No website, service, or platform is immune to being abused or exploited by hackers, and Google Analytics is no exception. To better understand how Google Analytics can help deliver payloads and bypass security protocols, one might want to learn how to use Google Analytics from a user's perspective first.
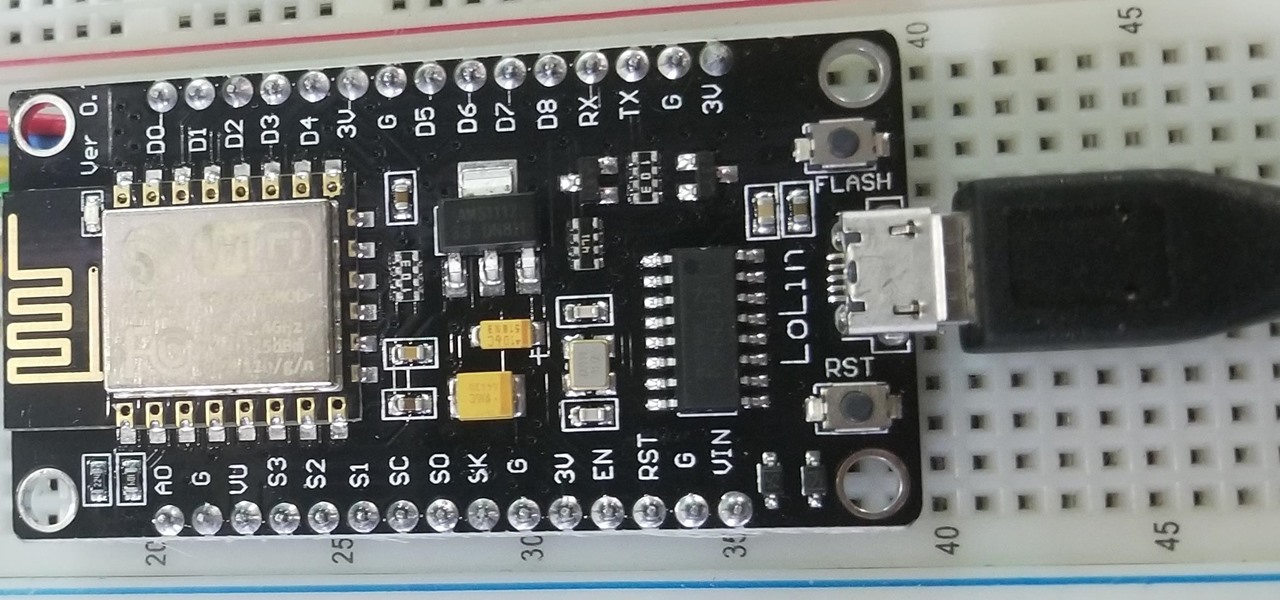
A macOS computer can reveal a lot of information about the owner, including which Wi-Fi network they have permission to access. With an Arduino-based attack, we'll use a five-dollar setup to inject a rogue Wi-Fi network and steal the list of trusted Wi-Fi networks, allowing us to see where the computer has been.

Amid the coronavirus chaos, two companies at the forefront of augmented reality technology took starkly different approaches to their upcoming developers conferences, as Facebook has canceled its annual F8 conference and Magic Leap plans to invite a limited number of attendees to its Florida headquarters for LEAP Developer Days.
Do price tags on mobile games give you pause? We get it. With so many freemium games out there, it's tough to justify spending three or four dollars on a game for your iPhone or Android device. That's why you wait for moments like this one, as both "Reigns" and "Reigns: Her Majesty" are aggressively on sale.

The Shadow Brokers, a hacker group known for its dump of NSA hacking tools in 2016, has just leaked their remaining set of data which implies that the NSA compromised SWIFT, the global provider of secure financial services, to spy on banks in the Middle East.

Nintendo's first ever game for Android has finally touched down (unless you actually count the abomination that is Miitomo). Fire Emblem Heroes, a classic turn-based RPG optimized for mobile gaming, has come out for Android and iOS in Australia, Europe, and Japan, and is due out in North America and other worldwide locales very soon. Due to Nintendo's staggered release, the game isn't available to us in the United States at the time of this writing, but fret not—there's another way to downloa...

