If it has an internet connection, it's got a huge attack surface for hackers. But what makes your phone even more dangerous is its portability and the collection of sensors it houses that can be just as good at tracking you as the camera and mic.

You might be giving out your name to every stranger you see, and you don't even know it. That iPhone of yours has a name — generally a combination of your first name and device model — and it broadcasts it to others via AirDrop, Personal Hotspot, Bluetooth, Wi-Fi, and other connections. Sure, it's useful to keep your device name simple and to the point, but there are upsides to changing it.

An attacker can create three, five, or even ten new Netcat connections to a compromised MacBook with one command. Performing complex post-exploitation attacks might otherwise be difficult from a single shell without this essential trick.
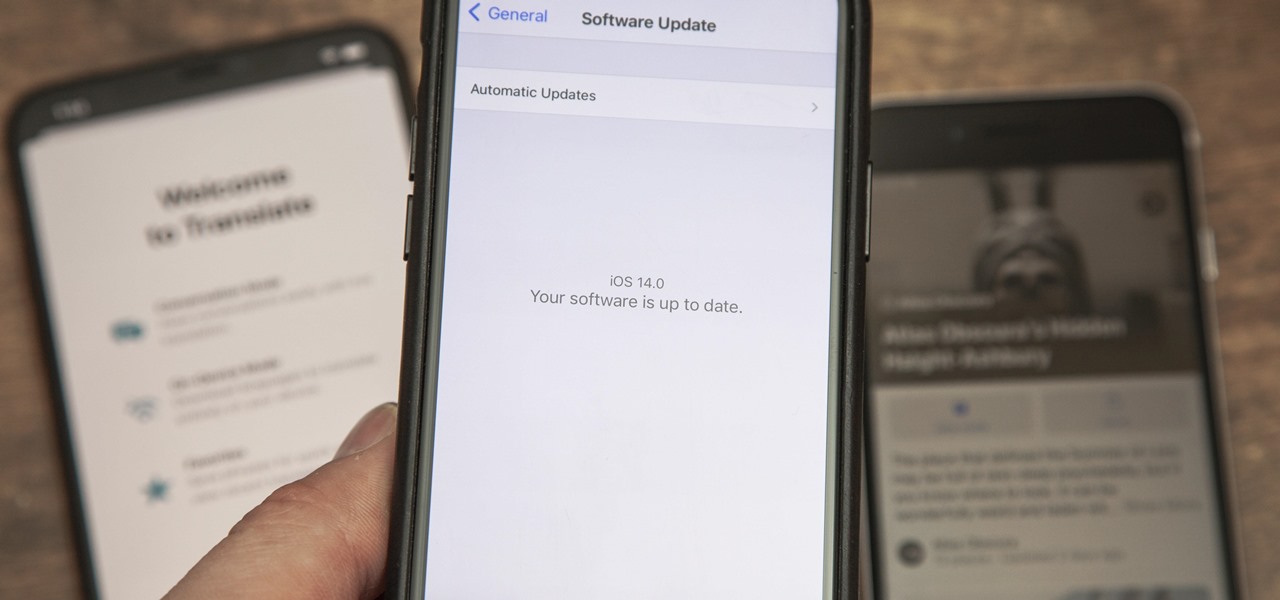
While the iPhone world's attention might be fixated on Apple's upcoming iOS 14 and all of its new features, it's still in beta. What's not in beta anymore? Apple's latest iOS 13 update — iOS 13.6 — which dropped on July 15.

Using a strong password is critical to the security of your online accounts. However, according to Dashlane, US users hold an average of 130 different accounts. Memorizing strong passwords for that many accounts is impractical. Fortunately, password managers solve the problem.

Trying to figure out which music streaming service to subscribe to can be a difficult task when the playing field is so crowded. Each has its benefits, as well as downsides, so finding the right one for your needs and wants can take a lot of overwhelming research. But we've done all the research for you to help you find the best music subscription your money can buy.

Over the past decade, Marvel Studios has been a dominant force at the box office, raking in more than $21 billion dollars. Averaged out over that span of time, the yearly earnings of those movies outweigh the gross domestic product of some countries.

