Hello people again, I wrote my last post about crypto about 10 months ago, now I will introduce something not fresh for the science, but fresh for the people who wants to learn. In my http://null-byte.wonderhowto.com/forum/cryptography-0161538/ post of crypto concepts, there is just basics, today we will see something that targets wide concepts like Symmetric crypto, Public Key Cryptography, Hashing, Keys etc...

It's a well-known fact (supported by myriad sources, including Fitness Magazine) that in order to lose a pound, you need to cut and/or burn 3,500 calories... which, divided by the number of days in the week, equals 500 calories a day.
Hello fellow Nullbytiens, I'm Washu, a long time commenter but first time poster. Today we'll be making an IRC bot, if you haven't seen OTW's post about the new IRC channel I would encourage you to go check it out. He does a good job at explaining what IRC is and how to get set up.
It's been a while, since I have just started High School. I have put a hiatus to my pentesting for a few weeks, and now, I am making a return. I have taken time to read about code, (even did a research article analysis on how humans can write "beautiful" code and something like that) and pentesting, but never made a full return. I will be occasionally coming back for a while.

My bathroom is like my own private arcade room. Whenever I'm seated comfortably on the toilet, no one is going to disturb me, so I can play anything I want on my smartphone. You probably do it, too — and your parents, kids, friends, colleagues, and boss — so don't be afraid to admit it.

Flowers may be beautiful, but they're not usually appetizing. Sure, nasturtiums are hip in fancy restaurants, but they're primarily used as a garnish. Granted, fried squash blossoms are incredible, but the point remains: flowers are usually reserved for looking at, not masticating.

Welcome back, my hacker novitiates! In the previous two posts in this series, we looked at the basics of buffer overflows. In this post, we will look at one technique for finding buffer overflows. We will try to send random, oversized, and invalid data at a variable to see whether we can make it crash or overflow. This process is known as fuzzing. It is often the first step to developing an exploit, as we need to find some variable that is susceptible to overflowing.

Welcome back, my aspiring hackers! In many of my earlier tutorials, I mentioned the complementary nature of hacking and forensics. Both disciplines, hacking and forensics, benefit from a knowledge of the other. In many cases, both disciplines will use the same tool. In this tutorial, we will use another tool that can be used in either discipline—Sysinternals—a suite of tools developed by Mark Russinovich.

My reliance on autocorrect has made me a horrible speller. I take it for granted that it'll catch all my mistakes, but it only ends up making matters worse (especially when it inadvertently makes correct words wrong). So instead of relying on autocorrect to fix typos, why not try to completely prevent mistakes from happening in the first place?

Welcome back, my hacker novitiates!

Hi everyone! In the previous part of this series, I introduced one way to hijack a program's execution flaw, though I only showed you how to crash the program and left you with a little mystery to solve. Today we are giving the solution of that and then introducing shellcode usage and remote command execution.

Hi everyone! Last time we finished analyzing the assembly representation of our vulnerable piece of code (have I ever told you it is vulnerable?). This time we are going to introduce some fundaments about exploitation by demonstrating how to crash a program's execution. If that sounds lame, next time we will see how this crash can in fact be useful to control the program's execution, achieving remote code execution!

When you have a parent who cooks—and has you act as sous chef—the kitchen automatically becomes a less intimidating place. In other words, kids who know their way around the kitchen will most likely become adults who cook for themselves, which also means that they'll eat more unprocessed whole foods, save money, and maintain a healthy weight.

After utilizing Spotify's My Year in Music tool, I came to realize that I listened to over 30,000 minutes of music in 2014. Most of that was played while working from my Mac using the desktop version of the service.

The importance of body language is stressed from an early age: watch those around you, and you'll know what they're thinking. While you might be skilled at deciphering the messages of crossed arms, slouched sitting, eye movements, and hand gestures, the key to understanding those around you is a little less obvious.

Welcome back, my greenhorn hackers! Before we attempt to exploit any target, it is wise to do proper reconnaissance. Without doing reconnaissance, you will likely be wasting your time and energy as well as risking your freedom. In previous guides, I have demonstrated multiple ways to perform reconnaissance including passive recon with Netcraft, active recon with Nmap or hping3, recon by exploiting DNS or SNMP, and many others.

