Despite their awkward appearance, Apple's AirPods have become the earbuds of choice for working out, largely thanks to quality audio without any wires to tangle. However, at $159 to start, they aren't exactly for everyone.

Let's face it, most of us do most of our shopping on Amazon these days. So why should Black Friday shopping be any different? The online retail giant always cooks up some great deals on high-demand items, like headphones. If you're looking to save some dollars on a new pair of Beats, Skullcandy, or Bose, you're going to want to check out Amazon.

Black Friday is upon us. Whether you prefer to duke it out in stores or calmly shop online, there's no doubt you'll find great deals on the items you're looking for this holiday season. It's the perfect time of year to buy something expensive, like a good pair of AirPods, Beats, or Bose, at a much more opportune price.

If you're looking to save big on Apple AirPods, Beats, Bose, and other major headphones brands this Black Friday, look no further than Walmart. The store is hosting a number of sales on Black Friday itself, but you don't need to wait until Thanksgiving night to take advantage of the savings.
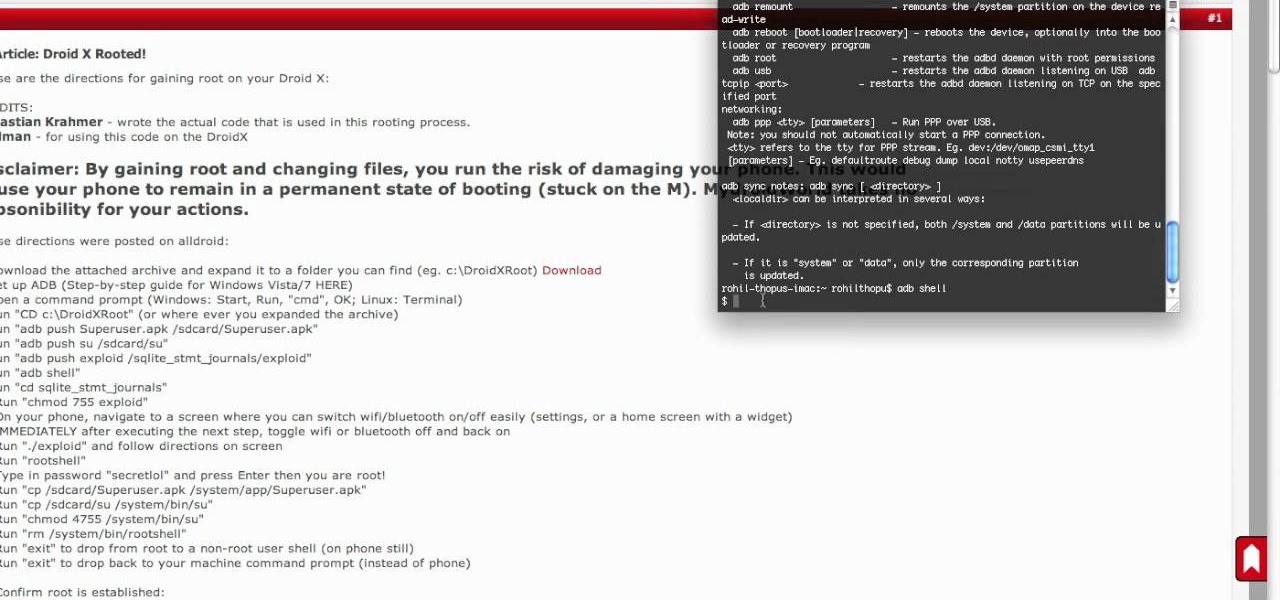
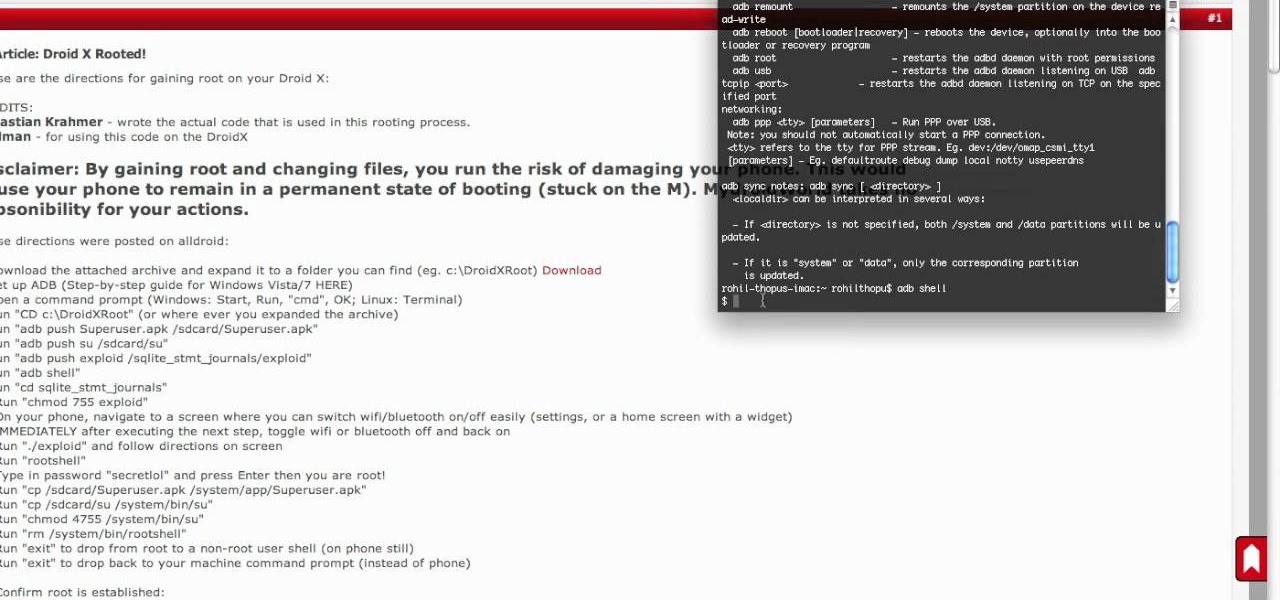
It seemed like an impossible task. No one could figure it out. Only God himself knew the answer. But the impossible has become possibly after only a week of trying. The Droid X has been rooted.

