As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.

One of the first things most people ask for when staying with a friend is the password to the Wi-Fi network. Even if you trust your friends to the end of the earth, a super secure password can be a pain to share with them, especially if it's just a bunch of random characters.
While becoming the next Mark Zuckerberg may be out of reach for someone just getting introduced to code, the skill has never been more valuable. Just understanding basic programming language is a great thing to put on your resume, and if you know how to code, you’re golden. Software developers and programmers have been the most resistant to the recession, as jobs in the tech industry continue to grow.
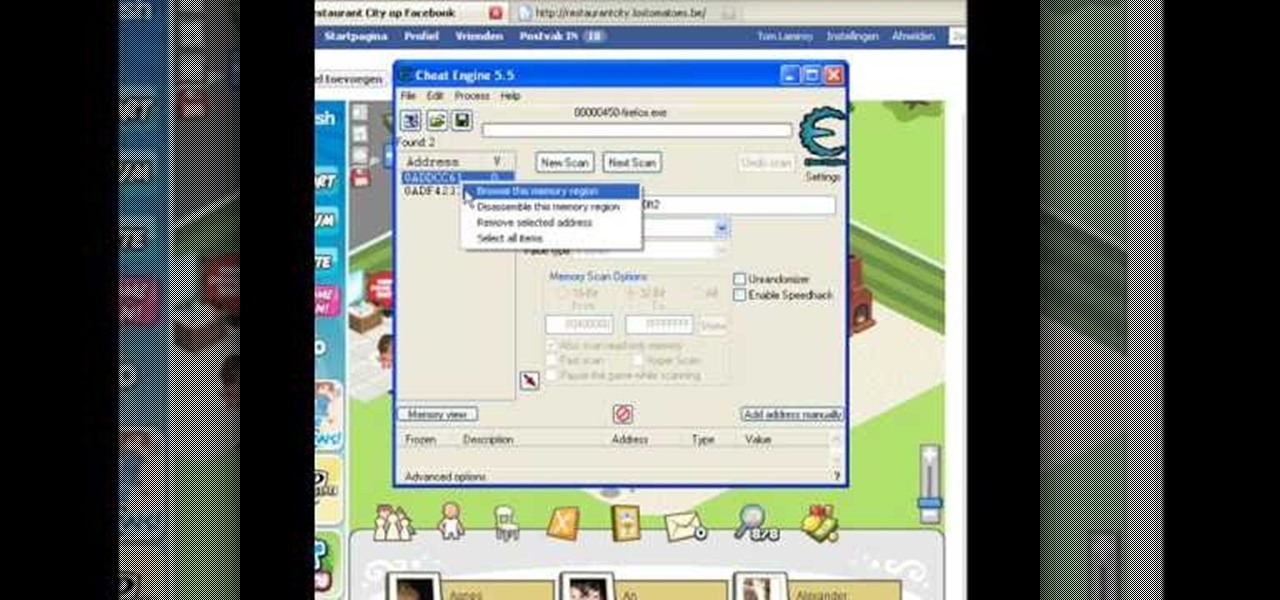
Make sure you use FLASH Player 9 First: Deinstall Flash Player 10

Managing your busy schedule just got easier in Entourage 2008 for Mac. Using the powerful Entourage Calendar feature lets you organize your time wisely. The Microsoft Office for Mac team shows you just how to organize your schedule with the calendar in this how-to video.

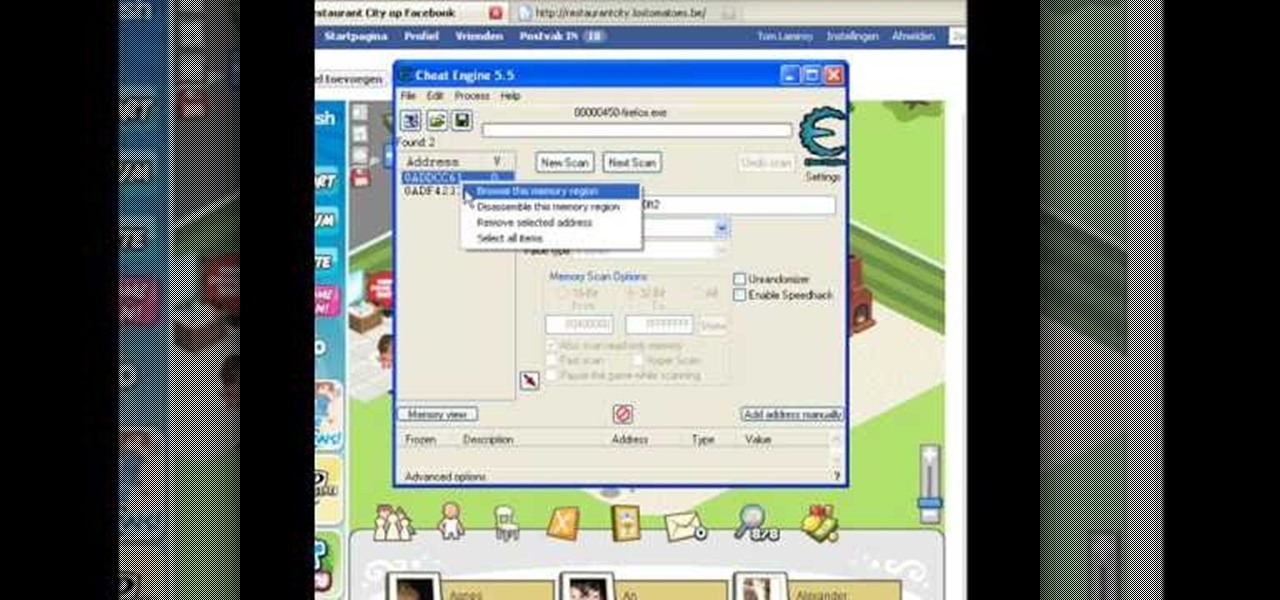
Looking for some fun cheat codes to get some extra fun out of your game of Grand Theft Auto: San Andreas? These codes are specifically for Playstation users. Make cars fly or float away when they get hit, or enter into Chaos Mode!

