Developers creating login systems know better than to store passwords in plain text, usually storing hashes of a password to prevent storing the credentials in a way a hacker could steal. Due to the way hashes work, not all are created equal. Some are more vulnerable than others, and a little Python could be used to brute-force any weak hashes to get the passwords they were created from.

Apple's next big developer event happened on June 4, and it was the first glimpse of iOS 12 that anyone's seen. While there were lots of rumored features to be unveiled at WWDC 2018, Apple concentrated mostly on squashing bugs and making iOS work as seamless as it did years ago. Still, we had hoped that Apple would have added these features in iOS 12, but only a few made the cut.
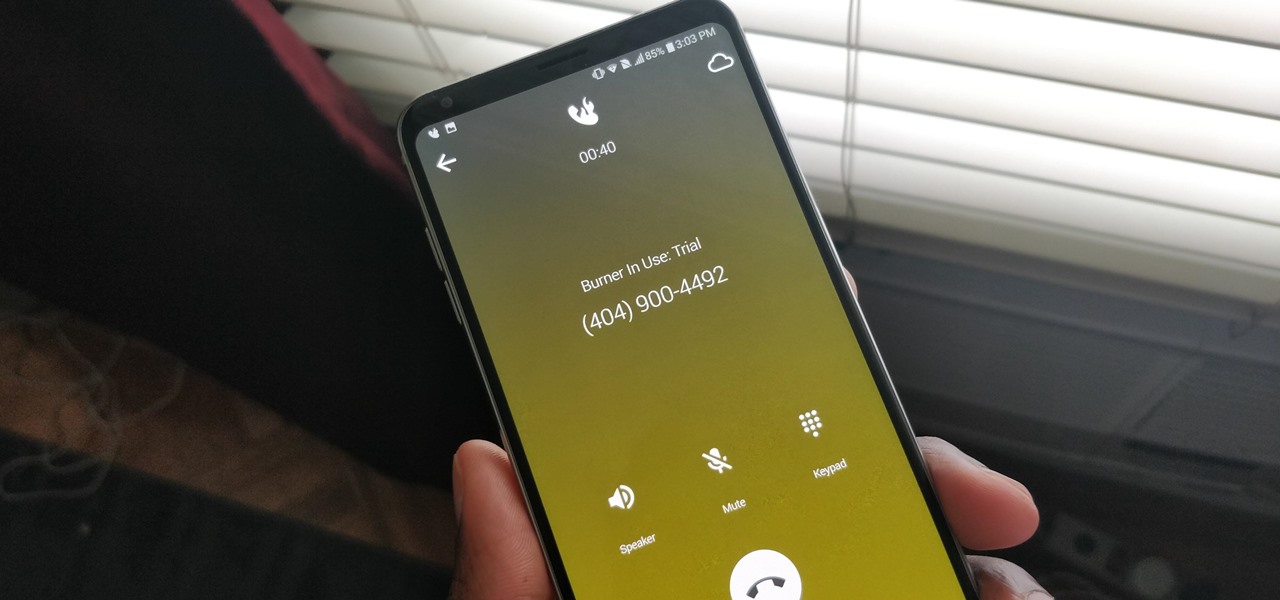
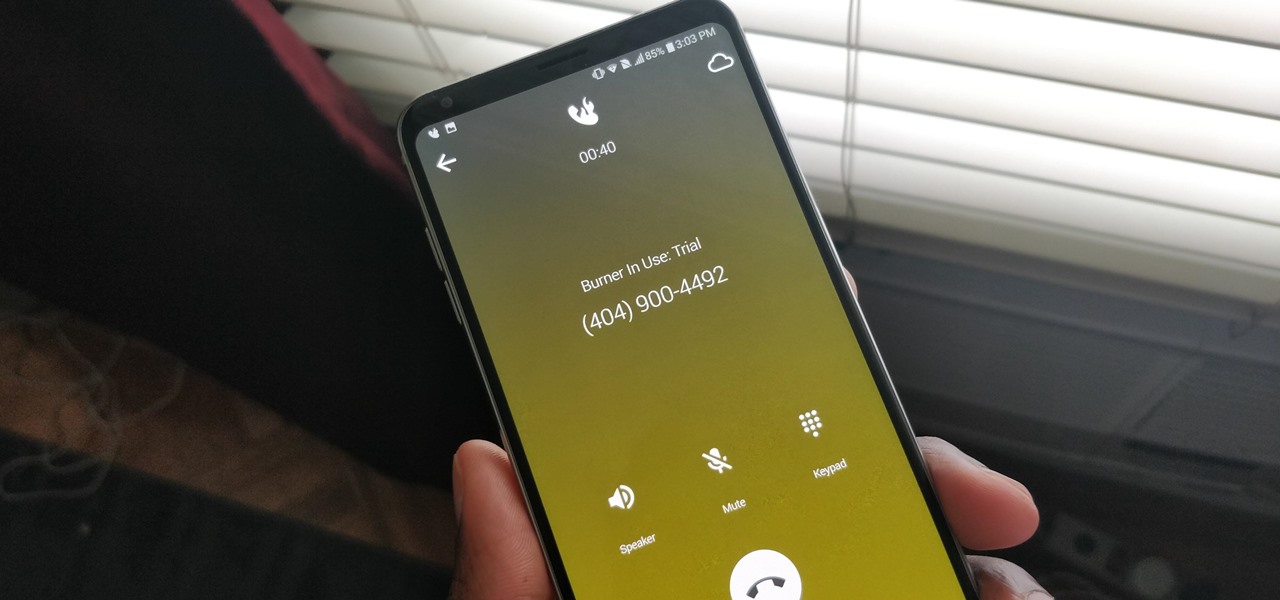
A burner number isn't just for criminals and cheating spouses. In this digital world, with many of our interactions being conducted online, a throwaway phone number acts as a buffer — it lets you enjoy the web without having to give out your personal information, such as real name or phone number.

