
How To: Hack and Decrypt WhatsApp Database (Remotely) [ROOT]
Hello my fellow hackers, it's been a while since my last post, I can't get the time now-a-days for the posts but can manage to tend to comments.


Hello my fellow hackers, it's been a while since my last post, I can't get the time now-a-days for the posts but can manage to tend to comments.

Recently, I've been experimenting with BeEF (Browser Exploitation Framework), and to say the least, I'm hooked. When using BeEF, you must "hook" the victims browser. This means that you must run the script provided by BeEF, which is titled "hook.js", in the victims browser. Once you've done that, you can run commands against the victims browser and cause all kinds of mayhem. Among these commands, there is an option to use the victims webcam. This is what we'll be doing here today, so, let's g...

Mobile payment systems have been around for almost 5 years now, starting with Google Wallet. But when Apple got into the game last year with their new Apple Pay service, things really started to take off. Around this time, Samsung responded by acquiring an up-and-coming mobile payments company that owned the rights to an incredibly innovative technology called Magnetic Secure Transmission (MST).

Welcome back, my novice hackers! This new series on Bluetooth hacking was inspired by a recent episode of Mr. Robot (my favorite TV show). In episode 6, Eliot hacked the bluetooth keyboard of the police office in order to hack the prison and release his nemesis, Vera. This is just one of the many hacks we will explore in the series.

The telecommunications industry has come a long way since Ma Bell opened the first telephone exchange in the late 1800s. With the advent of fiber optics and wireless broadband technology, we no longer have a need for a dedicated phone connection, as today's data networks can carry much more than a simple voice conversation.

Welcome back, my aspiring hackers! In many of my earlier tutorials, I mentioned the complementary nature of hacking and forensics. Both disciplines, hacking and forensics, benefit from a knowledge of the other. In many cases, both disciplines will use the same tool. In this tutorial, we will use another tool that can be used in either discipline—Sysinternals—a suite of tools developed by Mark Russinovich.

Welcome back, my greenhorn hackers! Digital forensics and hacking are complementary disciplines. The better you are at digital forensics, the better hacker you are, and the better hacker you are, the better you are digital forensics. Unfortunately, few people in either profession cross these discipline lines.

While the Apple Watch does have up to 18 hours of battery life each day on a full charge, your results will vary depending on how often you use it and what you're actually doing with it.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Look on any bistro or pub menu in America and you'll likely find the term caramelized onions as an option for your burger. The word "caramel" may conjure up images of candy, which is somewhat correct.

Welcome back, my fledgling hackers! In an earlier tutorial, I introduced you to probably the most popular scripting language for hackers, Python. To become a professional hacker, you need to have some scripting skills and Python is a good choice if you want to master just one. In this latest guide, I will expand your background in Python and offer you a tidbit of Python code to whet your appetite for all of the hacking to come.

Welcome back, my greenhorn hackers!

By now, nearly everyone with any type of media access is aware that Sony Pictures Entertainment was hacked on November 24th. Although there can be many interpretations and lessons drawn from this audacious act, there is one indisputable conclusion: it and its ripples across the globe underlines how important hacking has become in our all-digital 21st century. As I have emphasized so many times in this column, hacking is the discipline of the future. From cybercrime to cyber intelligence to cy...

Apple Pay has been available to use in stores, as well as in select apps and websites, ever since its first appearance in iOS 8.1. Now, with iOS 12, there are currently 13 different iPhone models that support Apple Pay functionality without the use of an Apple Watch, and the list of partnered stores that accept Apple Pay has only grown. Here's our always-up-to-date list to keep you in the know.

Apple just announced the iPhone 6, and no matter whether you've been with Android for a few months or few years, there's a good chance you're enticed by the idea of switching over to the other side.

We've all been there; waking up in the morning with a stiff, achy back. Maybe you overdid the yard work this weekend. Perhaps you were a bit too enthusiastic on the Nautilus circuit. Could be the long hours spent hunched over your computer are catching up with you. Perhaps your back pain is indicative of something more serious. Unfortunately, unless you've really injured your spine, your doctor isn't going to be much help; the best he can do is offer you pain medications and tell you to rest ...