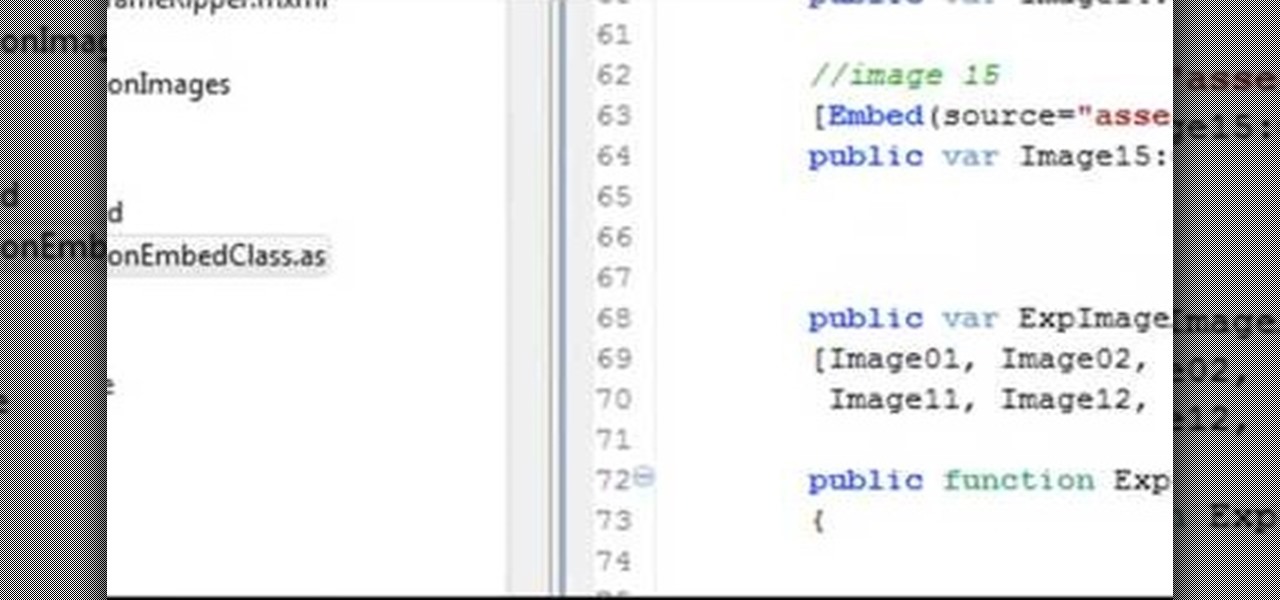
Make a Spark frame ripper

Error code P0401 on a 2004 Ford Focus indicates EGR Insufficient Flow, which usually means your DPFE sensor needs to be replaced. If you're not sure though, and you shouldn't be, watch this video to learn how to perform a test that will make sure your DPFE sensor is actually broken before you replace it.

Facebook has provided developers with a whole library of code usable for creating applications. This tutorial shows you how to get the code, and then how to use it so you can start developing your own Facebook apps using Adobe Flash and Action Script

Add an extra level of security to your website by creating your own dynamic 'Buy It Now' button for PayPal-using visitors to your website. Coding this button is very easy, and you can even animate it to draw more attention to your webstore.