This is the first installment in a new series that I am calling "Hacker Hurdles." These are things, methods, techniques that make our job as hackers more challenging and difficult. Don't misunderstand me, these items don't make our task impossible, but rather more challenging and, therefore, more gratifying when we are successful. One of the most important new hurdles for hackers is DEP and ASLR. Data Execution Prevention (DEP) and Address Space Layout Randomization (ASLR) are designed to pre...

Though many students spend four years of high school learning a foreign language, most of us probably retained very little. Chalk it up to the carelessness of youth, but chances are you've since been in situations or places that left you wishing you paid more attention in class or had continued practicing long after you graduated.

Welcome back, my budding hackers! People often ask me, "Why are you training hackers? Isn't that illegal?" Although I usually give them a short version of this post, there are MANY reasons why YOU should be studying hacking.

Last year, The New York Times wrote that certain restaurants in Manhattan and Brooklyn banned patrons from taking photos of their meals. That means no flash photography, no standing on chairs for a better angle, not even a quick pic for your Instagram followers before the first bite. Little do these restaurants know, this ban can actually make their customers' food taste worse, so to speak.

True story: a friend of mine regularly started a fight with her boyfriend everyday at 4 p.m. Every day. This went on for years until he finally got the bright idea of shoving a granola bar at her the minute she came home from work. Shazam! The fights were a thing of the past.

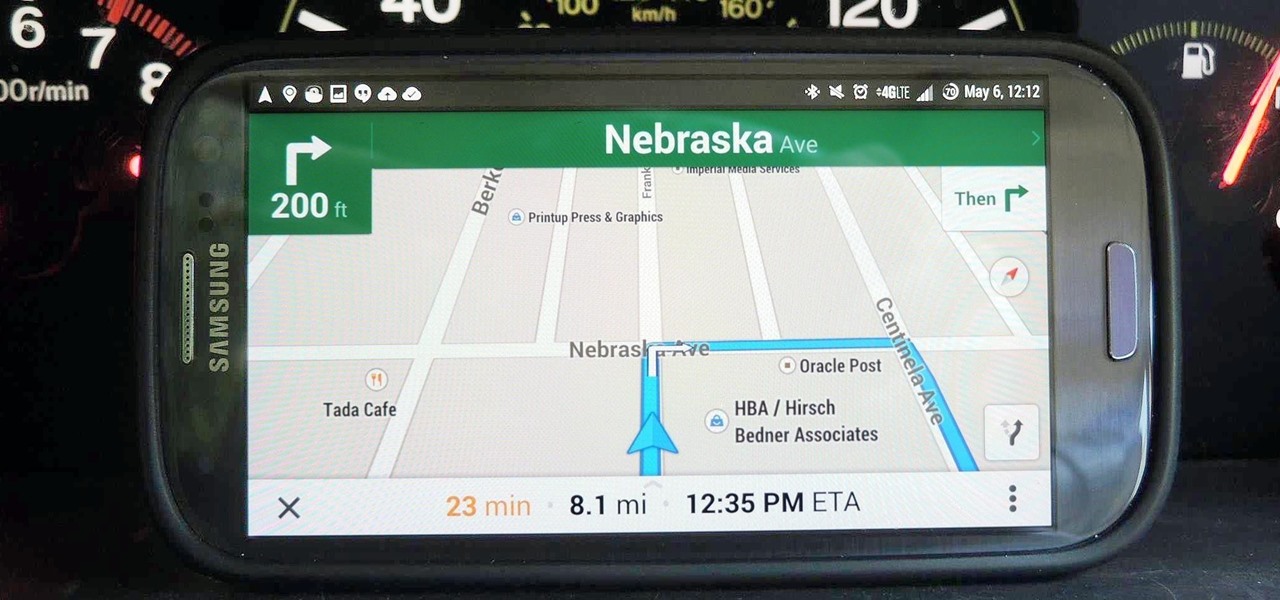
This week, Google sidestepped their usual "Update Wednesday" strategy by dropping a huge update to their Maps app for both Android and iOS. We're accustomed to seeing new features and bug fixes to their stable of apps on Wednesdays, but today's Maps update was presumably big enough to get its own release day (it's Tuesday, folks).