If you're anything like me, you started down the Android-modding path for two distinct reasons; to run cutting-edge software and squeeze every bit of performance out of your hardware. Utilizing the new F2FS file system on your rooted Nexus 4 or 5 fulfills both of those desires at the same time.
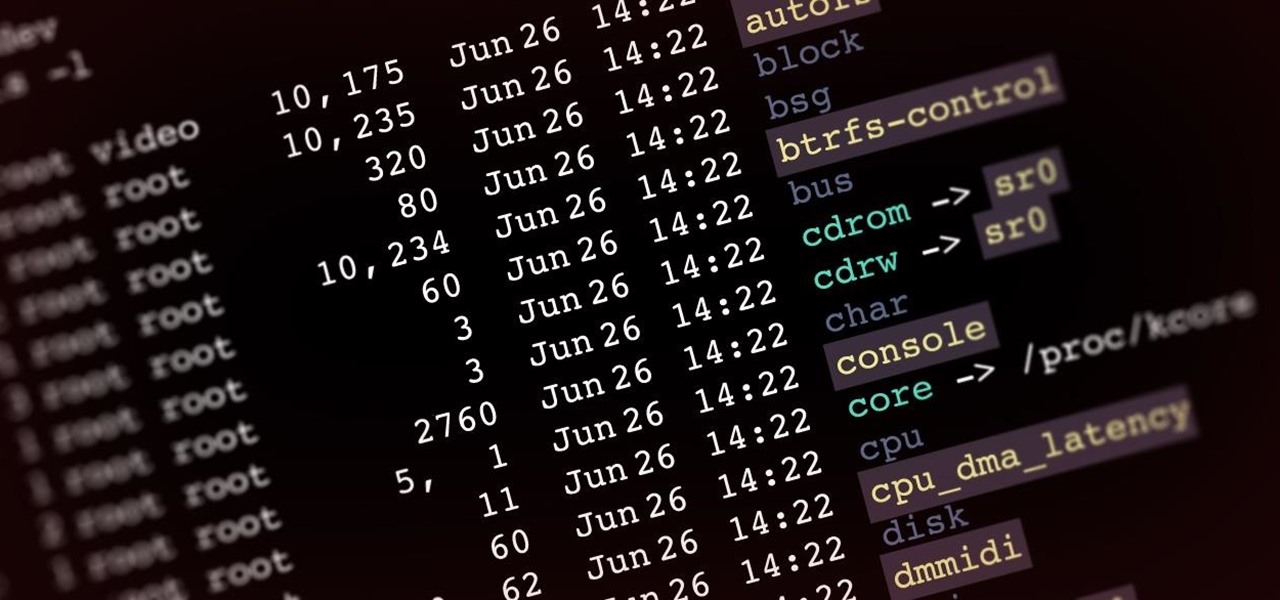
Welcome back, my aspiring hackers! In recent tutorials, I have made reference to the name and location of the Linux devices in the file system, such as sda (first SATA or SCSI drive). Specifically, I have mentioned the way that Linux designates hard drives when making an image of a hard drive for forensic purposes.

The long rumored and recently leaked Amazon phone has finally been unveiled, and in the interest of branding, continues down the Fire line—the Amazon Fire Phone. You can check out the full reveal here (warning: it's long), but I'll take you through all the features that sets this device apart from the rest. Before we get into that though, let's check out the specs:

Welcome back, my aspiring hackers and those who want to catch my aspiring hackers! As most of you know, this series on digital forensics is inspired by the motivation to keep all of you all out of custody. The more you know about the techniques used by law enforcement and forensic investigators, the better you can evade them.

Ever since the much-lauded effects of the Mediterranean diet became widely known, people have been buying olive oil by the gallon. A diet that prevents heart disease, is based on fresh, seasonal foods, and includes a tasty as hell fat like olive oil? Duh—that's a no-brainer.

Video: . Optimize your Marketing with a Mobile Website

With the new year right around the corner, it's time to talk about the end of the 19th century, a time which plays an enormous role in Steampunk. If you've done any reading of British books written from about 1890 to 1899, you may have come across the phrase 'fin de siecle' and wondered what it meant. You also may have come across this term in reading about the late Victorian era. No worries, I'll tell you all about it! Image by Giovanni Dicandia

TouchDevelop is a browser-based programming tool that allows anyone to build your own Windows 8 apps directly from any touchscreen device, including iPad, iPhone, Windows Phone, Android, PC and Macs. Once the script is created and the app proves to work, it can be placed in the Windows Store for free or purchase.