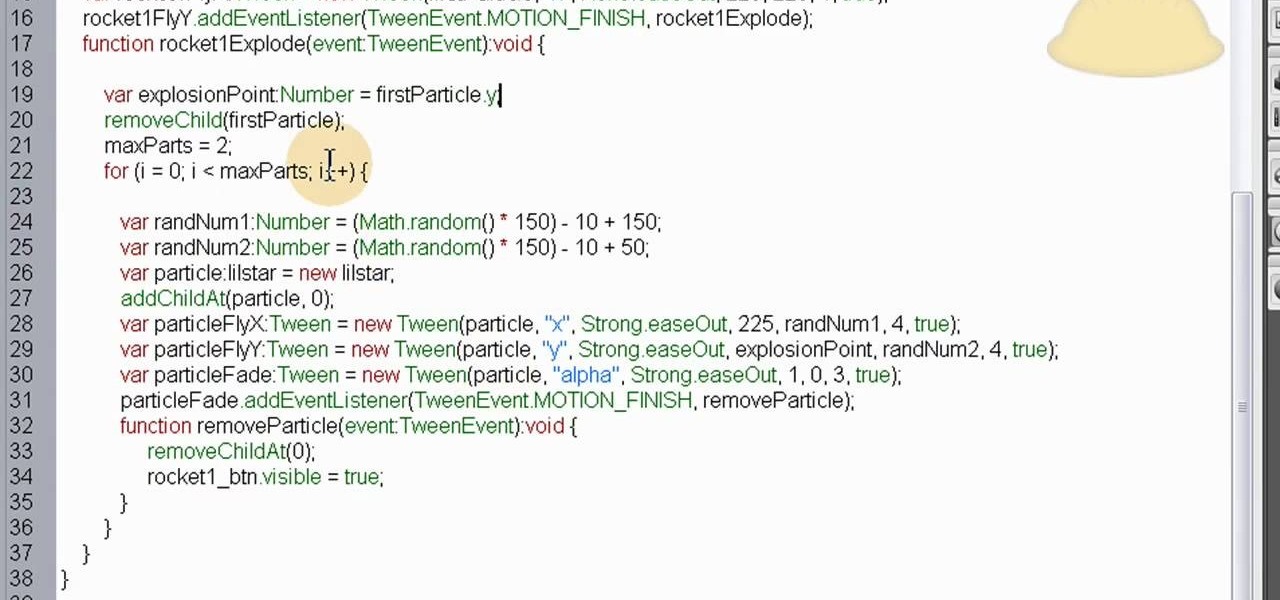
This is a custom particle effect, coded using ActionScript 3, that will recreate the effect of a rocket and fireworks explosion. The effect is also randomized, so you'll never get the same animation twice. This tutorial shows you how to code this effect using Fireworks.

If you have created a product that you want to sell, getting a UPC code for it will allow you to track purchases and give your business a more professional air. This video will explain how you go about getting a UPC code and using it to help your business.

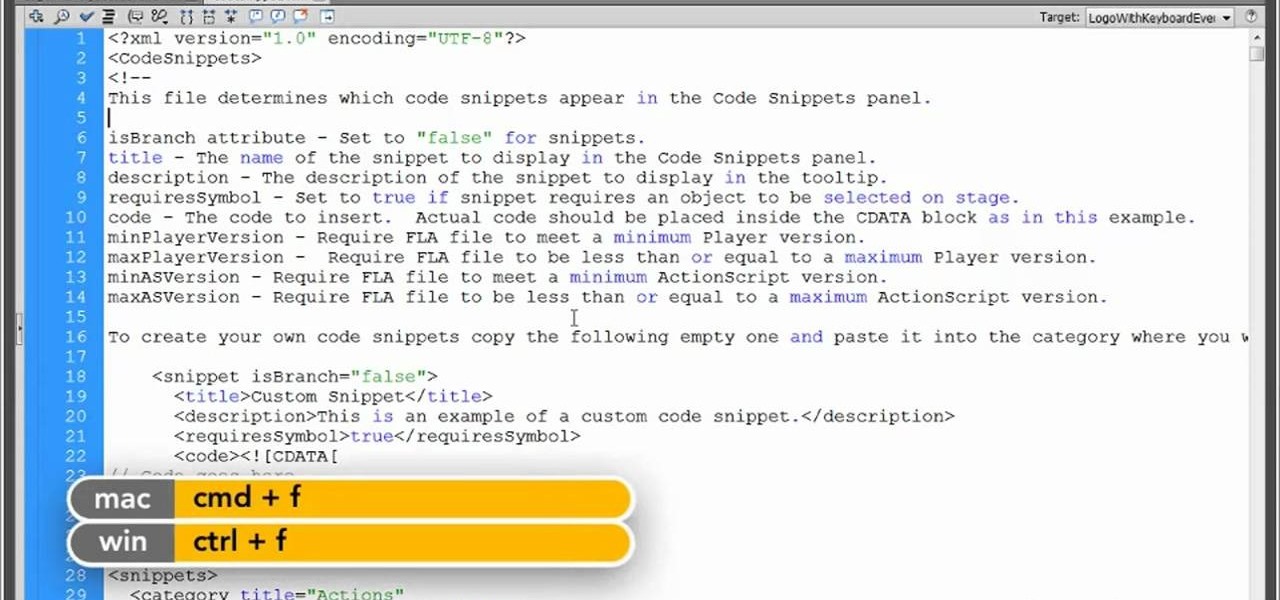
In this clip, you'll learn how to tweak any existing Code Snippet when working in Flash CS5. Whether you're new to Adobe Flash or merely unfamiliar with Flash Professional CS5, you're sure to benefit from this free video software tutorial from Lynda. For more information, including detailed, step-by-step instructions, take a look.

