
How To: Send a text message through email
Learn how to send a text message through e-mail. Just follow these steps. First step is to open a browser like Mozilla Firefox and other like Internet Explorer etc.


Learn how to send a text message through e-mail. Just follow these steps. First step is to open a browser like Mozilla Firefox and other like Internet Explorer etc.

This video is about how to make fine hair thick and wavy with a flat iron. This technique is done with an Ed Hardy iron. Before you start, it's good to put heat protector on the hair. Taking small sections, as you run the iron down hair make sure you are turning the iron. It helps that this particular flat iron is good at creating this type of look. As you are working, you should add hair spray so that the curls stay in place. This type of look is great for those women who have little or thin...

Learn how you would bypass a school’s web filters so that you can go to content sites that are always blocked in examples of YouTube. Click the ‘Start’ button and then click on ‘Run’ and type in cmd and hit enter on your keyboard. This will bring up a command prompt where you type in ‘ping’ and then when that populates the next prompt you enter in the website to bring up the IP address. By entering the populated number you can get into a website from the search field of a web browser. It incl...

This video shows you how to change you Mozilla Firefox page to look like Safari. -First go into your Mozilla Firefox page and go to Google.

Some artists don't even deserve a full star. Learn how to give them the half-assed rating they deserve.

Getting a tattoo will never be a walk in the park, but it can be less painful if you take a few simple precautions.
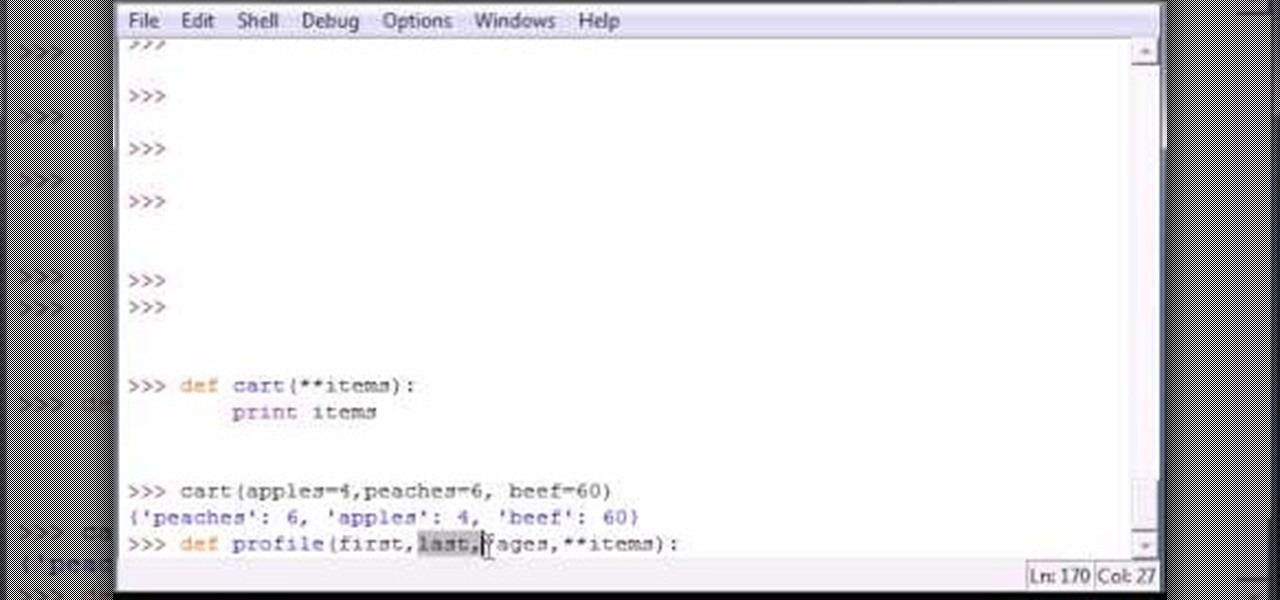
Bucky from The New Boston serves up this Python video tutorial on how to program parameters in Python. This is the program you use to write all of your Python code down. Different parameter types in the same function!