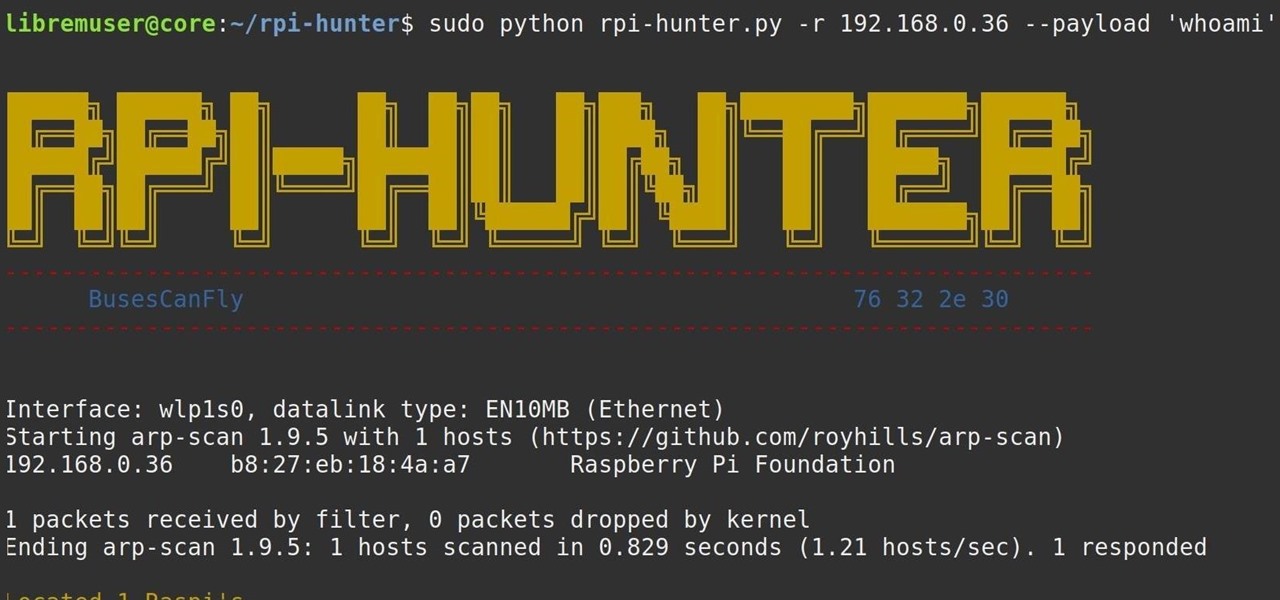
When setting up a Raspberry Pi, it's easy to overlook changing the default password. Like many IoT devices, the Raspberry Pi's default Raspbian operating system installs with a widely-known default password, leaving the device vulnerable to remote access. Using a tool called rpi-hunter, hackers can discover, access, and drop custom payloads on any weak Pi connected to the same network.

Traveling abroad can be a hassle. Between the flight, hotels, food, and the languages barriers, it can be a lot to manage. There's one tool you have that can help with all of this — your smartphone. Fortunately, nowadays, you don't have to change your carrier to continue using your phone.

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

You've protected your Ubuntu system from physical attacks, annoyed network hackers, and sandboxed potentially malicious applications. Great! Now, the next logical steps to locking down your OS include thoroughly auditing Ubuntu for weak points, using antivirus software that respects your privacy, and monitoring system logs like a boss.

Even though most phones don't have Oreo yet, Google has released Android 9.0 Pie. It's available on Google's own Pixel devices, and updates should soon be available to partnered devices from Essential, Nokia, Oppo, Sony, Vivo, and Xiaomi. We're already digging into it to highlight all of the features and changes.

While autonomous vehicles are almost assuredly the future of personal transportation, we are likely many years from seeing self-driving cars become as ubiquitous as manually-driven ones, as the auto industry has a myriad of government regulations and other constraints to contend with. Until then, augmented reality is looking like the next big thing in automotive technology.

Hi, everyone! Recently, I've been working on a pretty interesting and foolish project I had in mind, and here I'm bringing to all of you my findings. This guide's main aim is to document the process of building an Android kernel, specifically a CyanogenMod kernel and ROM, and modifying the kernel configuration to add special features, in this case, wireless adapter Alfa AWUS036H support, one of the most famous among Null Byters.

