In this tutorial I am going to show you how to create an undetectable Meterpreter Trojan using a Domain name. I have taken a few guides/tutorials and built it into one. The first part is creating the DNS Payload. The second part is creating the Executable file. Part 3 is using both in Shellter to create your undetectable Trojan. Part 4 is setting up your listener using Armitage.

Making yogurt at home doesn't sound like an easy task at first. We initially saw it as detailed, hands-on, and precise—a process that required special equipment, specialized (and expensive) live-culture bacteria, and loads of yogurt knowledge.
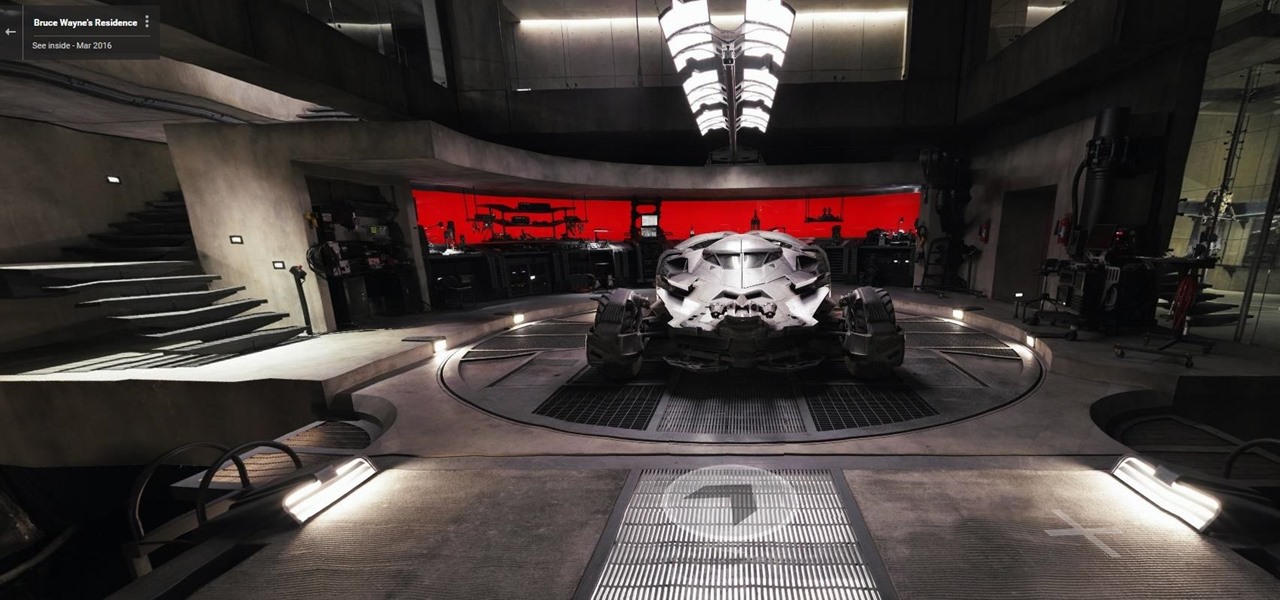
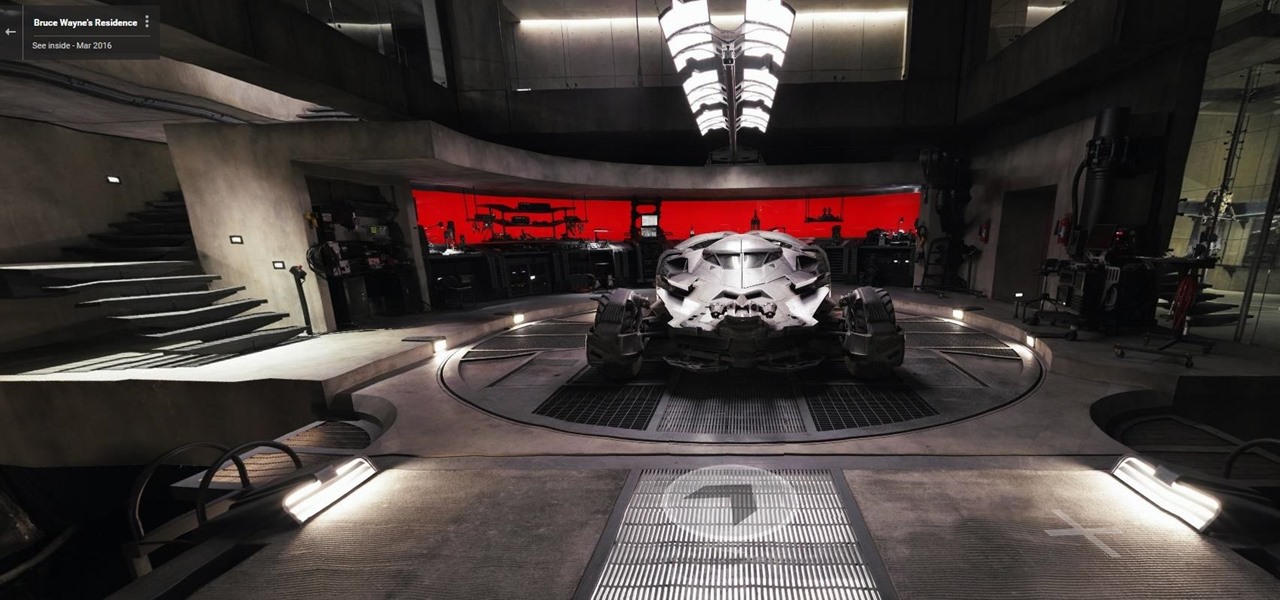
Nobody's supposed to know where the Batcave is, but as most everyone thought, Batman's underground lair lied below the estate of his secret identity, Bruce Wayne, in Gotham City.