Oftentimes a friend will send you a PDF, MP3 or some other type of document such as a spreadsheet. When you open the file, an application opens. But sometimes it's not the application you wanted to associate with that file. In this video tutorial, you'll learn how to define which programs open what sorts of files. For more, and to learn how to set filetype application defaults in Mac OS X, watch this video tutorial.

In this tutorial, you'll learn how to use the emacs text editor, accessible through the terminal on any computer running Mac OS X, to play a simple version of Tetris. The steps are simple and as follows:
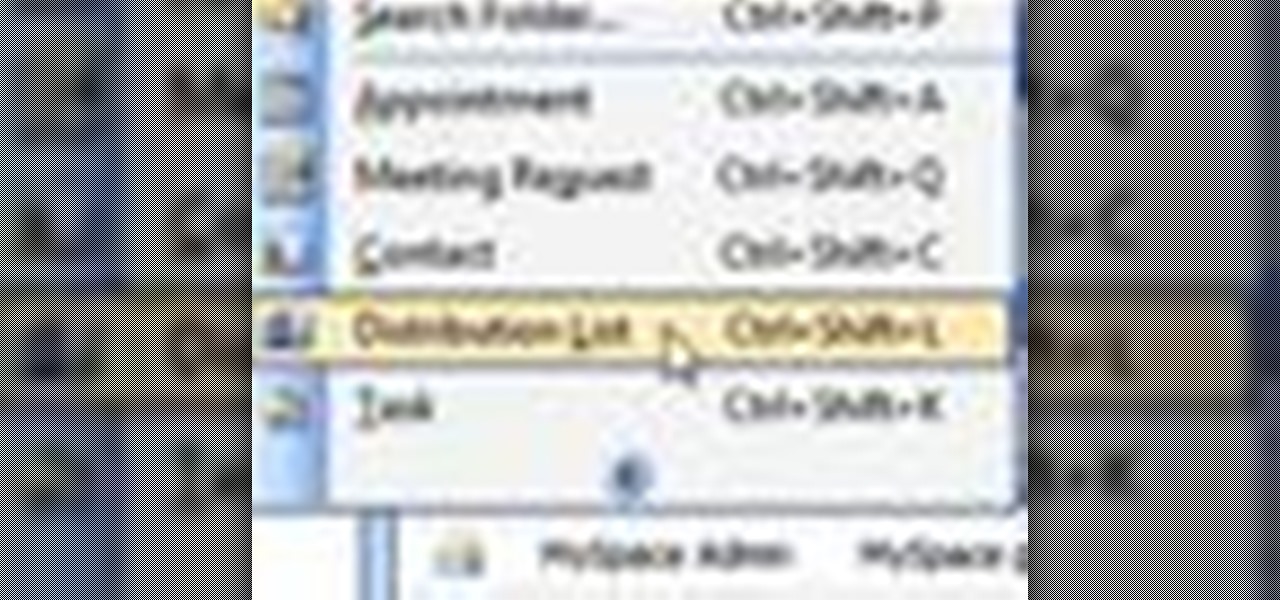
Whether you're a social type with a loooonnng list of friends or a PR gal with a bunch of people you've got to contact all at once to notify them of an event, it can often get time-consuming to type out the name of every single person you have to send the same email to.

