Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

Can't decide between the Galaxy S4 or the Galaxy Note 2? There are advantages to both the Galaxy S4 or the Note 2, it all boils down to what your needs are such as screen size, battery life, and more.

We'll show you how to use an attachment for a power washer called a "Foamer" - you'll never hand wash a car or boat again!

Welcome back, my newbie hackers! Hackers often are associated with clandestine and illegal activity, but that is not necessarily always the case. Hackers are increasingly being used and employed for law enforcement, national security, and other legitimate purposes. In this installment, we will look at how a single hacker could save the world from nuclear annihilation.
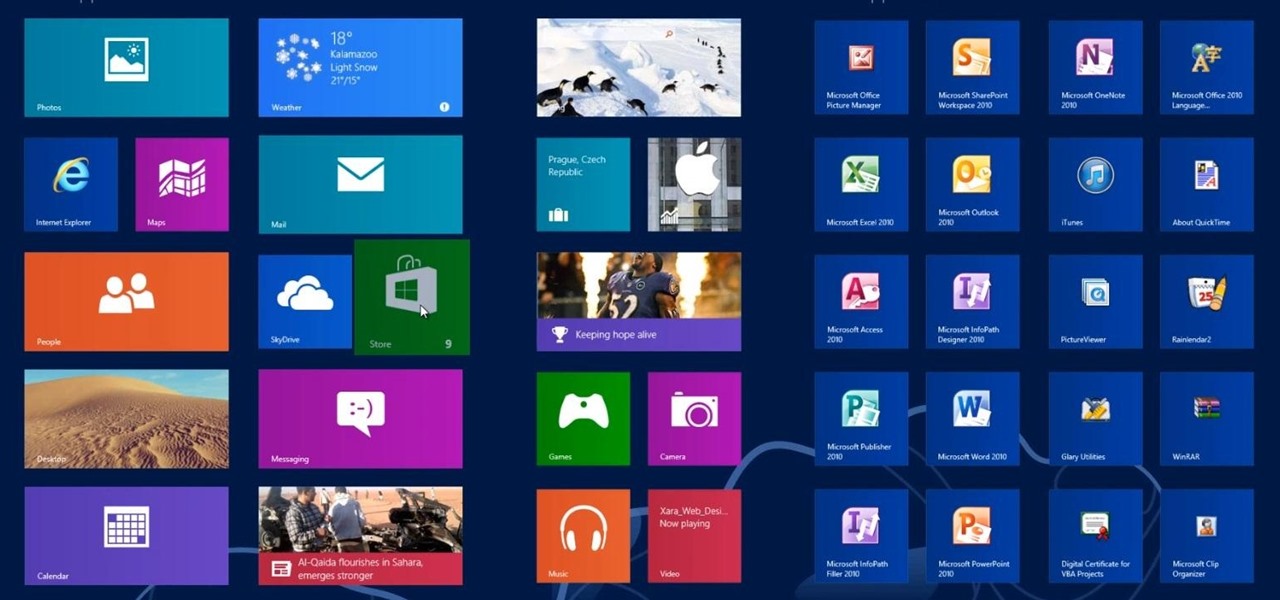
In this Windows 8 Tutorial you will learn how to search for application in the Windows 8 store. I know it can be a bit confusing for those who have just moved to the Windows 8 store on how to search for store applications in fact it took me like an hour to figure out how to search because all the visual cues were hidden away. However when you finish watching this Windows 8 tutorial you will see it is as easy as being able type on your keyboard to find applications in the Windows 8 store.

This Windows 8 tutorial, I will show you how to change the name of groups, and rearrange groups and applications in the Windows 8 start menu metro interface.

PRL, or Preferred Roaming List, basically tells your phone which towers to connect to first. Changing PRLs can improve reception and data speeds, and in some cases even give you access to corporate/test towers.

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.

In my last hack blog on crashing your roommates Win7 system, we started looking at client- side attacks. As promised, we will be looking at some more client-side attacks.

Automator is a built-in Mac utility found in Mac 10.4+ and can be used to convert a PDF file to text format.