Welcome back, my budding hackers! One of the keys to becoming a professional and successful hacker is to think creatively. There is always a way to get into any network or system, if you think creatively. In previous tutorials, I have demonstrated ways to crack passwords on both Linux and Windows systems, but in this case, I will show you a way to get the sysadmin password by intercepting it from a Remote Desktop session.

It's open season on Zoom, the video conferencing platform that has grown in popularity during the COVID-19 pandemic but has come under fire due to privacy issues.
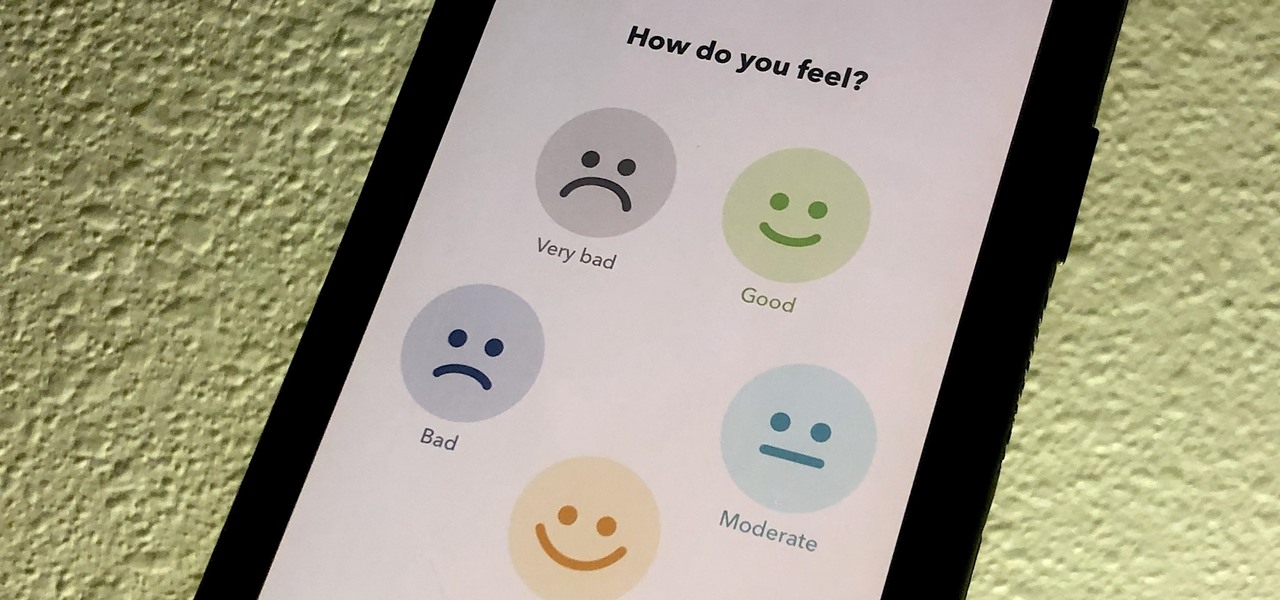
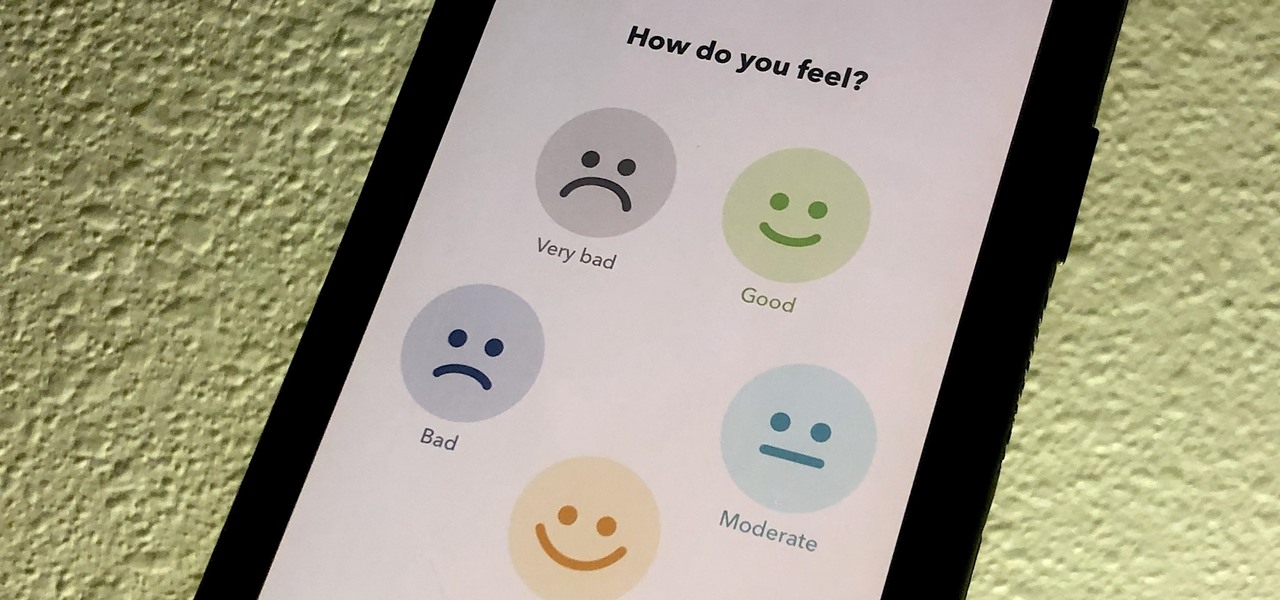
If you made a resolution for 2020 to get healthier, it's essential to concentrate on your mental health just as much as you do on physical fitness. Running and exercising is great, but a sound mind is integral to a healthy and balanced life, and you can improve your emotional and physiological well-being with your smartphone.