Over the years, the internet has become a dangerous place. As its popularity has increased, it has attracted more hackers looking to make a quick buck. However, as our dependency on the web grows, it becomes increasingly difficult to sever all ties. This means we have to protect one of our weakest points, the password.

Apple has finally given us a decent file manager in iOS 11. The new "Files" app replaces the not-very-old iCloud Drive app that appeared in iOS 9, but you can still access your iCloud Drive files in the new Files app, as well as files from third-party cloud services. A nice improvement, right?

One of the most popular things to do on Snapchat is to earn a Snapstreak. This occurs when you and one other friend have sent snaps (not chatted) to each other within 24 hours for at least three consecutive days. One you've passed the three-day mark, then you and your friend will receive a fire emoji next to your names.

Backdoors are convenient to leave behind once you've already found a way into a server, and they can come in handy for a variety of reasons. They're good for developers who want a quick way into machines they're working on, or for systems administrators who want similar access. Of course, backdoors are also a hacker's best friend, and can be added in a variety of ways. One good tool for doing this is Weevely, which uses a snippet of PHP code.

With the release of the Mirai source code, botnets are back in a big way. In the early days of botnets, zombies (infected hosts) would report to IRC (Internet Relay Chat) channels for CNC (command and control) instructions. Modern botnets have evolved, but they continue to use the same concepts as their predecessors.

Apple Pay has been available to use in stores, as well as in select apps and websites, ever since its first appearance in iOS 8.1. Now, with iOS 12, there are currently 13 different iPhone models that support Apple Pay functionality without the use of an Apple Watch, and the list of partnered stores that accept Apple Pay has only grown. Here's our always-up-to-date list to keep you in the know.

Welcome back, my budding hackers. So many of you are interested in hacking Wi-Fi that I have decided to revisit my Wi-Fi Hacking series with some updated and more in-depth material. I strongly suggest that you look at some of my earlier posts, such as "Getting Started with Terms and Technologies" and "Getting Started with the Aircrack-ng Suite of Wi-Fi Hacking Tools," before continuing here. If you're ready, you can also check out our updated 2017 buying guide here.

Welcome back, my novice hackers! The worst thing that can happen to any hacker is being detected by a security admin, the security technologies (IDS, firewall, etc.), or a forensic investigator.

Attention all veterans and active-duty military personnel—this coming Tuesday, November 11th, is Veterans Day, that time of year where the whole country thanks us for our service. For the most part, a simple thanks will do, but some folks like to go above and beyond and give us veterans free or discounted meals and discounts on merchandise in stores.

This year, like every year before it, Black Friday sales are starting earlier than ever. A lot of stores will be opening their doors as early as 5pm on Thanksgiving to get a head start on the madness (and it really is madness). As we've discussed in the past, one of the keys to emerging victorious on Black Friday is to plan, plan, plan. So, we've compiled some of the best deals in tech, gadgets and appliances to help you prepare for battle.