You may not know what HTTP is exactly, but you definitely know that every single website you visit starts with it. Without the Hypertext Transfer Protocol, there'd be no easy way to view all the text, media, and data that you're able to see online. However, all communication between your browser and a website are unencrypted, which means it can be eavesdropped on.

Here I will show you how to properly dig information on the web that has already been published, you just dont know it.

Over the past decade the Internet community has been witness to the rise of many new forms of online interaction. These new technologies have given rise to anonymous networks (like TOR), black markets within the deep web network (like the Silk Road), and even forms of digital currency, or more accurately crypto-currencies, such as Bitcoin. All of these technological advancements have contributed to securing users around the world and protecting their privacy. Therefore it is no surprise that ...

Mobile payment systems have been around for almost 5 years now, starting with Google Wallet. But when Apple got into the game last year with their new Apple Pay service, things really started to take off. Around this time, Samsung responded by acquiring an up-and-coming mobile payments company that owned the rights to an incredibly innovative technology called Magnetic Secure Transmission (MST).

Investing is like exercise—we all know we should be doing more of it, but we often just can't find the time. I mean, really, who's got the hours, inclination, and skill to pour through volumes of data and put together a balanced yet sophisticated portfolio of investment vehicles tailored specifically to optimize their returns while mitigating potential risks. Not me, that's for sure.

We've all been there. Stranded in a large lot or parking garage, braving the rows upon rows of identical cars in an endless concrete landscape because, for the very life of us, we can't remember where we stashed the very ride that brought us there.

Telling others that you have crabs isn't always a bad thing. Especially if those crabs of yours are baked into crab cakes! A delicious staple on the east coast, and a favorite in the Hamptons, crab cakes are the ultimate summer dish.

Here at WonderHowTo, we're used to seeing zillions of hairstyling tutorials that focus on "beachy, summer hair" or "bohemian braids a la Lauren Conrad." Summertime is a great time to experiment with your hair, but it seems that many of us lean on our braids and waves like LBDs.

Mike Callahan from Butterscotch describes how to manage the passwords on your iPhone by using the 1Password app. The application costs $5.99 for the Pro version. First, you enter an Unlock Code to give you access to the app. The icons across the bottom of the screen correspond to different features of the app. The Logins icon stores your login information. The Wallet icon stores information about your credit and bank cards. The Passwords icon holds all your passwords. The Add icon allows you ...

One of the most challenging, arduous parts of gardening is weeding vegetables that are close to the ground. Cabbage, for instance, leafs out near the earth and can be fiendishly tricky to weed. In this Growing Wisdom gardening tutorial, you'll learn about some of the tools that can help you weed those hard-to-reach spots without breaking your back in the process.

Do you actually trust your friends to not mess around with your files when you let them check their email or get on Facebook on your computer or laptop? You should think long and hard about that. If you insist on letting anyone get access to your computer, you should check out this tip from Tekzilla. Learn how to prevent people from messing with your files. Keep your files from being deleted or renamed, and keep them secure.

Super Fly Life brings this iPhone, three-part, traveling video tutorial to teach you how to ease travel with iPhone travel apps. You could even double your dating experience with these time saving applications on the Apple iPhone. Some of them are free from the Apple Store and iTunes. These iPhone travel tips will help you live a Super Fly Life!