This instructable aims to show you how to cut any type of disk to a desired shape. It is particularly useful in cutting down cheap 12cm DVD-+R 's into more expensive (can be up to 10 times more) 8cm DVD-+R disks. The technique shown here works with all disk types. The video below shows us cutting a music CD into a heart shape, and also illustrates the basics of cutting 12cm disks into 8cm ones. The actual cutting of a disk (and the guide) can be seen here:

Chef Don from HouseCallChef demonstrates how to grill mushrooms, asparagus, zucchini and yellow squash. You can also grill other vegetables such as parsnip, rutabaga, potatoes, tomatoes or peppers, and even some fruits like pineapple, watermelon, apples and oranges. You can use any type of grill that you want.
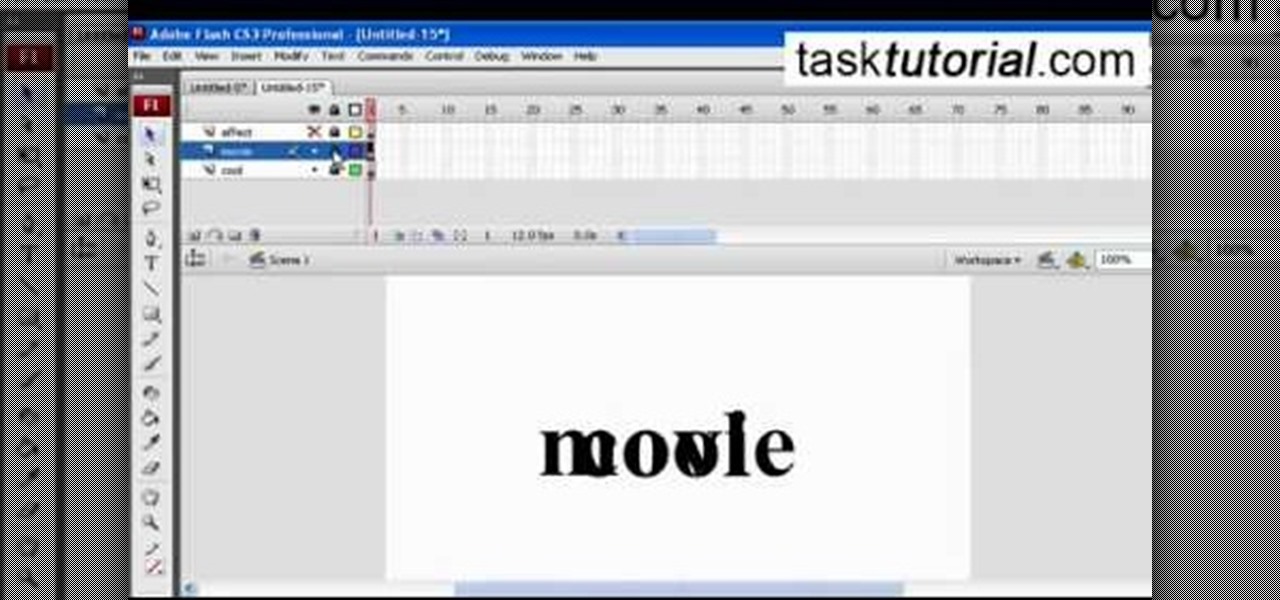
A great free video training from tasktutorial on how to create a cool movie text effect in Flash. Start by creating the text; type in "cool", rename the layer and lock it. Now type "movie" and rename the layer. Type in "effect" and rename this layer as well. Now focus on the first layer. Convert it to movie clip. Now convert the other two layers to movie clips as well. Stack the three layers on top of each other. Next add a key frame starting from frame 10. Select the "cool" layer. Re-size it...

Pixel Perfect is the "perfect" show to help you with your Photoshop skills. Be amazed and learn as master digital artist Bert Monroy takes a stylus and a digital pad and treats it as Monet and Picasso do with oil and canvas. Learn the tips and tricks you need to whip those digital pictures into shape with Adobe Photoshop and Illustrator. In this episode, Ben shows you how to transform a photo into a flashy poster in Photoshop.
This video teaches us how to make a quick cat animation in Photoshop, CS3 and Microsoft Movie Maker. She shows us really quickly on the computer. She starts off by drawing the cat itself. A solid knowledge of Adobe Photoshop is needed. You would need to know the different textures, tools, colors and many other features in order to draw the cat. After about 2 minutes of drawing the cat, she begins to narrate the first frame and then moves on to the animation itself. This is a start, watch the ...