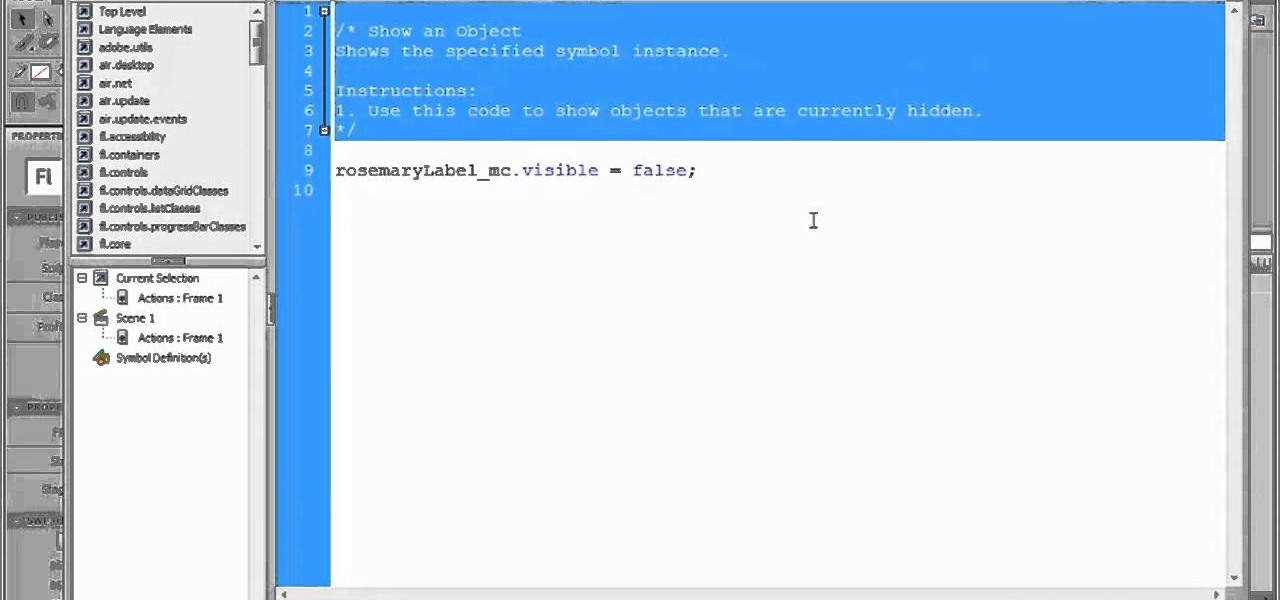
In this clip, you'll learn how to use Code Snippets to display and hide movie clips in Flash CS5.. Whether you're new to Adobe Flash or merely unfamiliar with Flash Professional CS5, you're sure to benefit from this free video software tutorial from Lynda. For more information, including detailed, step-by-step instructions, take a look.

Whether you're new to Adobe Flash or merely unfamiliar with Flash Professional CS5, you're sure to benefit from this free video software tutorial from Lynda, which presents a thorough, step-by-step overview on how to work with code snippets within Flash Professional CS5.

Google loves their little Konami Code Easter eggs. The Konami Code is famous among gamers for letting you cheat in video games. The latest one they come up with lets you try it out on Google Docs. All you have to do is open up Google Docs, and type in with the following keys: up, up, down, down, left, right, left, right, B, A, and then enter!