Programs that run automatically every time you start your computer can slow down your boot time—or just be plain annoying. Many of these programs are rarely used and don't even need to be running for your computer to function properly. So, if you want to disable these auto-run programs and increase your computer's startup speed, here are a few ways you can do it in the new Windows 8.

Here's a video on how to deal with pedestrian crossings in England. It's to help all of you taking driving lessons in Nottingham and the surrounding area, and can be used before or in-between your training.

Gardening school is in session and Shirley is teaching the absolute basics, such as: what to wear, what tools to use, what is the difference between an annual, perennial, and biennial? What is a garden zone, and which one is yours? Class is in session, so spit out your gum and listen up. Time to learn Gardening 101.

In my first few articles, we focused on operating system hacks. These hacks have been primarily on older operating systems such as Windows XP, Windows Vista, and Windows Server 2003.

Until recently, brainwave-reading devices have pretty much only existed in science fiction. Sure, electroencephalography (EEG), the technology that powers these devices, has been used in medicine and psychiatry since the late 1800s, but diagnosing people's brains and reading their minds are two totally different things. The first EEG headsets available to the public were used mostly in gaming and even in fashion, but in the last few years, they've gotten a little more sophisticated.

The video shows you how to calculate capital budgeting with a Texas Instruments BA2+ financial calculator. Capital budgeting will help you determine cash flows for given investments for a certain number of years in the future, thus helping you determine if the investment is worthwhile. The buttons you will use are the CF (cashflows) button, the NPV (net present value) button, and the IRR (internal rate of return) button. The video uses the example of a $10,000 investment that will return $5,0...

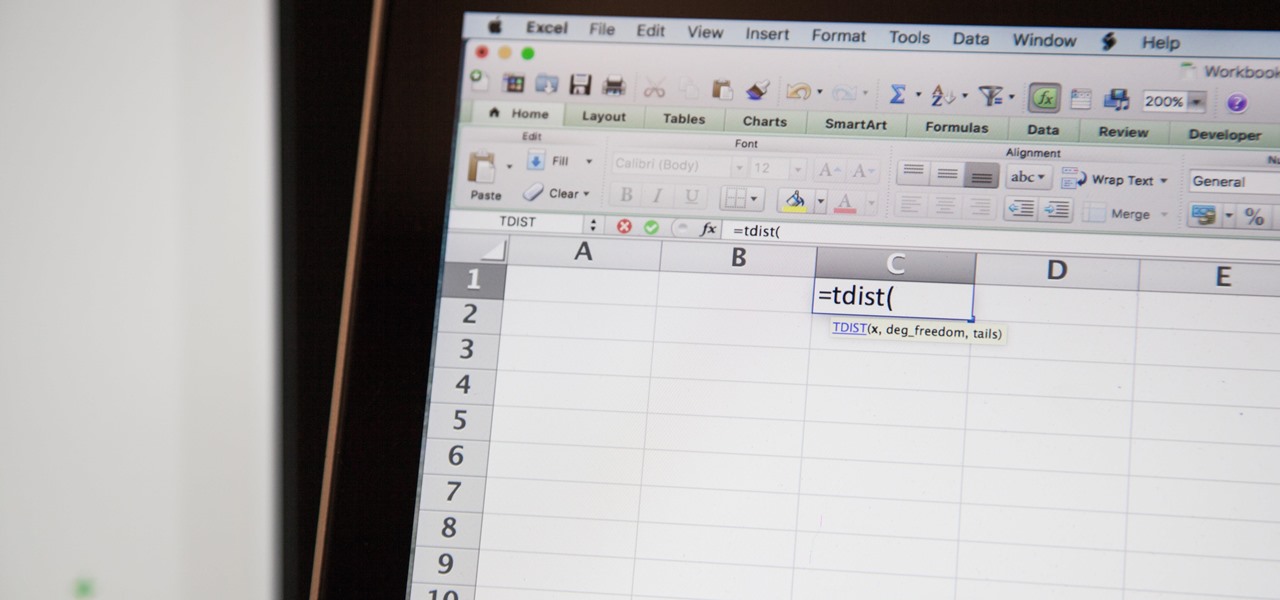
So you need to find the p-value for your hypothesis test. To do so, employ the spreadsheet program Microsoft Excel. Using a simple formula, you can easily determine the p-value for your tests and thereby conclude strong or weak support of the null hypothesis.

