Why play a ukulele? Well, other than the fact that it looks like a baby version of a guitar and therefore really damn cute, it creates a light, pleasant sound that resonates well with playing light melodies on the sand at the beach.

In this video tutorial, viewers learn how to draw Homer Simpson from the animated shot, The Simpson's. Begin by making a light outline of where the top of the head, sides of the head, ear and neck will be. Then do a light sketch of where the mouth, nose and eyes will go. Make the eyes large and make one eye overlap the other. Also make the nose into a sausage shape and mouth into a lemon shape. The eyes should be overlapped by the nose. Make the top of the ear line up with the bottom of the m...

The Survival Podcasting present how to handle leggy or spindly seedlings that have grown too fast. Potted swiss chard seedlings are used as examples. The seedlings are growing well but are a bit floppy or spindly. This happens because the warmth from being started indoors encouraged their fast growth but since there is not enough light for them, they started reaching for the light. A `head space` is developed between the root and the leaves that makes the seedling flop over. A simple trick to...

Learn how to apply makeup for hooded eyes. First apply a light base to the eyes. Use a light shimmery color to the lid using a flat brush. Add a medium to darker color on the crease. Use the darkest color above the crease and blend in well. Small circle motions work best in blending the colors. Use a color close to your skin tone to blend in the area from the tear duct to the eyebrow. line the upper lash line with a silver liner to bring attention. Using a pencil brush, smudge darker color on...

Miss Jessica Harlow replicates the makeup look from Britney Spears' music video "If U Seek Amy." This tutorial focuses on applying eye makeup.

The SSC P7 Flashlight is a tactical torch that's pretty bright at 900LM. But, it's totally possible to make it just a little brighter.

Here is a simple gradient eye look created with Cool Heat Mac products. Follow along and learn how easy it is to apply this dark and light blue eyelid color.

This is how to use a magnesium fire stick. Steps:

Chlorophyll glows blood red under a black light. Here is an easy and cheap experiment you can do at home to see the results. Just check out this video tutorial to learn how to take a handful of green spinach, some rubbing alcohol, and a blender to prep the amazing red glowing liquid. Then, just filter it out with a coffee filter and bottle it up. Then, get the black light out and get ready to party.

In this photography tutorial video, the self-appointed "Prince of Cheap" shows you how to use natural light and enhance it with continuous fluorescent light for some really killer headshots that stand strong! This photographs are really strong. In this 5 minute clip, David explains his thought process while you watch one of his garage shoots that lead to great quality and many "How'd he do that?" exclamations. This time you'll be able to see him on his session! How much can you learn in 5 min...

This how-To video shows you how to make an attractive and romantic centerpiece for your wedding, engagement party, or shower. A lovely mirrored acrylic heart with the couple’s first names, also in mirrored acrylic, is the center point. Turn off the lights and light up the tea candles for that romantic moment! Coordinating ribbon, metallic paper poof flowers, and onion grass lend accents. This is also suitable for Valentine’s Day, Sweetest Day, anniversaries, and other romantic events.

Arabic eye makeup can look extremely beautiful. This video will teach you how you can apply various makeup and eyeshadow products in order to make your eyes look beautiful.

f you are going to be towing a trailer, using an enclosed cargo carrier with lights, or if you want to use an electrical accessory (such as lights, or a winch) you are going to need to add a wiring harness. This video will show how to install a wiring harness on a Chevy Express full size van. It also includes some helpful tips about installing the ground wire, using dielectric grease, and installing a bracket to hold the wires so they are protected from damage.

Driving around and notice an accident the road keeping you from getting where you need to go? Well, you're in need of a GPS navigation system. Check out this video tutorial on how to Use media functions on a TomTom Go 930 Traffic navigator device. You'll see how to use the GPS system in details and see all of the key features of the Go 930 TomTom, like playing music, listening to audiobooks, and watching videos.

Driving around and notice an accident the road keeping you from getting where you need to go? Well, you're in need of a GPS navigation system. Check out this video tutorial on how to use the TomTom Go 930 Traffic GPS navigator device. You'll see how to use the GPS system in details and see all of the key features of the Go 930 TomTom.