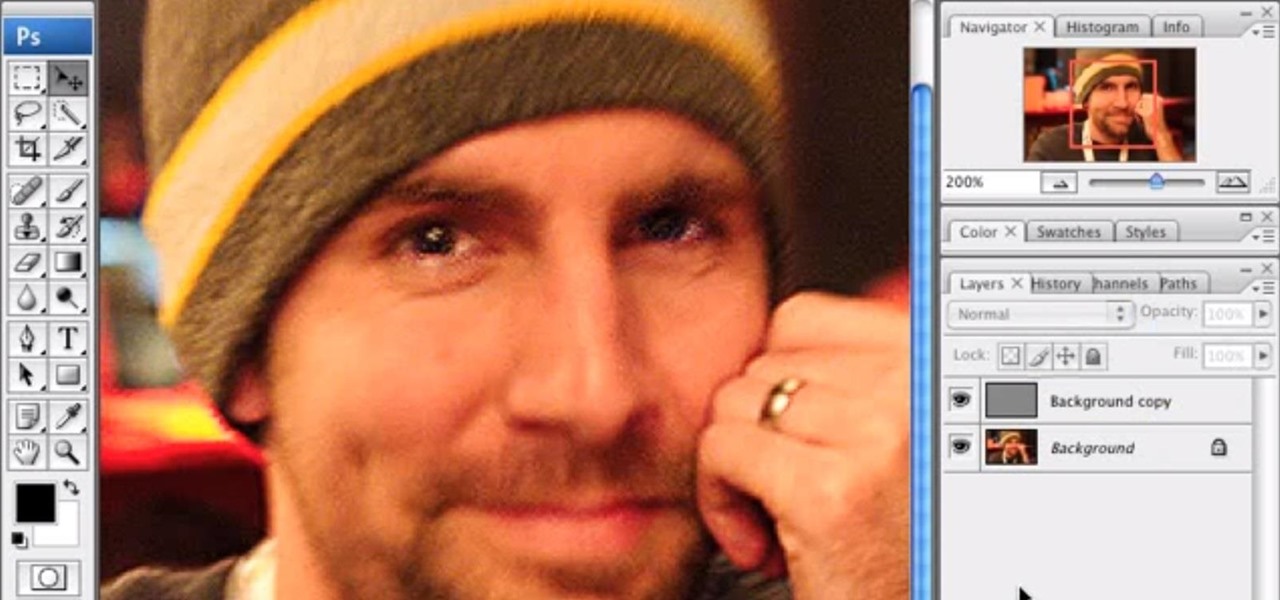
It's very easy to get a slightly blurry photograph due to a moving subject, camera shake, or just an incorrect auto-focus, but you don’t have to let that ruin an otherwise terrific picture. All it takes is a little finesse in Photoshop or another photo editing software. This guide covers sharpening a blurry image using Photoshop specifically.

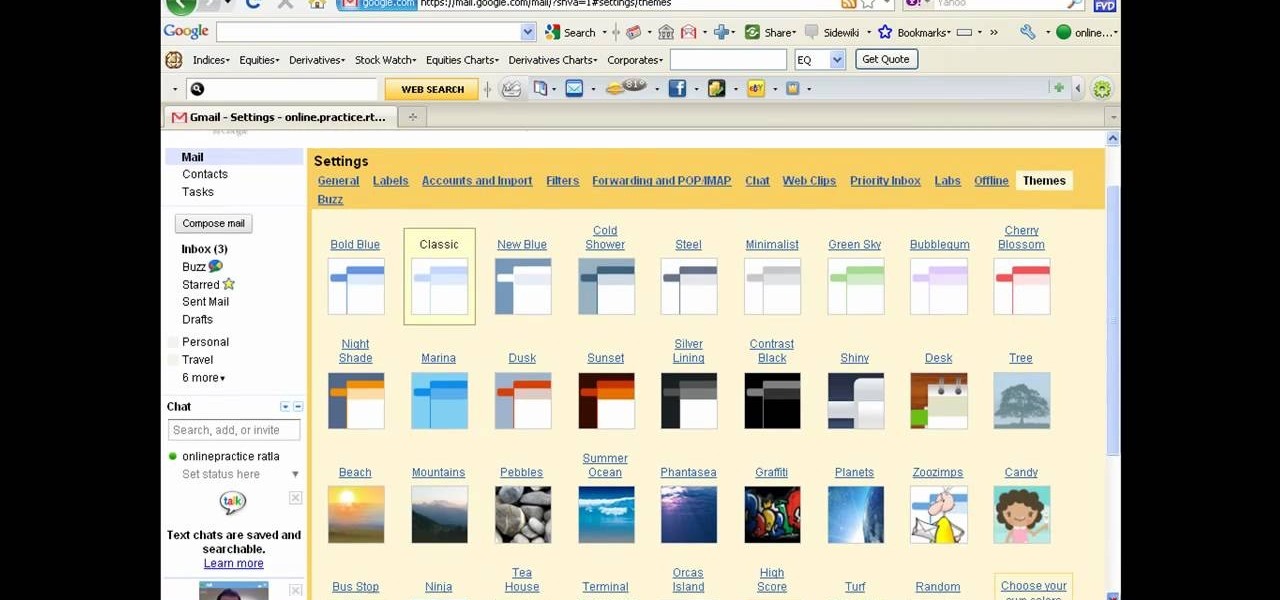
There a ways to personalize your Gmail experience, and one of those is picking personalized Gmail themes which make emailing funner. But if you're not sure what kind of theme you want to use from all the available Gmail theme choices, there's an option called "Random" which provides you a random theme based on your geographical location, and will change when in a different location.