Apple AirTags are super helpful for keeping track of your keys, backpack, and other frequently misplaced items, but there are some pretty clever things you can do with them beyond finding regularly used stuff.

Apple's iOS 16.3 update for iPhone had impressive new features, but iOS 16.4 might impress you even more.

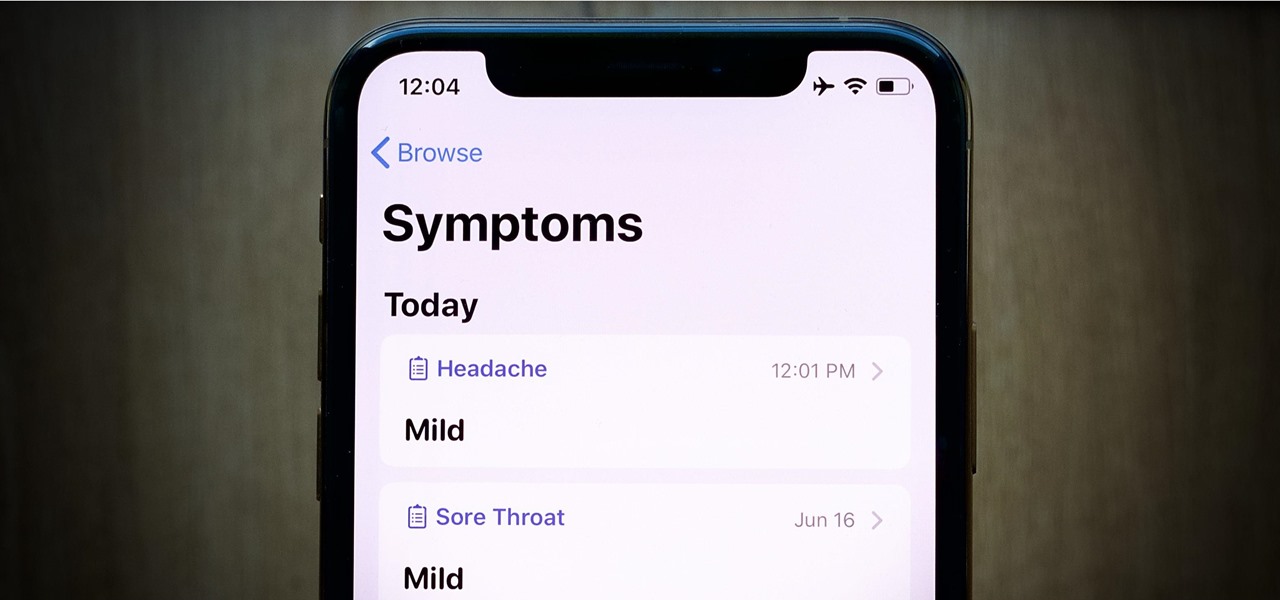
Live Activities is Apple's hottest new feature for iPhone, but it's not always straightforward. Sometimes you'll trigger one without realizing it, but it may seem frustratingly impossible to start one when you really want it.

