Want the convenience of a throwaway email address without all the hassle? How about anonymous text messaging so you can get to know someone before giving them your real information? Gliph has you covered. Gliph is a service that lets you create an identity around a set of three to five symbols called "artifacts" instead of your name, phone number, or email address. You choose how much information you reveal, and anytime you communicate with someone else who has Gliph, the data is protected us...

So, your buddy's getting married and it's time for that age-old tradition the "bachelor party". Make sure the party goes off with out a hitch by remembering the goal is to have fun and not to ruin the wedding, get a DUI or destroy the reputation of your friends. Plan accordingly.

Often considered the world’s oldest wind instrument, the didgeridoo originated among the Aboringine tribes of Australia. It looks like a simple wood tube, but by vibrating their lips, players can produce harmonic resonances which result in the instruments distinctive droning sound.

Summer is coming so start saving your popsicle sticks (or more conveniently buy them from a craft store) to make your very own mini American flag. This is a great activity to take into the class room or just to pass the time on a summer’s afternoon.

JB skating combines roller-skating with a variety of dance styles. If you’re board of your normal Friday nights or looking for a fun and funky way to exercise, grab a pair of skates, watch a few videos and then try it for yourself.

A butterfly twist is an acrobatic kick that originated in china, get expert tips and advice on martial arts in this free video.

Reiki is a form of holistic healing that originated in Japan. It is a way of magnifying the healing "ki" energy of the hands. Reiki uses the same kind of non-physical "ki" energy martial artists use to nourish the body's health and vitality.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

Virtual reality holds the promise of electronically visiting distant places we'd otherwise struggle to reach, but that teleportation-esque ability isn't possible without the right content. YouVisit created a platform that makes it easy for almost anyone to create immersive 360-degree experiences so we can map our lives and see the world through the eyes of our fellow humans.

Developer Options is your first step to becoming a power user. If the Pixel 4a feels a bit slow, Developer Options can fix that. You want to root your device for unprecedented controls and powerful apps? You need to enable OEM unlocking in this hidden menu. ADB, secret features — Developer Options is where it all originates.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

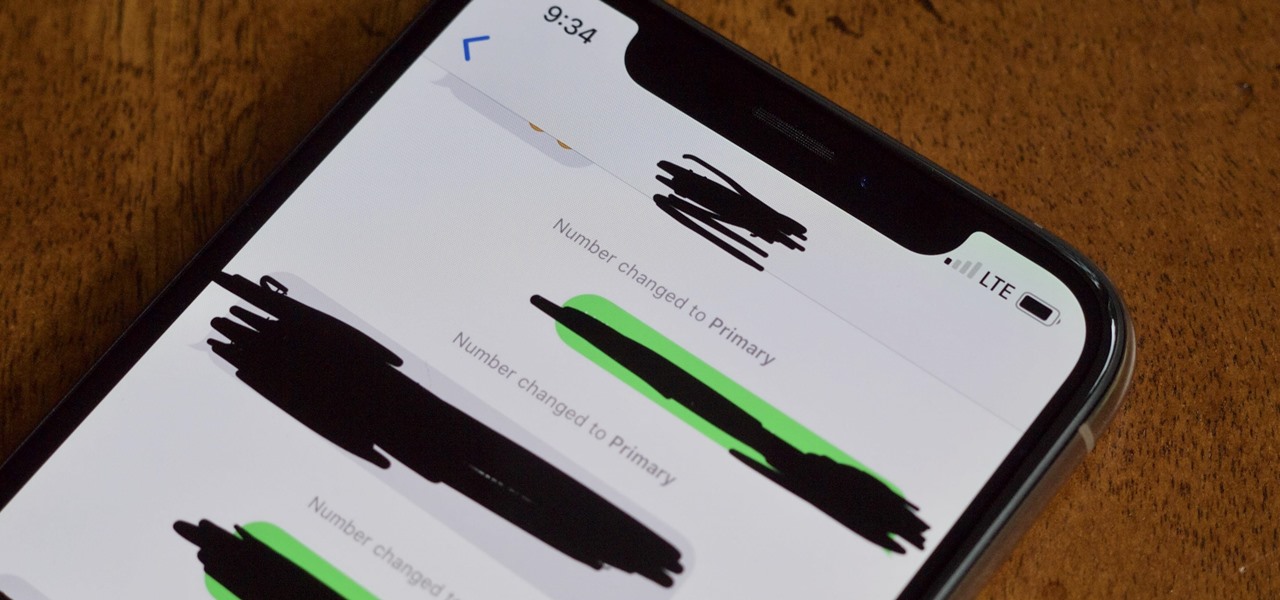
The iPhone XS, XS Max, and XR aren't the newest devices from Apple Inc., but all three have a serious problem in Messages. When sending a friend an SMS/MMS text rather than an iMessage, the phrase "Number changed to Primary" appears in front of every message. What gives? If this issue is driving you mad, there are a few tricks that may exterminate the bug until Apple gets around to issuing a patch.