Start by clicking start and type regedit in the search box. Hit enter and when the screen opens go under hkey current user and click on control panel and then desktop. Under desktop go to menushowdelay. Under menushowdelay right click and then click modify. In the box that pops up set the value to zero and click ok. Then close the registry editor. Next you will want to download ram booster 2. 0. Once you have downloaded and installed the ram booster program you will want to edit your options....

There are three main types of exfoliates : the mechanical ones with the little scrubby beads; enzymatic ones made from the acids of fruits such as pineapple or papaya; and AHA’s (Alpha-hydroxy Acids).

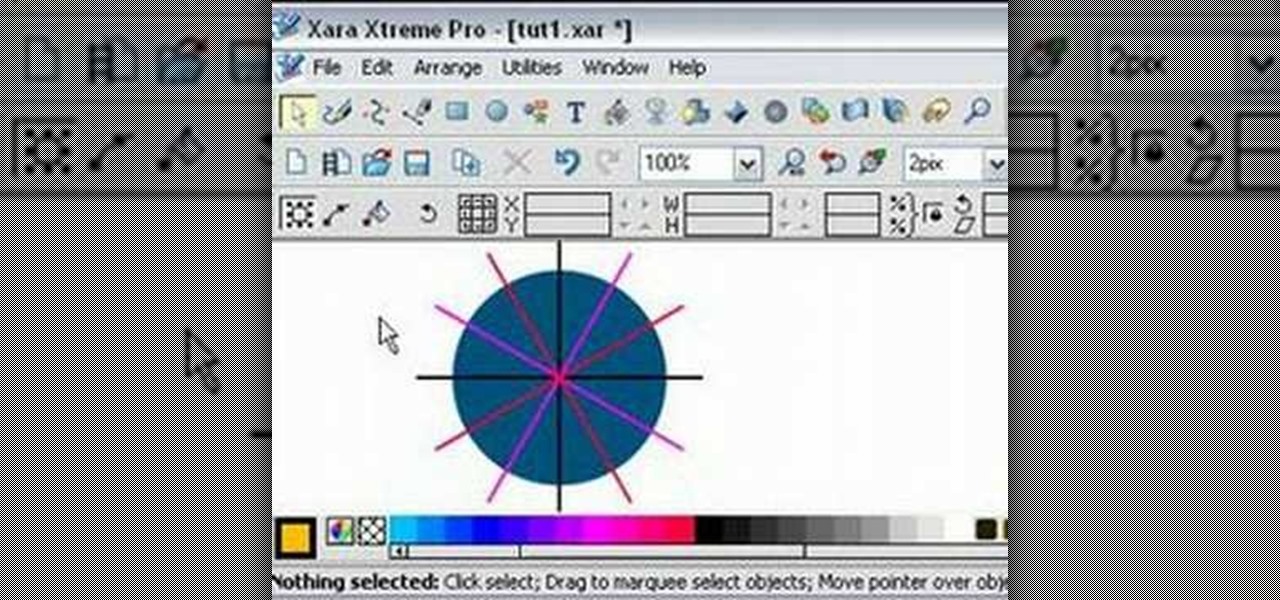
Learn how to split a circle into segments with Xara Xtreme. First select the shape editor tool. Drag the tool to the circle. The dialogue at the bottom communicates what steps to choose next. Holding the Ctrl key drag a straight line within the circle, click on the selector tool (yellow arrow on the left of the middle row) to enable the option of selecting. This saves 1 line on drawing layer 1 also and enables the marquee (flexible box) that you want to manipulate around the circle encasing t...

Taking up fishing anytime soon? The first thing you'll need to learn is how to bait a hook. Different types of bait require different methods of getting them onto the hook. Follow these steps.