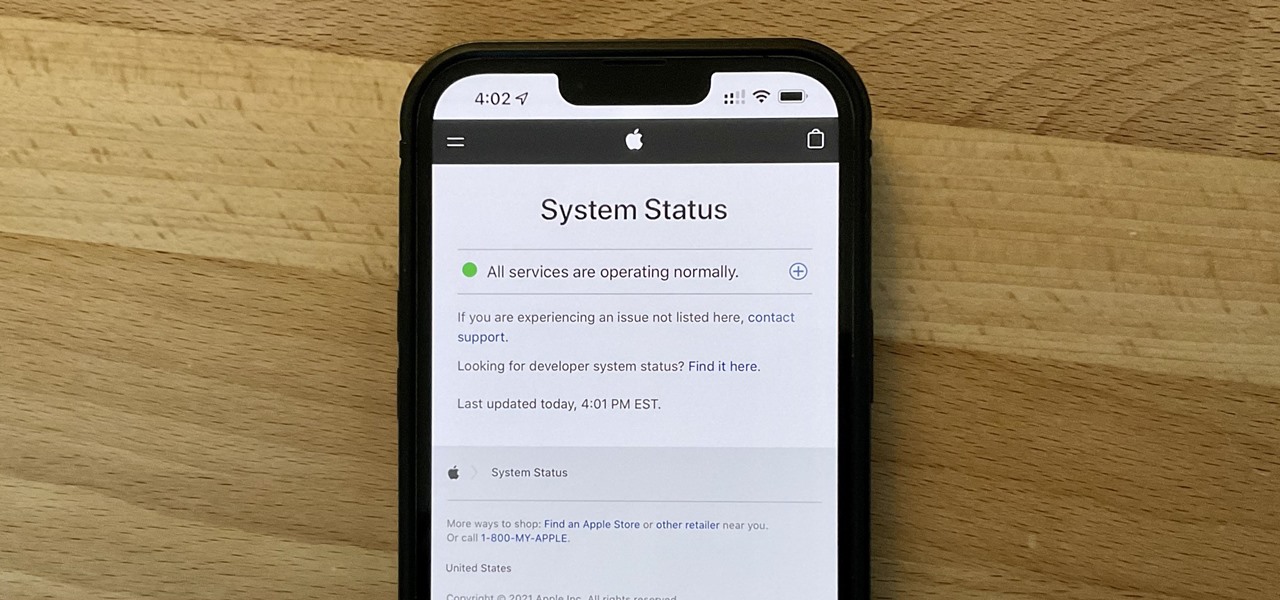
It can be very frustrating: You open your Messages app, send an iMessage, and then see that dreaded red exclamation point or horrible green SMS bubble. At this point, you may be curious whether it's just your iPhone or whether iMessage is broken for everyone, but how do you find out?

Apple released the second beta for iOS 15 on Thursday, June 24. The update includes FaceTime's "SharePlay" feature for the first time, a new Maps icon, updates to Focus mode, in addition to many other changes and bug fixes.

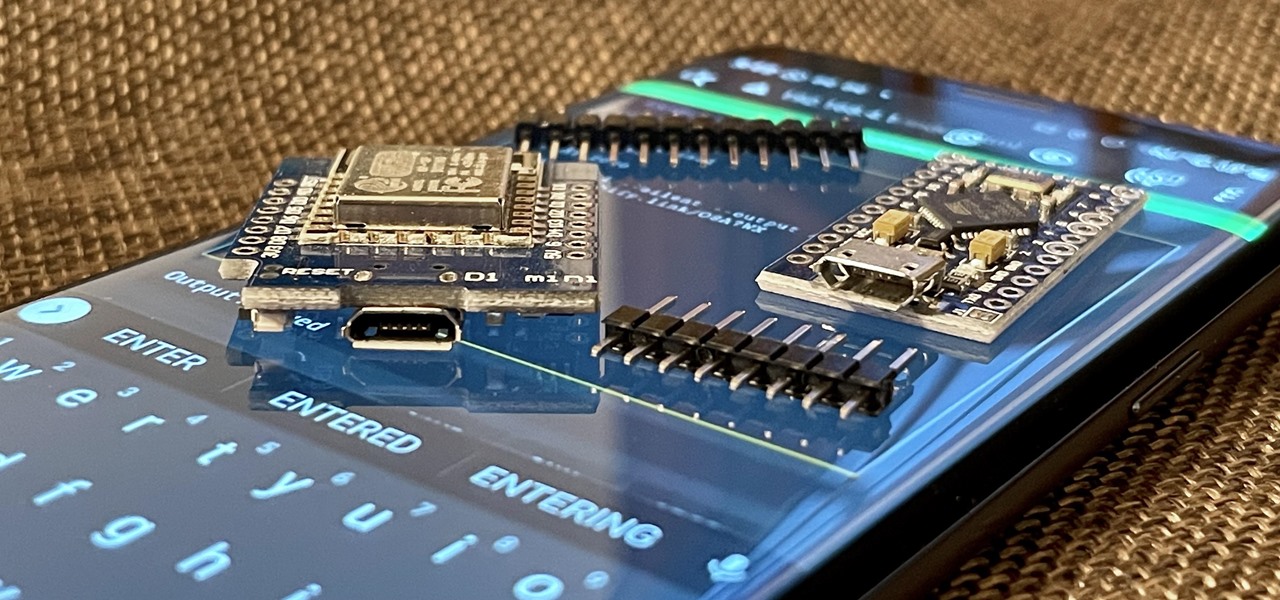
With just two microcontrollers soldered together, you can inject keystrokes into a computer from a smartphone. After building and programming the device, you plug it into a desktop or laptop, access it over a smartphone, and inject keystrokes as you would with a USB Rubber Ducky.

