The USB Rubber Ducky comes with two software components, the payload script to be deployed and the firmware which controls how the Ducky behaves and what kind of device it pretends to be. This firmware can be reflashed to allow for custom Ducky behaviors, such as mounting USB mass storage to copy files from any system the Duck is plugged into.

If the rumors are right, Microsoft has decided to cancel the second version of the HoloLens, and they will instead move onto version three of their mixed reality headset. In the latest report, Thurrott's Brad Sams states that the expected release date of this new Windows Holographic device wouldn't be until 2019, a long two years away for those of us putting full effort into HoloLens app development.

It feels like someone reached into your chest and squeezed. Your head throbs in unison with your heartbeat. Clammy dread coats your body in sweat. Whether you call 911 or someone does it for you, the ER is your next stop.

Months before London-based Jonathan Moon would turn 30, he started musing over how to celebrate. While he had rung in past birthdays at home, he wanted to do something out of the ordinary as a farewell kiss to his twenties. A short ski vacation with friends felt like the perfect idea.

When performing something such as a mass mailer attack on a company, sending executables usually isn't the best option. That's why, in this tutorial, I'll be teaching you how to code a VBA script macro into a Word document in order to compromise a system. Combined with a little social engineering, this can be a very effective technique.

Smartphones are almost always connected to the internet, so it stands to reason that they can be hacked remotely. Or perhaps a jealous boyfriend or girlfriend got hold of your device physically, in which case they could've potentially installed a keystroke logger, a virus, or any other type of tracking app to spy on you.

With the countless daytime talk shows starring and featuring doctors, nurses, and other medical specialists, discovering new ways to live a healthy life is just a remote click away. Although their shows might draw you in with incredible facts and mind-blowing secrets to weight loss success, it's important to take each televised recommendation with a bit of suspicion—most of these familiar faces aren't exactly telling the truth.

The advent of a new Nexus phone begins with the bigwigs at Google partnering with a manufacturer, then selecting that manufacturer's flagship as the model for the new Nexus hardware.

Welcome back, my hacker apprentices! Several of you have written asking me how you can check on whether your boyfriend, girlfriend, or spouse is cheating on you, so I dedicate this tutorial to all of you with doubts about the fidelity of your spouse, girlfriend, or boyfriend.

Play "Scream" from High School Musical 3, an acoustic guitar tutorial. Follow along with this demonstration, tabs & lyrics here:

The Library of Congress video archives brings this Baroque dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a pas de menuet de deux mouvements. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a Baroque pas de menuet de deux mouvements or minuet step of two movements dance.

The Library of Congress video archives brings this Baroque dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a pas de menuet de trois mouvements. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a Baroque pas de menuet de trois mouvements or minuet step of three movements dance.

The Library of Congress video archives brings this early nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Quadrille combination step dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do an early nineteenth century Quadrille step combination for figures forward and back as well as cross over.

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Grand March dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century Grand March dance, also known as The March, Polonaise, Grand Promenade, and Opening March.

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a German cotillon dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century German dance, also known as cotillon, German cotillon, "Blind Man's Buff," Le Colin Maillard,...

The Library of Congress video archives brings this mid-nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a three step waltz dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a mid-nineteenth century waltz dance, also known as La valse à trois temps, plain waltz, waltz of three steps, new vals...

The Library of Congress video archives brings this mid-nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Five Step Waltz dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a mid-nineteenth century Five Step Waltz, also known as Cinq Temps, Valse en Cinq Temps, or Waltze à Cinque Temps dance.

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Waltz dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century Waltz dance.

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a heel-and-toe polka or Bohemian dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century Bohemian or neel-and-toe polka dance.

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Carlton dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century Carlton dance.

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Loomis' Glide Mazurka dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century Loomis' Glide Mazurka dance.

In the great smartglasses race, component makers, such as those that supply the crucial waveguide displays that make visualization of virtual content possible, have a vested interest in pushing the industry forward in order to ship units.