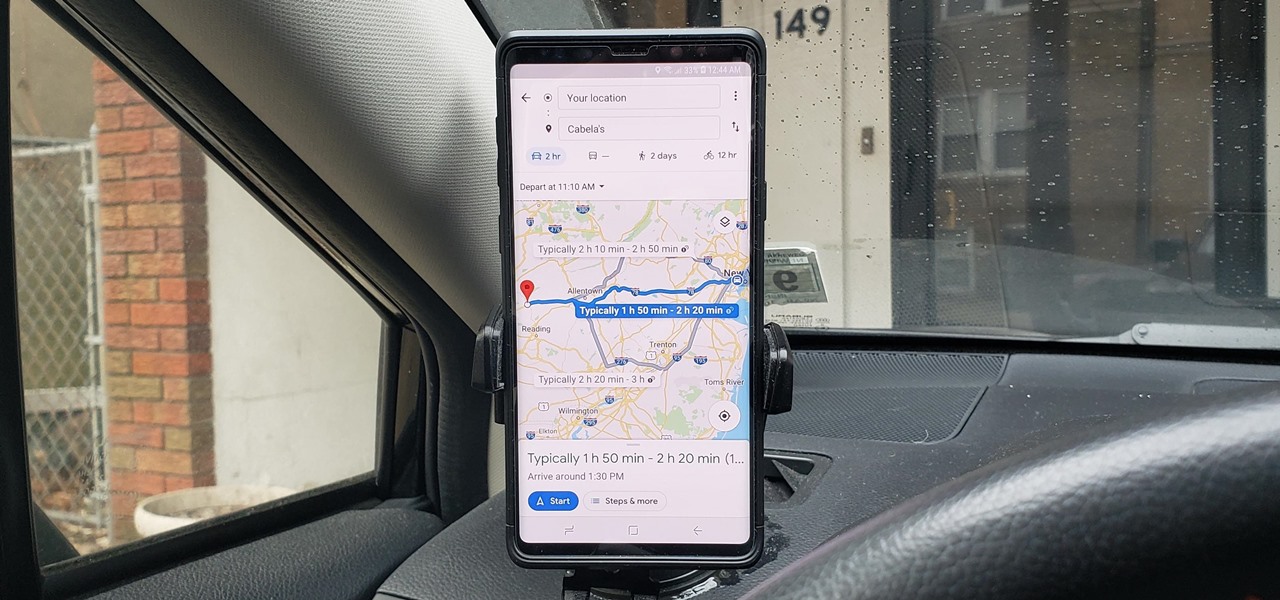
If you're in the market for a new house, how do you know what your commute would be like if current traffic is unseasonably low? Or if you're considering a new job across town and want to weigh the pay raise against the extra time stuck in a gridlock, how do you measure the discrepancy? Google Maps can help.

When joining a new network, computers use the Address Resolution Protocol to discover the MAC address of other devices on the same network. A hacker can take advantage of ARP messages to silently discover the MAC and IP address of network devices or actively scan the network with spoofed ARP requests.

Picture this: You finally get that awesome angle, the perfect selfie. You can't wait to post it on your Instagram, except there's one problem — it looks a little flat and the colors just seem off. Maybe it's the lights? Or maybe your new smartphone camera isn't as good as you thought? How are your friends getting those beautiful photos they've been posting on social media?

As intuitive as Google Maps is for finding the best routes, it never let you choose departure and arrival times in the mobile app. This feature has long been available on the desktop site, allowing you to see what traffic should be like at a certain time and how long your drive would take at a point in the future. Fortunately, Google has finally added this feature to the app for iPhone and Android.

Christmas has arrived early for ARCore app developers, as Google just unwrapped a few iterative improvements to the augmented reality toolkit in version 1.6.