The new iOS 14 for iPhone arrived Wednesday, Sept. 15, 2020, alongside iPadOS 14, and there are a lot of features to uncover. Improved widgets. Better home screen customization. Exciting Messages improvements. New abilities in Camera and Photos. There's so much here that it'll take months for you to learn everything by heart.

What appears to be an ordinary MP4 may have been designed by an attacker to compromise your Linux Mint operating system. Opening the file will indeed play the intended video, but it will also silently create a connection to the attacker's system.

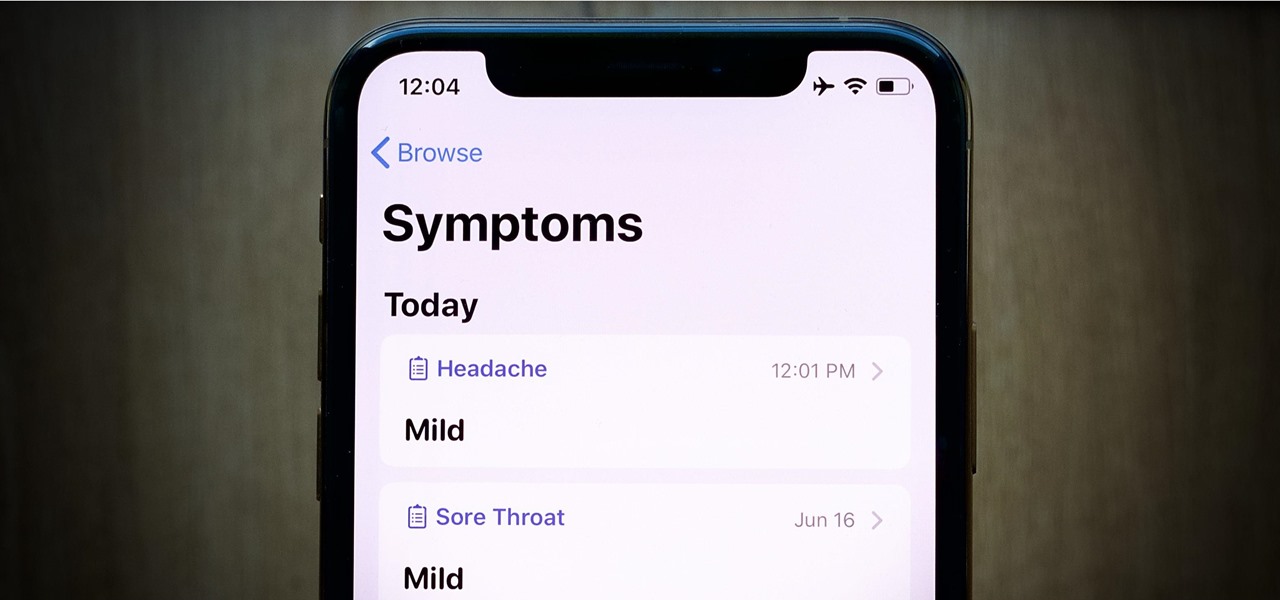
Apple's iOS 13 has been available for beta testing since June, and the stable release pushed out to everyone on Thursday, Sept. 19. To help you make the most out of iOS 13 for iPhone, we've rounded up everything you'll want to know, whether a colossal feature, small settings change, interface update, or hidden improvement.