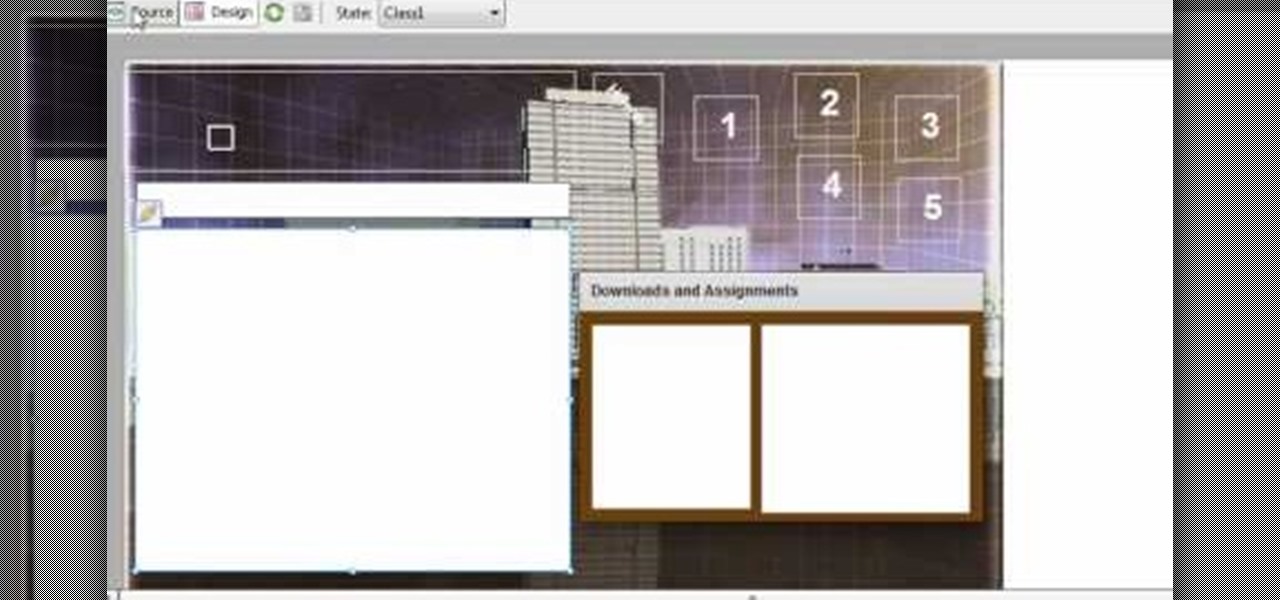
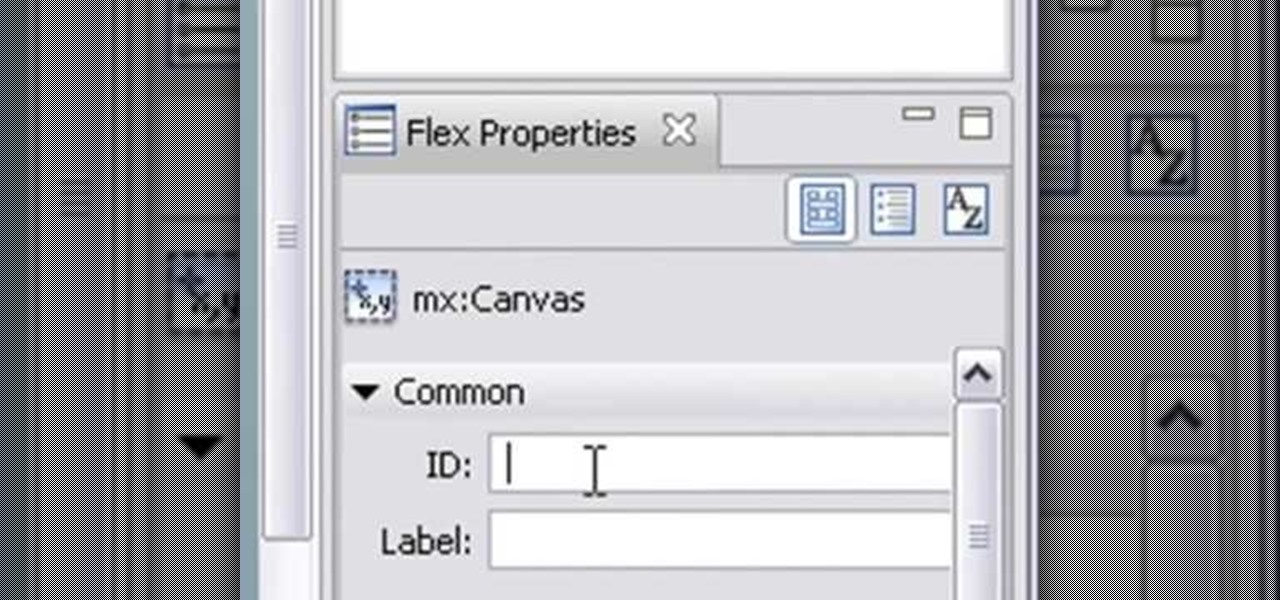
In this clip, learn how to program state codes and route buttons in Adobe Flash Builder. Whether you're new to Adobe's popular Flash IDE (previously titled Adobe Flex Builder) or simply wish to become better acquainted with the program, you're sure to find benefit in this free video software tutorial. For more information, including specific, step-by-step instructions, take a look.

See how to scan and read QR codes with your iPhone's camera. Whether you're the proud owner of an Apple iPhone 4G or perhaps just considering picking one up, you're sure to benefit from this free video tutorial. For more information, including a detailed overview, watch this iPhone user's guide.

It goes by many names. The RLoD (Red Lights of Death), the RRoD (Red Ring of Death), absolute disaster. Whatever you call it, the XBox 360 error that causes many console's front LED's to turn red in rage and cessation of function has caused all sorts of headaches for consumers and Microsoft. It can be caused by a couple of different cooling-related issues, and determining the error code that has caused your console to malfunction can go a long way to helping you fix it. This video will show y...

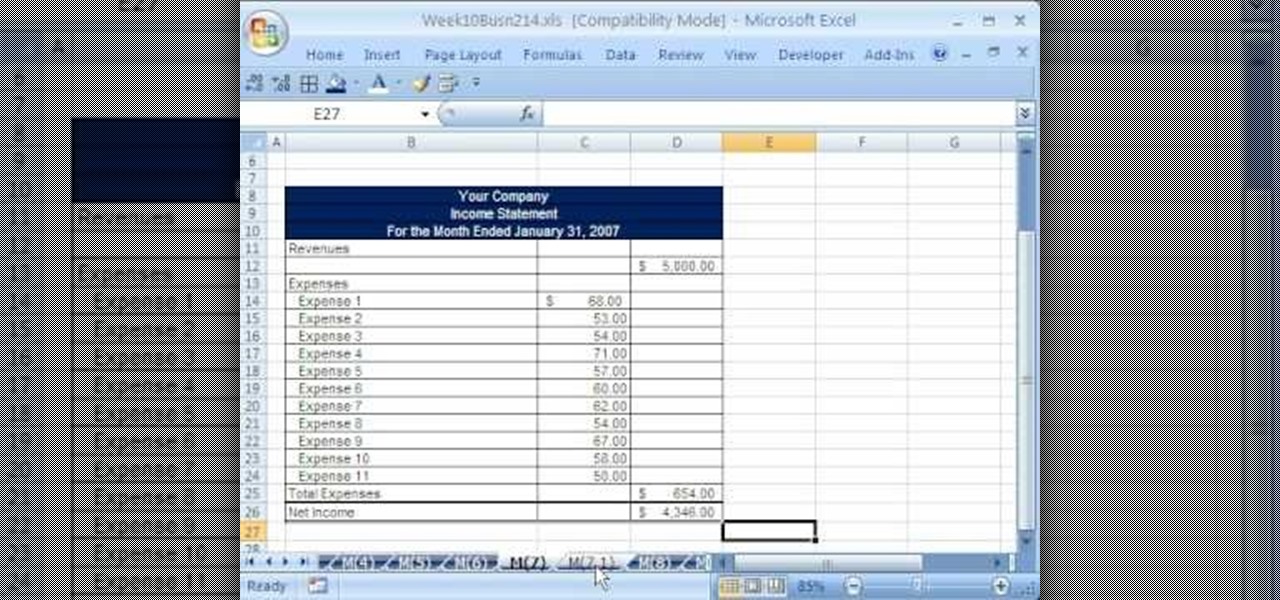
Whether you're interested in learning Microsoft Excel from the bottom up or just looking to pick up a few tips and tricks, you've come to the right place. In this tutorial from everyone's favorite digital spreadsheet guru, ExcelIsFun, the 54th installment in his "Highline Excel Class" series of free video Excel lessons, you'll learn how to find, download and use VBA code in your MS Excel projects.

This Dreamweaver CS4 tutorial takes you on a step by step process for installing an automated comment box system for your website. The system is a great way for communicating and interacting with your website users. It has a great feature that automatically sends you an email everytime someone comments in your website. Also it will allow you to post a reply by email.

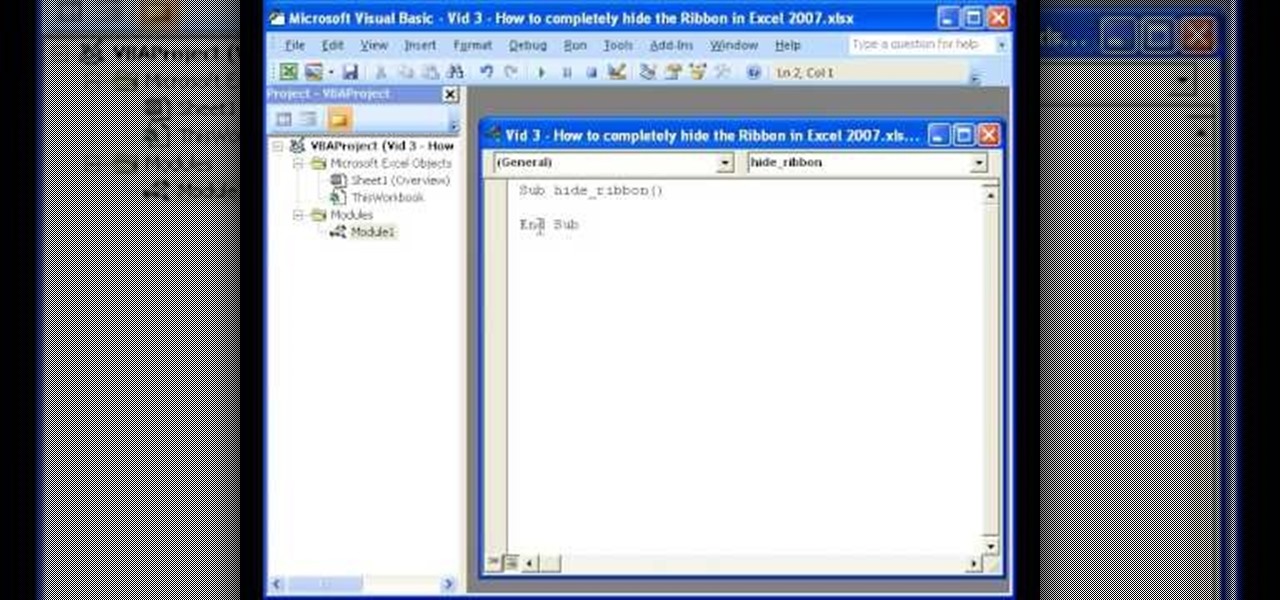
The instructor of this video shows you how to completely hide the ribbon, or the menu, in Excel. If you only want to partially hide the ribbon, you can use the shortcut control + F1. To completely hide the ribbon, though, go to the Visual Basic screen, hit Alt + F11. Then, go to insert, then module, and type in the macro "sub (Your name for macro)" then hit enter, then type in the code "application.executeExcel4macro''show.toolbar(""Ribbon"", false)''". To set up the code to show the ribbon a...

