
How To: Set Up a Normal Printer for Wireless Printing in Windows
Want to be able to print wirelessly without having to buy a pricey network printer? Now you can! All you need to do is follow these simple, quick, steps.


Want to be able to print wirelessly without having to buy a pricey network printer? Now you can! All you need to do is follow these simple, quick, steps.

Intro Everyone who has, or at one point in time owned an iPod or iPhone has used iTunes. And we all know the problems with iTunes. For example, sometimes it doesn't detect the device or thinks your iPod's just a camera, or there are bugs in the software.

Metal is a great material to work with. It's rigid, tough, malleable and conductive, but sometimes the part we need doesn't exist in any store. In order to create custom pieces, you need to either melt the metal and cast it in a mold, or heat it until it's soft enough to shape with your hammer. Properly melting metals can be a bit dangerous in our home shop, but we can make a coffee can forge for all of our home blacksmithing needs.

Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use your network as a spring board for who knows what. When the police come a few days after, they are coming to your door—and not to talk about how nice your lawn is. Don't be that guy.

TOP MOVIES 2011 The Artist (2011)
Are you a Minecraft cake fanatic, but have a hard time gathering enough eggs together to satisfy your addiction? Have you ever wondered if there was an easier solution to getting those "hard to get" chicken eggs? Well, today we will be going over a method of chicken egg farming.

For our final part of recognizing crowd control, we shall look at the mind. It's the most complicated thing in the universe, but also the most easily influenced. What makes us to gullible? What methods to commercials, companies and the media use to influence our position on things? These are just a few of the questions we will answer.

Okay, so what are we going to make our videos about? I’ve written before about creating articles, and what kind of content we are going to put in our articles. So what are we going to put into our videos? Let me give you a few ideas that I have. These are some things that I would do if I had a service business.

Social engineering is described as the clever manipulation of the natural tendency of human trust. All of the passwords, locks, and encryption in the entire world are useless against a good social engineer who can charm or trick you into giving it up.
In this series on weaponized lasers, I'll be exploring the function, operation, strength and building instructions for three basic laser weapons; CO2, Diode, and Flashlamp. These laser types are just a few of many, selected because of their simplicity and basic construction (depending on your experience).
Welcome to Microwave Energy—the next part of my Making Electromagnetic Weapons series. For the Electromagnetic Pulse Generator, check out the last three articles (One, Two and Three).
Does this video prove that otherworldly intelligent life has visited Earth? No. It does not prove anything other than there are designs ‘etched’ onto the surface of a field. Does the video immediately above prove that otherworldly intelligent life hasn’t visited Earth? Yeah, you saw it coming; no, it proves nothing more than humans are able to ‘etch’ designs in a field of grain.
Sergio Peralta Advisor: Jessica Davis

Yes, you read the title correctly. GameStop has problems, and if you're lax in morals, you can take advantage of them for free games and cash. I'm bringing you all yet another exclusive Null Byte that falls into the fascinating category of life hacking.

Minecraft mods (modifications) are additions to the game that change the way you play. They include texture packs, shaders, changes in gameplay, additions and subtractions and everything in between. Some of this information is very basic, other bits might help you along if you've been stuck. We'll start with the simple stuff.

Antimatter15, author of the popular Surplus Chrome extension, was suspended from Google+ for using a pseudonym instead of a name that fits Google's community standards. As such, he's no longer supporting the extension, and if you're using it, now might be a good time to find a replacement. It's a reminder that nothing on the web is guaranteed to work forever. Luckily, there's no shortage of innovative coders whipping up creative and useful Google Chrome extensions.

+Randall Munroe, the man behind the web's most popular web comic, XKCD, has always had a knack for getting to the heart of the larger social issues on the web. During the 1st 48 hours after Google+ started letting non-Googlers in, one of the most shared posts within its private walls was his latest comic about Google+:
I don't know what I'd do without my computer. I can't do my job without the internet. I communicate with employers, friends, and family through emails, video chat and Twitter. I schedule meetings and plan deadlines. I bank. I shop. I read the news. I play games. I watch my favorite shows. Yes, I'd be rather lost without this little plastic box of circuits.