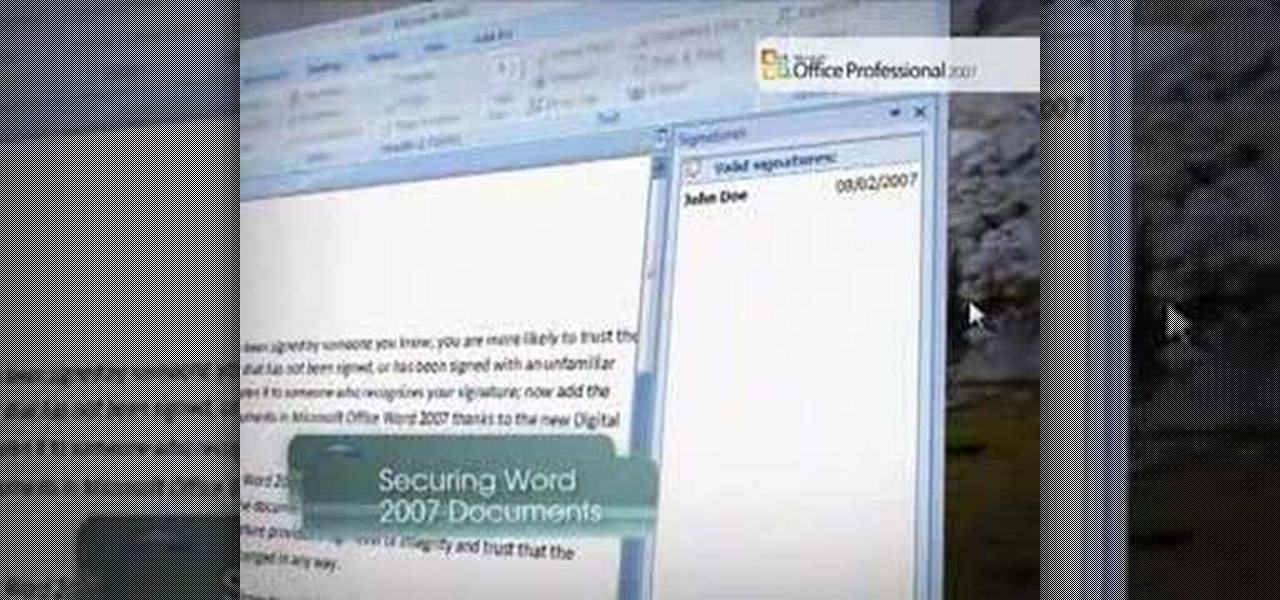
Securing Microsoft Office Word 2007 documents with Digital Signatures - When you receive a document that has been signed by someone you know, you are more likely to trust the contents than those of a document that has not been signed, or has been signed with an unfamiliar signature. Signing a document validates it to someone who recognizes your signature, now add the same degree of integrity to your documents in Microsoft Office Word 2007 thanks to the new Digital Signatures feature. For more...

Add a little South American flavor to your wrist by learning to make your own Peruvian bracelet. You'll need some heavy string and some macramé skills to craft your own Peru-style bracelet, but trust us—it's not hard. Just follow along with the video and see how easy it is.

This new episode of Full Disclosure shows you how to use a SSH Tunnel to secure your data when you are on an untrusted LAN (ex. Coffee Shop, School's network, or Defcon). Furthermore, you can use the SSH Tunnel to bypass the LAN's internet filters. The SSH tunnel protocol works by encapsulates your data into an encrypted payload and transmitting it to the SSH Server which is setup on a trusted LAN.

If you like to shop online then it is extremely helpful to have a PayPal account to safely make your online purchases. Help reduce your risk of identity theft by using protected methods like PayPal when your credit card information is involved.

Everyone benefits from positive coping strategies when dealing with divorce – learn how. Step 1: Stay in touch with both parents

If you're trying to learn a new skill, you wouldn't want to waste your time learning from someone with sub-par experience. No, you'd want to learn from the very best of the best to ensure you're getting a quality education.