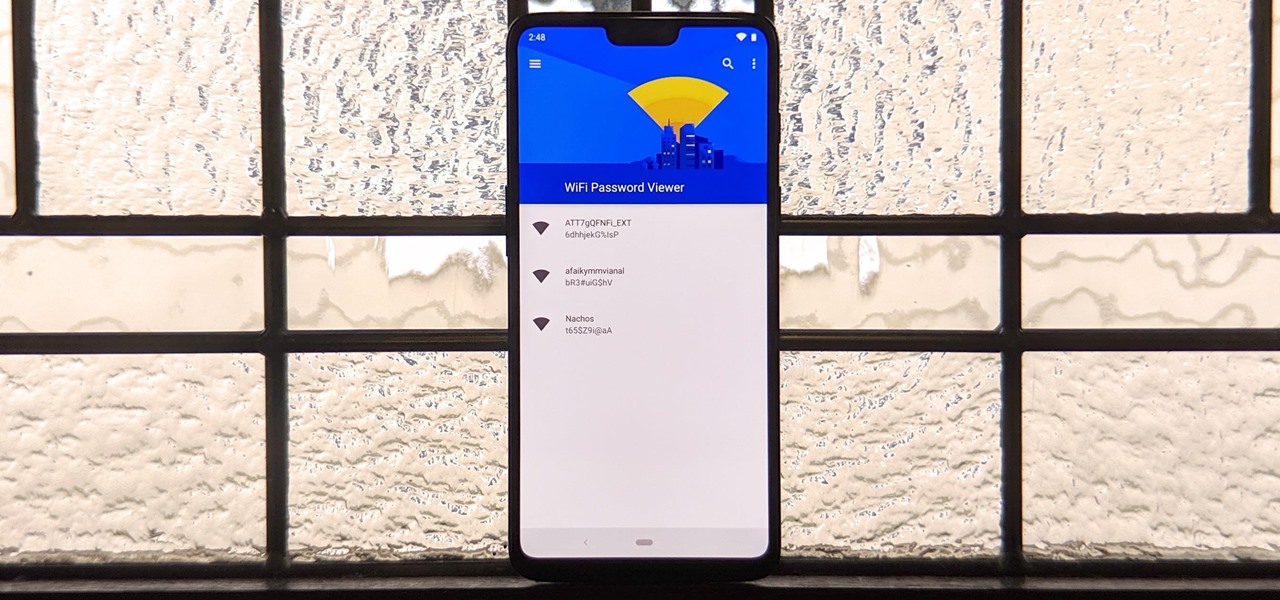
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

Data can be injected into images quickly without the use of metadata tools. Attackers may use this knowledge to exfiltrate sensitive information from a MacBook by sending the pictures to ordinary file-sharing websites.

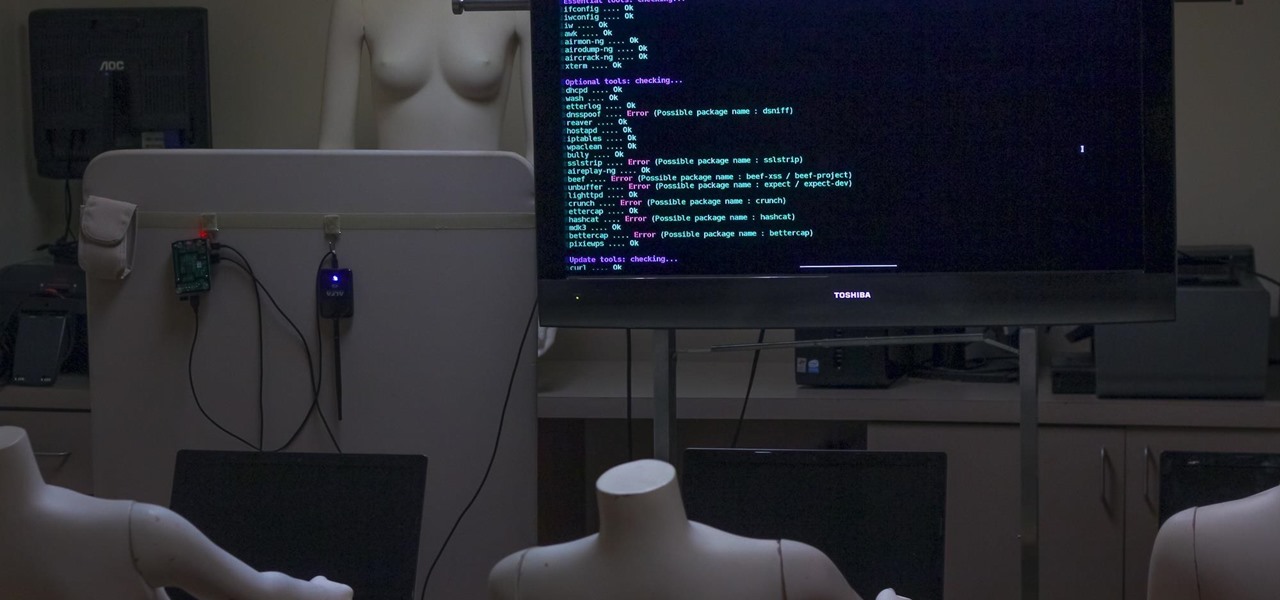
Airgeddon is a multi-Bash network auditor capable of Wi-Fi jamming. This capability lets you target and disconnect devices from a wireless network, all without joining it. It runs on Kali, and we'll cover installing, configuring, and using its jamming functionalities on a small, inexpensive Raspberry Pi. When done correctly, it will deny service to a wireless network for up to several blocks.