Many of us in the Steampunk community have pets that we love and cherish, myself included, and we want those pets to share our joy of Steampunk. In reality, they couldn't care less, but for some reason we still love to dress them up. Their reactions usually range from bemused acceptance to temper tantrums, but the awwwws we get from onlookers usually makes it worthwhile.

People are always looking for ways to save money, and for the most part, saving money and cheating the system are synonymous when it comes to things like free internet access. Practically every new gadget is capable of connecting to the web, which means more and more people are looking for ways around those hefty internet bills.

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

In the first part of this series, we took a factual and technical look at the history of the Internet. I explained how all of these wires and servers got here in the first place. Obviously, a firm did not just create and build the Internet around 1995! Now that we know how the Internet came to be, we can get into the really fun stuff—what the Internet looks like now! Well, that's not quite the network design I was talking about, but it does show what the Internet looked like back in 2007 befo...

Spammers are the bane of every email user. No matter what you do, junk mail always breaks through the spam filters. And some of the best ones seem to come from legit companies, and that's because they aren't legit companies— they're spammers masquerading as legit companies.

All you science and astronomy nuts out there, pay attention, this detailed video tutorial series will tell you everything you need to know about using the Meade EQ Series Telescope to ogle the universe.

Trees, shrubs, and hedges in your home garden have not only aesthetic appeal because of their beauty but also are very practical. Trees offer shade from the sun, and hedges provide privacy for your yard. These plants however, must be well taken care of to continue to provide their beauty and function. Tree pruning is an essential part of landscape maintenance that must be done regularly to ensure that your trees continue to look beautiful and grow a large healthy canopy. Similarly, hedge trim...

Watch this instructional sewing video to learn about the zip bind tool and how to adjust it for your quilting projects. This video provides a helpful introduction to this quilting tool. The zip bind tool is a sewing tool that makes quilt bindings perfect from end to end. There's no need for straight pinning and there's no measuring involved.

In this video tutorial, viewers learn how to lose belly fat without having to do crunches. The exercises provided in this video are: push-ups, squats and dumbbell squat raises. These exercise don't just work on the abdominal muscles. It is recommended to do each exercise until failure. These exercises use the abdominal muscles as stabilizers. The key to losing fat is to push yourself hard to do the exercise. Abdominal muscles are not designed to flex. Crunches do not help lose belly fat. This...

In this video the tutor shows how to mount ISO's using Power ISO software. To do this follow the simple procedure shown in this video. Download the Power ISO program from the link given in this video and install it. You need to purchase the key to install the software or you can use the key provided in this video. Now restart your computer. After restarting open the software and go to mount ISO at the top right corner. Select the image that you want to be loaded. Finally run the virtual CD dr...

In this video, viewers learn how to use foil to apply patterns on nails. Viewers learn how to create great metallic designs. Other nail art products can be used with the foil to create even more sparkly nails! This video lists all of the required materials. The materials required include: foil, foil adhesive, base coat, nail varnish, top coats, and optional nail gems. The video provides easy step-by-step instructions that allows viewers to easily follow along. This video will benefit those vi...

Check out this video for info on how to origami a paper boat. This is no ordinary paper boat, either! This boat actually floats! All you need is some paper, a bit of tape and your fingers and pretty soon you will have a fun new bath toy. Granted, it is still paper so it won't last long in water, but it sure does provide a cool effect when you first make it! And on a breezy day, your paper sailboat will take off like a kite!!

Interested in metal inert gas welding? This video tutorial provides some sage advice for beginning MIG welders. It's important not to dive into your welding projects without the proper tools. You will need a welding table, and wire brushes for steel and aluminum. You will also need wire cutters, sheet metal shears, a canister for storing stick electrodes, a chipping hammer, and an angle grinder. Once you have these simple tools on hand, you can begin to troubleshoot with larger welding equipm...

Who doesn't want to be able to speak like a New Yorker? Whether for acting, comedy or impressing your friends and family, speaking in a New York dialect will provide you with hours of entertainment. Learn how to speak in a New York dialect in this free video series from communications and public speaking expert, Tracy Goodwin.

An iPhone's display can get seriously bright, whether LCD or OLED. When you're in bed at night or in a dark room where you don't want to disturb others visually, the brightness is even more noticeable. But there are a few built-in ways in iOS to reduce brightness below the default levels for less eye strain and other reasons.
Hello Hackers/Viewers, It is a new day, and you might be thinking, It is so boring, why not try to be cool with computers in front of my friends? That is why, I have made this tutorial to make fake viruses using notepad to look cool!