Don't let Bejeweled Blitz get the best of you. Show it who's boss and get the highest score possible. Of course, you'll need Cheat Engine to overpower the game, so make sure you have Cheat Engine 5.5 or higher and check out this video for the hacking Bejeweled Blitz (10/09/10).

Whether you are protecting your children or hiding personal information, there are ways to block unwanted websites from your computer. Follow this tutorial and learn how to accomplish this on a Windows PC easily.

This video will show you how to use the ‘find’ and ‘replace’ text buttons in Microsoft Word 2007. Microsoft Word 7 is slightly different from the Microsoft you might be used to but with these instruction you’ll have no problem finding the buttons.

This video will go over how to insert a check box in Microsoft Word for printing or for electronic distribution. With just a few clicks you can get a check box. You can even add different symbols or styles for your check box.
Stan shows an easy way to see and clean the files that are hogging hard drive space in the computer using a free software called "windirtstat". Now enter the following address in the web browser "windirtstat.info" and scroll down the page until you get the downloading and installing section. Click on the link "windirtstat1.1.2Setup(Ansi&Unicode)" which will be right after the "for all flavors of windows" this will direct you to "SOURCEFORGE.NET" download creations. This will ask you to save t...

In this series of videos you'll learn how to draw with charcoal from a professional artist. Expert William Cotterell shows you what types of art supplies you'll need to get started, including various types of charcoal, compressed and pencil varieties, types of erasers that work best with charcoal, and the best types of paper for making charcoal drawings. He also shares tips for choosing a subject, understanding light, blending techniques, adding highlights, and using Fixatif to protect your w...

Remember when typing without physical keys seemed ridiculous? Now, touch typing is the smartphone norm. That said, mistakes are inevitable on small screens. So before you start hammering on that delete key or shaking your iPhone like a madman, know that there's a better way to undo text you didn't mean to type — no shaking involved.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

In the world of technology, there's often a trade-off between convenience and security. The Java Remote Method Invocation is a system where that trade-off is all too real. The ability for a program written in Java to communicate with another program remotely can greatly extend the usability of an app, but it can also open up critical vulnerabilities that allow it to be compromised by an attacker.

You may have heard of a signal jammer before, which usually refers to a device that blasts out a strong enough radio signal to drown out the reception of nearby devices like cell phones. Purpose-built jammer hardware is outright illegal in many countries. Still, Wi-Fi is vulnerable to several different jamming attacks that can be done with Kali Linux and a wireless network adapter.

Your Instagram bio could always be used to link to other websites or profiles or just to show off your witty personality. Now, you also have the ability to use this section to tag other Instagram accounts as well as add tappable hashtags. Whether you want to link out to your best friend, company, or the latest trend in your city — if it has a profile name or tag, it can be in your bio.

After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vulnerability.

PowerShell Empire is an amazing framework that is widely used by penetration testers for exploiting Microsoft Windows hosts. In our previous guide, we discussed why and when it's important to use, as well as some general info on listeners, stagers, agents, and modules. Now, we will actually explore setting up listeners and generating a stager.

JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.
Typing out thirty hashtags on Instagram is always such an annoying process. Figuring out the best hashtags to use to get more likes is also tricky. You can't just keep copying and pasting the same hashtags on every post — that's like attacking the same tribe every time. You got to diversify, which takes a lot of conscious effort to be on top of the current best hashtags to use.

Dramatic new research may change the fate of the hundreds of people who wait for a kidney transplant every year. The study hinged on the ability to cure hepatitis C infections, a possibility that became a reality in 2014.

Kik is an extremely popular messaging app, but it has a few annoying features that we all just sort of put up with. You can't turn off read receipts, nor can you hide when you're typing, and the photos you take with Kik's camera show up differently than ones you send from your gallery app. At least a couple of these features should be subject to change, but they aren't — well, not without some tinkering.

