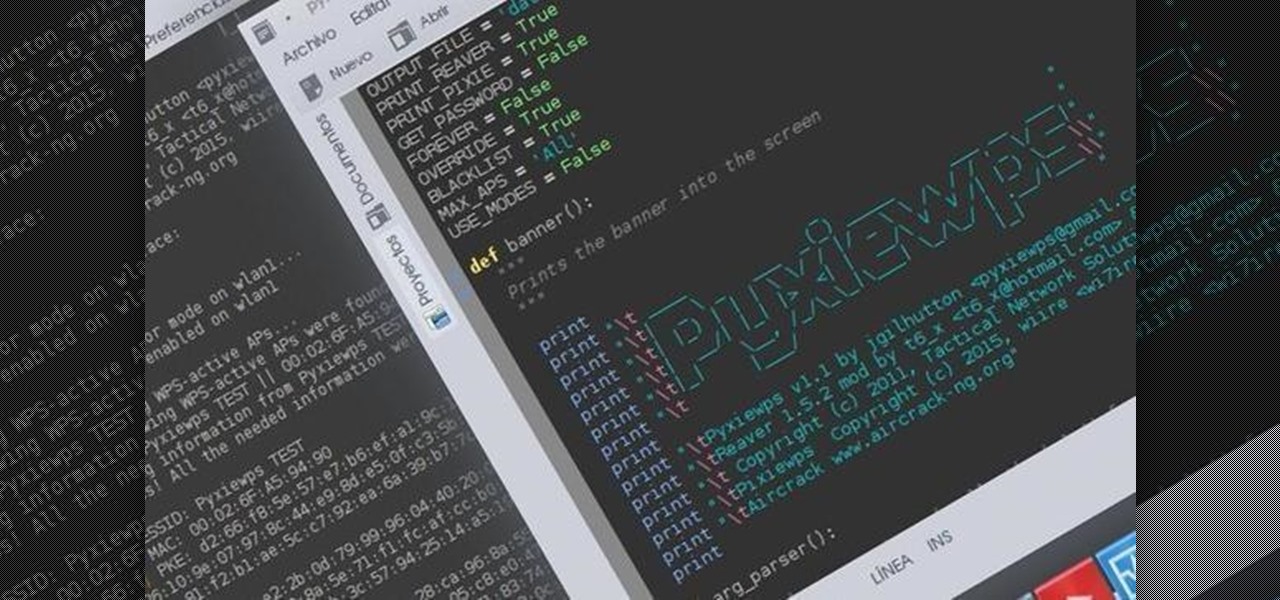
Helo my dear friends! A few days ago, I shared with this community my wrapper-script (a wrapper is a program that joins other programs that do the real job) to automatize the attacks on Pixie-Dust vulnerable routers. I was recieving complains from non-Kali users that had problems trying to launch the program, so I decided to make a good installer so anybody can use it in any DEB based distro.

Charlie Miller and Chris Valasek conducted an experiment earlier this month that ended up with a Jeep in a ditch, although the driver didn't drive it there. The two remotely hijacked the car, controlling it through a laptop and a cell phone. FCA says vehicles from the 2013 and 2014 model years with 8.4-inch touchscreen are affected. That includes Ram pickup trucks, the Dodge Durango, the Jeep Grand Cherokee and the Viper. Some 2015 Chrysler 200 sedans are also affected.

This is a followup from my recent series on XSS exploitation, giving a few extra attacks/tricks to try.

In the wake of a horrific attack on its Paris headquarters, satirical newspaper Charlie Hebdo has responded by upping its print run from a typical 60,000 to upwards of 3 million. This commemorative issue, Tout est pardonné ("All is forgiven"), has been met by such demand that the publisher is turning to alternative forms of media to reach as many viewers as possible.

Over the last few months I have been getting more and more into computers over the last few months, and I discovered my new favorite thing to do..... notepad stuff!