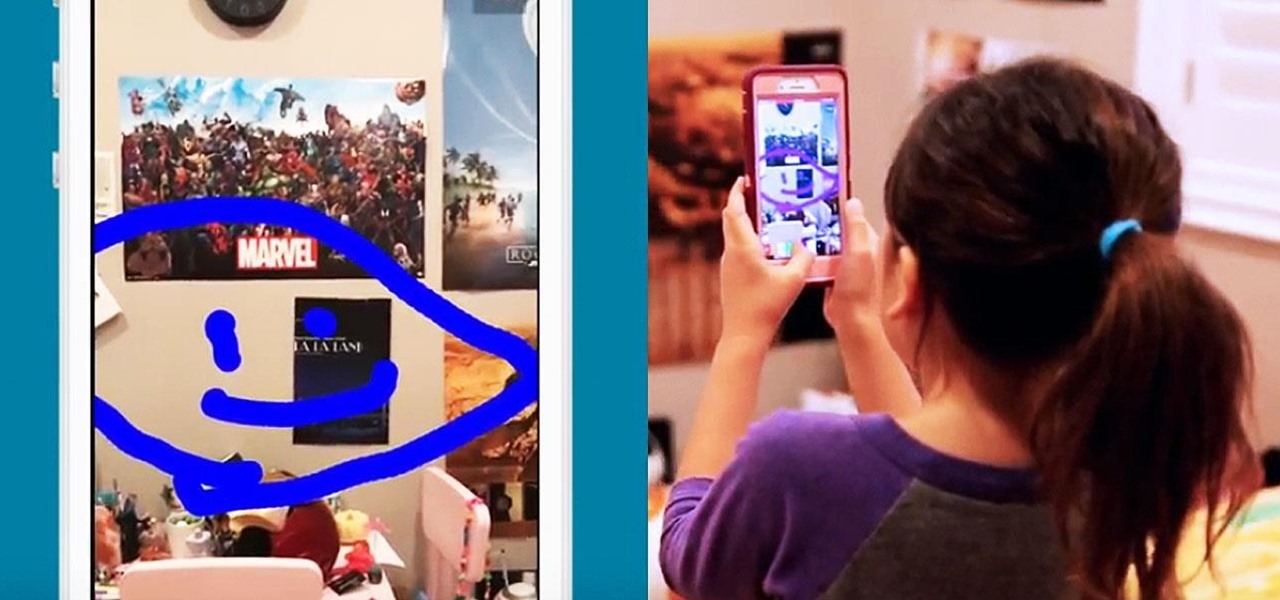
While you were busy browsing Instagram, composing tweets, or chasing Snapchat updates, an eight-year-old ARKit developer was hard at work on her first step toward taking over the tech world via augmented reality.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

Social engineering is a pretty important item in a hacker's toolkit. In Mr robot there was a time, we saw Elliot using social engineering to gain access to his therapist's boyfriend's email and bank accounts by calling him and pretending to be someone from his bank, then Elliot asked him for some info that were really useful to gain access to his account, the target believed to be someone from the bank and gave him the info Elliot was looking for. But How Is It in the Real World?

What's your top pet peeve? Open-mouthed chewing? Nail biting and knuckle cracking? The sound of silverware scraping? Or perhaps it's a bigger behavior, like leaving the toilet seat up?

In most cases, when the free trial of software is over, that's it—you're left to either pay for it or find an alternative. But what happens if the trial wasn't long enough to sell you on the product? It'd be nice if there was a way to test it out again without having to whip out your credit card.

Hangouts are one of the most fun features in Google+. As long as you have a webcam and a microphone, you can "hangout" with up to 10 of your buddies on Google+ and do just about anything. Of course, sometimes it can get kind of awkward when you are hanging out and you don't really have anything to say. This problem can be mitigated if you host hangouts with a plan.

Before starting a boxing training session it is important to wrap hands properly. A boxer's hands are useless if not properly cared for. Learn how to wrap hands in this boxing video tutorial.

From A Hamburger Today: your guide to regional hamburger and cheeseburger styles. What red-blooded American doesn't love hamburgers? Think you're an enthusiast? Think again. There's more to the burger than the Big Mac (though the Big Mac is included in this guide, of course).