Congress is asking top U.S. defense contractors to disclose their corporate plans if the military is forced to cut $500 billion from its budget early next year, putting the companies in the middle of a political fight between Republicans and the White House. U.S. defense firms drawn into Congress budget politics - CNN.com.

Are these guys running for politics? I'm buying whatever they are selling. Really great trailer with an overview of what Guild Wars 2 will bring new to the MMO scene. Narrated by the developers of the game, they offer some good points on what you can expect from the game when it launches early next year (date has yet to be determined, but it does not look like it will make it into the holiday period).

In this Red Giant tutorial, Aharon Rabinowitz shows you how to create a realistic traffic pattern backdrop - great for a scene in which the camera overlooks a low lying, but developed area - perhaps looking down from a high hill onto a residential neighborhood.

This is a video for children to learn about the traffic light for pedestrians use. It is an interaction game where the children can push the proper light to answer questions pertaining to the traffic light. Teach children about traffic lights.

These are a series of clips to show you how to deal with the different situations when turning right at traffic lights. In the U.S. or countries that drive on the right, these principles will apply to left hand turns. Deal with right turns at traffic lights - UK.

In this video tutorial, we learn how to create a realistic traffic pattern backdrop within After Effects through use of the PlaneSpace and Text Anarchy plugins. Whether you're new to Adobe's popular motion graphics and compositing software or a seasoned video professional just looking to better acquaint yourself with the program and its various features and filters, you're sure to be well served by this video tutorial. For more information, including detailed, step-by-step instructions, watch...
If you haven't heard already (the mainstream media doesn't cover this), the 2012 Bilderberg meeting in the US is under way. What is this meeting? We don't really know. It's when the top politicians and some of the most powerful people in the planet meet in a location and bar all access to it, thereby keeping their motives a secret.

I personally don't owe him an apology because as soon as the plane left Argentina for South Africa, I was done criticizing and started rooting for the team, regardless of who was in it. Nyeeeh! ;p

Hello World! Welcome to the place wholly devoted to the local surf of Southern California. I am like many people a transplant from the East Coast. I started surfing when I moved here for college 8 years ago.

Curious about the newest obscure zines to hit the streets? Words and Stuff is a great website full of reviews on zines (mostly in the punk, politics, eroticism, and art arena) that either give the thumbs up or the thumbs down on what's worth purchasing.
Sen. Dick Durbin, D-Ill., the Senate majority whip, asked on NBC’s Meet the Press, “Why is Mitt Romney running away from his company, Bain Capital, like a scalded cat? Because there’s abundant evidence that under Bain Capital they were exporting American jobs to low-wage countries and he doesn’t want to be associated with it.” Durbin says Romney running from Bain 'like a scalded cat' - NBC Politics.
The rhetorical skirmish over this question is the prelude for bargaining that’s likely to culminate after Election Day as President Barack Obama tries to persuade Congress to raise income tax rates on people with incomes over $200,000 and Republican try to keep the current tax rates in place at least for 2013.