Essay writing is the bane of most students' educational existence. Whether you're a college student tired of slaving away over 30-plus page research papers or a high school student just trying to get through AP Language, chances are you'd love to find a way to cut down on all the writing. Before you spend hours googling facts and figures to cram into your next paper, work smarter by cutting down on content.

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.

Welcome back, my fledgling hackers! With this first article, I am initiating a new series intended to convey to my readers the skills necessary to develop your own exploits.

We always want to find more ways to help brilliantly lazy cooks make great-tasting food and save money and time in the process. Luckily, our Facebook fans are invaluable sources of information when it comes to getting cool tips, behind-the-scenes info, and more.

Can you tell when your friends are serving up a bunch of BS, or are you constantly oblivious, unsure if they're spinning a valid story? With so many ways to lie and fake information floating around, it can be impossible to tell what's the truth from what's complete BS. Here's how to sort through what you hear and find the real truth.

Welcome back, my tenderfoot hackers! In continuing my series on digital forensics using Kali, I want to introduce you to two complementary tools, both built right into Kali Linux. These are Brian Carrier's tools Autopsy and Sleuth Kit.

Welcome back, my novice hackers! It has become clear from some of your questions that quite a few of you are unfamiliar with the hexadecimal system, or simply, hex. The hexadecimal system is used throughout computing and if you have never studied this Base16 numering system, it may appear relatively opaque.

What would you say if I told you it was entirely possible—even desirable—to cook anything from a simple dinner to a great loaf of bread without using measuring cups, spoons, or a scale?

Apps that have no business accessing the internet can share your location, device ID, and other personal information with potentially malicious data snatchers. If you're connected to the internet on your Nexus 7 tablet, you're a potential target for cyber threats.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.

Welcome back, my budding hackers! In my continuing series on Linux basics for aspiring hackers, I now want to address Loadable kernel modules (LKMs), which are key to the Linux administrator because they provide us the capability to add functionality to the kernel without having to recompile the kernel. Things like video and other device drivers can now be added to the kernel without shutting down the system, recompiling, and rebooting.

Everyone hates to feel like they've been taken advantage of, especially when buying a used vehicle. The thought comes across every car buyer's mind... "Did I just get taken by that smooth-talking salesman?" When it comes to cars, how do you know if you're really getting a good deal, or if you're being offered a fair price for your car? After all, cars are most peoples second largest investment, so we need to make this decision wisely.

PRL, or Preferred Roaming List, basically tells your phone which towers to connect to first. Changing PRLs can improve reception and data speeds, and in some cases even give you access to corporate/test towers.

This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:

There’s a good chance that you’ll be alone in life one day, and no... I’m not talking about a couch-bound, dateless loser with a pocket pussy and a bag of potato chips. I’m talking about alone. In the wilderness. Hungry. Cold. Lost. You can’t stay in one place too long, so it would be nice to have something to carry your belongings in. Maybe it’s post-apocalyptic land where you’re the sole survivor, and all the backpacks and rucksacks in the world are but mere ash. Either way, knowing this si...

The best wedding cakes are tall and regal. In this tutorial, learn how to stack a traditional wedding cake. Use this technique to create tiers and levels for your cake, and make it really stand out. Whether you are making the cake for yourself or designing for someone else, make sure you watch this video first for information on how to stack a simple wedding cake and impress wedding guests, no matter what!

Marlina Richardson teaches how to make traditional Columbian tamales in simple steps. Spread out some of the paste on a leaf and add some rice in its center. Add a piece of pork, chicken, egg, some slices of carrots and potatoes and some more paste. Now fold the leaf carefully and tie it up, repeat the same process to make more of them. Finally cook it well and serve hot.

This video presents a system for automatically producing a wide variety of video enhancements and visual effects. Unlike traditional visual effects software (e.g., After Effects, Shake, Boujou, etc), the system is completely automatic and no manual labor is required from the user. The major limitation of the work is that it can currently handle only videos of static scenes (i.e., videos shot with a moving camera but containing no moving objects in the scene). Efforts are being made to lift th...

This origami light saber actually needs a rectangular piece of paper, instead of the traditional origami square paper. This video demonstration uses foil origami paper, for an authentic look and finish. Watch this video origami tutorial and learn how to fold an origami lightsaber.

Forget the takeout, watch this how to video and learn how to cook Job Chae. Job chae is Korean stir fried noodles with vegetables. Preparing and cooking this traditional Korean dish is very simple.

This video origami tutorial shows how to use the traditional Japanese art of paper folding to make a pretty paper rose. You might not have money to buy someone flowers, but you can always make your own. Follow along with this instructional video and learn how to fold your own paper rose.

Watch this how to video and learn how to wrap a shemagh, traditional headdress of Arab men.

This is the first part of the video showing how to fold a 3D 12 point star using Origami techniques and paper. Learn how to use the traditional Japanese art of origami to fold a three dimensional 12 point star.

In this lesson,you will learn how to play one of the most famous of ALL Jewish songs; "Hevenu Shalom Aleichem". The transliteration from Hebrew, and the translation into English of the words of this song is as follows:

SQLite is a small C library that implements a self-contained, embeddable, zero-configuration SQL database engine. SQLite implements a large subset of SQL-92 and stores a complete database in a single disk file. The library footprint is less than 250 KB making is suitable for use in embedded devices and applications where memory space is scarce.