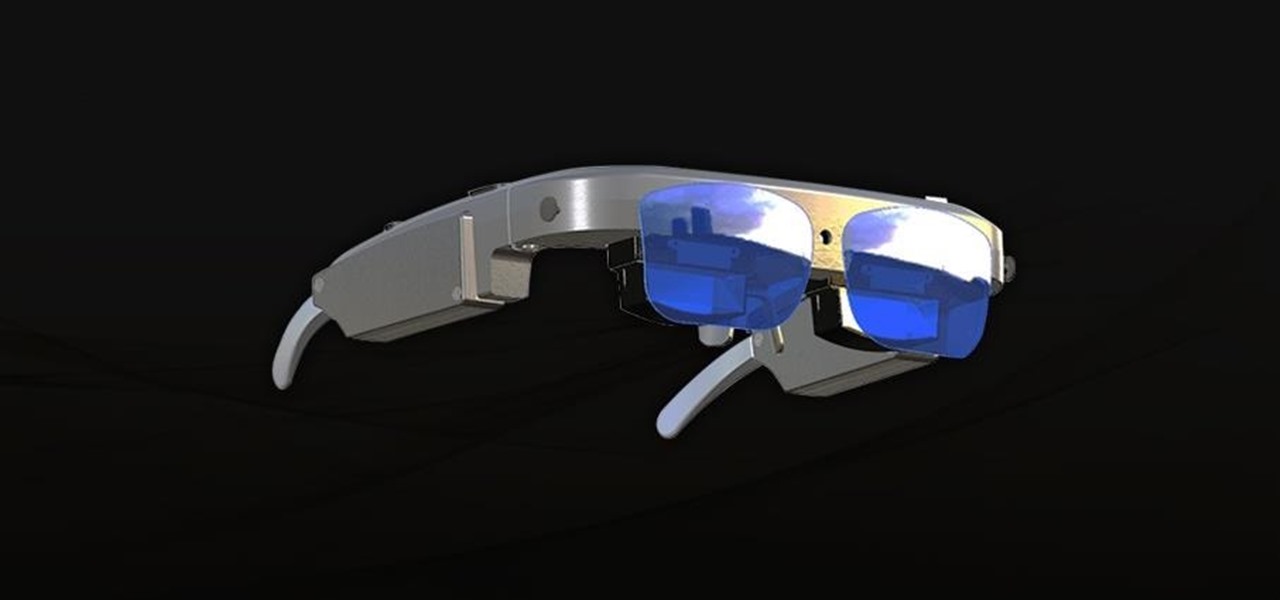
The first headset running on the Qualcomm Snapdragon XR2 chipset from an original equipment manufacturer is official.

Following in the steps of Snapchat, Instagram, and YouCam, another popular photo app has gotten into the virtual try-on augmented reality game.

Businesses that have adopted enterprise-grade wearables for their workforces now have a new option among the multitude of AR productivity apps that can help their team members communicate in AR.

In this era of smartphones, we all know very well how easily we can get addicted to our devices. Spending hours each day doing the endless scroll through Facebook and other social media sites just because we feel like we'll miss something if we don't. Both Google and Apple are aware of this and are trying to help control smartphone addition in their own way for Android and iOS.

If you've been putting off upgrading your iPhone or iPad, you might want to start shopping for a current-generation device to take advantage of the latest capabilities in ARKit 3.