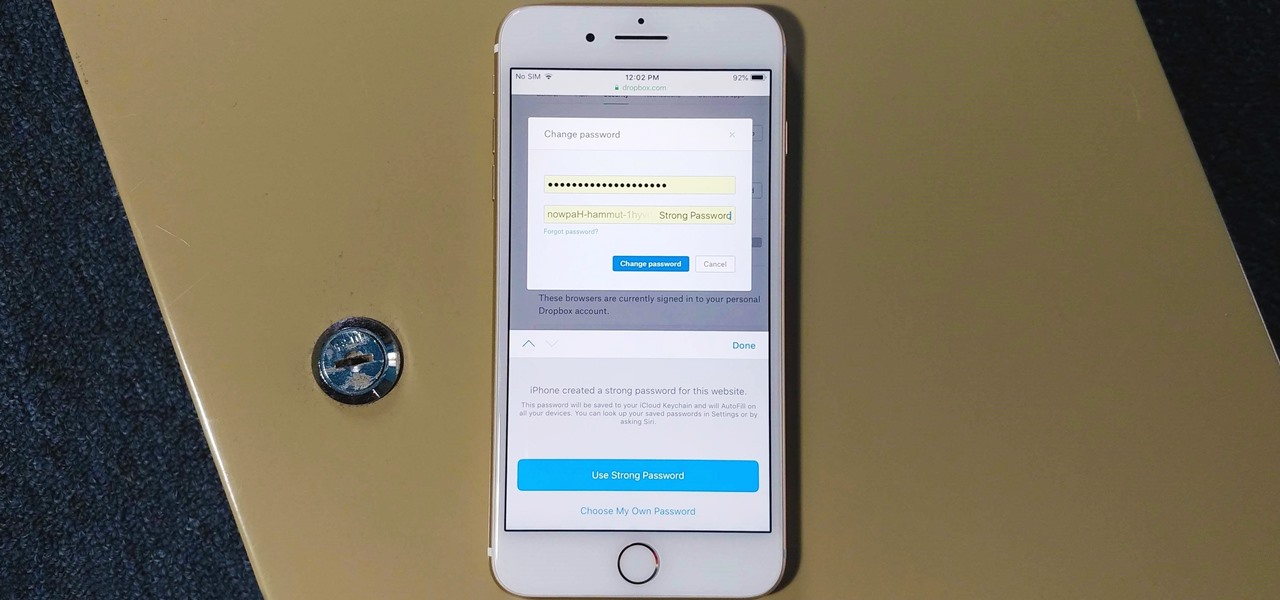
The option to auto-fill passwords on your iPhone has been around a while now, but iOS 12 improves on it by suggesting strong passwords when first creating an account online in Safari or within apps. Apple has also added "password reuse auditing" for your iCloud Keychain, where all your logins are housed, which will find and change your weak passwords to strong ones.

There are some nasty iOS bugs out there, many determined to crash the Messages app. For example, in February 2018, we saw a Telugu character render the iPhone messaging app totally useless. While that bug has been fixed, the nightmare continues in a new bug, aptly dubbed the "Black Dot."