The holiday season is upon us, and that means all the big-box stores are competing against each other to offer the best prices on electronics. What was once a 24-hour period of flash deals the day after Thanksgiving has now become a holiday in and of itself — Black Friday is an event you don't want to miss.

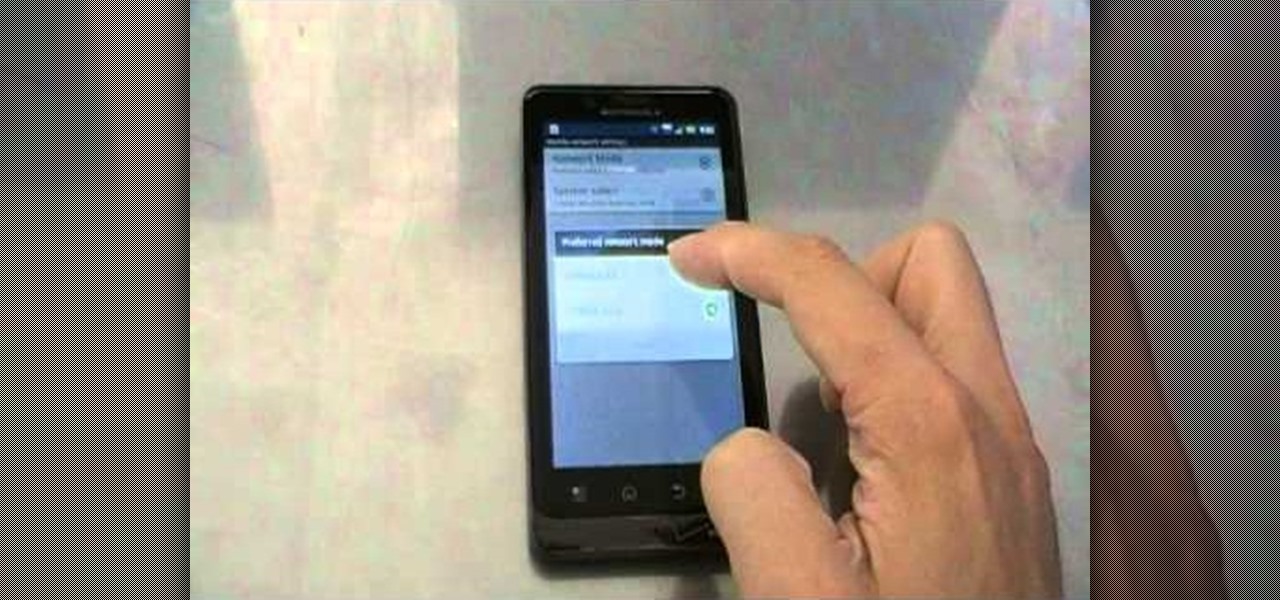
Verizon Wireless's most recent Android smartphone, the Motorola Droid Bionic, is having quite a few problems with activation. If you need support activating your Droid Bionic, take a look at this walkthrough for a quick little work around for the activation problem.

Want to mod your HTC HD2 Microsoft Windows smartphone to use wireless charging—without breaking your warantee in the process? It can be done! And quite easily at that. For complete details, and to get started modding your own HD2 phone to work with wireless chargers, watch this handy hacker's how-to.

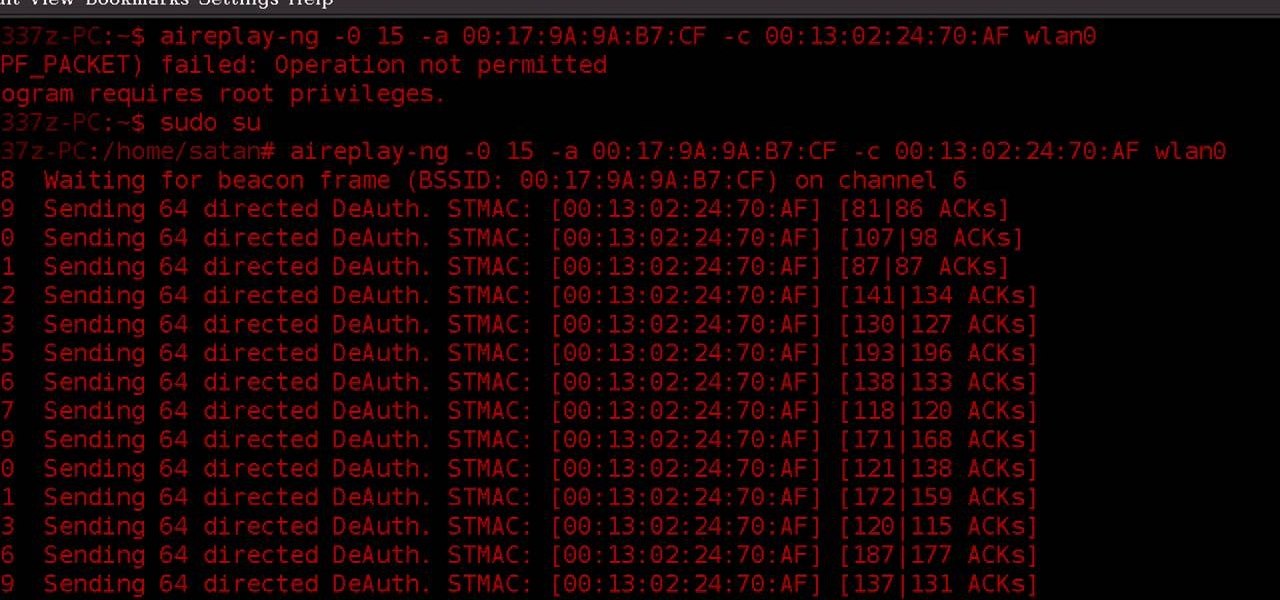
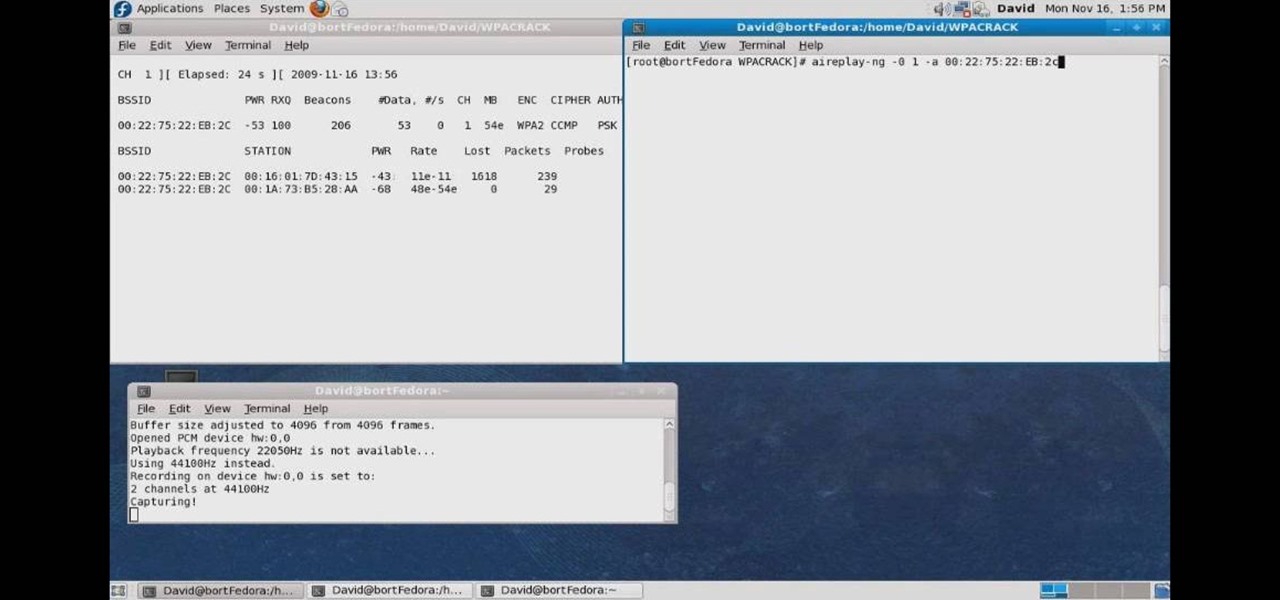
WPA-secured wireless networks, or WiFI Protected Access, is a form of internet security that secures your wireless LAN from being accessed by unauthorized users. Safer than WEP, or wireless equivalent privacy, WPA still has weaknesses that are prone to cracking - IF, that is, you know what you're doing.

