Hacking Wi-Fi is a lot easier than most people think, but the ways of doing so are clustered around a few common techniques most hackers use. With a few simple actions, the average user can go a long way toward defending against the five most common methods of Wi-Fi hacking, which include password cracking, social engineering, WPS attacks, remote access, and rogue access points.

In its latest feature with an assist from augmented reality in storytelling, the New York Times shows readers the virtual crime scene it constructed to prove that the Syrian military conducted chemical warfare against its citizens.

Using Hydra, Ncrack, and other brute-forcing tools to crack passwords for the first time can be frustrating and confusing. To ease into the process, let's discuss automating and optimizing brute-force attacks for potentially vulnerable services such as SMTP, SSH, IMAP, and FTP discovered by Nmap, a popular network scanning utility.

In October of 2017, Mathy Vanhoef released "Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2." This paper demonstrates a way to decrypt traffic on practically any WPA2 network, the most commonly used form of wireless security (seeing as all other forms of Wi-Fi encryption have already been broken). Practically all of the network-connected devices we use will need to be updated in some way in order to protect against this vulnerability, each of them in a different way.

If you've ever wanted to scour the basement of a Hollywood hotel looking for evidence of a gruesome murder spree, this new AR experience might be the game for you.
The evidence is mounting and is becoming indisputable: Gut bacteria play a role in strokes and heart attacks. The link may seem a little far-fetched, but cardiovascular disease may have less to do with what we eat and more to do with what chemicals gut bacteria make from the food we eat.

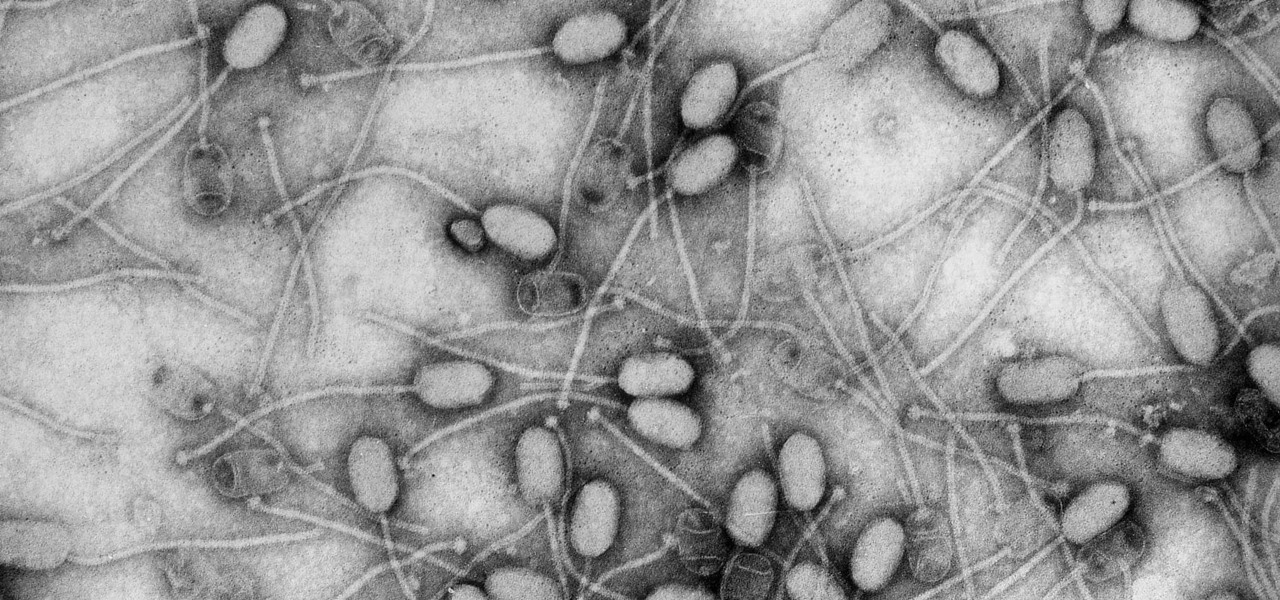
Fighting fire with fire, scientists are harnessing the adaptability of helpful microbes to challenge the adaptability of deadly microbes. What are we talking about? Hunting with phages — viruses that attack and kill bacteria.

Although there has been much speculation about how much damage could be done if hackers were to take control of a country's SCADA systems, there have been few examples - until a few months ago, with the power outage in Ukraine caused by hackers.

NMAP is an essential tool in any hacker's arsenal. Originally written by Gordon Lyon aka Fydor, it's used to locate hosts and services and create a map of the network. NMAP has always been an incredibly powerful tool, but with it's newest release, which dropped mid-November of last year, they've really out done themselves.
Mostly all hackers like to have a laugh. We like to have fun! We like to troll. And maybe, even cause some havoc once in a while. But, while we do this, we must always stay in the line of the law.