Want to make a Bloody Jack like a champion bartender? This clip will show you how it's done. With the proper technique, mixing the perfect drink can be easy. So easy, in fact, that this free video bartenders' guide can present an overview of the process in about a minute's time. For more information, including a full list of ingredients and complete instructions on how to mix this drink yourself, take a look.

In this video tutorial, viewers learn how to enable hidden God Mode in Windows Vista 32 bit and 7. This option does not work on Windows Vista 64 bit. Begin by right-clicking on the desktop. Then go to New and select Folder. Now name the folder to a desired name and paste this code behind it: .{ED7BA470-8E54-465E-825C-99712043E01C}. Users will now have a full list of control options for their computer system. This video will benefit those viewers who use Windows 7 and Vista, and would like to ...

In this video, Rick Pin teaches us how to measure the clutch fork pedal travel in a Saturn S series. First, remove the air box and the resonator box from the vehicle. Also remove the duct work from the vehicle and set aside. Once these are removed, you will be able to see the plate cylinder underneath where the air box was. To measure the fork travel, us a piece of wire with tape on it that has measurements listed. Push down on the clutch travel as you do this, then remove the wire and you wi...

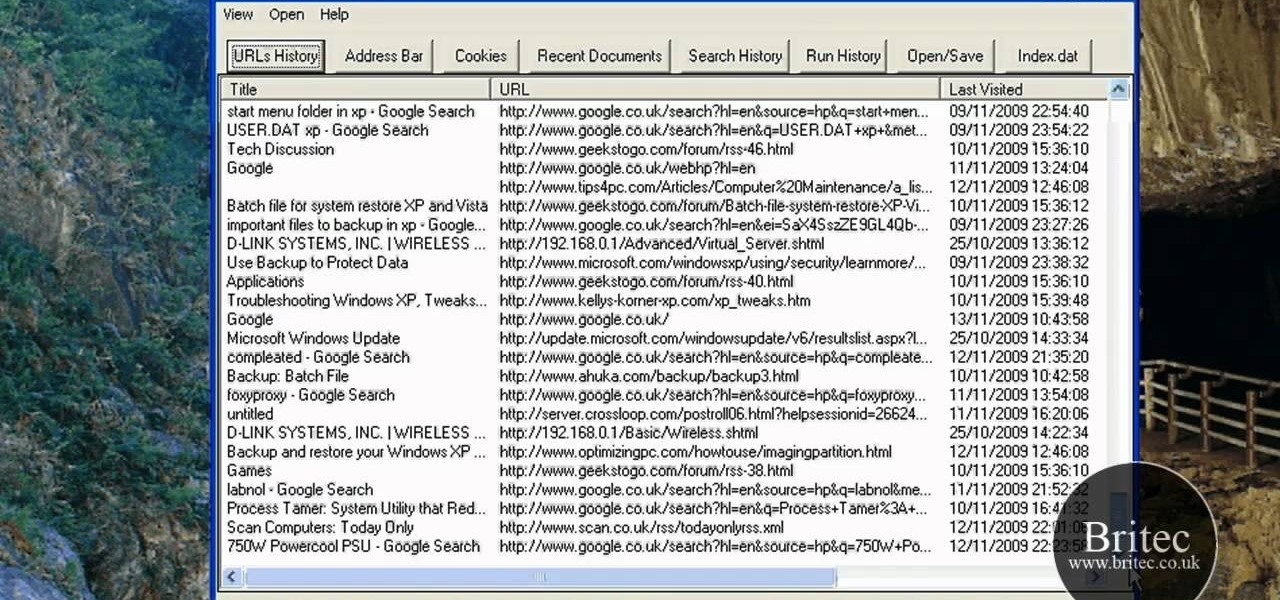
Interested in reading the list of web addresses in an index.dat file on a Microsoft Windows computer? This clip will teach you everything you'll need to know. With WinSpy, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over two minutes. For more information, including detailed, step-by-step instructions, take a look.