Automotive augmented reality display maker WayRay is making a move to help developers get all those slick, futuristic AR functions we see in concept videos into the real cars of today.

On Thursday, yet another piece of the Magic Leap puzzle fell into place at Twilio's Signal developer and customer conference in San Francisco.

Apple first added a "Drag and Drop" feature to iPads in iOS 11, but your iPhone can do a little of the magic, too. It's just not so obvious. While you can't drag and drop items from one app to another like you can on an iPad using Split View and Slide Over, you can move things around in certain stock applications. And it works the same whether you're using iOS 11, 12, or 13.

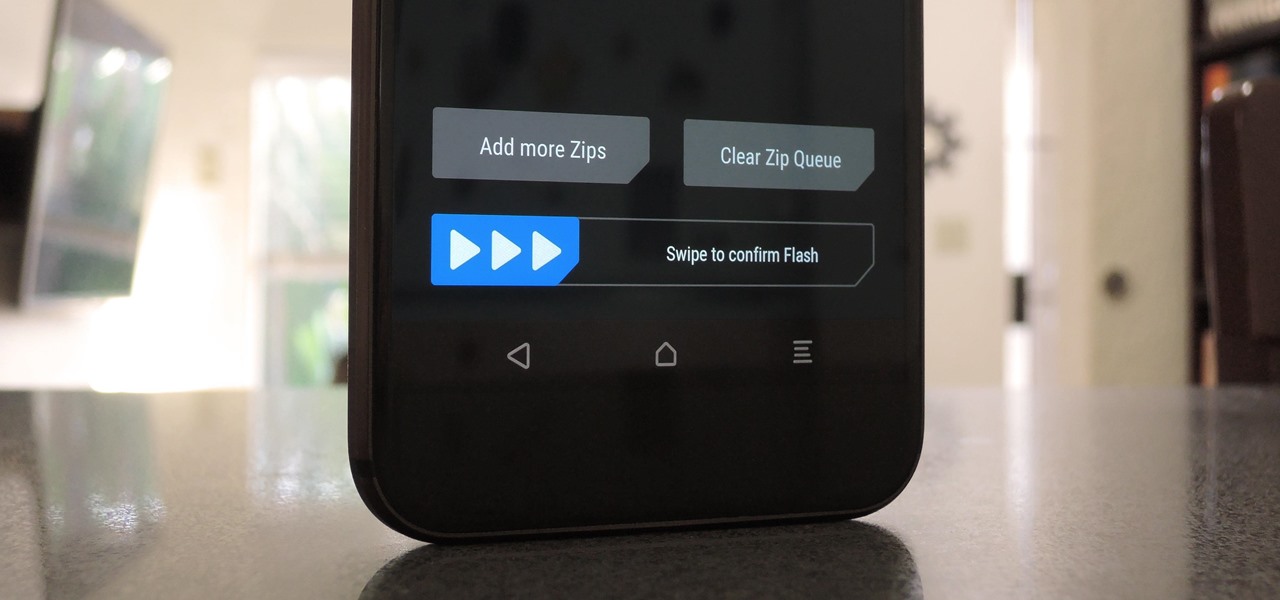
When you're flashing a custom ROM with TWRP recovery, it's almost never just one ZIP. Instead, you have to flash the ROM file, the Gapps, a custom kernel, and maybe even Xposed or Magisk, which results in a lot of back-and-forth. Thankfully, it doesn't have to be this way.