Hi everyone! In the previous part of this series, I introduced one way to hijack a program's execution flaw, though I only showed you how to crash the program and left you with a little mystery to solve. Today we are giving the solution of that and then introducing shellcode usage and remote command execution.

Hi everyone! Last time we finished analyzing the assembly representation of our vulnerable piece of code (have I ever told you it is vulnerable?). This time we are going to introduce some fundaments about exploitation by demonstrating how to crash a program's execution. If that sounds lame, next time we will see how this crash can in fact be useful to control the program's execution, achieving remote code execution!

Hi everyone! Last time we explained what roles Ebp and Esp registers have. We first introduced function's stack frame building, return address and calling conventions, but left some of the concepts floating without a full stop.

Hi everyone! After messing around a little bit with IDA and Hopper disassemblers and briefly introducing you to memory, registers and Assembly, we are going to understand what happens when a process is running, which variables join the play and especially what happens when a function is called and why is this procedure-logic so interesting and useful along with the concept of stack.

As was mentioned by the great OTW last week, TOR, aka The Onion Router, has had its integrity attacked by the NSA. In an attempt to reduce the anonymity granted by the service, the NSA has opened a great many nodes of their own. The purpose is presumably to trace the origin of a communication by compromising some entrance and exit nodes. Once both are compromised, it is much easier to correlate traffic with a particular individual.

The Asylum Demon boss fight in Dark Souls showcases yet another demon with a giant weapon. You'll need to be able to dodge his jumps and mace attacks if you're planning on defeating him. This video walkthrough will show you how to quickly beat the boss.

A recent addition to Mortal Kombat 9 in the form of DLC has reintroduced several classical features of Scorpion, Sub-Zero, and Reptile including some of the more traditional fatalities. Take a look at this video from the Achievement Hunter team and watch for the commands necessary to perform each of these violent attacks.

Keep your Runescape account safe from hackers by following the instructions in this video. Don't get hacked by giving your password away or using unsafe websites. Watch this video and learn how to take precautions against hackers so you can enjoy Runescape worry free.

Are you working on a zombie movie and need to step your gore up? Or do you just want to scare your friends with an ultra-realistic halloween costume? Check out this video that shows you how to apply a prosthetic.

Are you interested in developing your artistic talents? Have you got great ideas for cartoons but not enough technical know-how to make them come to life? This video will show you to draw a cartoon cat that will jump right off the page.

Dragon Age 2 is the latest fantasy RPG from the folks at Bioware, and if you're watching this video you've probably either just gotten it or are thinking about it. Check out the vid for a walkthrough of the prologue quest, Destruction of Lothering.

As Desmond travels into the past, he discovers some strange layered memories hidden within Ezio's consciousness. And then as Ezio, you must journey to Roma and confront the forces of the Borgia Pope, who has brought your family under attack.

The boomerang wielding Nomad is good at both ranged stun attacks and crowd control, and can be adapted to fit a variety of play styles. Here's how to integrate Nomad into your own team matches when you play Bloodline Champions.

King Dedede is the final boss in Snow Land in Kirby's Epic Yarn. He's one of the tougher bosses to defeat, since grabbing the buttons to defeat him can be challenging. Fortunately, his hammer attack is fairly easy for Kirby to dodge!

Halo Reach is newest edition to come out from the "Halo" series, featuring really cool advanced CGI and super fast attack vehicles called ghosts. These cars look almost like gigantic beetles, with a pod-like midsection and two wings on the side.

Want to be the best spear fighter you can be? This tutorial show you two basic shots you can make when wielding a foam spear on the fields of battle at your next boffer larp. You're also shown how you can thwart a javelin shot with a spear.

If you or someone you love is undergoing heart surgery in the near future, it's important that you have a solid grasp of the potential complications such that you can do everything in your power to avoid them. In this brief medical-minded tutorial from ICYou, you'll learn about a few of the most common complications including bleeding, infection, damage to blood vessels, heart damage, heart attacks or strokes.