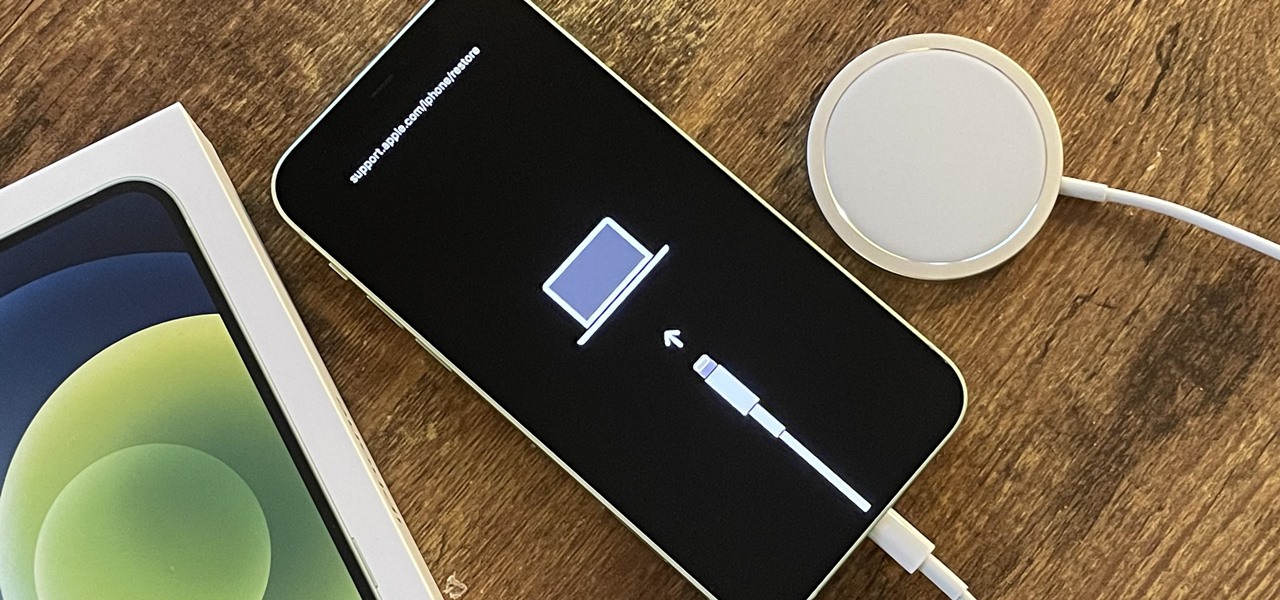
While it's rare, there could be a day when your iPhone 12, 12 mini, 12 Pro, or 12 Pro Max isn't responding, where taps and swipes on the screen do nothing, and the Side button won't let you force a restart. The culprit could be any number of problems, from corrupted files to beta software or even manufacturing issues. But one thing is certain: recovery mode could help you get back up and running.

No website, service, or platform is immune to being abused or exploited by hackers, and Google Analytics is no exception. To better understand how Google Analytics can help deliver payloads and bypass security protocols, one might want to learn how to use Google Analytics from a user's perspective first.

Alongside Sesame Street, the Dr. Seuss universe has been a constant presence in the formative years of several generations of children in the US.

XDA recently reported on a leaked version of the upcoming Pixel 4's camera app. By testing the app, they were able to find upcoming Pixel 4 features like a new Night Sight mode that can photograph stars. Well that leaked version has leaked itself, so now you can install it on your own Pixel phone.

As a root user, you have a lot of responsibilities to make sure your phone stays secure. Expectedly, some things may slip through the cracks. Remembering to check which apps have been granted root access is extremely important. All it takes is one bad app, so it's good to learn how to avoid that at all cost.

A lot of people still trust their web browsers to remember every online account password for them. If you're one of those users, you need to adopt a more secure way of managing passwords, because browser-stored passwords are hacker gold mines. With a USB Rubber Ducky and physical access to your computer, they can have a screenshot of all your credentials in their inbox in less than 60 seconds.

Yelp reviews are great for getting a feel for how a business operates, but they can't always be trusted, and they don't always get to the point fast enough. That's where "Tips" come in, and you can view and make them whether you're on an iPhone or Android phone.

When you think of companies that represent pillars like "privacy" or "security," Facebook is pretty far from the top of that list. However, the social media empire is making strides — small strides — to win trust with how it handles your user data. One of those efforts involves a way to prevent Facebook from tracking your iPhone or Android phone's location when you're not using the app.