Want to make a Special K like a champion bartender? This clip will show you how it's done. With the proper technique, mixing the perfect drink can be easy. So easy, in fact, that this free video bartenders' guide can present an overview of the process in about a minute's time. For more information, including a full list of ingredients and complete instructions on how to mix this drink yourself, take a look.

This video tutorial is in the Computers & Programming category where you will learn how to secure your wireless internet connection. If you don't secure your wireless internet connection you are allowing others to enter in to your network. Open the set up CD and first change the network name from the default name to anything that you like. For this go to step 3 of 'naming your network', type in your network name and click 'next'. Then you enable security on the network by choosing 'WPA2'. Nex...

In this tutorial, we learn how to remove the ads from Spotify. First, you will need a proxy, which you can get from the website: Proxylist. Just simply click on a free proxy once you get to the site, then write down the proxy and port. Next, go to edit, then preferences. After this, change the auto-detect to https, then put the proxy next to the box that says "host". Next, type in the port next to where it says "port", then click on the "apply" button listed at the bottom of this window. Now ...

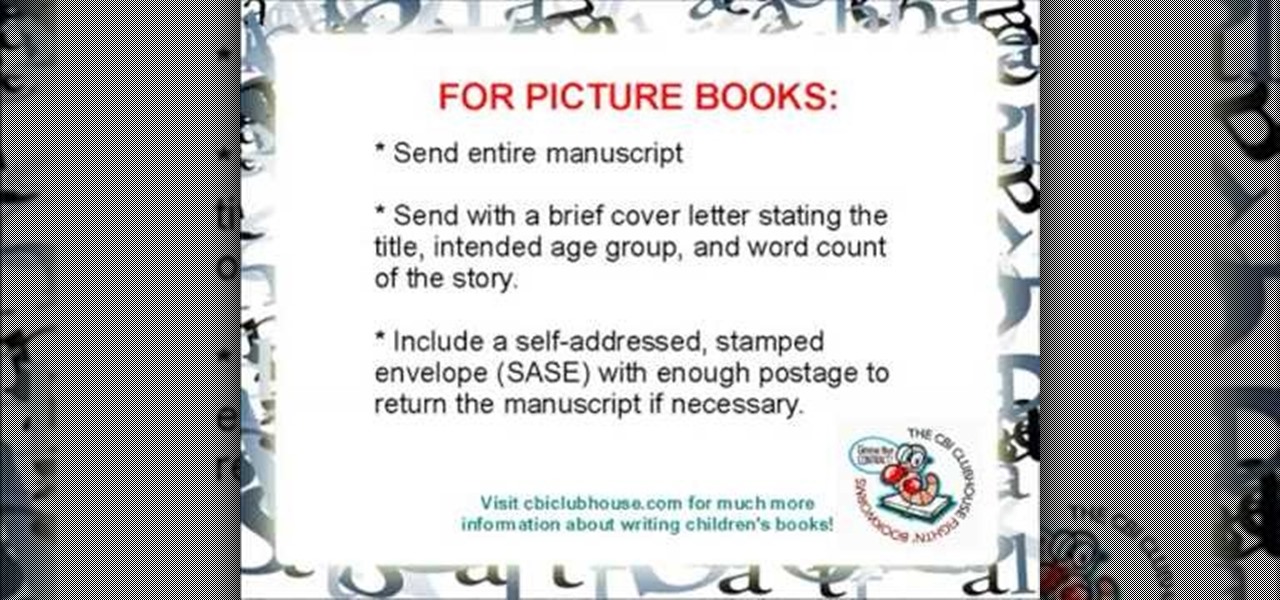
In this video, we learn how to submit a children's book manuscript to publishers. First, you will want to type your manuscript oh white paper and make sure it's double spaced and indented at the beginning of each paragraph. Use one inch margins on each side as well. Make sure the pages are number consecutively and your name, address, phone number, and e-mail are listed on the cover page. Don't break the text up and don't include pictures unless you're a professional illustrator. When you are ...