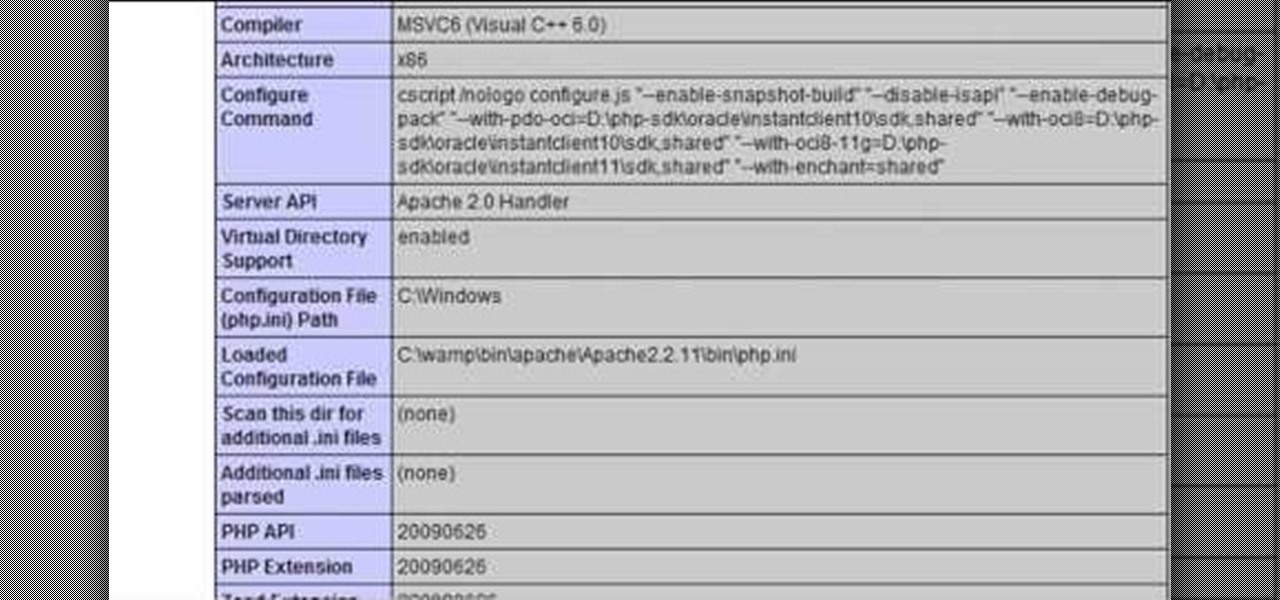
In this clip, you'll learn about how to prevent SQL injection when writing code in PHP. Whether you're new to the PHP: Hypertext Preprocessor scripting language or are a seasoned web developer merely looking to improve your chops, you're sure to find benefit in this free video programming lesson. For more information, including detailed, step-by-step instructions, take a look.

In this God of War 3 tutorial, discover what it takes to complete the Knockout Challenge. It's easy to complete and requires you to do two things:

Computers are vulnerable to all kinds of viruses, hacks and other attacks that can do serious damage and cost you money. Make sure your version of Windows is the real deal and protect it from counterfeiters by making it genuine. This video will show you how to make Windows XP genuine.

Grab some paper, pennies, and paper clips, and create this stealth weapon in the comfort of your own bedroom. Scaled to actual size, this craftable katana can be used to fend off paper-based attacks, or displayed for decoration. Add as many, or as few, foldable components to customize your sword size.

Spidering enables you to maintain a position of power, where you can pass, shoot or move quickly. Spidering is the position where one hand is sculling, and both legs are doing eggbeaters. This is a standard water polo position for both attack and defense.

Shooting in water polo is a basic skill for attackers. Water polo shot requires good height out of the water, arm position, shoulder rotation, and head stall. Shot strategy is important to building your water polo game. Concentrate on improving your rotation to follow through and speed up the shot. This is an attack focused water polo drill.

They are after you from all over the globe. Looking for ways to exploit you. Ways to hurt you. Not political terrorists, but rather "info terrorists." Each month thousands of websites get hacked into and have hidden links inserted into the pages by people wanting their spam sites to rank highly in the search engines.

The famous ADSR Envelope (Attack, Decay, Sustain and Release)... It's seen in almost every virtual instrument or software synthesizer from Albino to Halion to SampleTank to Z3ta but do you know what it does?

This is the set up I use for the straight jacket submission when someone defends the gogoplata. This submission attacks the shoulders depending on how flexible you are. There are a couple of ways to set this up.

This tutorial shows you how to path Artificial Intelligence monsters in Unreal Engine 3 for Gears of War. This allows them to move around and get them to attack players.

It's Jaws! No it's just face paint, but watch this video to learn the tricks and tips to apply face paint and look like a shark!

Today's word is "thwart". This is a verb which means to prevent from accomplishing a purpose or a plan. For example, you can say "The police thwarted three terrorist attacks at LAX last month."

After a series of quarte disengage attacks, Bijan takes several counter-ripostes before finishing with a fleche. (For those striving for perfection--He's too close when I'm coming forward/hand is too far back in his sixte parry & he's not fully stretched in the fleche--Aside from these things, I think Bijan has admirable form but I'm his coach & biased...)