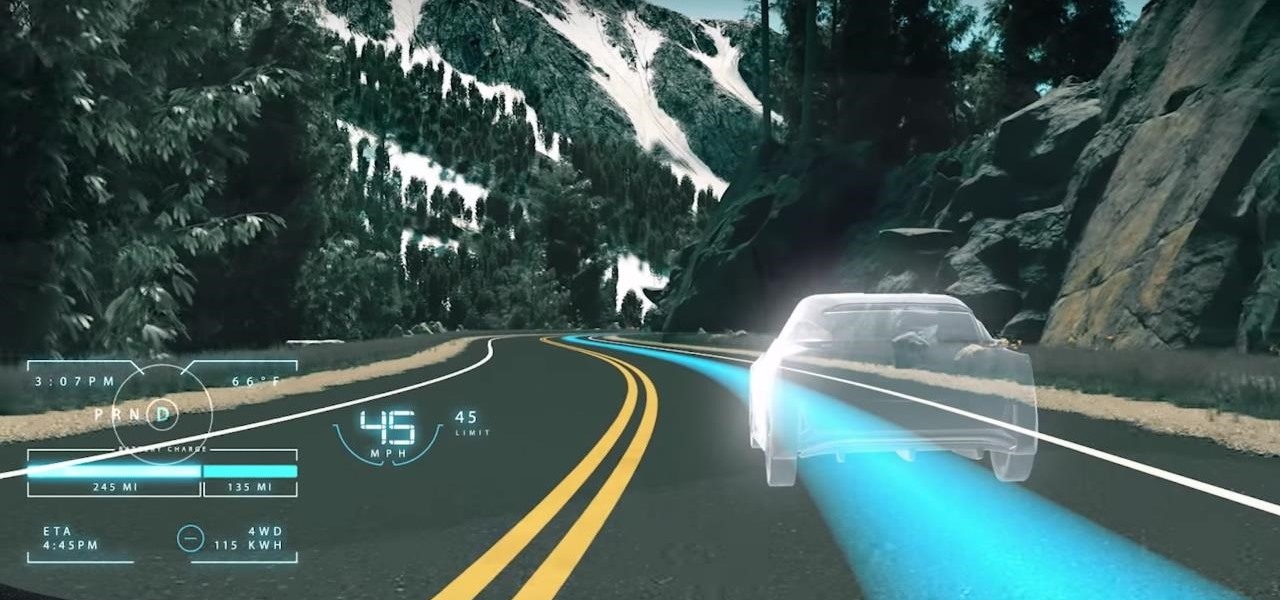
While the technology companies continue to drive forward with autonomous vehicles, Nissan's vision of the future of self-driving automobiles lies in a cooperative experience between human and machine, facilitated by augmented reality.

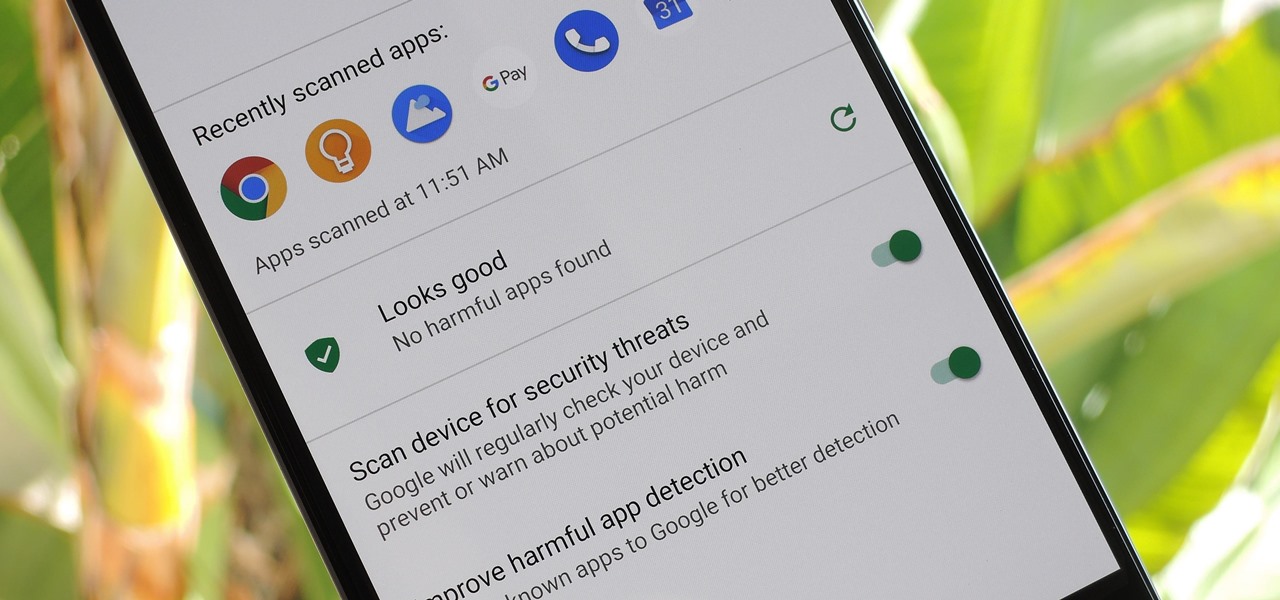
According to Google's new Android ecosystem transparency report, you're eleven times more likely to be infected by malware if you're running Android Lollipop (5.0) as opposed to Android Pie (9). The same report shows that if you sideload apps, you're almost seven times more likely to be infected than if you stick to Google Play as your app source. All of the data provided in the report is quite interesting, but there's a clear pattern among malware-infected users.