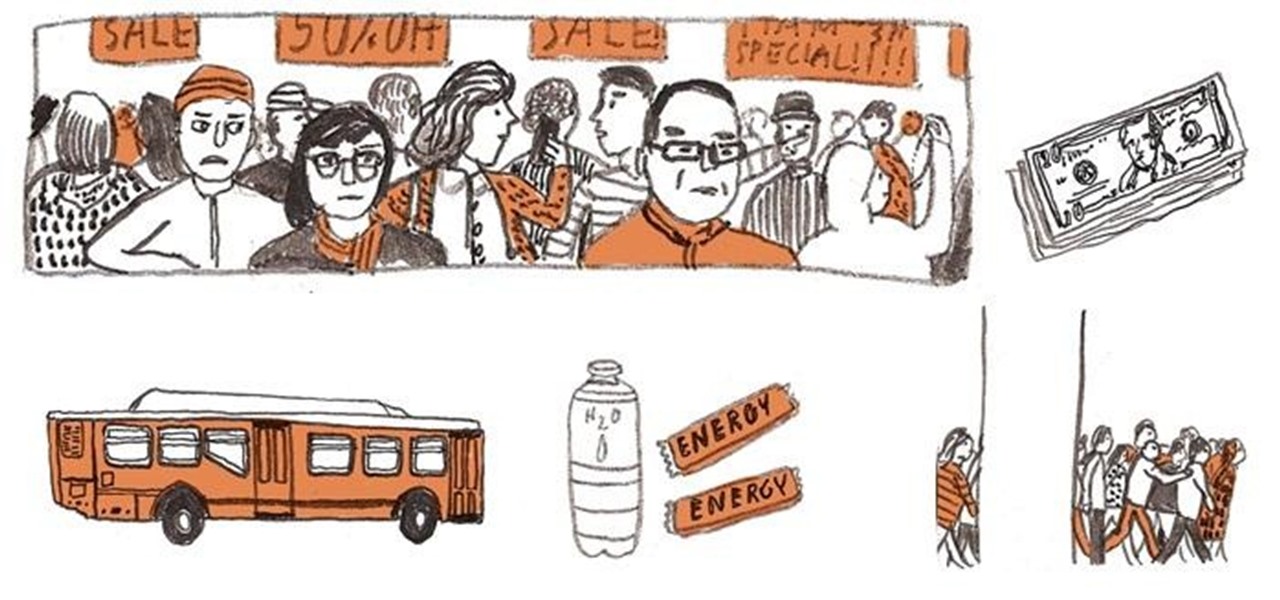
The Black Friday shopping battle is just around the corner. At the end of the day, will you emerge empty-handed or victorious with an armful of shopping bags bursting at the seams?

Are you sitting down as you read this? You might want to stand up for a little bit. In case you haven't heard, sitting for prolonged periods of time is really bad for your long-term health—so bad that chronic sitters are 54% more likely to die of a heart attack, even if they are non-smokers or regular exercisers.

In northern style kung fu, practice the rising block, reverse punch, shin kick, side kick and side punch combination to add power to a martial arts arsenal. Perform this unique attack combo with tips from a professional kung fu instructor in this free martial arts video. Perform a northern style Kung Fu combination - Part 1 of 20.

You want to put out a live web server, but you don't want to be owned in the process. An expert eye for security is not needed if you take a few basic steps in locking down the hatches. Most successful attacks today are not the complex, time-consuming tasks you might think, but simple lapses in policy that a hacker can take advantage of to compromise your server.

In my recent Darknet series, I attempted to connect the dots on the Deep Web. I covered the two largest anonymity networks on the Internet today, Tor and I2P. While my initial four articles were meant as an introduction, I ended up receiving a lot of interesting comments and messages asking the technical differences between the two. I'd like to thank all of you for letting me know what was on your minds, as you should always!

Sometimes mining and crafting gets boring. The thrill of hunting mobs, exploring strongholds, or the Nether is often much more satisfying and appeals to the RPG nerd in all of us. Well, Mojang took the hint and as part of the 1.9 release, there will be potions, more mobs, other worlds, and enchantments added to the game. To preview this release, read my tutorial on how to download and install 1.9.3.

Okay so it begins with someone either me or one of the jackass crew in the classic old person makeup that makes them look as nasty as possible. Then we get in an elevator with unsuspecting people and the "old person" pretends to be having a heart attack or something. finally, then we convince one of the strangers to give the nasty-ass old man mouth-to-mouth resucitation :) the person playing the old man make it gross as possible and throw in some tongue moves too.
Some interesting news this week, from Obama's new political ad, to the $20,000 payments by Cardinal Dolan. Take a look:

Have you ever found a photograph - a photograph of complete strangers? Maybe in a used book or at a flea market? Not a photograph of anyone you know or anybody famous or of a place you’ve ever heard of. Just somebody else's ordinary, precious personal photo. Working at a used bookstore I found a number of photos tucked into books over the years. There's one on my fridge. There used to be one tucked into the edge of my mirror. There’s one that I brought home and put in a frame.

Who hasn't gone mad trying to fix his/her computer, trying to delete all of the harmful software? It may not be funny with a real virus, but a fake one is. Or course, you can make a simple virus just with Notepad. There's no need to download applications to fool others; in less than 1 minute you will learn how to create a fake virus to scare friends, family or even teachers! Why not?

Oh yeah, this is a big topic, at-least for me. All the frequent flyers will/should be interested in this topic. I'm sure all of you have heard at-least something about the TSA, and most of it should have been bad. Complaints, lawsuits and general disgust surround this organization. Is there a reason, or are the 'extremist liberals' at it again? Let's find out!

Ivy League schools aren't just places for people to row and sip their drinks out of glasses normal people would never use (i.e. snifters). They also the place for trolling on a grand scale. Just take a look at these Trolls de la Resistance!

I write this post as an afterthought on the recent mass burnings of the Quran by U.S troops. Let me lay down the facts first to clear any misunderstandings:

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

Here's another delicious Byte. Ucha Gobejishvili, a Georgian Security Researcher under the handle of longrifle0x, discovered two cross site scripting (XSS) vulnerabilities on the official website of Forbes. He discovered the hole in two different locations on the site, and has already informed the website of the vulnerability.

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials of any skill level, about anything you feel like sharing that is ...