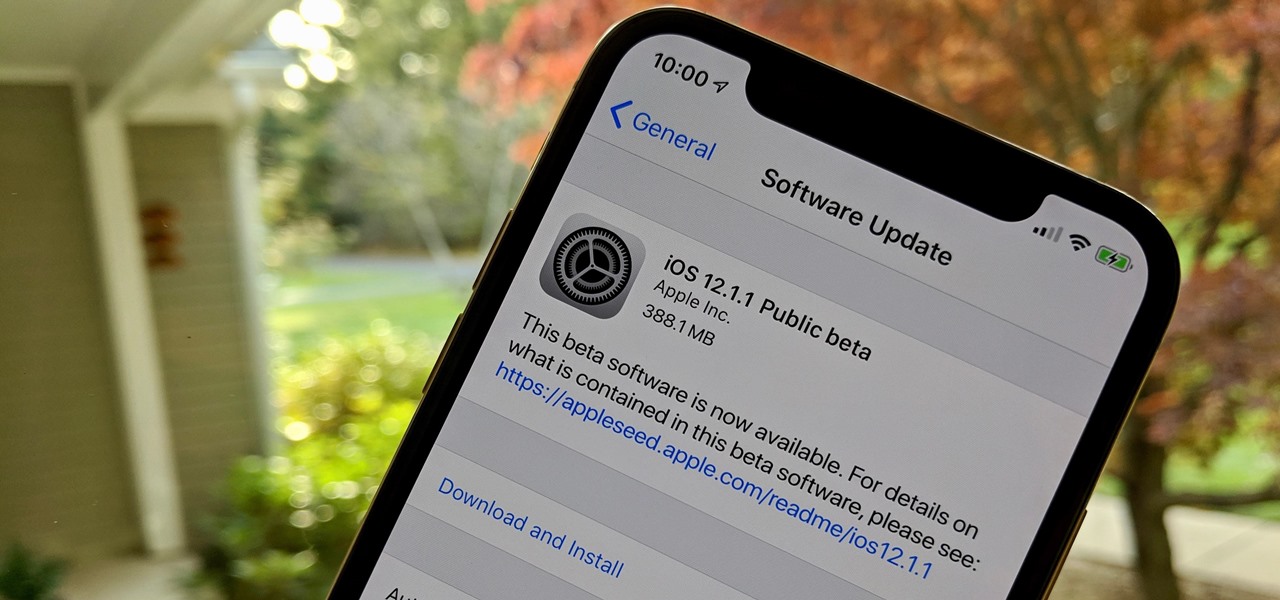
Get ready for more software testing. Just two days after the official release of iOS 12.1, Apple seeded public software testers iOS 12.1.1 — one day after developers received the update. While the rest of the iOS world is just getting to know all of the cool, new 12.1 features, testers are now sinking their teeth into what the next iteration of iOS has to offer.

US blood banks have assured the American public that they have the tools to prevent a Zika contamination, despite the rapid spread of the disease.

Emojis, for better or for worse, have essentially taken over online forms of communication. And now, thanks to a recently discovered feature in iOS, they are going to change the way you search for nearby places.

If you haven't read the last article, feel free to stop by and give it a read, but abstaining from reading it will not, for the most part, be detrimental to your understanding.

Google recently rolled out a new Smart Lock option labeled "On-body detection" for Android Lollipop via an update to Google Play Services. As I'm sure you can gather from the name, this new function keeps your phone or tablet unlocked using the built-in accelerometer to determine whether or not your device is being carried on your body, allowing you to set it down and walk away carefree knowing that's it's locked again.