Do price tags on mobile games give you pause? We get it. With so many freemium games out there, it's tough to justify spending three or four dollars on a game for your iPhone or Android device. That's why you wait for moments like this one, as both "Reigns" and "Reigns: Her Majesty" are aggressively on sale.

Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Escape rooms, those real world puzzle games that challenge teams to solve a mystery and gain their freedom from a locked room, are all the rage right now. But augmented reality games such as The Lockdown could make them obsolete.

While privacy and security are cornerstones of Apple's ecosystem, your iPhone isn't bulletproof. Creating a strong passcode will protect you from most threats, but there exist tools that can break through even the toughest passcodes via the Lightning port. Luckily, Apple has implemented a new security feature to disable your Lightning port and keep your data safe and secure.

With the change to a glass back, many of us are concerned about the durability of OnePlus 6. While glass does offer some benefits such as lighter weight, without proper reinforcement, it can easily shatter in one drop. Now we have our our first look at its durability thanks to JerryRigEverything.

Last week, we told you about Microsoft's Alex Kipman and his nomination for the annual European Inventor Award, presented by the European Patent Office (EPO). And while that's big news in and of itself, it turns out we overlooked a very important detail buried in the EPO's video presentation. What was it? Only one of the most sought-after data points related to the HoloLens since its launch: how many have been sold.

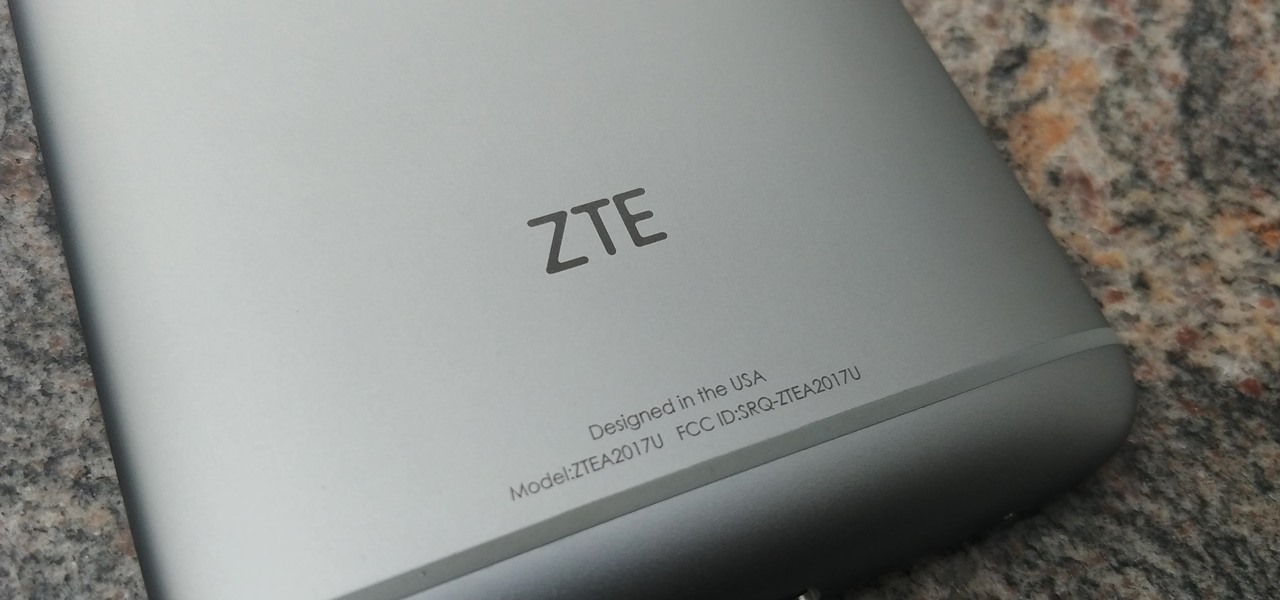
When Google first announced Android Oreo (Go edition), many believed these devices would be focused more on developing countries. However, thanks to ZTE, we'll be getting Android Go stateside, so US customers on even the tightest of budgets can still enjoy the convenience of a smartphone.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.