In this video, we learn how to upload Wordpress files using Filezilla. Before you get started, you will need to know the host, username, and password for your domain name. After this, click the quick connect button to connect to your server. The left hand side will show the local files on your server. Look in the root directory of your server and right click, then choose "create directory". Now, click on the plus sign to see a blog sub directory. Next, find where you downloaded Wordpress onto...

In this video tutorial, viewers learn how to uninstall the video card drivers on a Windows computer. Begin by clicking on the Start menu. Then right-click on My Computer and select Properties. Now click on the Hardware tab and click on Device Manager. In the list, click on Display Doctors and select the desired video card. Now double-click on the video card and select the Driver tab. Finally, click on Uninstall and follow the process to remove the drive. This video will benefit those viewers ...

In this tutorial, we learn how to eject devices from the use of the terminal for Mac. First, go to the terminal of your computer where you will see a notepad sort of page. Next, type in "df" and then press return. You will now see a list displaying processes on your computer. On the bottom will be your public zoning device, which is your USB device. Next, type in "hdiutil eject -force (the code under "mounted on)- volumes-publiczone". This is not case sensitive, but don't forget or add in any...

In this video tutorial, viewers learn how to speed up the Windows XP Start menu. Begin by clicking on the Start menu and select the Run program. Then type in "regedit" and click on OK. Now select H KEY_CURRENT_USER, go to Control Panel and click on Desktop. On the right side of the window, scroll down the list to find Menu Show Delay. Double-click on it, change the value to 0 and click OK. This video will benefit those viewers who use a Windows computer, and would like to learn how to speed u...

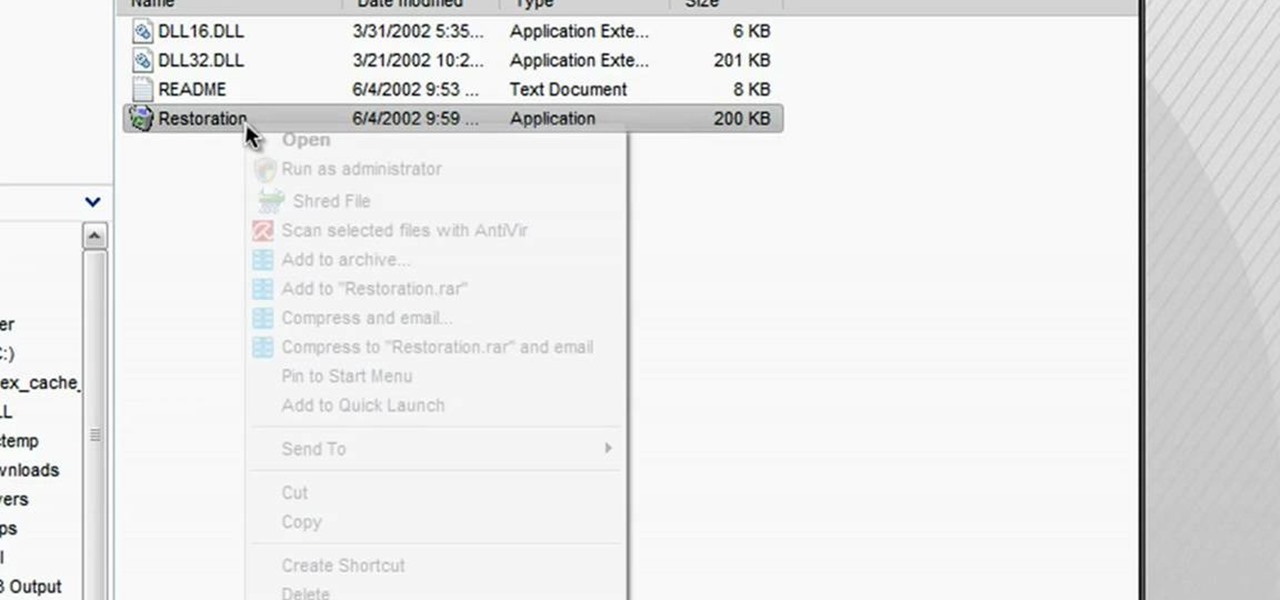
In this tutorial, we learn how to restore deleted files. This is how to retrieve them after you have deleted them from the recycle bin. First, load your internet browser and open up snap files and download it to your browser. Unzip the file from your desktop and load it to your C drive. When it's done, right click on it and click "run as administrator". Under the "drives" section, click on the drive then type in the name of the file you deleted as well as clicking the check marks on both boxe...