Smartglass maker ThirdEye Gen, Inc. has introduced an augmented reality solution for enterprises that includes their X1 Smartglass and a suite of software applications that enable completely hands-free computing.

Some Montana inhabitants have been making impassioned pleas to legalize raw milk this week. The debate took place during a hearing on House Bill 325, which was held by the Senate Agriculture, Livestock, and Irrigation Committee on Tuesday, March 21.

Five Phases of Hacking:- The five phases of Hacking are as follow:

Hello My Fellow Hackerzz.. This is my first How-to and i'll be updating the “Hacking Android Using Kali” to msfvenom and some FAQ about known problems from comments. So Here we GO!!

If you want to watch a movie on Netflix with a friend, family member, or significant other, but can't meet up in the same living room, the next best thing is doing it remotely from the comfort of your own homes.

Now that we have control over a victim's browser, we need to use some attacks to maintain the connection, or even better: upload a shell.

OTW's great Tutorial Hack Like a Pro: How to Save the World from Nuclear Annihilation gives me the inspiration to try this on Win7 sp1.

We recently showed you how to recover your Shazam history from Siri, which is a lot less intuitive than finding the songs you've tagged directly in the Shazam app. But with a subscription to Rdio or Spotify, there's no need to even locate your history. You can Shazam songs and have them automatically added to a newly created playlist titled "My Shazam Tracks."

With the the general computer users understanding of Information security rising (at least to the point of not clicking on unknown links), and operating system security getting better by default. We need to look for new and creative ways to gain a foothold in a system.

I'm still amazed by all the things some people just don't know. Script-kiddies often refer to Metasploit if someone asks them how to hack a computer because they think there's simply no other way. Well here I am today trying to increase your set of tools and -of course- skills.

In this article, I'll show you how to easily "hack" Facebook, Twitter, YouTube, and any number of similar account types with an Android app called FaceNiff.

The Website above is about congress. It has the recent activities of Congress. It also allows you to contact them to stop any law which you might disagree with. This is a great way to help make a decision that might effect others.

What's your highest scoring game of Scrabble? Since starting this Scrabble World, I've been able to break 500 points on a regular basis. This year I've even managed to break the 600-point barrier a couple times. If you ask me, that's a pretty hefty sum to score in one game, but I'm not on par with the professionals yet.

Welcome to the second Goonight Byte! Our second coding session was kindly hosted by th3m, so props to him for letting this happen.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Other than keeping your popsicles and frozen veggies frosty, who would have thought that your everyday freezer had so many uses? Just like your dishwasher can be used for many non-cookware items, the freezer can be used in a variety of useful ways that don't involve perishable food.

For travelers on-the-go, or penny pinchers who like to surf the web for free in public places, there are necessary precautions one must take when accessing sensitive information over a public WiFi connection. For advice on doing this safely, check out Glenn Fleishmann'sguide to staying protecting your private information. Fleishmann outlines how to: