Deafall traps are the type of trap most familiar to the American public, largely due to the efforts of Elmer Fudd to catch Bugs Bunny on Looney Tunes. In real life, they tend to work quite a bit better than they did on the show. In this video, Wilderness Outfitters presenter Crier demonstrates how to construct one type of deadfall trap, the Ojibwa Deadfall. Knowing how to make traps like this will make you much are able to survive if you are stranded in the wilderness with no food.

This video shows us the method to find the percent sign on Blackberry. The first step involves going to a place on the Blackberry where text can be inserted. This place is ideal for inserting a % sign. Look in the keypad carefully. There are various keys in it. Search for the key named 'SYM'. SYM stands for symbol. This key is helpful in typing various symbols in the text to be entered through the keypad. When the 'SYM' key is pressed, it opens a window containing various symbols. The % sign ...
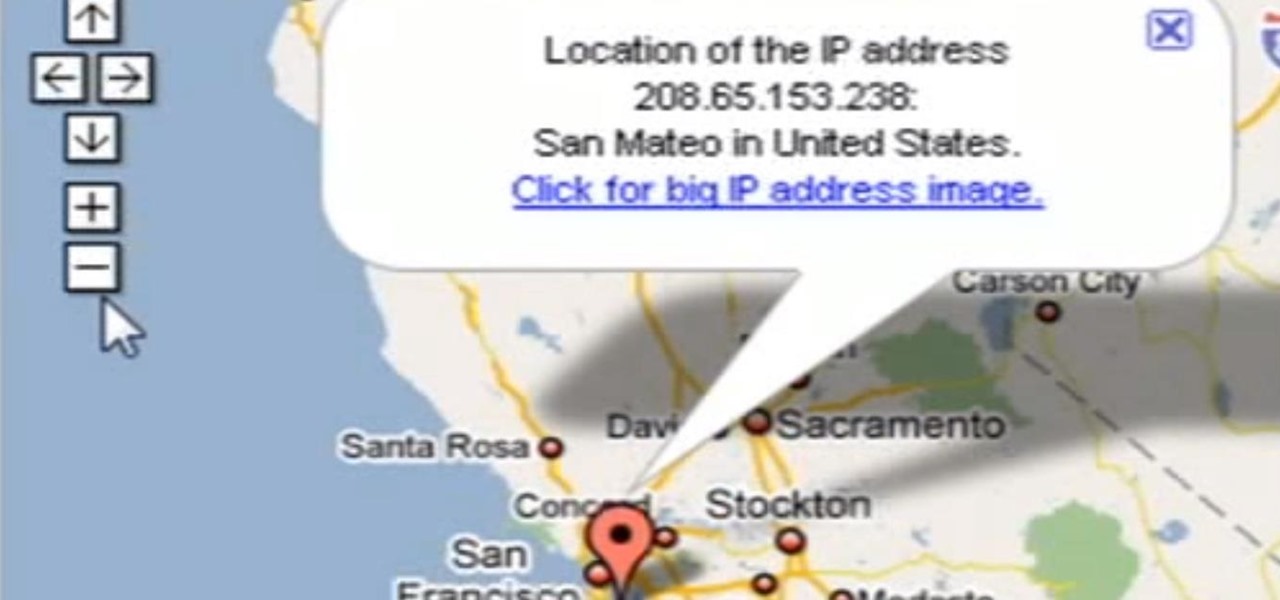
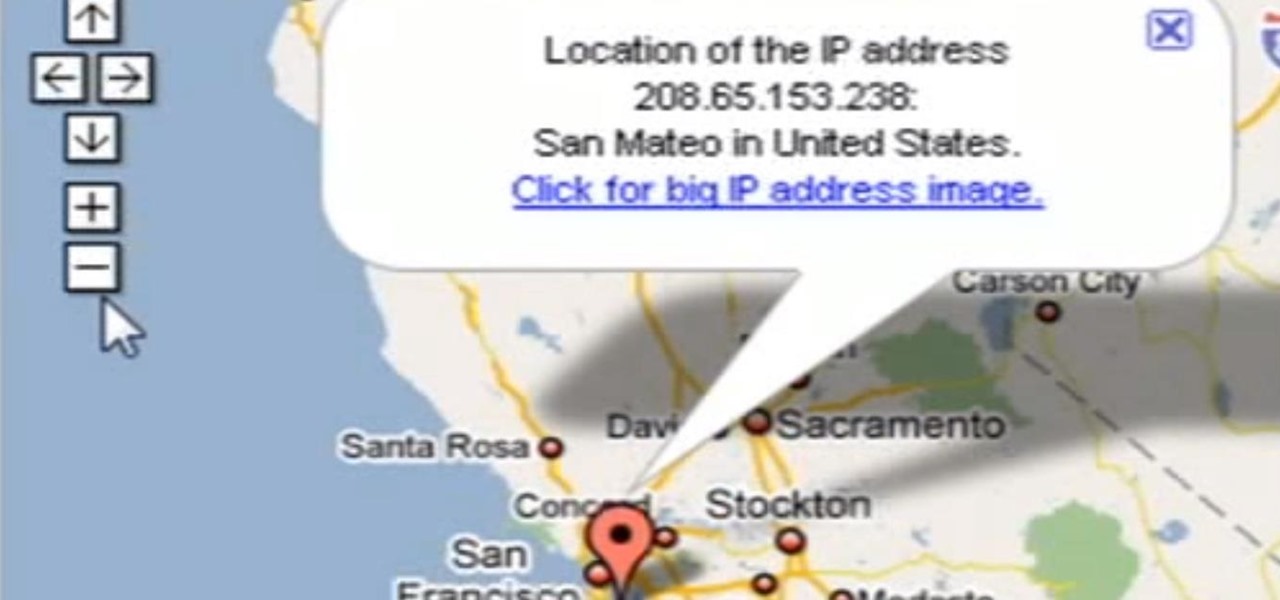
Need help tracing an IP address to a location? Well, Tinkernut has a clear and effect way to help out.
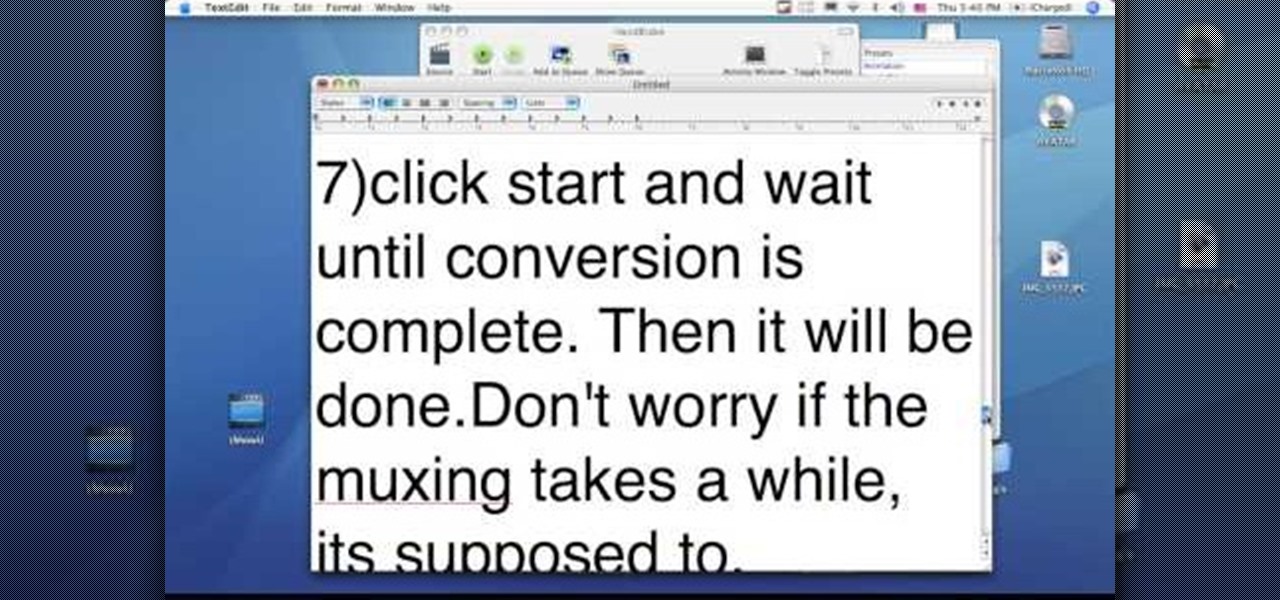
This video tutorial from dproxisback presents how to download and install Handbrake DVD ripping tool.To avoid installation problems, carefully choose application version for each type of computer and operating system.Open your internet browser and visit http://handbrake.fr/?article=download web page.Choose correct version for your type of operating system (MacOS, Linux, Windows).Download and install the application. Run Handbrake once it's installed.Click File-Select Source. Browse for your f...

Whether you are protecting your children or hiding personal information, there are ways to block unwanted websites from your computer. Follow this tutorial and learn how to accomplish this on a Windows PC easily.

