
How to Train Your Python: Part 13, Advanced Lists, Slicing, and Comprehension
Welcome back! In the last training session, we covered logical and membership operators. We're going to switch gears and expand our knowledge of lists.


Welcome back! In the last training session, we covered logical and membership operators. We're going to switch gears and expand our knowledge of lists.

Hi I am a new member of null byte(although I am reading this website from the beginning) and this is going to be my first post.

Back in the '80s, recording live radio was as simple as popping a cassette tape into your boombox and pressing the record button. While we've come along way with regard to accessing radio stations thanks to websites and apps that stream live broadcasts over the internet, it's no longer quite as easy to record.

Notifications are an integral part of our day-to-day smartphone usage. They allow us to easily see and act upon all of the latest information that comes our way. Well, most of the time, that is.

Welcome back, my hackers apprentices! To own a network and retrieve the key data, we only need to find ONE weak link in the network. It makes little sense to beat our heads against heavily fortified systems like the file and database server when we can take advantage of the biggest weak link of all—humans.
Welcome back My sleepless army of young hackers, Everyone uses internet, right? So for this tutorial, i'll start with the basics and slowly we'll get to the UPD Protocol.

Welcome back, my aspiring hackers!

Welcome back, my fledgling hackers! In one of my recent articles, I showed you how to install BackTrack as a dual boot system on a Windows computer. In this tutorial, I will walk you through BackTrack, giving you a tour of the most salient features for the hacker-to-be.

Sunday, April 29, 2012 2:00pm until 6:00pm

Last Friday's mission was to accomplish solving HackThisSite, basic mission 10. This mission teaches us how to use JavaScript to manipulate cookies on poorly coded cookie-based authorization.

Welcome to another Community Byte announcement from Null Byte! The goal of the Community Bytes is to teach people in a co-operative, hands-on manner. Learning from experience and immersing yourself in a subject is the best way to learn something foreign to you, so that is exactly what we do! In our sessions, we have started to both code and complete HTS missions. This means that there is something for everyone here, so make sure you join us.

Firesheep caused quite a stir when it was released last October, giving both hackers and non-hackers instant access to people's account information when on a public Wi-Fi connection. When logged into an insecure website on the same network as someone with Firesheep, you're giving them access to the cookies that keep you logged in. This is called session hijacking, and grants them easy access to your accounts, like Facebook, Flickr and Twitter. Now, there's an even easier way to do this—a mobi...

If you're not familiar with the animations of Jan Švankmajer, you're in for quite a trip. The Czech artist and filmmaker is known for his metaphorical, captivatingly surreal stop-motion and claymation films, and is God to many (including talents such as Tim Burton, Terry Gilliam and the Brothers Quay).

FOXBORO, Mass. - The New England Patriots Alumni Club (NEPAC), announced that more than a dozen former Patriots players are gearing up to host a "Football for You" youth clinic in Worcester on Saturday, May 29 from 12:30-5:00 p.m.

So you're collecting stuff and crafting stuff, but what's it all for? You could wait and find out when you get there, or check out some screen shots of what's inside each building.

Oh Alice Waters and her magical Edible Schoolyard! Back in 1994, Alice Waters and King Middle School principal Neil Smith, worked with the community to refurbish their 1930's cafeteria kitchen into a wonderland of food education. The kitchen along with a one acre garden was the begining of what turned into the Edible Schoolyard project.

El Zonte, is a right hand pointbreak breaking over sand and rock bottom. The long right point is fairly consistant. With the right conditions there are two lefthand peaks out north a bit from the river mouth. In El Salvador, a left is quite hard to come by.

There are a variety of ways to speed up your body’s ability to heal. Things like keeping the incision clean, resting, nutritious foods and physical therapy will get you feeling strong quickly. Avoid negativity, as it may actually slow down your recovery. No one likes to be laid up in bed after surgery. Follow the advice on your “get well soon” card and be back to your old self in no time.

No more Internet Explorer 9 Beta. Not today. Now you can explore the web with Microsoft's new Internet Explorer 9 Release Candidate (RC). It wasn't supposed to be released until tomorrow, February 10th, but it's been leaked a little early, WinRumors reports.