Wrestling with the whys are wherefores of WiFi? Can't figure out how to secure your network? Take heart: This remarkably thorough, seven-part home networking tutorial will get you up and running faster than you can say `Wireless G.'

Anyone can set up their own wireless network. All you need is a little know-how. You will need a computer with wireless capability, a high-speed modem, a wireless router, and a broadband internet connection. Don't get tied to the wall; a wireless connection will allow you to move the computer freely around your home and still get an internet connection. Watch this video tutorial and learn how to hook up a wireless network at home.

With Verizon Wireless's Android phone numbers growing rapidly (e.g. Droid X, Droid Incredible, Motorola Droid), one of the of the favorites remains to be the HTC Droid Eris. If you have one of these mobile devices, Verizon Wireless would like to show you a little more about it. This video gives an overview of the features and the basics on how to use it.

Check out this film and theater video tutorial on how to set up a wireless microphone for sound recording.

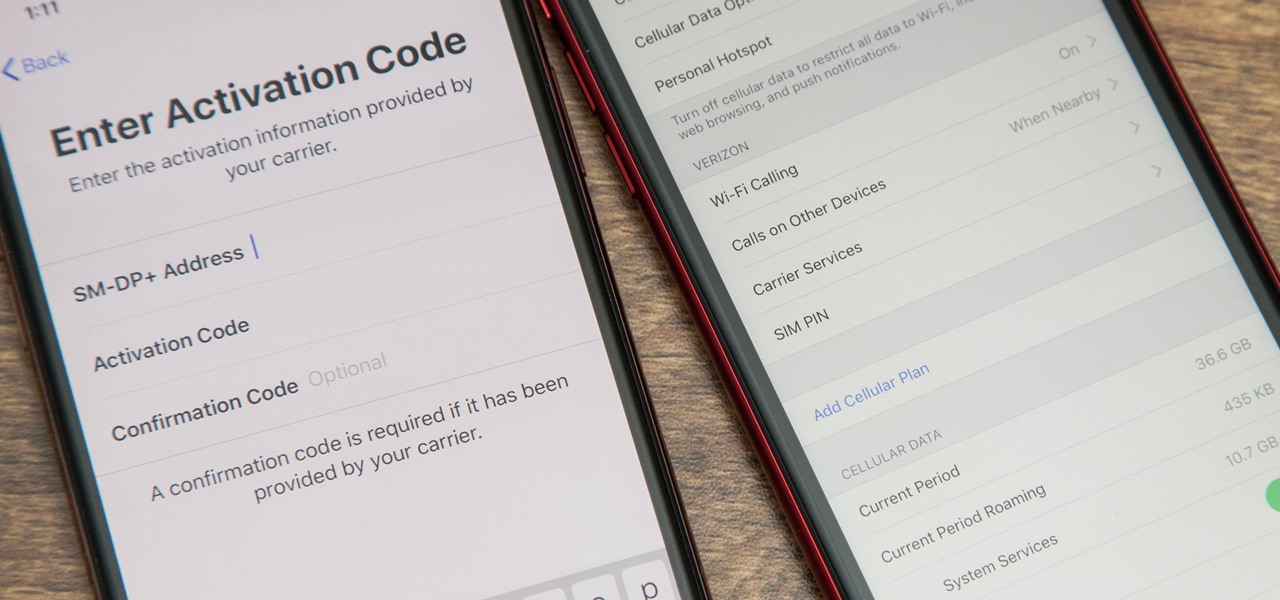
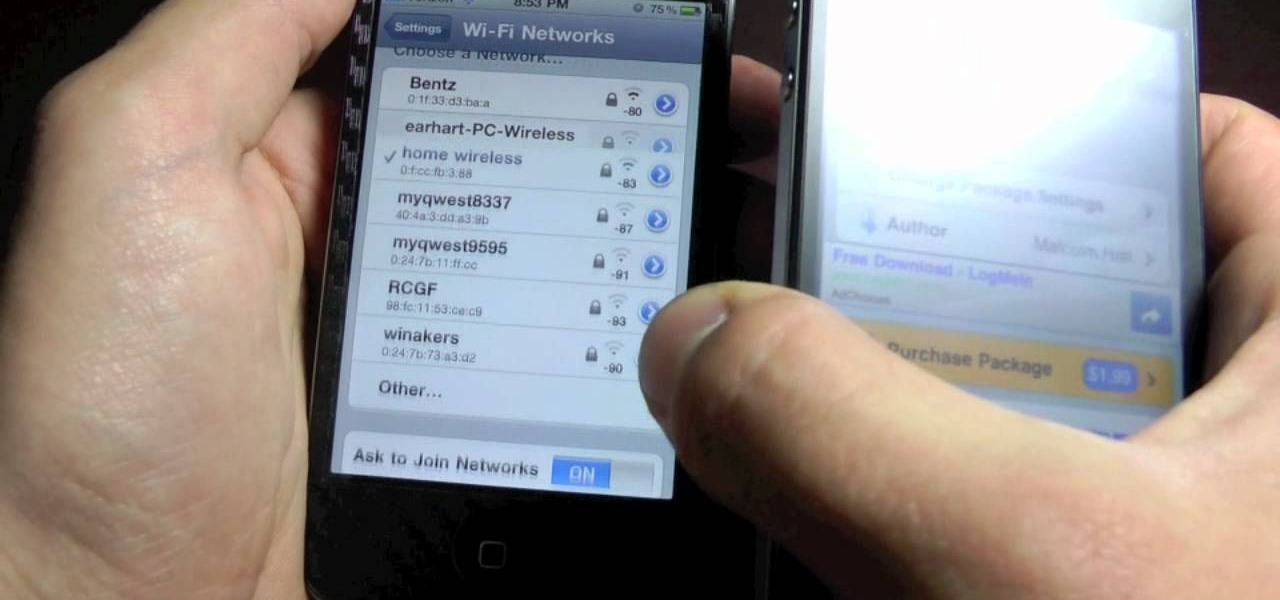
With an iPhone that includes a digital eSIM option aside its standard Nano-SIM card, you can have two cellular service accounts. One can be your primary line with your main wireless carrier, and the other can be from your main carrier or another provider. The eSIM account can be prepaid or postpaid as well as data-only, which is great for traveling. But which wireless providers support eSIM?