First download Paint.net. Save the YouTube logo on your computer and then open it using Paint.net. Press S and select the "You" from YouTube, once selected press delete. Now press F and choose the white color, pain the deleted area to fill it with the white color. Press T to select the text tool, select the font Arial Narrow and choose the font size 144, press ctrl+shift+N to create a new layer. Now click on where you want to the text appears and type anything you want. Go to File and Save As...

How to Install Installous on any iPhone or iPod Touch? Learn about it in this video tutorial in the Electronics category. For this purpose you will need a jailbroken iPod Touch or iPhone. First go to Cydia and open it. It takes a little time to load. Go to manage -> source -> edit -> add. Then type in this source: Cydia.touch-mania.com. Download and install it. Now you go to search and type in Installous in the search box. Download it and go back to your springboard. Open it up, search for an...

In this video the instructor shows how to hide any kind of file in a .Jpeg image file. To do this take the image in a new folder. Go to start button and then to run. Type cmd in the run and hit enter to open the command prompt. Now browse to the directory that contains the picture and also the file that you want to store using the CD command. Type the command to create our required file as shown in the video. Now a new file will be created that contains your image as well as the file that you...

First, on your computer access your command prompt and type in ipconfig. Find the line called default gateway and write it down for later. Type your default gateway into your internet address bar and it will bring up your router setup page. Find your upnp and enable it, this will open your NAT. Start your XBox 360 and go to system settings on your XBox dashboard, go down to network settings and test your connection. Next go to IP settings then manual then IP settings. You want to change your ...

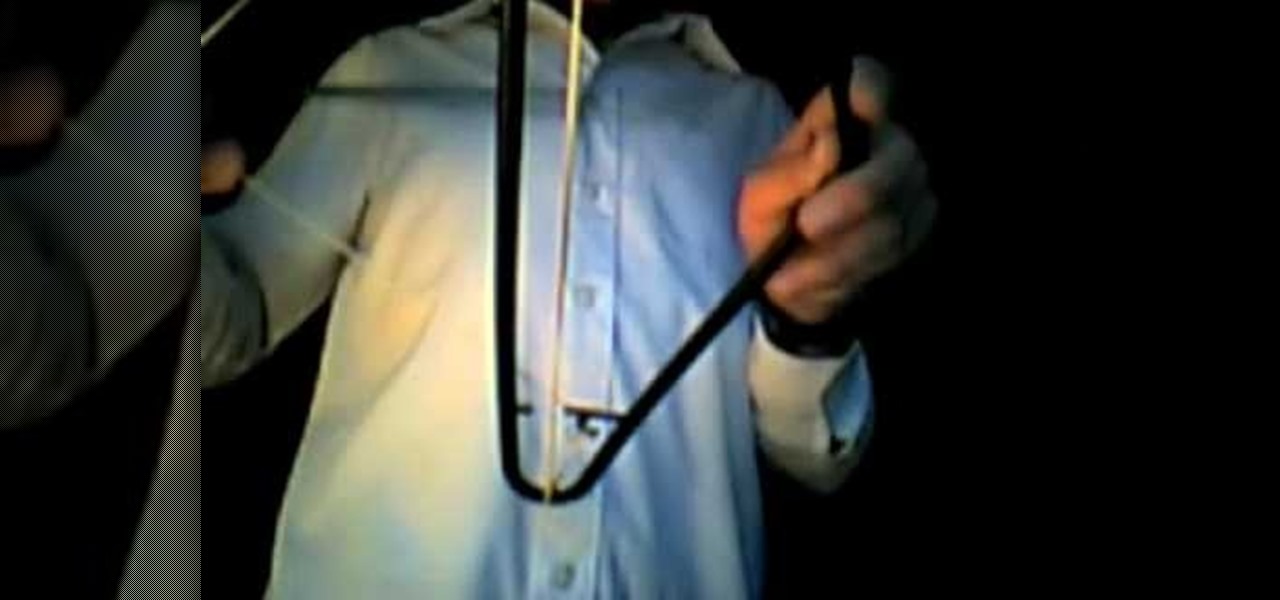
In this video, Lusitano 9514 will show you how to make a homemade rubber band bow and arrow out of common household items. To do it, you will only need a basic plastic coat hanger, a long rubber band, and some kind of a stick (for the "arrow"), all of which are quite inexpensive. Watch Lusitano 9514 demonstrate for you exactly how to make the bow and arrow, and show how it works. You will also learn tips and tricks, such as what materials make better ammunition, and what kind of "arrows" are ...

In that video you learn how to hack ikariam.

There is a wide rage of variables to consider when considering getting breast implants. This includes everything from if you are a good candidate, the type of implants, the size of the implants, the type of surgery, the size and the possible side-effects.