Love them or hate them, Live Photos have their place. The problem is, they're always on, requiring you to disable the feature every single time you open the Camera app. At least, that's how Apple has things set by default — but you can change that with just a few taps.
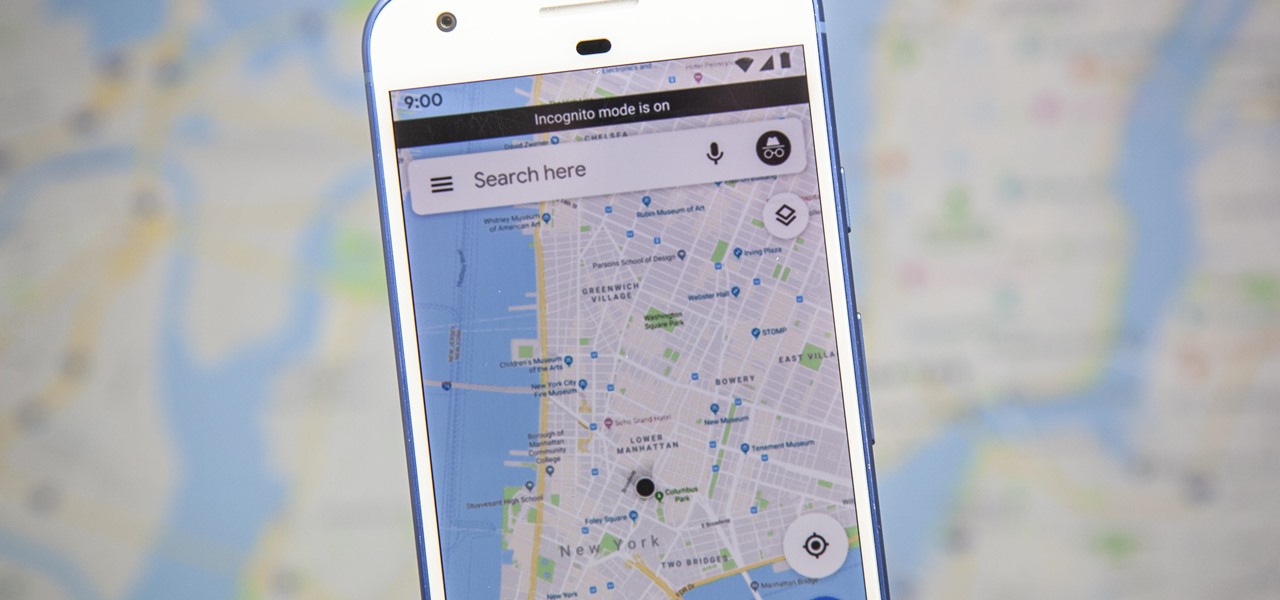
Google just recently added an incognito mode feature to Google Maps for iPhone and Android. With that, you can now use Maps in private at any time, which means you can browse and search with peace of mind.

What to do when your motivation is running low and you absolutely don't want to do something that needs to get done? If nothing is working for you, hack your brain with the following techniques to motivate yourself.

When that midday fatigue starts hitting you, sometimes the best solution is to just give in to sleep and nap it off. But how long should you sleep? Nap for too long and you often wake up feeling even worse than before, and it could be hours before you finally feel fully awake. Australian researchers conducted a study that back up this idea. They found that not only is a very short nap perfectly fine for recharging your brain, but that longer sleep sessions can cause a period of impaired alert...

Google Drive has been a gamechanger in the business world. First launched in 2006, Google Sheets has become much more than an alternative to Microsoft Excel. The powerful spreadsheet program is a boon for efficiency that's accessible wherever you have an internet connection—or when you have time edit offline.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

Working from home has its perks. You don't need to commute, you can work in your pajamas, and you don't even need to clean your house, especially if you're using Zoom for video meetings on your smartphone. Instead of clearing toys from the floor or moving that pile of clothes on your chair, you can take advantage of Zoom's virtual background feature to hide what's really behind you.

It's always a good idea to know how an attack works at the very basic level. Manual techniques for exploitation often find holes that even the most sophisticated tool cannot. Sometimes, though, using one of these tools can make things so much easier, especially if one has a solid foundation of how it works. One such tool can help us perform a cross-site request forgery with minimal difficulty.
So, you want to perform an exploit on a victim, but you're not on the same network as their machine. In this tutorial, I'll be showing you how to set up a meterpreter reverse_tcp attack to work over the internet.