Grow some of your own food by starting a vegetable garden. You'll eat better and save money. You Will Need

In this how to video, you will learn how to use Google Earth. First, download the program. Type in a city and state in the form. In the lower left, check street view to turn it on. Click the magnifying glass to zoom in. Some cities have 3d buildings. When you get really close, you will see cameras indicating street view images. If you get even closer, you will see spheres of the actual street view images. Click on it and the photo to get into the photo. In the upper right, you see controls to...

Everybody has a blood type. There are four types of blood in the ABO system: A, B, AB, and O. In this medical how-to video, learn how easy and important it is to find out what your blood type is. The procedure is very watch and find out.

Drummers have their choice of drum stick styles and grips and unless they know about them it is hard to know what is best for each. Learn about several of both from an expert drummer in this free video clip series.

There are a lot of things on your computer that can reveal information about you when you are surfing the Internet. If you are like me, then you will do anything to maintain your privacy and prevent those little leaks of information from happening. Here's a list of a few of the "threats" that can reveal information about you:

Update: this article is referring to the 1.9 pre-release beta version, which is now commonly referred to as 0.1.9, released in October of 2011.

This video is a must-see for any Dragon Age 2 player. It will teach you how to use a small glitch to get as much money and XP as you want, quickly and easily. It has not been patched, and will allow you to cheat your way through Dragon Age 2 as much as you see fit.

If you've ever seen something called ThinkPoint Antivirus on your computer, you have gotten one ofhte most widespread and infectious fake antivirus malware programs out there. To get it off your PC, follow the instructions below, or watch this video for an alternate method if this one doesn't work.

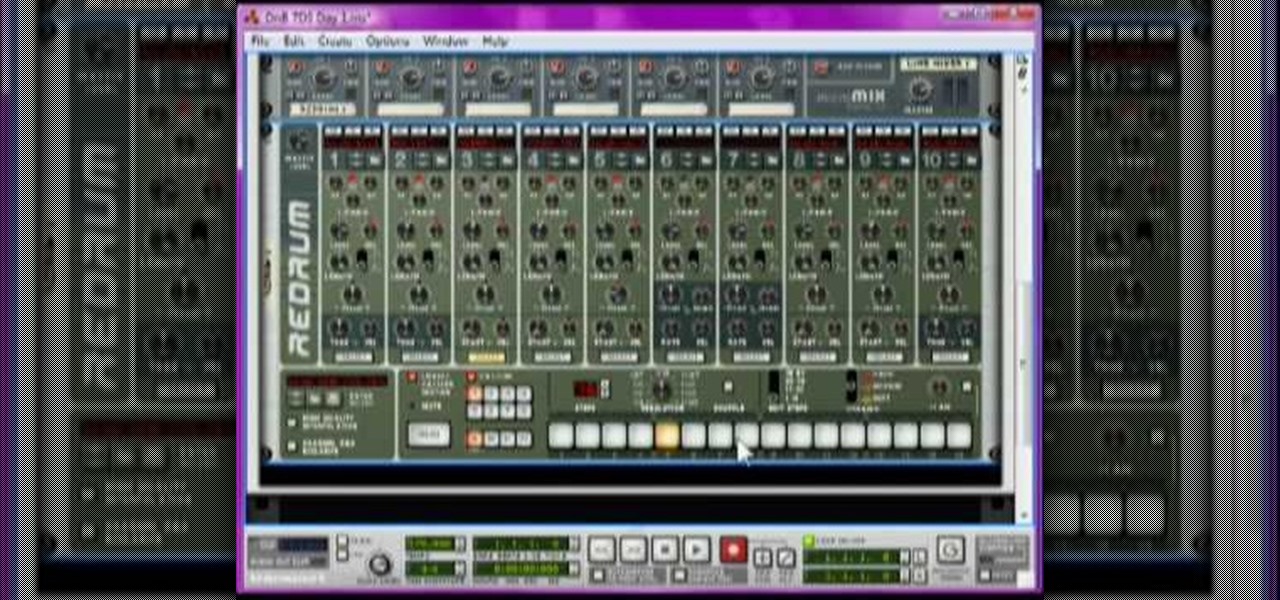
Drum and bass started off as a subgenre of Jungle and has since become one of the biggest types of electronic dance music on Earth. If you have Reason 4 and want to start producing drum and bass tracks, you've found the perfect place to start. This video will teach you how to make a DnB song from scratch over seven days using Reason 4.