This walk-through video tutorial shows you how to find out your IP address for XBox live. First press the start button and search for run as shown, click the result, bring up the dialog and type in the given command to open the command prompt window. Type the command in the given window and hit enter. The number that appears is your IP address, use it as the key for XBox Live. In the case of XBox 360, it automatically detects it.

Epson sells many different digital imaging products, including ink jet printers and all-in-ones, digital photo printers, multimedia projectors for business, education, and home entertainment, scanners, digital photo viewers, professional imaging/wide format printers, and more. Check out this video to learn how useful and versatile your new Epson Artisan 810 all-in-one printer can be.

Byrd Designs Hair Accessories and Jewelry brings you this video tutorial on how to style your hair in a French Twist updo. This simple updo works in all types of hair.

A bean salad is a great way to get the health benefits from beans. Beans are a good source of protein, they're full of fiber and are said to "pull" cholesterol out of your body.

When shooting a shotgun, you don't really have to aim--just point and shoot. Whether you hit what you're shooting at depends on how well you did your homework. "Patterning" your shotgun allows you to choose exactly the right brand of shells, size and type of shot and type of choke required for the game you're pursuing. Set yourself up 40 yards from a 30-inch circle target, and bring along several brands of shells in various shot sizes. Use some form of rest like sandbags on a table or a rolle...

This Scooby's Workshop video shows proper form of the incline dumbbell fly exercise for pecs. Fly type exercises have done far more for my pec development than the pushing type exercises. In doing flys, make sure that your arms do NOT go behind the plane of your body as this puts too much stress on the shoulder joint. If you don't have a incline bench, you can make one as I have done here by tying a 2x8 securely to a coffee table. This exercise is best done with a spotter for safety, if you m...

How to fix those loose and jiggly cupboard doors on your kitchen or bathroom cabinets. For this repair, you're going to need a flat head or phillips head screwdriver. Now, the type of screwdriver you're going to need is really dependent on the type of screw you have holding your cabinet door to your cabinet. We're going to use a phillips head screwdriver because, as you can see here, the top of our screw head is shaped like that of a crosshair. If it were shaped like one long groove in a stra...

Waking up your Apple Watch to see "your heart has shown signs of an irregular rhythm suggestive of atrial fibrillation" might come as a shock. While your watch can send you warnings if it detects a fast or low heart rate, those messages are pretty vague, while the abnormal arrhythmia alert can downright scary. So what should you do if you receive one of these AFib notifications?

The rumors are still hot that Apple might include an 18-watt USB Type-C power adapter with the upcoming iPhone lineup so that there's fast-charging capability right out of the box. Leaked photos have surfaced that substantiate this rumor, though, they could also be fake. But how would ditching the old-style 5-watt USB Type-A power cube affect you if it's true?

Your Instagram bio could always be used to link to other websites or profiles or just to show off your witty personality. Now, you also have the ability to use this section to tag other Instagram accounts as well as add tappable hashtags. Whether you want to link out to your best friend, company, or the latest trend in your city — if it has a profile name or tag, it can be in your bio.

Configuring onion services for the first time can be tricky. A surprising number of system administrators make seemingly trivial mistakes that ultimately lead to catastrophic cases of de-anonymizing supposedly anonymous sites on the dark web. OnionScan is a tool designed to identify common misconfigurations in onion services and aid us in understanding how to fix them.

PowerShell Empire is an amazing framework that is widely used by penetration testers for exploiting Microsoft Windows hosts. In our previous guide, we discussed why and when it's important to use, as well as some general info on listeners, stagers, agents, and modules. Now, we will actually explore setting up listeners and generating a stager.

While hackers adore the command line, working with the GUI (graphical user interface) of an operating system has some advantages. This is especially true when it comes to post-exploitation. When we can control the mouse and keyboard of a remote computer, we can truly say we have complete control over the device. Today, I'm going to introduce to you the PyAutoGUI module, which does just that, and just how much fun you can have with it!

PowerShell Empire is a post-exploitation framework for computers and servers running Microsoft Windows, Windows Server operating systems, or both. In these tutorials, we will be exploring everything from how to install Powershell Empire to how to snoop around a target's computer without the antivirus software knowing about it. If we are lucky, we might even be able to obtain domain administrator credentials and own the whole network.

Typing out thirty hashtags on Instagram is always such an annoying process. Figuring out the best hashtags to use to get more likes is also tricky. You can't just keep copying and pasting the same hashtags on every post — that's like attacking the same tribe every time. You got to diversify, which takes a lot of conscious effort to be on top of the current best hashtags to use.