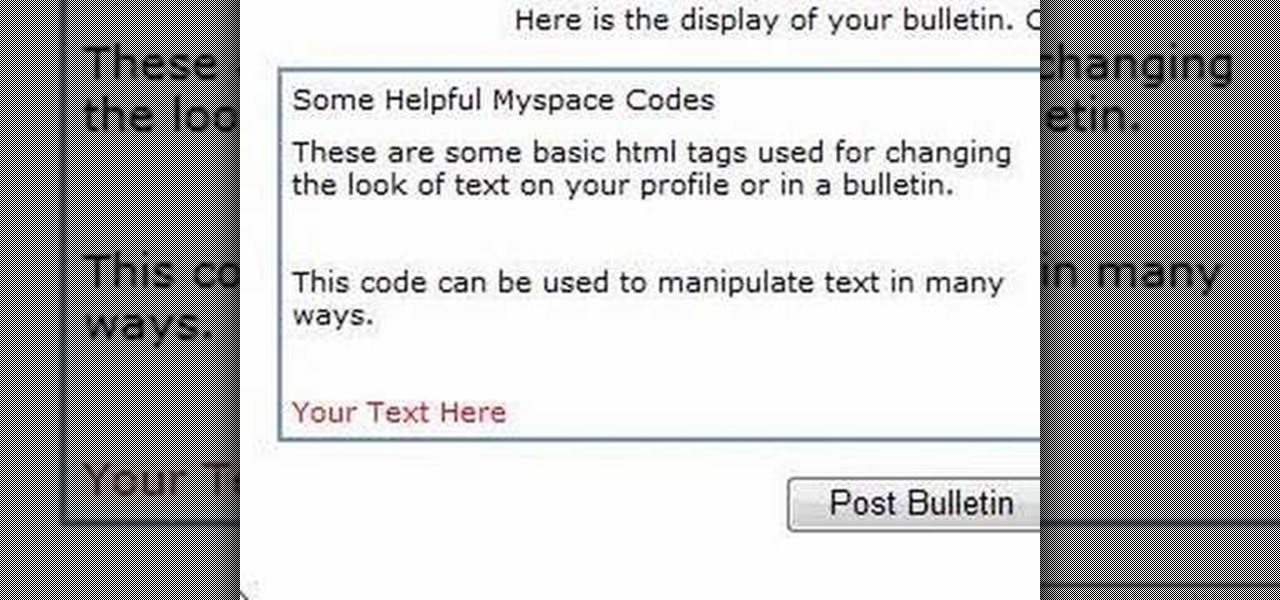
In this Computers & Programming video tutorial you will learn how to alter text on MySpace using HTML codes. Here are a few basic html codes used to change the look of text on your profile or in a bulletin. <b> for starting bold text and </b> for ending bold text. <i> this text will be italicized</i>. For underlining text use the code <u> </u>. <b><i><u> This text will be bold, italicized and underlined </b></i></u>. To change color of your text to ‘red’ use the code <font color=”red”> </font...

Cami, theburntmatches, shows us how to unlock all songs on Rock Band! It is a simple way to unlock all the songs in XBOX 360, PS3 or Wii Rock Band . This probably doesn't work with Rock Band 2 (RBII or RB2). This is a simple glitch or cheat code for the guitar hero like game.

Mike Lively of Northern Kentucky University demonstrates how to create a 3D plotting program for the sinc math function. Part 1 shows how to convert a Flash Package into a Flex application. Part 2 shows how to get the sinc function running and add different textures. Create a cool interactive 3D plotter in thie Adobe Flex Builder 3 and Papervision3D tutorial.

Mike Lively of Northern Kentucky University demonstrates how to build a jet band using Jeff Heaton's jet pack code. What is a jet band? Well, it's like a jet pack but smaller and allows you to go higher than 200 meters when flying in Second Life. Part one shows you how to create the code for the jet band. In part 2, the code is modified to remove the altitude reading below 70 meters.

There are a couple ways to include HTML when coding PHP. Learn two options that work equally well, then decide which one makes the code more clear and concise for you.

You may have seen a "check engine" sign on your car's dashboard when driving your vehicle. Maybe "service engine soon," or just "check". What does this mean if the alarm won't turn off, or comes on when you're driving? Find out in this automotive video tutorial how to read those trouble codes on your automobile.

This video demonstrates how to import XML code from the Internet into Movie Maker. The video shows you how to find the XML code on the Internet, how to download it, and how to import it into Movie Maker.

A stager is a small piece of software that's typically used by malware to hide what's happening in the early stages of infection and to download a larger payload later.

Being stuck inside for the near future is less than ideal, but at least you have the world of eLearning to sharpen your skills while you kick back on your couch. Case in point, The 2020 Premium Learn To Code Certification Bundle has all the training you need to start coding like a pro right at home, and it'll only cost you $39 today.