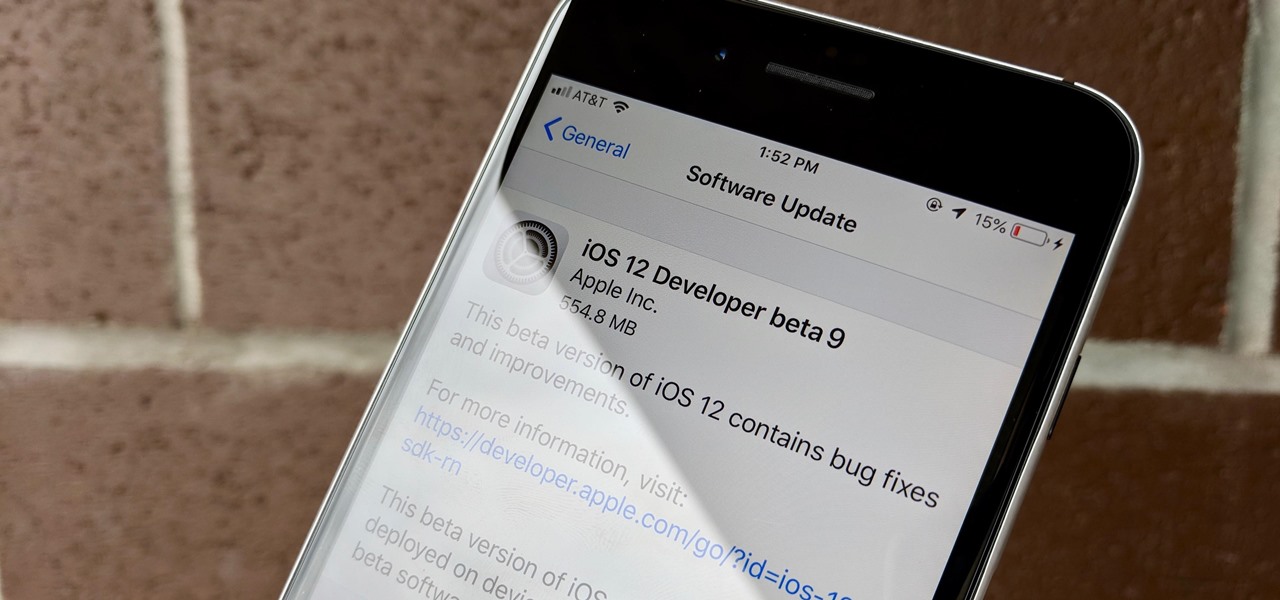
Can't say we didn't see this coming — Apple released iOS 12 public beta 7 on Monday, August 20, the same day it seeded the ninth version of the beta to developers. While the two betas may have different names, public beta 7 and dev beta 9 are virtually identical, so public testers shouldn't feel as though they are missing out.

Apple released iOS 12 beta 9 to developers on Monday, August 20. The company seeded the update just five days after releasing dev beta 8 to testers, itself a quick replacement for the problematic beta 7. This update was followed closely by public beta 7, confirming Apple's new same-day release schedule for both developer and public betas.

While Vuzix is beefing up the processing power of its next-generation smartglasses with the Qualcomm Snapdragon XR1, the company will also give its devices an upgraded display engine.

The LG G7 ThinQ will likely be lambasted for its notch and awkward name, but one thing they seem to have gotten right is the new display. The G7 ThinQ will give many a first look at a new type of panel with lots of promise. While it was previously limited to TVs, from what we know, it should really shine on a smaller screen.

Avegant Corporation has begun shipping display development kits based on its light field technology that other companies can use in their augmented and mixed reality devices.

Virtual private networks, or VPNs, are popular for helping you stay anonymous online by changing your IP address, encrypting traffic, and hiding your location. However, common IoT devices, media players, and smart TVs are hard to connect to a VPN, but we have a solution: Turn a Raspberry Pi into a router running through PIA VPN, which will ensure every connected device gets the VPN treatment.

The new iPhone 8 and 8 Plus models come with a gorgeous Retina HD display with Apple's True Tone technology, which automatically adjusts the white balance on the screen to match the ambient light around you. The iPhone X also has True Tone built into its Super Retina HD display. However, if you're coming over from any previous model iPhone, it may look a little strange in some situations.

The dark web is an intimidating place for a newbie hacker, but it's a powerful tool once you've learned to navigate it safely. To help you out with that, this guide will cover some need-to-know information for traversing the dark corners of the internet while keeping your identity and data safe. (Hint: Using Tor is not enough.)