Null Byte is looking for moderators. More threats to computers exist every day. Not only do we have computer viruses and malware, but we have rootkits and other nasty pieces of code that can log your keyboard strokes or even add your computer to a botnet to attack other websites. Your computer can be infected even if you have anti-virus software installed. I can't stress enough how easy it is for a hacker to write a piece of code that gets around every piece of anti-virus software.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Sometimes it's easy to get overwhelmed with the sheer scale or complexity of a build or group project on your favorite server. Too much stress from any creative endeavour can lead to mistakes, discouragement, or fighting among a community. What better way to relieve stress and entertain the troops than some old fashioned competition?

There is a near-infinite amount of ways a computer can be broken into. But that does not mean that there isn't a reason to secure our computers as best as we possibly can. It's like the principles of a secure house. Which are the most secure houses? The ones with locks and advanced alarms, obviously, but not for the reasons people normally think.

Cinderella, Little Red Riding Hood and Sleeping Beauty are some of the most horrific fairy tales ever written, but over the course of nearly 200 years they've become watered down and sugar coated for innocent children everywhere. The original tales by the Brothers Grimm are virtually opposites of how we know them today, because they were never really intended for unsullied youngsters. The folk tales came from storytellers across the German countryside, recounting the terrors they've heard ove...

Leaving your wireless router at its default settings is a bad idea. The sad thing is, most people still do it. Once they've penetrated your network, hackers will change your router settings so they'll have an easy way back in. This allows them to change your network into a shell or proxy so they can forward their traffic anonymously through you when committing other dirty deeds.

Earlier last month, I wrote on how to subscribe to Google+ users using PlusFeed. I used it, and then I realized that I wasn't getting my own feed anymore. I discovered that the free service had been disabled due to cost issues, as detailed by the creator +Russell Beattie. The code is open source, and you can roll your own service, if you have the know-how and the time. If you don't, but still want to create RSS feeds for your own public posts, or just to track your favorite Google+ users, the...

The UK seems to have become an international hotbed of gamers going wild on society. Last week a British Navy sailor killed his superior officer, which parts of the tabloid media blamed on Grand Theft Auto. Today, a more concretely video game related tale of real life violence comes to us from The Daily Mail.

This Null Byte is the first part in a mini-series on the art of Social Engineering. I will be teaching you how to effectively defend yourself against it.

Dead Island is known for having the most successful trailer of any game ever. It was a beautiful cinematic experience. But sadly, as details of the game itself emerged, and after it was shown at conventions around the world, doubt began to set in about whether this five-year-long project would live up to the hype.

Like a great acting performance, making a really good game is all about choices. While creating or playing a game, those involved have to constantly make small choices that will affect the outcome, either positively or negatively. And the only thing worse than choosing wrongly is not choosing at all. Too many games, especially today, stick to what they're supposed to do from the get-go and avoid making difficult, small, meaningful choices to differentiate themselves and make their performance...

Behavioral ad targeting companies are diving deeper into the realms of your subconscious with a new approach to serving adverts to you online—and they're using your television.

Tower defense games have covered a lot of creative ground over the last five years. They've gone from simple desktop amusements to a staple of the indie game scene, having been integreated into nearly every other type of game and released on every platform. They have taken place in ancient times, the far future, and on alien planets. But one place they (and most other types of video games) have never taken place is the real world. Not a virtual recreation of the world, but on the very terra f...

In a recent episode of The Big Bang Theory, character Sheldon Cooper designed a highly complicated three-person game of chess, with an odd-shaped nonagon board and two new pieces—serpent and old woman. Seemingly pioneering, in truth, three-player chess has been around since the early-1700s, with many different variations, most of which retain the basic game structure and sixteen pieces that each player controls.

Could the world really be coming to an end tomorrow? Presuming you believe the biblical prediction from 89-year-old Harold Camping, May 21st, 2011 is undeniably Judgment Day. If you have confidence in that prophecy, you're probably not even reading this because you're too busy either A) preparing for the Rapture or B) sitting in your backyard bunker hoping to outwit annihilationism.

In December 2009, Angry Birds was released to the public. The iPhone and iPod touch were the first to take on the demand, then a devoted HD version for the iPad. Since then, it's transcended iOS devices to appear on Android, Nokia, Palm phones, and many others. Next, it broke away from mobile devices with versions available on PSP, PS3, Xbox 360, Wii, Nintendo DS, 3DS, Windows PC and Mac computers. Facebook and Windows Phone 7 apps are in the works.

Great controls are the most important and difficult part of game design. Games with vector graphics and non-existent stories are classics because their creators managed to create a system where using buttons to control a shape on a screen was intuitive and fun. This is the tradition that Pac-Man has left us with, a gaming world in which controlling the character onscreen in an engaging way is the crux of the game's enjoyment.

Any time a feature is introduced in an MTG set and not replicated in subsequent sets, balancing issues are surely forthcoming. You wind up with one set that can do things the others can't, forcing players to counter that set with other cards from it, and generally limiting the creativity with which one can effectively play the game. Playing these types of cards is like playing trap defense in hockey or boxing like Floyd Mayweather: you might win, but neither you, your opponents, nor the peopl...