The whole world seems better when you’ve had a full night’s sleep, and if you don’t believe me, you’re JUST FRIGGIN’ WRONG. Studies show that getting enough sleep during nighttime hours can make you less irritable, help you lose weight, and reduce your risk of cancer and other totally bogus-time diseases.

Keanu Reeves is a really good actor and I'm not even kidding Pity the fate of the blank-faced man or: Why you need to rewatch Bill & Ted's Excellent Adventure

On a Wednesday evening when friends are going to a movie or out to dinner, you’re at the dojo training.

I've been curious to watch one of these famed '3D' games for a while now. Last April at NAB, I attended several 3D panels and folks from ESPN suggested that one of the strongest experiences that would bring 3D into the home would be live sports. I've missed opportunities to watch the PGA Masters broacasts, and NCAA games, but being a hardcore Soccer (Futbol) fan, I've been most excited about this possibility. It did not disappoint, but not without some concessions. I will be as detailed as po...

If you're just starting out learning to drive, get the lowdown on some of the basic car controls with this video tutorial.

So, you're all excited you went ahead and 'upgraded' your iPhone 3G to IOS 4.0X so you could reap all the benefits of all the new features.

This movie shows how to enable the visualizer feature in iTunes, focusing on PCs. All you have to do is open iTunes and press the control and T keys. Use the iTunes visualizer.

In this particleIllusion video tutorial you will learn how to render AVI and sequential PNG files. Learn to export the files with enabled Alpha Channel. This allows output of PNG files with transparency Export footage as AVI/PNG sequence in particleIllusion.

One of the things you've likely gotten used to if you have a rooted Android phone is not installing OTA system updates in a typical fashion. Depending on your version of Android, you might not actually be able to swipe away that nagging update notification at all. Thankfully, there's a way to prevent your system from automatically checking for OTA updates.
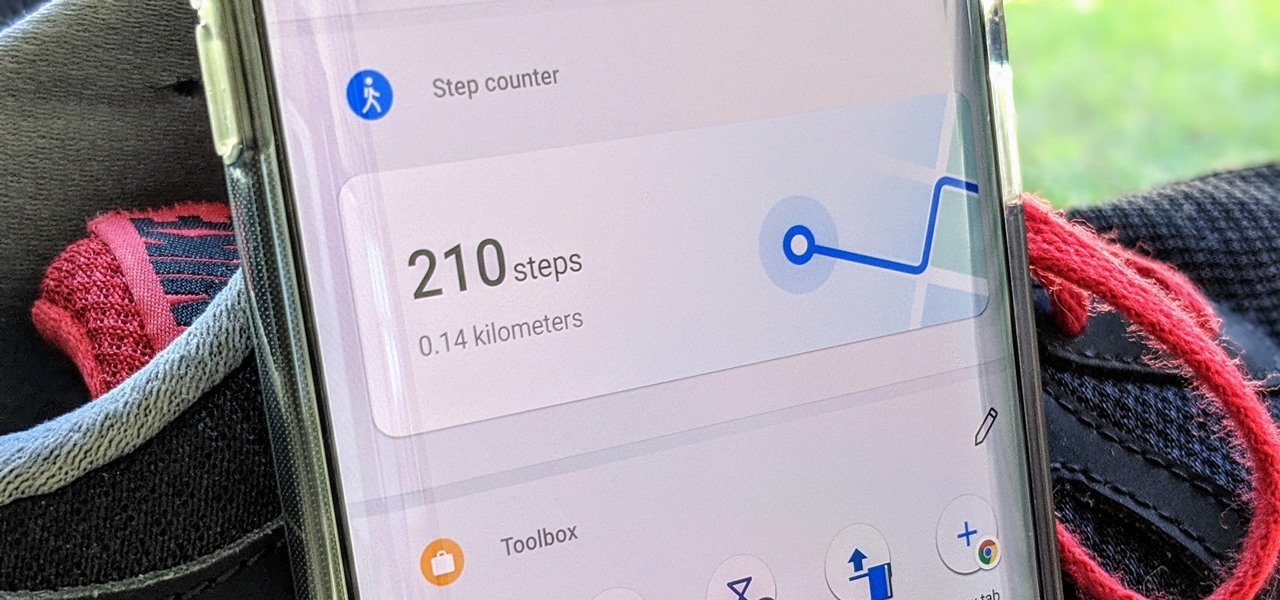
A great way to incorporate a healthy exercise routine is by taking lots of steps throughout the day. While most smartphones can track and report your steps via a third-party app, you can check them right from your home screen if you have a OnePlus phone.