Everyone gets bad body odor at some point, whether it's because you are genetically predisposed (sorry) or because you just finished running two miles for gym class. But slathering on deodorant, which contains a miles-long list of petrochemicals and other cancer-causing paraphernalia, is probably not the safest choice for your well being.

So, you're browsing the web on your iPhone using Safari, and you come across a picture you really want to keep forever and ever… what do you do? You can save it directly to your phone! But how do you download that web image? Best Buy has answers. The Best Buy Mobile team explains how simple it is to save web images from Safari on your Apple iPhone.

This tutorial gives a start to finish explanation of how to make an Internet Wi-Fi router with Windows Vista. With real time computer screen video and narrative, it is easy to follow along at home.

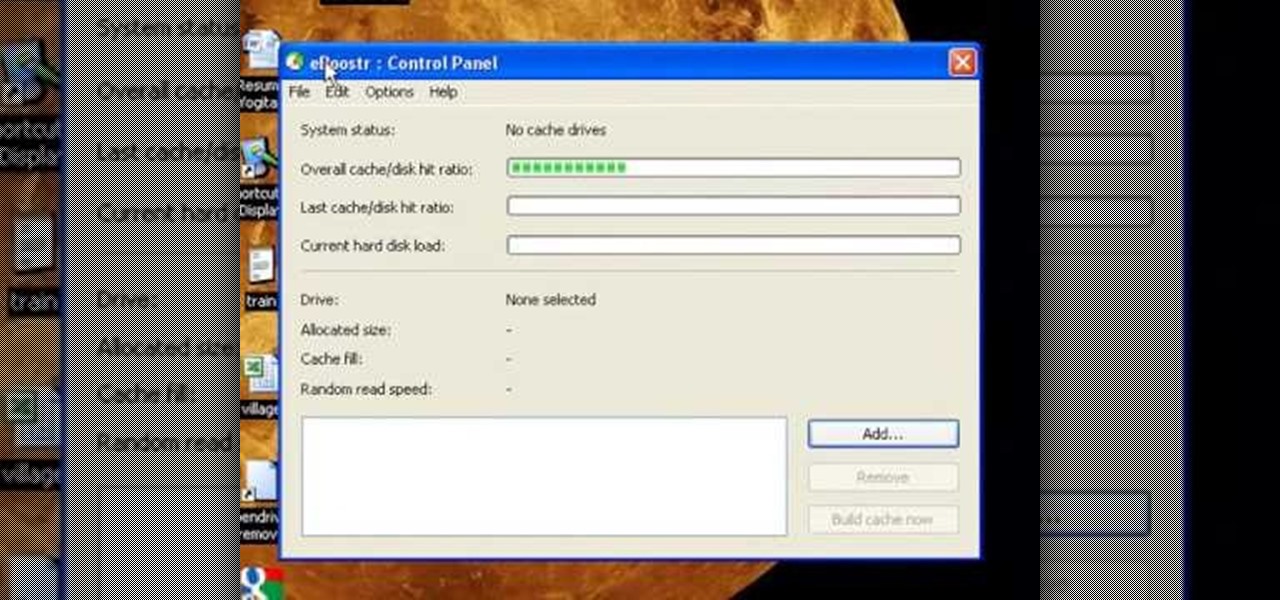
To use a USB (flash drive) pen drive as RAM on your computer. First open the drive by clicking on "My Computer" then double clicking on the drive. Next open the eBoostr control panel. When the control panel dialogue box opens click "Add..." this will open the "Add cache device" dialogue box. Once this dialogue is open click the select device drop-down menu and select your removable USB drive (pen drive) from the list. Then click "OK" and wait for the "allocating cache file..." process to comp...

Chef John from foodwishes.com shares his recipe for Argentinian Chimichurri sauce and is assisted by his wife Michelle. He lists the ingredients as garlic, spices, and herbs including italian parsley, cilantro, and oregano. Chef John suggests shaving the leaves of the herbs off the stems and then throwing them into a blender with all his spices, oil, and vinegar. Chef John uses a long spatula to push the herbs down. He purees the sauce slowly in the blender, scraping down the sides of the ble...

In this Software video tutorial you will learn how to mount an image using Daemon Tools Lite. This software takes many different types files and puts them on a virtual DVD drive. Go to www.daemon-tools.cc and download the Daemon Tools Lite program. You then install it. After that double click on the icon on your desktop and it will appear on the bottom right hand corner of the screen. It will say Daemon Tools and the version. Right click > virtual Cd/DVD ROM. To mount an image, click on ‘mo...