Illustrator and Character designer Joe Bluhm goes over his thoughts and process while digitally painting an exaggerated animal sketch in Illustrator. You can apply these principles to any digital or traditional drawing mediums. Good video for people who learn visually with little verbal direction.

In this Mexican food recipe, you can learn how to make the traditional Mexican breakfast called chilaquiles.

Next time you have a backyard bash, serve up a tray of yummy pigs in a blanket. In this recipe, hot dogs are wrapped in light, flaky pastry dough and topped with an egg wash. o make this recipe, you will need:a package of hot dogs, though you can substitute sausage or less traditional types of hot dogs, like turkey or tofu, package puff pastry dough, egg yolk, optional. Homemade pigs in a blanket look delicious, and they are really a home run hit with everybody.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

Make a table lamp from home with some tools, wood, and woodworking knowledge. Learn how to make a table lamp base out of wood in this free video on home decor and lighting.

Watch this instructional origami video to learn how to fold an origami paper dragon. This is a fairly difficult origami dragon to fold, and it deviates a bit from the more traditional Japanese origami dragon. You may want to use a pen to further sculpt the dragon wings.

Watch this instructional video to fold a traditional Japanese origami morning glory. You will need a colored piece of origami paper for the flower blossom and a green piece of origami paper for the folded leaf. You will also need a pair of scissors and a small amount of glue. The video includes verbal instructions in Japanese, although the visual guide is quite clear.

Expert tattoo artist Rick Wyckoff offers a wealth of knowledge on the history of tattoos, explains how the tattoo machine works, and offers tips on how to care for a new tattoo, how to preserve the pigment, and how to deal with the pain that comes with being tattooed.

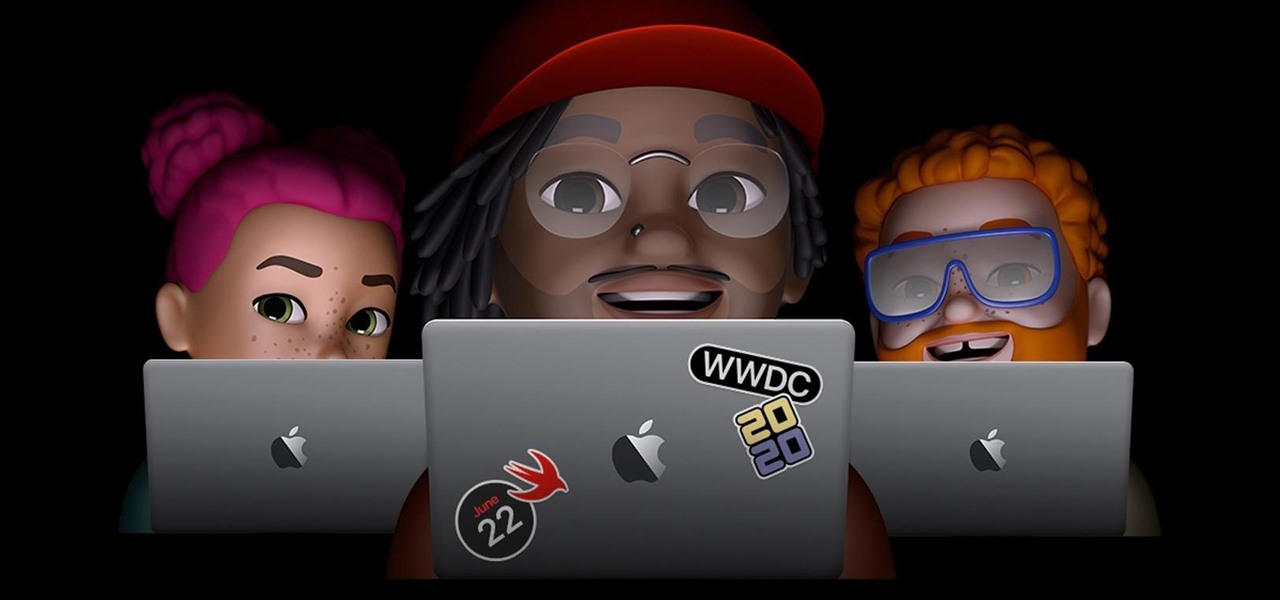
For the last three years, Apple has hosted its Worldwide Developers Conference at the San Jose Convention Center, but thanks to the COVID-19 pandemic, WWDC 2020 is now an online-only event. So what can you expect from the new virtual format and when and how can you watch the keynote and developer sessions?

In many urban areas, GPS doesn't work well. Buildings reflect GPS signals on themselves to create a confusing mess for phones to sort out. As a result, most modern devices determine their location using a blend of techniques, including nearby Wi-Fi networks. By using SkyLift to create fake networks known to be in other areas, we can manipulate where a device thinks it is with an ESP8266 microcontroller.

The landscape of podcasting has exploded in recent years, with everyone from dedicated longtime podcasters reaching the mainstream spotlight, to traditional media personalities moving from TV, radio, and newspapers to grab a slice of the listening pie. The good news is that the barrier to entry is relatively low, so even if you're not a celebrity or media luminary, you can still get your voice out there by starting a podcast.