Change object colors via ActionScript in Flash 8

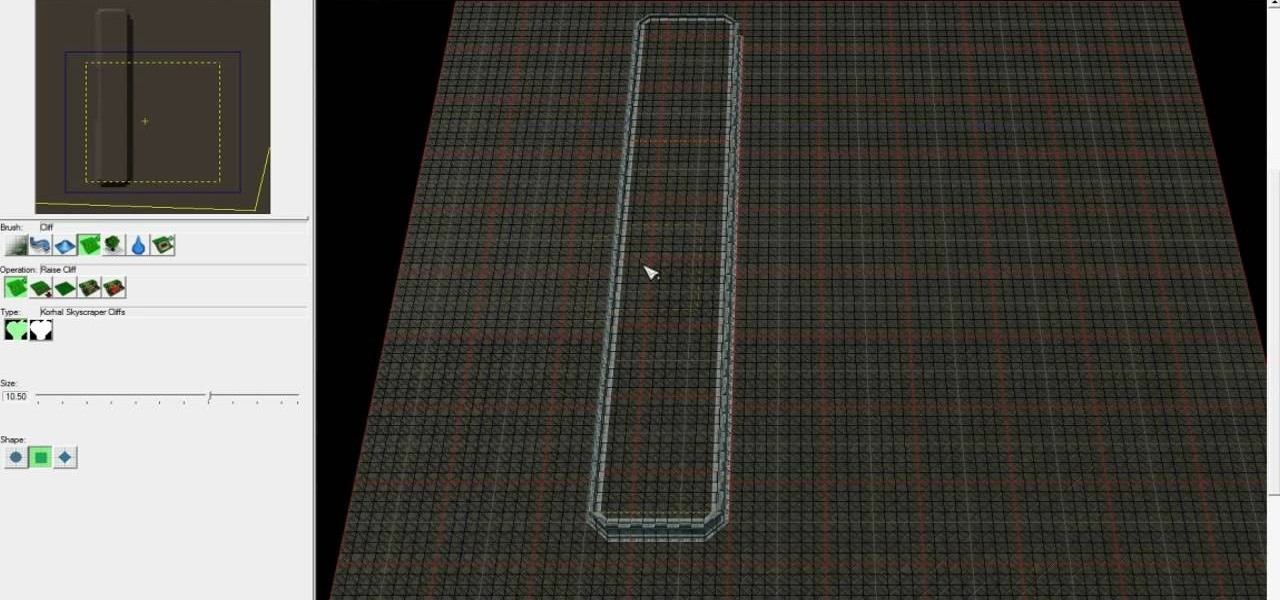
Starcraft 2, like it's predecessor before it, has a very robust level editor that allows you, the DIY modder, to create nearly any scenario within the bounds of the Starcraft 2 engine that you could imagine. We have compiled videos on how to do all sorts of fun things with it, from making RPG's and Tower Defense games to just making you dream Starcraft 2 level. This video will teach you how to create a complete and advanced Tower Defense game in the Starcraft 2 editor, allowing you to create ...