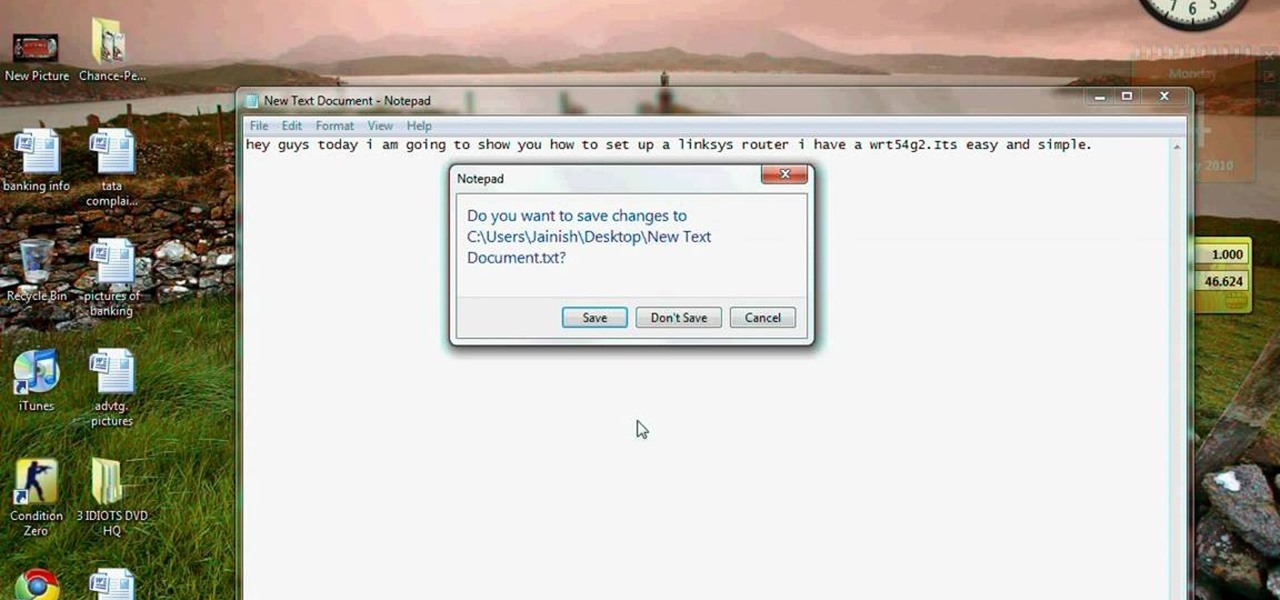
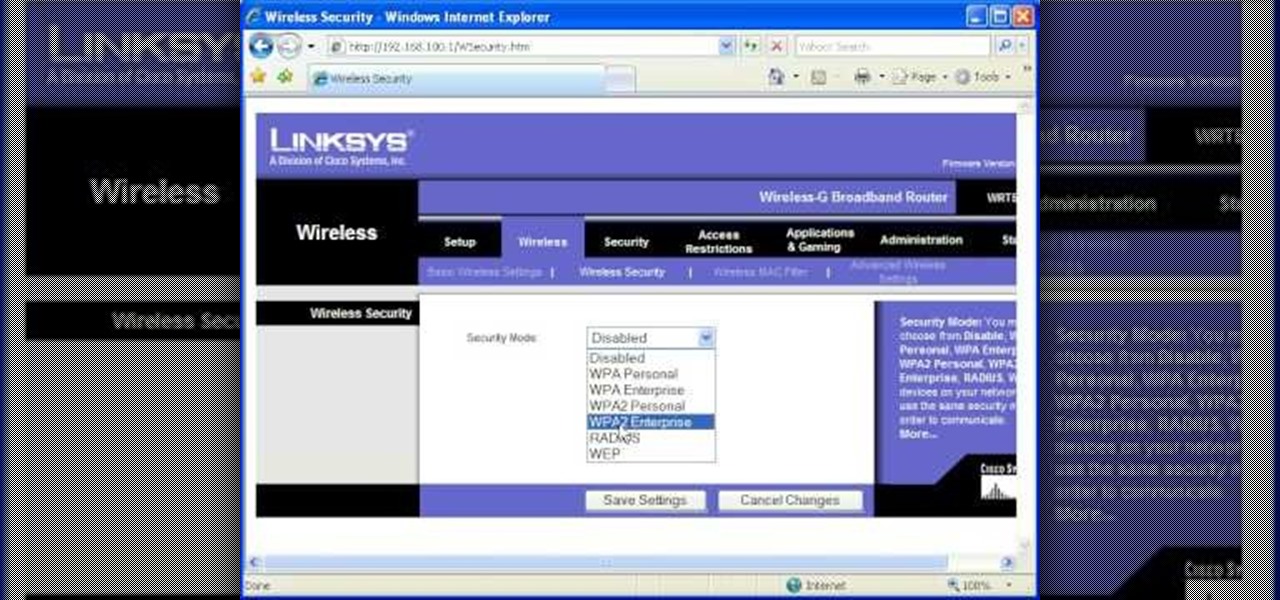
This video tutorial is in the Computers & Programming category which will show you how to set up a Linksys WR54g or WRT54g2 wireless router. First you connect to your Linksys router. Then go to http://192.168.1.1 and type in "admin' as your password in to log in window and click "log in'. then go to the "wireless' tab and enter your wireless network name. In the wireless channel select '11 2.462GHz' and click save. Next go to "wireless security' and type in the wireless network key. This is t...