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

Decisions are rarely easy to make, and there are countless ways to mull your options over. You can sleep on it, pluck flower petals, make a list of pros and cons, or even follow the advice of a psychic. Yet to make the best decision possible, you might want to consider holding off until a certain time of the day—or even until you feel specific emotions. The state you find yourself in has significant impact on each decision you make.
Back in the eighties, I used to hate television commercials, but I eventually got used to them. Had to, in order to enjoy my favorite shows. Then, the increasing number of billboard ads annoyed me in the nineties. They followed me everywhere I went—no escape—persuading me to buy the newest whatever. It seemed like Big Brotherism—like They Live. But, I got used to it. When I finally entered the digital age and became a web addict, I was peeved at the constant sight of online ads everywhere I v...

A practice amplifier can be just about anything, but by definition it’s probably not something you are going to gig with.
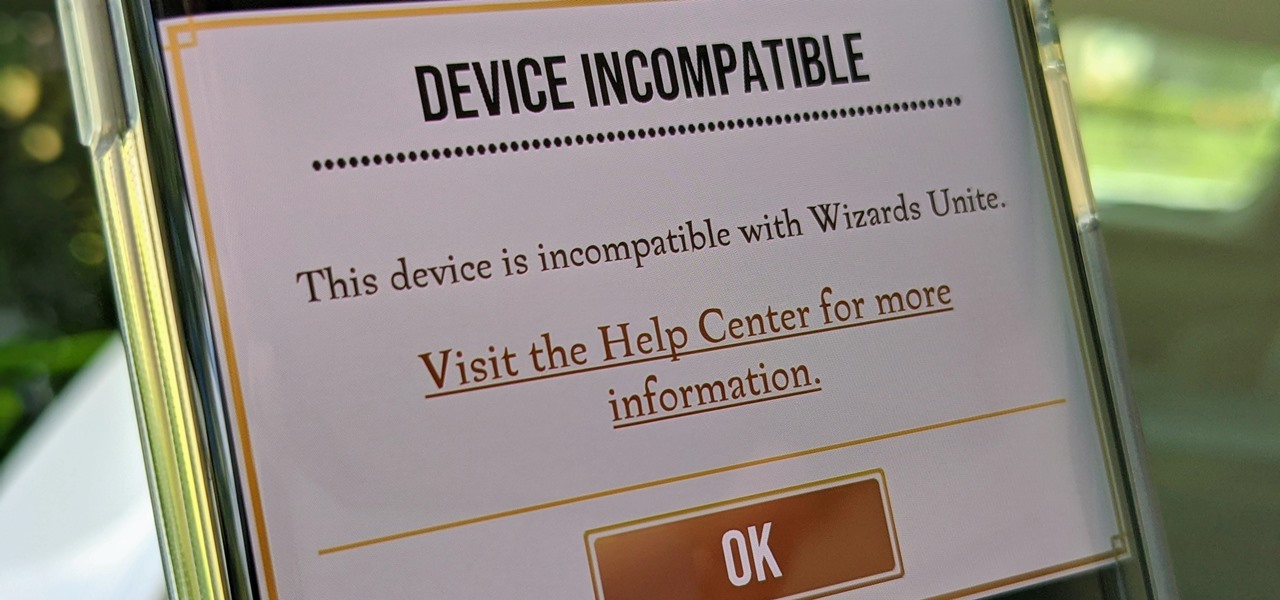
Harry Potter: Wizards Unite has gained quite the fan base since its launch, but not without a few bumps along the way. Niantic, the game's developer, has a long-running history with trying to block all root users on Android. The methods will vary for each game, but this time around with Wizards Unite, they appear to have a new detection feature at play from the recent 2.9.0 update. Let's find out what's going on.

Let's be honest, nobody enjoys doing cardio — they tolerate it. That dreadful, loathsome feeling you experience when you're doing cardio workouts isn't unique to you, it's almost universal. Sure, it gets easier the more you do it, but there are some ways to make it better now.

There once was a time before smartphones when you had to actually remember where you parked your vehicle. This really sucked when visiting a location with a large parking lot — they even made a whole Seinfeld episode about it. But now you can just tap a button to solve this problem. Who says we're not living in the future?

Because of its ability to place digital content into the real world, augmented reality lends itself well to artists and creatives.

The release of Avatar Chat for Magic Leap One and Spatial for HoloLens during the fourth quarter of 2018 appeared to revolutionize video calling via augmented reality.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

Augmented reality is really picking up steam as a tool for marketing departments to pitch their products.

There are a lot of things that make iOS great, but lock screen widgets are not among them. If you want more information on your lock screen other than the date, time, and notifications without having to swipe to a sidebar of widgets, you'd normally look toward Android. However, iOS 12 aims to shake that up a bit with a secret Weather widget for the lock screen — not for the Today view.