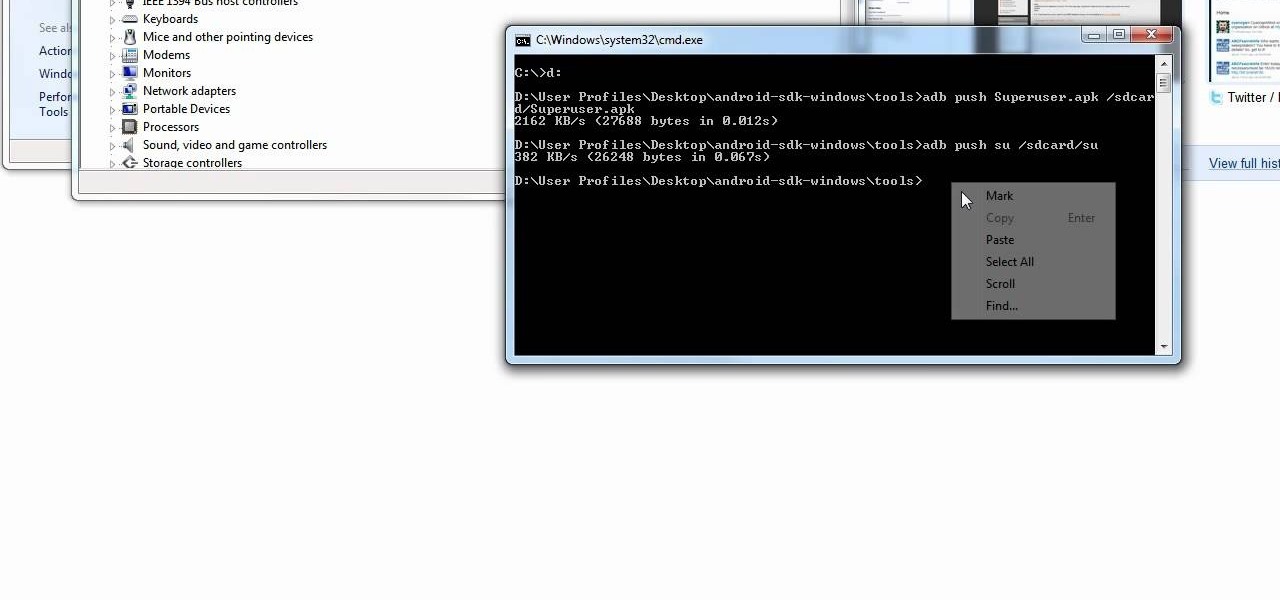
Yes, the Droid X from Motorola can be rooted, and yes, you can do it at home. Just make sure you follow the directions precisely. If you succeed, you'll have a completely rooted smartphone. eFuse doesn't matter. If you want to expand your options on Verizon Wireless's Droid X, then you just have to take a chance… use this video in conjunction with the links and description below.

In this software video tutorial you will learn how to create a column line graph in Microsoft Excel 2007. First you type in the data in to the work sheet. Then highlight the data and click 'insert' on the menu bar. Here you select the 'column' option and go down and click on the type of column that you want. And the graph is automatically presented. Now click on 'move chart' and select a sheet where you want the graph to be moved to and click OK. To change any field in the chart in to a line ...

mIQ? What is it exactly? It's a handy web service that helps you manage your mobile life, with free and easy online access to all of the content and information stored on your mobile device. How does it work? Best Buy has answers. The Best Buy Mobile team explains how simple it is to use mIQ to backup all the data on your cell phone, including messages, photos and contacts.

The tutor advises that the beans are high in protein and fiber but the problem is that when you buy it from the market they are high in sugar and also have artificial colors. So to make healthy beans first of all you need to take a can of 'cannellini organic beans'. You can also use any other type of beans. Now you need some water and some salt to go with it. Add these beans in a pan. You can also add some left over beans. You can now add some 'organic strained tomatoes' which is just like a ...

First of all you need to a set up deck. You need to learn about two things. First you need to learn about calculating the numerical value of the card and also work out the suit the card. First take out a card and lay it face up. This is 4 of clubs. The rule here is that next card shall be 3 more in numerical value because this deck is a set up. So pick the next card that is 7(4+3) of hearts then 10 of spade (10+3) and then king of diamonds (10+3). Now remember the phrase "chsd", c for club, h...

Pigs in a blanket are the perfect appetizer for any occasion. They are great snacks at Super Bowl parties, family functions or birthdays. They are easy to eat finger foods and with only 3 ingredients, require very little work or clean up! In this tutorial, Betty shows us how to make inexpensive pigs in a blanket with Vienna sausages. Enjoy!