Most of the home wireless networks are not set up by professionals and hence they might lack in security features. People just set up the wireless networks by connecting the devices and powering them up and never care to apply security settings to the network. This may result in your wireless network being compromised by unwanted external entities. How ever you can do a web based configuration settings and secure your wireless network by password protecting it. This settings differ from the m...

Video tutorial showing how to make your own solar-powered wireless security camera using an off-the-shelf solar panel and any wireless webcam. See creator site for more detailed graphics.

Check out this video tutorial on how to hack into WEP encrypted wireless networks. The aim of this video is to show people how easy it is to crack a wireless network with WEP encryption. Seriously, if you know how to do it, even a little kid could if you showed them how. Now that you know this, you should upgrade to WPA! It is much harder and takes much longer to crack.

Although the Motorola Droid isn't the newest Android cell phone from Verizon Wireless (e.g. Droid X, Droid Incredible), a lot of mobile phone users are reluctant to switch because of its reliability and QWERTY keyboard. If you're one of those users, but haven't quite fully realized the potential of your Motorola Droid, this video straight from Verizon Wireless will give the lowdown on all the features and uses.

Verizon Wireless's latest Android smartphone the Motorola Droid Bionic, has an 8 MP built-in camera that takes great pictures with the built in Camera app on the Android Gingerbread OS. This Motorola guide will walk you through the process of taking pictures, as well as sharing them to Facebook, Twitter, Picasa, or via text message.

The Droid Bionic was rooted the same day it came out with the one click method used to root the Droid 3. This tutorial will walk you through the process of rooting Motorola's Android device so that you can unlock the full potential of Verizon Wireless's flagship device.

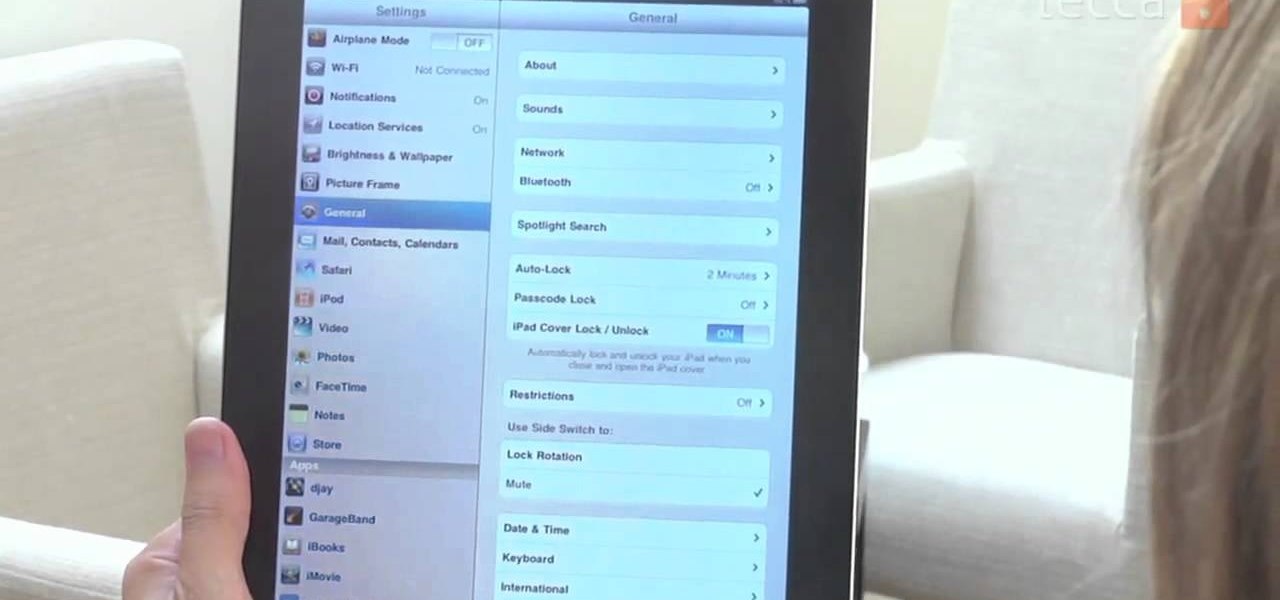
If you're trying to learn how to use Wi-Fi on your iPad, take a look at this tutorial on connecting your iPad to a wireless network so that you can access the internet. You'll need to use the settings and know the name of the wireless connection you want to use. Make sure you have the password handy, too!

If you want to connect your Mac notebook or desktop to a wireless network, you'll need to set up the wifi connection on your computer first. Take a look at this walkthrough to find out how to find and connect to available wireless networks in OS X. This is a great skill to know if you own an Apple laptop and need to connect to the Wi-Fi networks at different locations.

You can easily share and transport your photo and videos on the Canon EOS 7D by using the wireless file transmission option. See exactly how sharing and downloading your files to computers and other devices works in this video. When the digital SLR camera is combined with the WFT-E5A Wireless File Transmitter, transmitting is easy.