Traditional subdomain enumeration techniques create a lot of noise on the target server and may alert intrusion detection systems to an attacker's intentions. For a stealthier approach, there's a tool with the capability of finding hundreds of subdomains related to the target website without alarming the server administrators.

OnePlus is on track to deliver Android 8.0 Oreo to its flagship users by Q1 2018. Open Beta 1 was released for the 5T in late December, and we just received Open Beta 2. But this update isn't just tweaks and bug fixes, OnePlus has included a few new features to enhance the Android experience.

Citrus greening disease — caused by a bacteria spread by psyllid insects — is threatening to wipe out Florida's citrus crop. Researchers have identified a small protein found in a second bacteria living in the insects that helps bacteria causing citrus greening disease survive and spread. They believe the discovery could result in a spray that could potentially help save the trees from the bacterial invasion.

In the worst measles outbreak in the state since 1990, the Minneapolis Department of Heath races to contain the spread of an infection believed to have originated from an infected traveler. Mistaken attitudes and unvaccinated travelers are creating a world of hurt and disease for Americans. A recent study found that more than half of eligible travelers from the US are electing to skip their pre-trip measles vaccine.

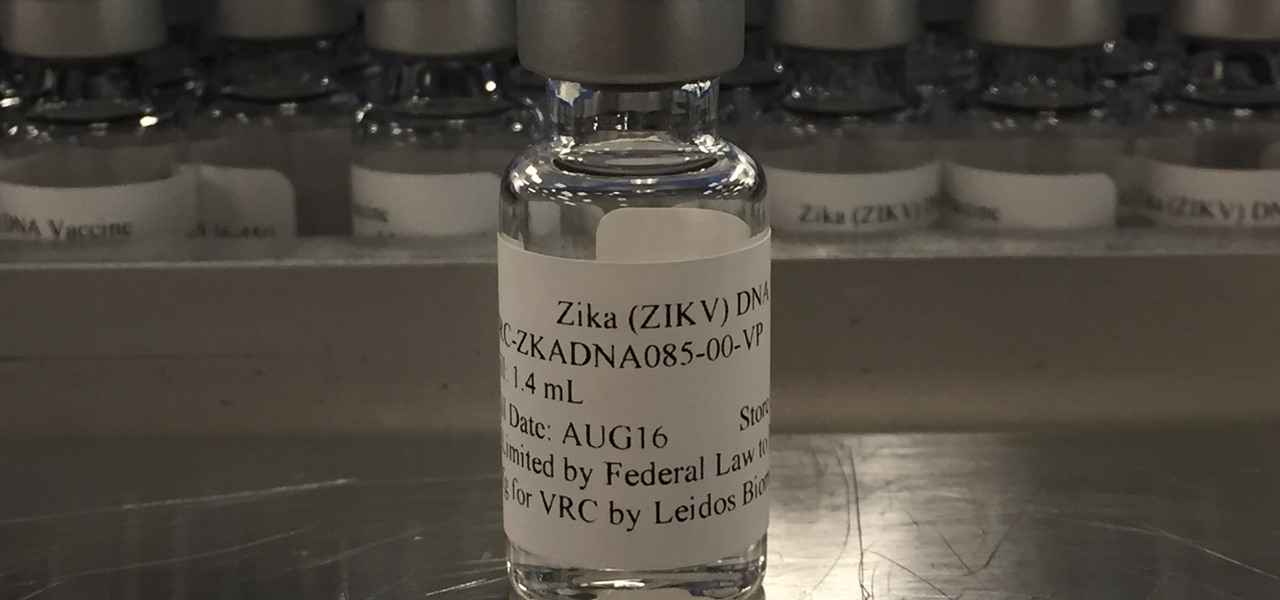
Phase 2 of a Zika vaccine trial began in the United States this week, along with Central and South America.

As a fan of the HTC One series, I almost always upgrade my phone soon after the new model becomes available. I purchased the M7 when it first came out, upgraded to the M8 shortly after its launch, and then jumped on the M9. However, I stopped right there.

A tiny louse is responsible for decimating the citrus industry. Diaphorina citri, the louse in question, better known as the Asian citrus psyllid, harbors and spreads the "Candidatus Liberibacter asiaticus" bacteria that causes citrus greening disease.