Looks like Minecraft is getting some cool new features, including editable books and colorful wooden half slabs. Check out the video below to see the newest Minecraft Snapshot 12w17a in action. Warning: This release is for experienced users only! It may corrupt your world or mess up things badly otherwise. Only download and use this if you know what to do with a minecraft.jar file!

How many people use the big search engines here? I'm going to estimate 90% of everyone on WonderHowto uses one of the following on a regular basis: Google, Bing or Yahoo! Search. The question is: are you in that 10%? You should seriously consider dumping Google search for DuckDuckGo. Why? DuckDuckGo does not track you.

Being able to spell a seven-letter word on the board is one of the most enjoyable things about playing Scrabble. It's even better when those seven letters are all from your rack, giving you a bingo—those 50 bonus points in addition to your regular score.

With the plethora of programming that we promote at Null Byte, I figured a lot of you newbies that stop by IRC will need a big boost in the right direction to make your dive into programming a lot easier. A hot question that has been thrown around in IRC a lot when making the initial dive is, "How do I write code?". People who do not know much about computers can't understand how code is written. Code that we write here is usually scripted and written in Python, so we will use it as our examp...

Google announced a lot of great feature updates this week! Most of them are content-related, and help you more easily find out what's going on in the overall Google+ community.

In Linux, all password hashes are normally stored using the MD5 hashing algorithm in the /etc/shadow file, but MD5 is algorithmically weak due to collision vulnerabilities. The new recommended standard are the higher level SHA-2 hashing algorithms, SHA256 or SHA512. As a friend pointed out to me, Ubuntu is currently the only distro implementing SHA-2 as the default. With SHA-2, your passwords take an unreasonably larger amount of time to calculate. This will greatly decrease how many password...

Since its inception, Google+ users have been a loud, vocal bunch, and they've made their displeasure known about many issues, especially on the lack of support for pseudonyms, Google Apps, and brand pages. It's been especially galling for many Google loyalists, who found their Google+ profiles suspended, when they ended up violating the Google+ "common name" policy.

Formerly ipchains, iptables is a script-based firewall that's included with both Mac and Linux operating systems. In my opinion, it's the best firewall in existence. The only downfall is that it's complicated for some people to use due to its script-based nature. But this should be disregarded, as firewalls are nearly the entire security of your computer.

One of the main reasons I was held back from fully switching over to Linux was the fact that media streaming is nearly impossible. You have two choices in Windows: either you use file sharing with Windows Media Player, or you can just use the Windows Media Center. But both of these softwares are not for Linux or Mac. Microsoft doesn't like to make open source software because they believe in making a profit, instead of allowing others to innovate it.

Sharing a laptop's wireless Internet connection with other computers connected to its Ethernet port is a great skill to know. It can be good for a number of reasons; Your computer may not have proper hardware to have a standard setup, or you may have an awkward network topology where sharing your wireless Internet via Ethernet would just be a better option.

The dreaded moment you hope never happens—someone has stolen your laptop. You could have private information, pictures, or even private information belonging to the company you work for, all lost forever. It can cause you pain, money, or even a job.

This week, we saw the implementation of collapsed comments, Google+ games were rolled out to everyone, and yesterday, there were several more announcements of enhanced features and tweaks.