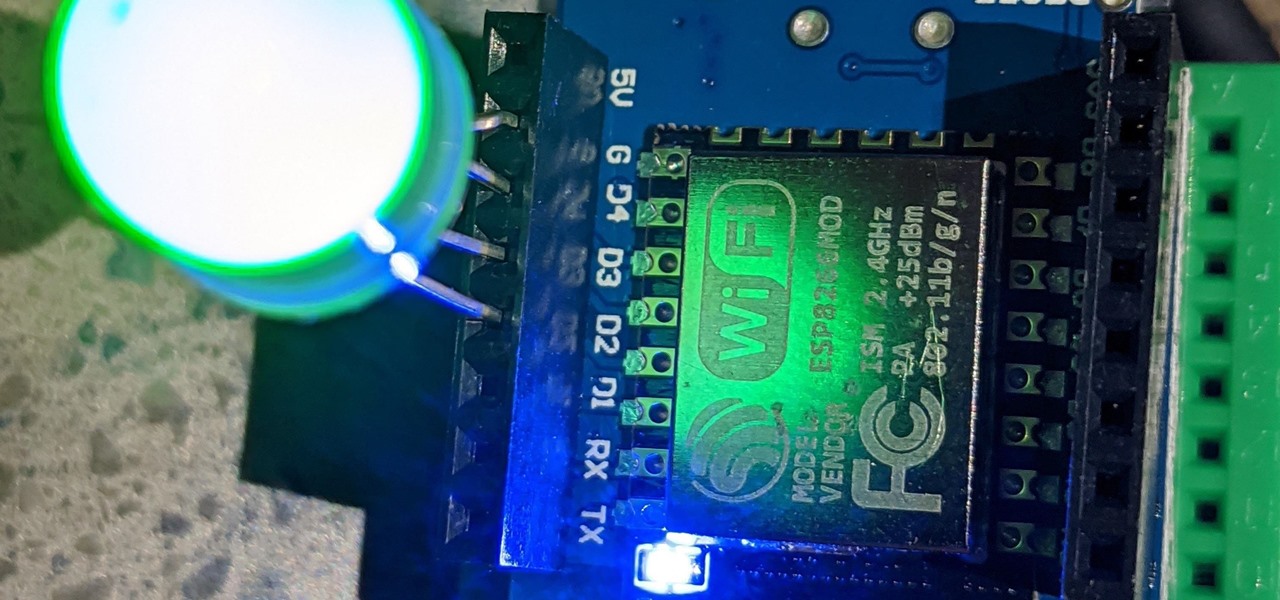
For anyone interested in using cheap, Wi-Fi-connected microcontrollers like the ESP8266, the Arduino programming language can be a barrier to entry. Based on C++, Arduino requires knowledge of more computer science than languages like Python. Fortunately for beginners, setting up MicroPython on an ESP8266 allows anyone to write Python on affordable microcontrollers in a matter of minutes.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

With a tiny computer, hackers can see every website you visit, exploit services on the network, and break into your Wi-Fi router's gateway to manipulate sensitive settings. These attacks can be performed from anywhere once the attacker's computer has been connected to the router via a network implant.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

QR codes have become a staple in our everyday lives. Companies use them for everything from marketing promotions to movie tickets thanks to security they provided for these types of transactions. But for years, Android users had to download an app to scan these codes. Well, not anymore.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

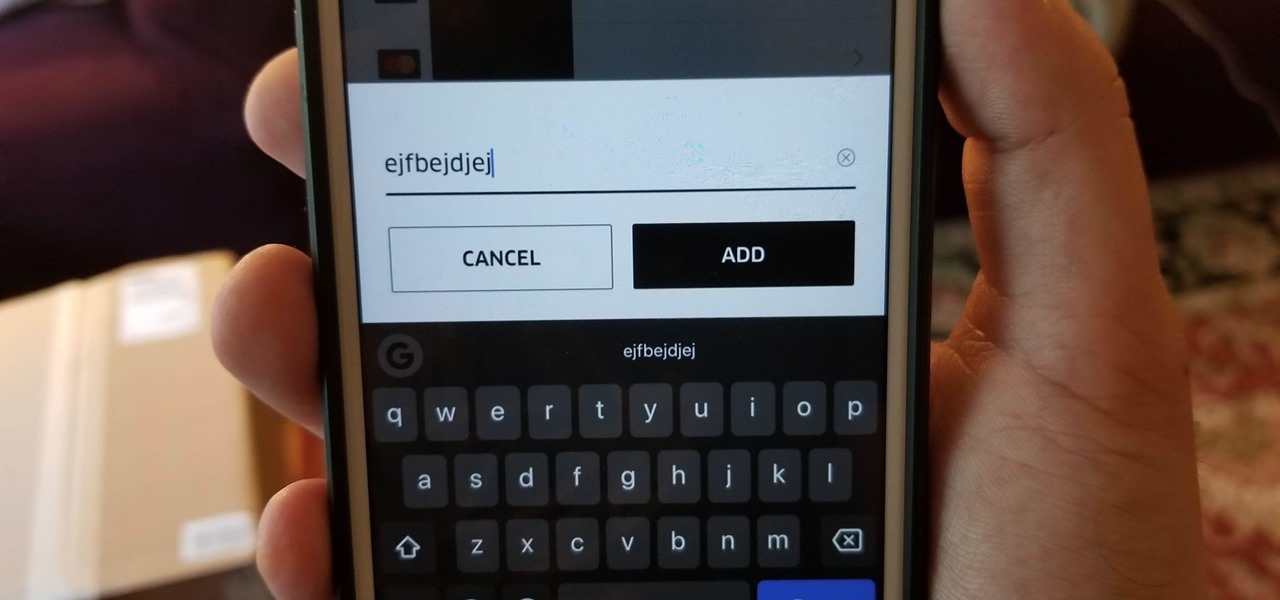
Uber is one of the best ways to get around, but nobody said it was cheap. What's even more infuriating is when you have a bad experience with a ride. Sure, you can get a refund, but then you need to figure out where to enter in the promo code for the coupon that Uber sends your way.

Using Hydra, Ncrack, and other brute-forcing tools to crack passwords for the first time can be frustrating and confusing. To ease into the process, let's discuss automating and optimizing brute-force attacks for potentially vulnerable services such as SMTP, SSH, IMAP, and FTP discovered by Nmap, a popular network scanning utility.