This is a video tutorial on how to cancel your Verizon contract without having to pay an early termination fee (ETF).

The Lab Rats, Andy Walker and Sean Carruthers, explain Media Access Control (MAC) addresses. Filtering MAC addresses allow you to very specifically control access to your wireless network.

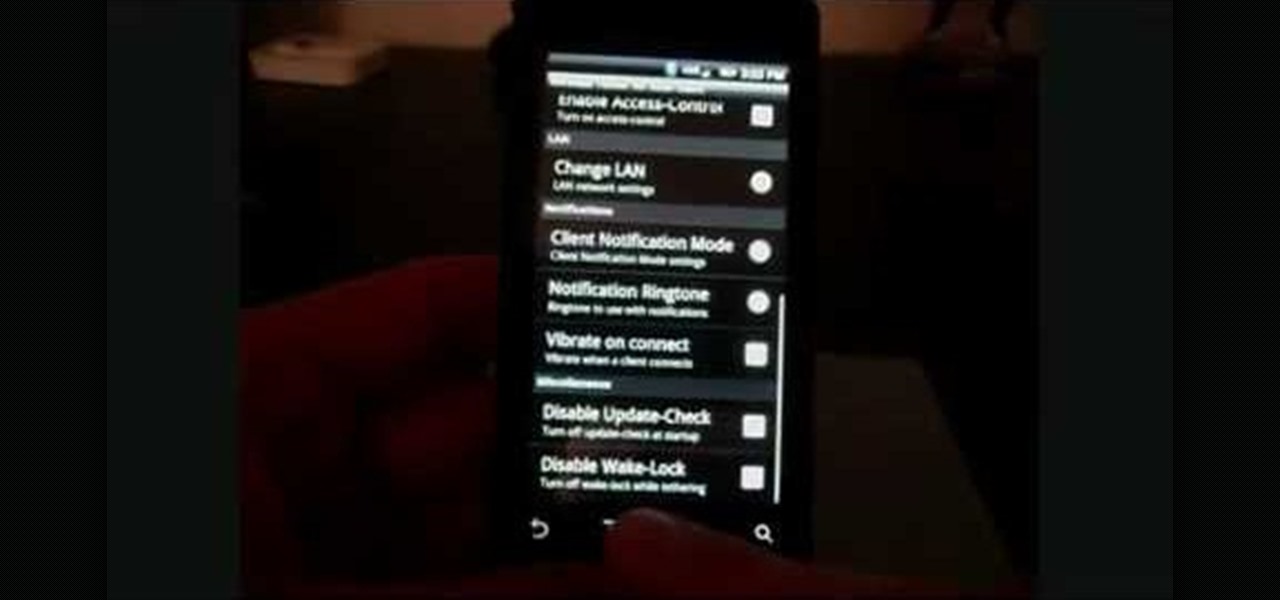
In this clip, learn how to tether your rooted Droid to a WiFi network and use it as a modem for your other Wireless devices. This process is pretty easy and only requires a network and that your phone be rooted.

In this tutorial, we learn how to set up and secure a wireless router. First, take your cable and plug it into your modem from your computer. After this, plug in an Ethernet cable into your modem to a wireless router. Now, plug the wireless router and modem into the wall. Now, look for the icon on your computer that says you have connected a new device to it. Go through the set up wizard to make a new wireless network, once it doesn't find one, connect a USB to the computer. Now, click on the...

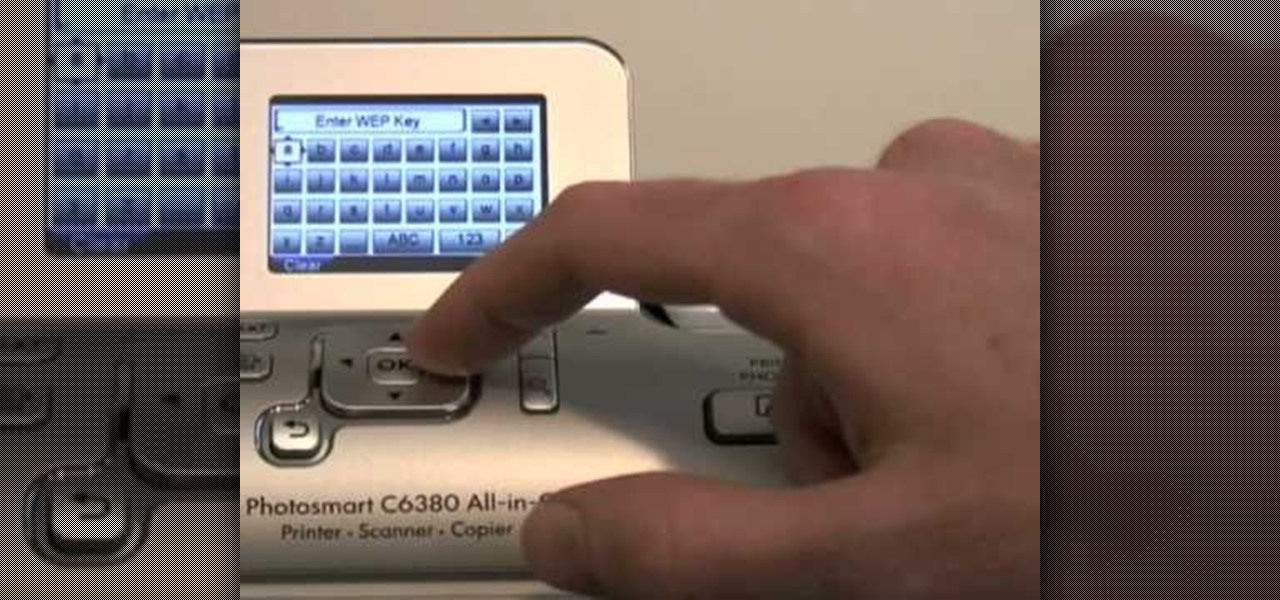
In this tutorial, we learn how to set up an HP wireless printer. First, click "setup" on the printer, then go to "network", then "wireless setup wizard". The printer will now go through the setup process and show you available wireless networks in your area. If your network requires a password, enter it by typing it in with the keypad. Now, install the software to any computer and wait for the blue wireless light to turn on. When this is done, you will be able to print wirelessly from any com...