Dramatic new research may change the fate of the hundreds of people who wait for a kidney transplant every year. The study hinged on the ability to cure hepatitis C infections, a possibility that became a reality in 2014.

Kik is an extremely popular messaging app, but it has a few annoying features that we all just sort of put up with. You can't turn off read receipts, nor can you hide when you're typing, and the photos you take with Kik's camera show up differently than ones you send from your gallery app. At least a couple of these features should be subject to change, but they aren't — well, not without some tinkering.

As many as 700 species of bacteria live on our teeth and in our mouth, and just like the microbiomes inhabiting other parts of our bodies, they change in response to diseases and other health conditions.

Android is a highly customizable operating system. Sometimes, we use these capabilities to add core functionality or streamline the user experience, but there are other times when customization is just about having fun and making your smartphone's interface more enjoyable.

Google has added a number of new features in the latest update to Google Keyboard including a one-handed mode and a setting that lets you adjust the height of the keys. The update hasn't gone live on the Play Store yet, but you can download the APK right now for both 32-bit and 64-bit phones.

Welcome back, my novice hackers! As many of you know, recon is crucial to a successful hack/pentest. In most cases, hackers spend more time doing good reconnaissance than actually hacking. Without proper recon, you are simply guessing at what type of approach or exploit is going to work and, as a result, your time is wasted without any useful outcomes.

In my last tutorial, I talked about creating a virus inside of a Word Document in the scenario of a mass-mailer attack. In this post, however, I'm going to be covering creating a fake image or screenshot with a meterpreter backdoor hidden inside to be used in a similar scenario. Step 1: Creating the Virus

Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear that are not added to the Metasploit repository.

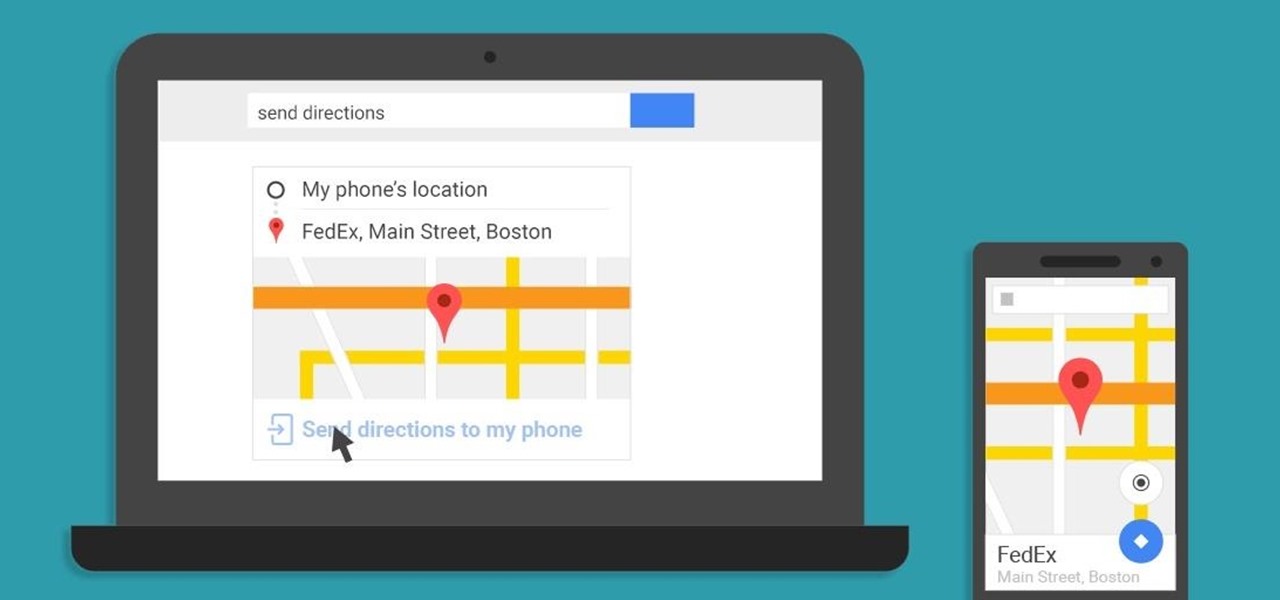
A set of cool new Android-related Google Search functions made their debut this week, which will allow you to locate your phone, send directions to your mobile device, set alarms and reminders, and send notes from any web browser.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

Hello Elite Hackers! Welcome to my 3rd Post, which explains how to hack any account like G-mail, Facebook, etc.

The Nexus 6 is one of the few devices on the market that sports a 1440p "QHD" display. This means that the amount of pixels displayed is higher than almost any other smartphone, which sounds great on the surface, but is not without its drawbacks.