The Galaxy S5 is a flagship-level device with some pretty advanced features, like its 4K video recording capability, water-resistant casing, fingerprint sensor, and KitKat running out of the gate.

Wondering how to get long hair naturally? How do you grow your hair? In this video Rachelle and Sam give you 10 tips to get those long locks naturally!

What can't coconut oil do? This edible oil, extracted from the copra or meat of a coconut, has done what most other food, beauty, and health trends have not: demonstrated real lasting power. Indeed, the "superfood" continues to make headlines, with its many uses the subject of debate, study, and fervent support. From the obvious (cooking) to the less so (home improvement), there are likely many coconut oil uses you're not yet aware of.

The final chapter of Christopher Nolan's Batman trilogy is here, The Dark Knight Rises, and if you're anything like me, it made you want to immediately don a cowl of your own and run around punching criminals. Don't forget though, one of the most awesome aspects of Batman is his never-ending supply of crazy gadgets. Unfortunately for most of us, we don't have a billion dollars, nor Morgan Freeman, so we'll just have to make do with some good old-fashioned DIY tricks. Read on for a rundown of ...

If you read my article on the OSI model, you got a good overview on communications from that model's perspective, but how does that relate to TCP/IP? We're going to take it a step further, getting into the idea behind the two address concept. How does an IP address and a MAC address work together? If you want to hijack sessions and all sorts of lulz like that, you need to understand these concepts. Let's get into it, mates!

DarkStar One: Broken Alliance is an updated version of the space flight simulation video game DarkStar One (2006), and was made exclusively for the Xbox 360. It features updated graphics and presentation, making it the perfect space flight game for you wannabe astronauts.

With a little bit of planning, you can avoid a lot of blood-pressure-raising traffic messes. You Will Need

Tick bites should be treated immediately, the concern being transmission of Lyme disease. If you've received a tick bite, what you should do is to remove the tick promptly and carefully. Use tweezers to grasp the body of the tick near its head and pull out very gently to remove the tick whole without crushing it. Learn more about tick bites and how to treat them in this medical how-to video.

If you want to improve your violin bowing technique then this tutorial is for you. This violin lesson teaches you a great exercise to improve your spiccato bowing technique. This exercise , based on the Yost system, is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this exercise you should re...

Do you want to improve your violin playing technique? This violin lesson teaches you a great exercise to improve your octave technique. This exercise is based on the Yost system. This exercise is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this exercise you should relax your fingers, hand ...

Do you want to improve your violin playing technique? This violin lesson teaches you a great exercise to improve your tenths technique. This exercise is based on the Yost system. This exercise is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this tenths exercise you should relax your fingers...

Do you want to improve your violin playing technique? This violin lesson teaches you a exercise in broken octaves in first and third position. This exercise is based on the Yost system. This exercise is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this exercise you should relax your fingers...

Do you want to improve your violin playing technique? This violin lesson teaches you a great exercise to improve your octave technique in first and third position. This exercise is based on the Yost system. This exercise is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this exercise you shou...

Do you want to improve your violin playing technique? This violin lesson teaches you a great exercise to improve your octave technique in thirds in first and third position. This exercise is based on the Yost system. This exercise is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this exercis...

Do you want to improve your violin playing technique? This violin lesson teaches you a great exercise to play your octaves in broken thirds, seconds, and fourths. This exercise is based on the Yost system. This exercise is designed to increase your familiarity and comfort in all positions, develop confidence and accuracy in all positions, develop an understanding of what to listen for while shifting, and improve your ear training and overall intonation. When practicing this exercise you shoul...

Learn all about functional training and resistance exercises with expert advice and demonstrations in this free fitness video series on functional training with the kinesis system.

See advanced Aikido techniques to help you learn Aikido in this free martial arts training video series.

Learn advanced Aikido techniques and principle of motion in these free Aikido training videos featuring a 4th degree black belt.