In this how to video, you will learn how to crack a WPA encrypted wireless network. To do this, you will need the Air Crack package for Linux. First, disable the wireless adapter and enable monitor mode. Next, identify the channel in the wireless network and Mac address. Once you have this, you can listen to the traffic coming to and from this point. Wait for the handshake or disconnect something in order to force it to reconnect. From here, you are ready to perform the attack. With any encry...

See how to make an X10 wireless security camera into a nice helmet cam on the cheap in this three-part video. All it takes is an X10 camera, ten bucks in parts, and two hours of your time.

If you're planning on picking up a new iPhone X, 8, or 8 Plus, or maybe a Samsung Galaxy S8, S8+, or Note 8, you'll want to consider a wireless charger. While you might feel a bit fancy charging your smartphone without a cable, that pomp might come at a price. Thankfully, Black Friday is almost upon us, and we know all about the best deals.

Check out this video if you are interested in learning about improving your jailbroken iPhone's wireless signal reception. This video explains Wifi booster, an app available in Cydia, which removes Apple's barrier against weak wireless signals, giving you more range.

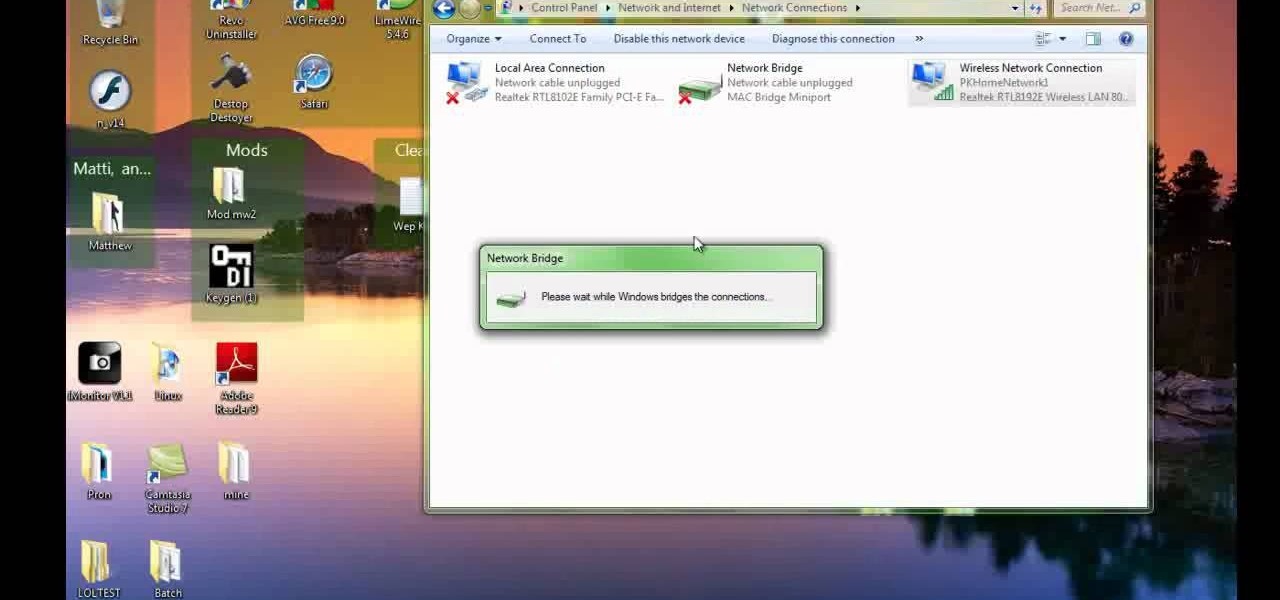
Check out this video to learn how to set up your computer as a wireless router for your Xbox 360. This video contains instructions for creating a bridge so that your laptop can act as a wireless adapter for your Xbox 360.

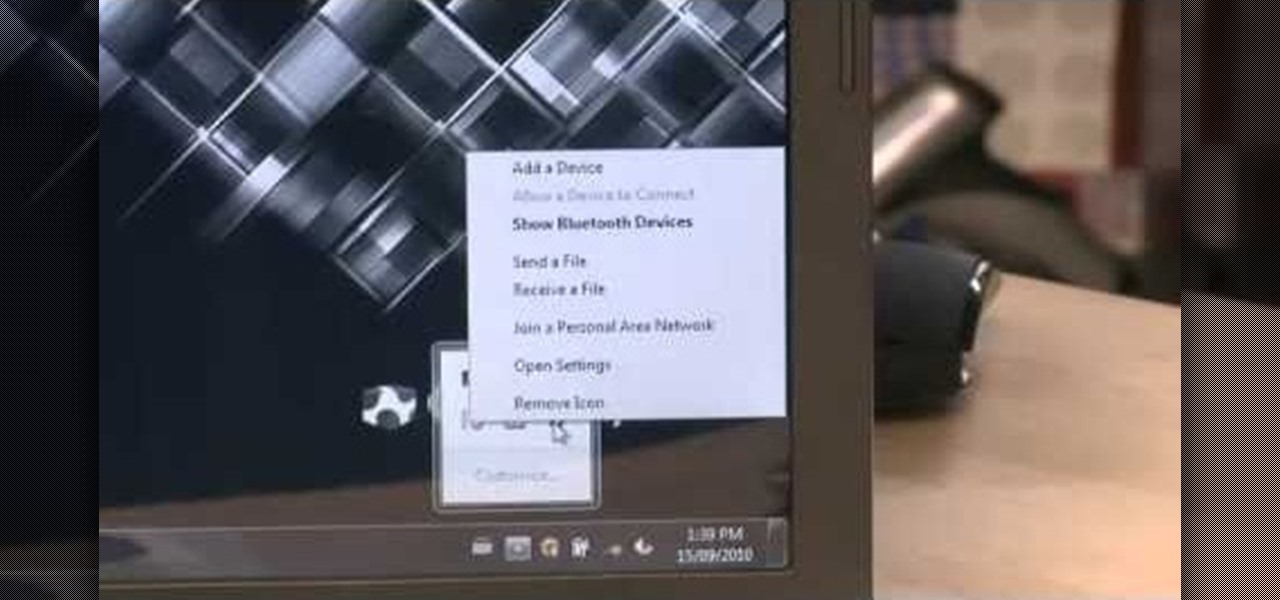
In this clip, you'll learn how to go about pairing a Bluetooth-enabled wireless keyboard or mouse to a Microsoft Windows (Vista, XP, 7) PC. For more information, including a complete demonstration, and to get started setting up your own wireless peripherals, take a look.