The iconic, lovable gummy bear originated in Germany, where it goes by the name Gummibär— but that's not what makes it so much fun. The base of gummy bears is made up of gelatin, which gives them the signature elasticity that makes you feel like a kid again. But the fun doesn't have to stop there.

After seeing the title of this post from me, you might be thinking, "Why did The Joker made another post on a topic on which we already have a nice sticky post?"

Before I get ostracized by all of you whisky lovers who live and die by whisky served neat, let me say my piece.

Everyone has the same five spirits in their bar: vodka, rum, whiskey, tequila, and gin. They're all great, but every so often the mood strikes to try a cocktail with a little something different. We'd like you to meet three spirits from South America that would make a welcome addition to your next cocktail party.

Now that the Super Bowl is over, you might find that you have an econo-sized bag or two of opened potato chips slowly going stale in your pantry. After all, there are only so many bowls of Buffalo Chicken Pizza Beer Dip you can eat with 'em—and you definitely don't want them to get so old that you have to throw them out.

I know people who hate mayonnaise. I know people who detest ketchup. But I know almost no one that hates mustard, and that's because mustard has a complexity and depth that bland mayo and ketchup do not. Mustard runs the gamut from smooth and subtle to sharp and spicy, especially when you know how to make your own.

The Spanish and Portuguese introduced many things (some desirable, some not, depending on your POV) to Mexico in the sixteenth century: Christianity, language, and lots of flora and fauna.

This is evil and it destroys people. Let's just get that out of the way. Nonetheless, suppose you need to make someone distrust their own memory and perception of reality. Suppose you want someone to believe in you more than they believe in themselves.

This Hello Kitty drawing is a sketch of an image from the "Hello Kitty" website. It's adorable and isn't the typical image you see on a Hello Kitty character. DragoArt has this video tutorial on how to draw Hello Kitty. Get more detailed instructions on the step-by-step cartoon drawing here.

West Coast Swing is a partner dance which incorporates Blues, Rock, and Country Music. Learn the dance steps for ladies and gentleman in West Coast Swing, and moves such as the Sugar Push, Under Arm Turn of West Coast Swing, and the right and left side passes.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

In a way, Twitter is the town square of our era, where people can share and discuss ideas on a wide variety of topics. While the tech giant has its own app for Android, it's pretty bare-bones when it comes to features. This has paved the way for third-party clients that are rich with customization options.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

Welcome back, my hacker trainees! A score of my readers have been begging for tutorials on how to hack Wi-Fi, so with this article, I'm initiating a new series dedicated to Wi-Fi hacks. This will probably be around 6-9 articles, starting with the basics of the technologies. I can hear you all groan, but you need to know the basics before you get into more advanced hacking. Then hopefully, developing your own hacks.

You no longer have to resort to a third-party email client on your iPhone to schedule messages to send whenever you want. Apple built the scheduling functionality into its Mail app, and it works with any email service you use in Mail, whether that's iCloud, Gmail, Yahoo, Outlook, or another service.

You don't need an obsessive ex stalking you to benefit from the ability to record calls on your iPhone in a pinch. Besides protecting yourself from nefarious intent, recording important conversations like verbal contracts and agreements can help you cover all your bases and ensure you're insulated from any potential liabilities that may appear down the road.

While there are a variety of privacy-focused search engines available like StartPage and DuckDuckGo, nothing can offer the complete trust offered by creating one's own search engine. For complete trust and security, Searx can be used as free metasearch engine which can be hosted locally and index results from over 70 different search engines.

Every industry has its own jargon, acronyms, initializations, and terminology that serve as shorthand to make communication more efficient among veteran members of that particular space. But while handy for insiders, those same terms can often create a learning curve for novices entering a particular field. The same holds true for the augmented reality (also known as "AR") business.

You may have seen news reports over the last two days detailing a major security flaw in virtually all smartphones. The devices that are at risk are not limited to either iPhone or Android — all of us are affected. If you want to make sure your smartphone and its data stay secure, there are a few steps you can take.