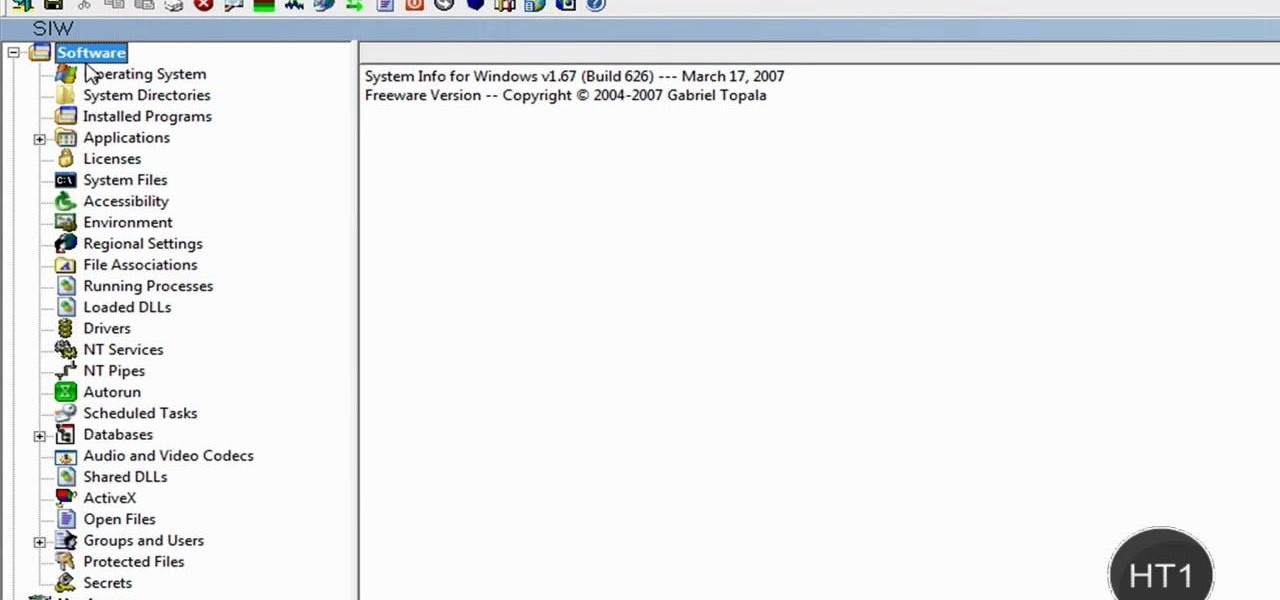
How to find out information / details about your computer? To find out the information about your computer, you need to download software from the website PC World. The following are the steps to download the software:

Chuck Cook, listed as one of the top 100 golf instructor's by Golf Magazine is going to cure your pull shot by making just a simple change in your alignment. The most common mistakes occur when people may have great swings but line up to far to the left, or line up to far to the right and over compensate with the swing. To fix this common problem there is a simple solution just follow the videos step by step instructions by using two other clubs to create a shoot to line up your shot. If prac...

You start the game from the Kongregate website and then run Cheat Engine. Look for your browser in the Process list. It could be Firefox, Chrome or Internet Explorer. Set the value type to Array of bytes. Then check the Hex box above and use the values from the description to apply the effects there, like no mp drain, chain doesn't end on hit and unlimited chain time. After you've searched for the value, click New scan and then add it from the left to the bottom by double clicking it. To acti...

The video shows users how to change the boot sequence in a computer with an older AMI (American Megatrends, Inc.) BIOS to boot from the CD/DVD drive. This is required, for instance, if you need to reinstall an operating system, or fix a corrupted windows installation by running Windows Setup from the installation CD. Users should first enter the BIOS setup by pressing the delete key when prompted shortly after powering the computer on. Once the Bios Setup screen has loaded, users may navigate...

FROMAN1115 teaches you how to change your NAT type to Open on your PlayStation 3. On the PlayStation 3, go to Settings-Network Settings-Settings and Connection Status List and write down your IP. Go to your PC and start your internet browser. Type in 192.168.1.1. This will bring up the router settings page. Go to Applications and games and then DMZ. Check the first box that says Enabled. Enter your IP address below and click ok. Your settings have been saved and you can enter a new internet m...

This video explains how to install and uninstall applications on the iPhone or iPod touch. You click on the installer icon on the iPhone or iPod touch and it provides a list of installable applications that are available in the app store. You can then scroll through these applications and select any application that you want to install on your device. Once you have selected the application, you just click on the install button at the bottom of the screen and the application will be installed ...