As many as 700 species of bacteria live on our teeth and in our mouth, and just like the microbiomes inhabiting other parts of our bodies, they change in response to diseases and other health conditions.

Android is a highly customizable operating system. Sometimes, we use these capabilities to add core functionality or streamline the user experience, but there are other times when customization is just about having fun and making your smartphone's interface more enjoyable.

It seems to me you can't swing a dead cat near an augmented reality developer without hearing the word Vuforia escape their lips. PTC's software solution has become the go-to for most developers in the mobile AR space, and since they recently added full support for the HoloLens in Unity, I figured it was about time we learn to make something with it.

Google has added a number of new features in the latest update to Google Keyboard including a one-handed mode and a setting that lets you adjust the height of the keys. The update hasn't gone live on the Play Store yet, but you can download the APK right now for both 32-bit and 64-bit phones.
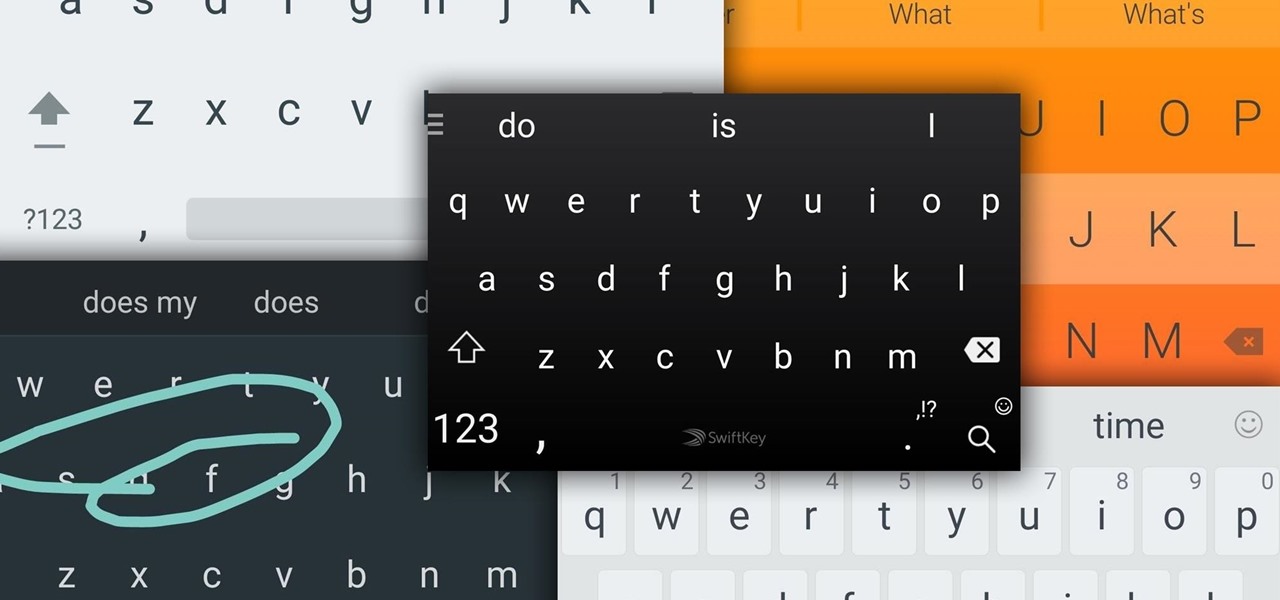
Google Now, Siri, and Cortana aside, the main way you interact with your smartphone is through the keyboard. Every app you use, every search you perform, every message you send—the most fundamental interface between you and your device is that handful of characters and those 26 letters on the bottom half of your screen.

In my last tutorial, I talked about creating a virus inside of a Word Document in the scenario of a mass-mailer attack. In this post, however, I'm going to be covering creating a fake image or screenshot with a meterpreter backdoor hidden inside to be used in a similar scenario. Step 1: Creating the Virus

Hello Everyone! I wanted to share a free and open source note taking tool that I've been using for quite some time now.

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them