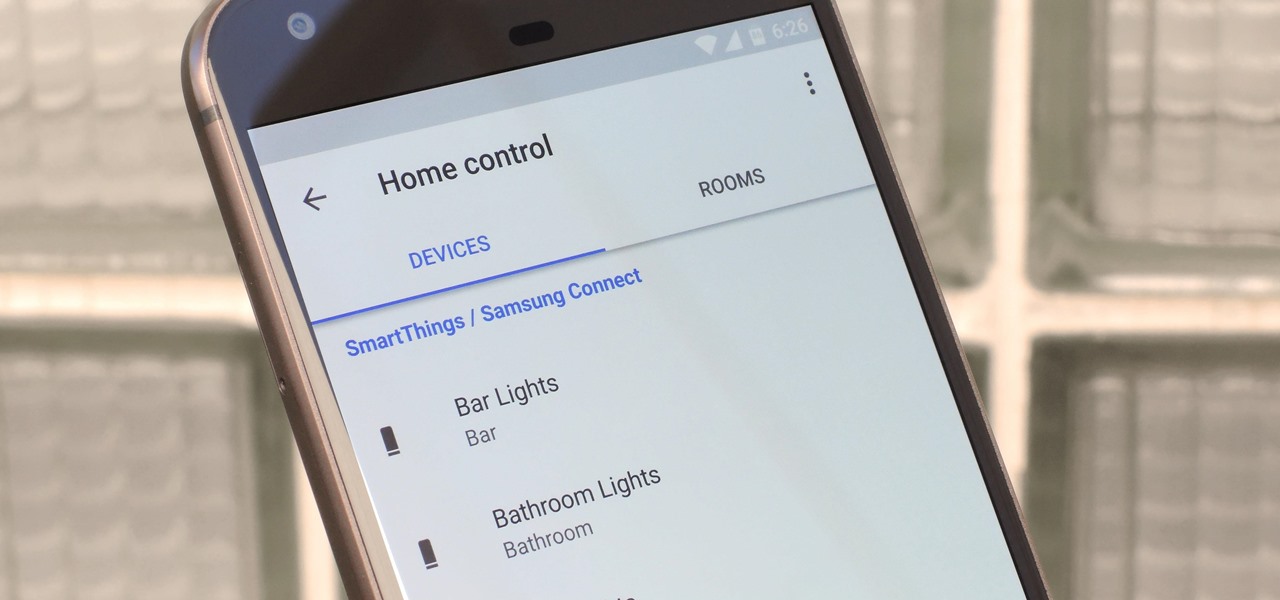
The world around us keeps getting smarter. Not only do we have advanced AI services like the Google Assistant, but now we've got the Internet of Things connecting physical objects to the digital world. It's amazing when you think about it, but the real sci-fi stuff starts to happen when these two technologies intersect.

Well, well, well. Uber, we knew you were investing a ton of money into creating self-driving taxis and flying cars, but what we didn't know is that you were already testing out your driverless vehicles on the streets of New York City.

Welcome back, my greenhorn hackers! Over the years, I have written many articles here on Null Byte chronicling the many the hacks of the NSA, including the recent hack of the Juniper Networks VPN. (By the way, my speculation in that article has proven to be correct. The NSA did embed a backdoor on those devices.)

Greetings all. Today I intend to append a new series to my mini-collection of posts. This series will consist of informative guides for the purpose of depicting certain aspects of the White Hat profession that I believe are of profound importance. Furthermore, I will keep this series simple for everyone to follow, regardless of your tech level. So without further ado, let's get right into it.

Welcome back, my budding hackers! As I have mentioned many times throughout this series, knowing a bit of digital forensics might keep you out of a lot of trouble. In addition, digital forensics is a burgeoning and high paying career. Some knowledge and certifications in this field will likely help you land a Security Engineer position or put you on the Incident Response Team at your employer.

When I tried to set up an eviltwin for a MitM-constelation in kali 2.0, I couldn't provide internet to the victim. The origin was the brctl bridging. I have read many tutorials but all of them where explained in backtrack and older versions of kali. So i was searching for a solution without using brctl and this solution will be explained now. This will just work on unencrypted wireless-environments.

You're smashing your keyboard to increase your screen brightness, yet it won't go any higher, but you know you've been able to set it higher before. Angered by this, you get up and move your laptop, only to suddenly notice that the display does in fact get a lot brighter.

Cortana, Microsoft's voice-activated personal assistant, originally launch on Windows Phone, but is now built directly into Windows 10 complete with "Hey Cortana" voice search (take that, Apple). It can help you locate files, set up reminders, control music.

Part 1: What is Popcorn Time? Part 2: What is a torrent?

It's Friday night, nail polish, makeup, wine and girlfriends at the ready! But what do you wear? Here's a little number for all the brunettes out there :)

The weather outside might be frightful, but heating bills are downright scary this time of year. Heat is absolutely essential during the winter season, but it's also really expensive. If you aren't blessed with a fireplace or unlimited disposable income, fear not, because you can still heat your home on the cheap using flower pots and tea lights—even if the power goes out.

Welcome back, my budding hackers! We've spent a lot of time learning to compromise Windows systems, and we've successfully compromised them with Metasploit, cracked their passwords, and hacked their Wi-Fi. However, very little time was spent developing ways to extract the information from the system once inside.