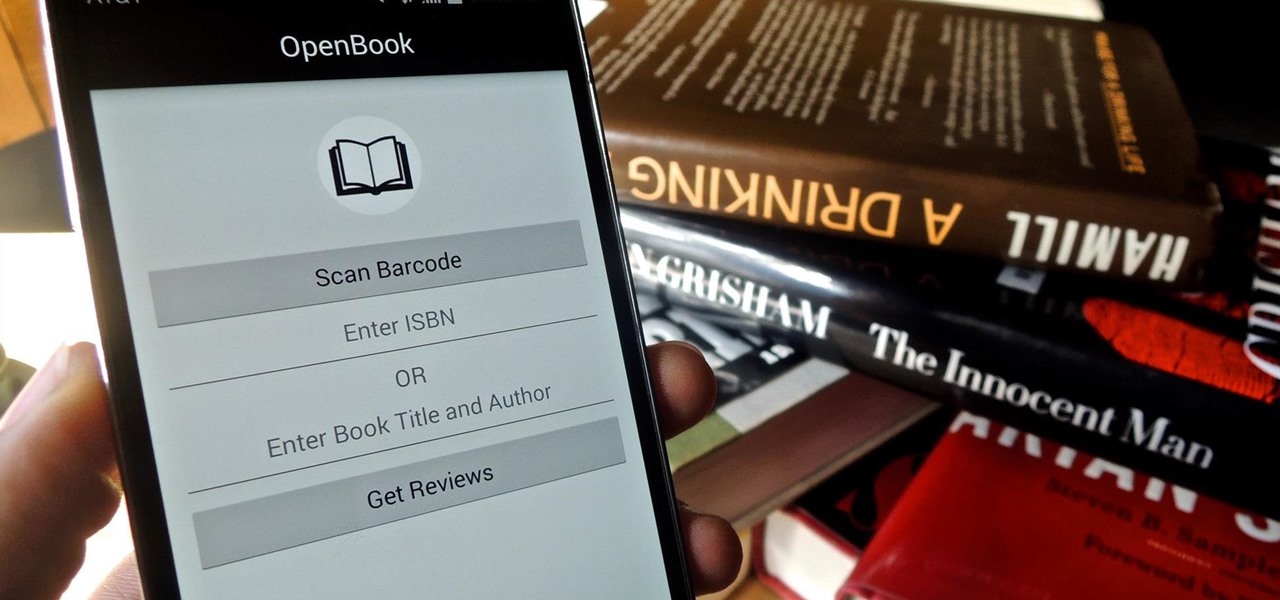
Purchasing an actual book from a brick-and-mortar store is becoming increasingly less common for people to do, but it hasn't completely gone out of style just yet. There's something about entering a bookstore and viewing all the potential great stories and epic tales just sitting on the shelves, waiting to be discovered.

People who know that I am a professional hacker often ask me what they can do to make their computers and personal information safe from people like me. The answer, of course, is that nothing will make you completely safe, but there are a number of measures any computer user can take to reduce the chances of being a victim of a hacker.

Let's be real, browser histories are virtually useless. Trying to find something you passed up a week ago is like, pardon the cliché, finding a needle in a haystack.

Snapchat is like that very attractive girl at the bar that has one too many shots and ends up slobbering on the bouncer as she gets led out. Of course she can still recover since she is hot, but you only get so many chances before you just become a complete failure. And that's where Snapchat has been treading these past few weeks.

A wave of shock and anger swept across the country after Edward Snowden released private documents recounting the U.S. government's secretive mass surveillance programs. Although some of the fear was unwarranted (they don't read your emails or listen to your calls), many scrambled to find privacy of new heights for protection from the all-watchful eye. While the government may not be tracking you down, there are a myriad of other candidates that fill that Big Brother role—and I'm not talking ...

Whether it's because you have no access to the internet or because you're simply on vacation, having someone else check your emails may be a possibility. You can give them your password and screen name, but that's never a good thing. Giving out your password to anyone, even someone you trust, is not something that I would ever suggest for two reasons:

With this video, we learn how to deal with a girlfriend who tends to tell white lies. First, don't set an ultimatum with the girl, this will end up in a verbal fight and can ruin the relationship. You need to start to create a new relationship with your girlfriend so she feels more comfortable with you. You need to tell her that if she keeps lying to you then it can cause you guys to end your relationship. The average person tells 26 lies a day, even if they are just white lies. Try working w...

By now you've probably heard of the duct tape crafting trend. If nothing else, the sour economy has inspired an upsurge of popularity in DIY stuff, including using duct tape to make everything from prom dresses to wallets.

Are you practically handicapped when it comes to crafting or doing anything at all that requires hand-eye coordination? We hear ya. While we aren't the most coordinated ourselves, even we have been able to complete the simple origami project in this video.

Trust is one of the most important aspects of a relationship. But there can be times when your instincts may be saying something that may conflict it. If you are dating someone who you think is still interested in his ex, then you need to find out before it's too late.

You've probably heard of cheetah print nails and even cheetah print eyeshadow (think the eyeshadow "rub-ons" at Sephora), but we can bet you've never heard of cheetah print hair. Your first question is probably whether or not this is even possible, but trust us, with a compressor doing cheetah prints on your hair is as easy as pie.