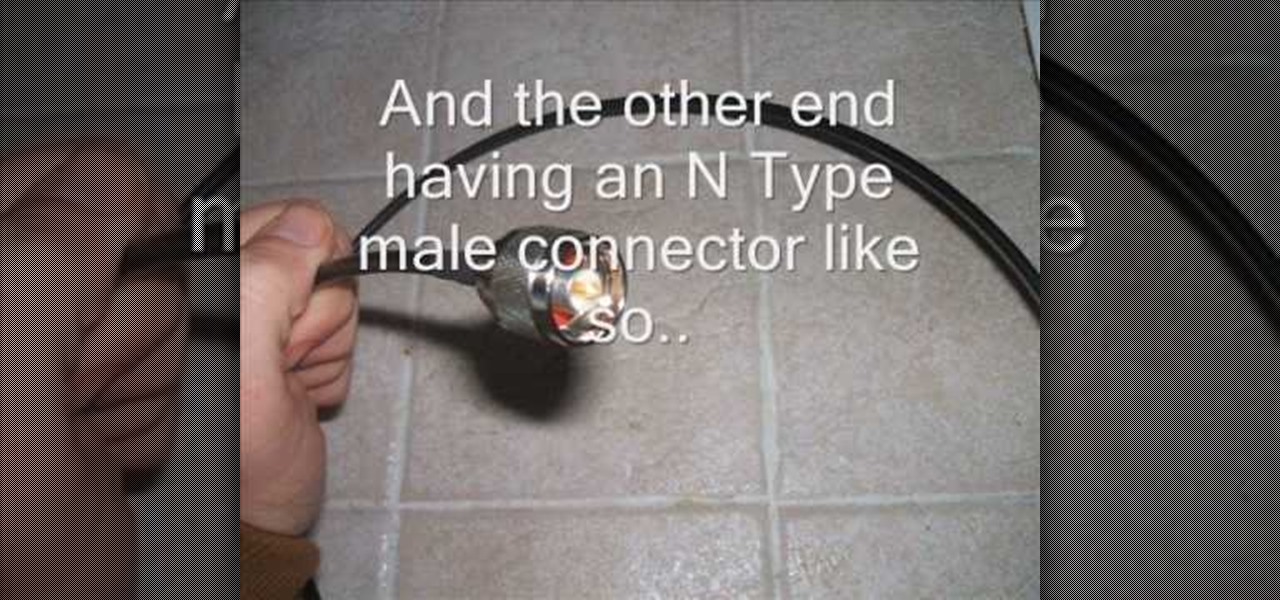
The cantenna has become something of a cult figure in the world of online signal enhancement. Making your own wireless-internet-boosting antenna out of a tin / aluminum can and a small wireless antenna can improve your internet life a lot, and this video will show you how to make one.

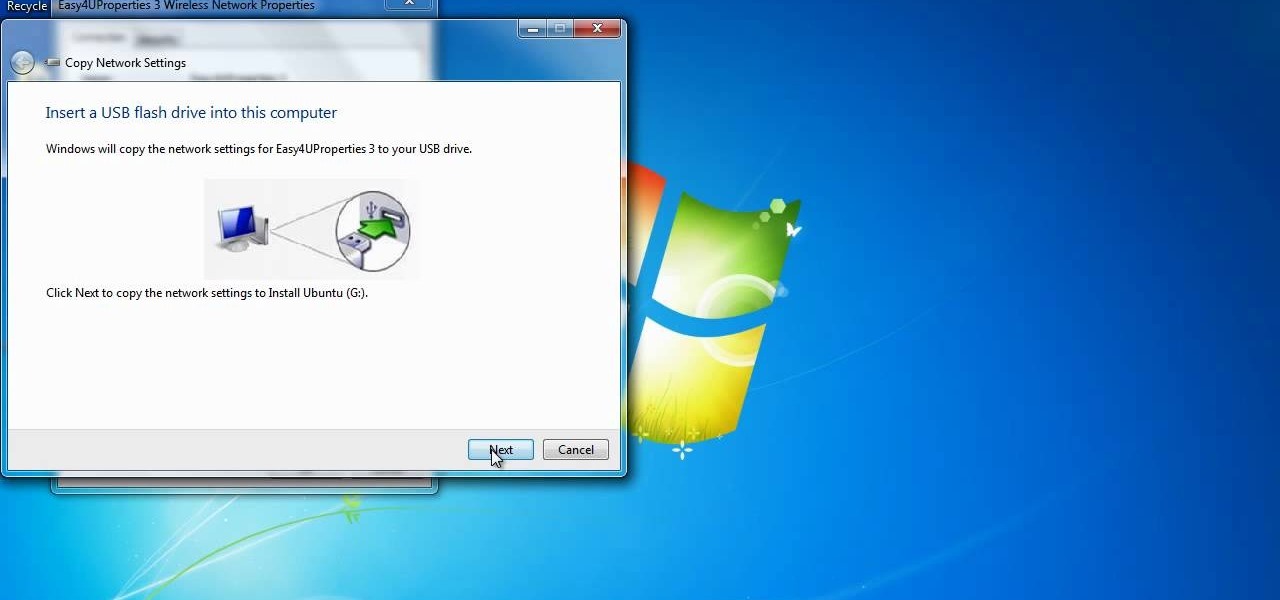
Interested in exporting wireless profiles from a PC running MS Windows 7? Well, you're in luck, as this guide will show you how to do just that. For details, including complete step-by-step instructions, and to get started exporting your own wireless profiles, watch this helpful home-computing how-to.

One of the best tools for audio systems is a wireless microphone. This video will give you tips on how to use a wireless microphone if you're shooting on the move, or if you're a one man band type producer.

This is a tutorial of how to take advantage of wireless printing, set up a backup system, and set up wireless speakers to listen to music from anywhere in your house.

In this movie is going to teach you how to increase your wireless signal strength with a soda can. Cut the aluminum can in half to create a parabolic shape. Then fit the can around the WiFi antenna to help boost the signal's strength and direct it towards your wireless computers or laptops.