In this Software video tutorial you will learn how to change the font color in Word 2007. The default font color in Word 2007 is black. But, you can change the color of the font to just about any color that you want. Click on the ‘home’ tab of the ribbon on top of the page and you will see a small window with the letter ‘A’ in it. Click on the arrow next to it and it will display a color palette with automatic, theme colors, standard colors and more colors sections. Here you select any color ...

The Mac OS's Disc Utility allows for the encryption of files. To open Disc Utility click on the magnifying glass (spot light) up in the top right hand corner, and search for Disc Utility. Click on the first result in the list. Once Disc Utility is open, click on "create a new image" in the top tool bar. A new window will drop down, where you choose what you want to save the new image as. Give it a name, and choose the size you want it to be. Moving down, choose the encryption you want to use ...
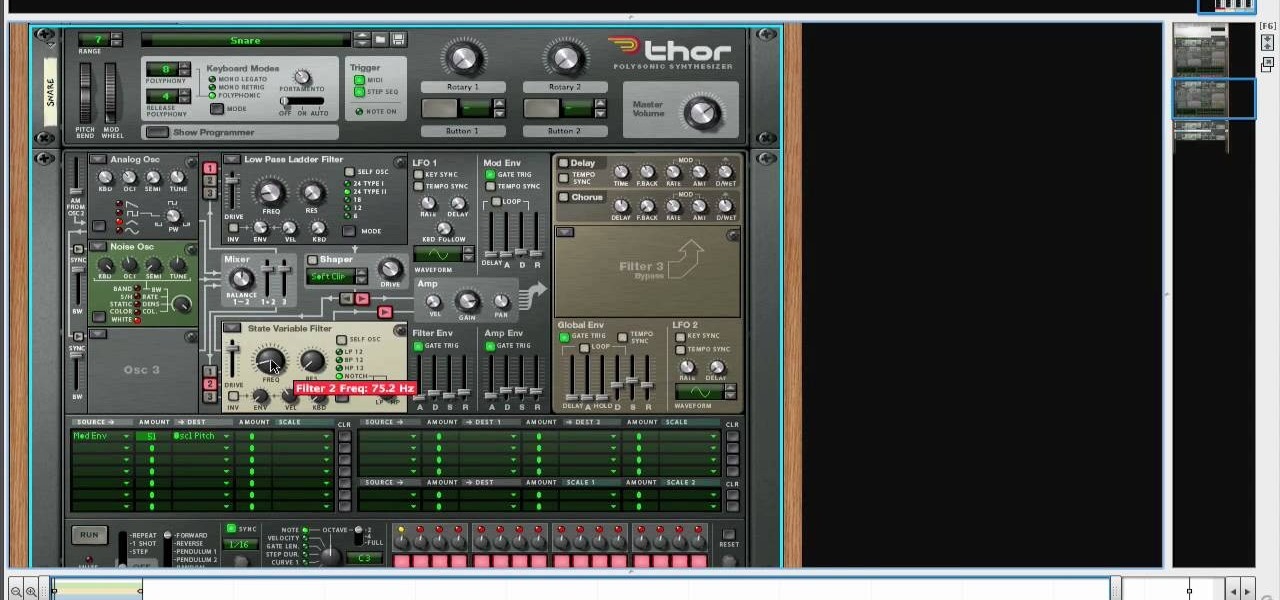
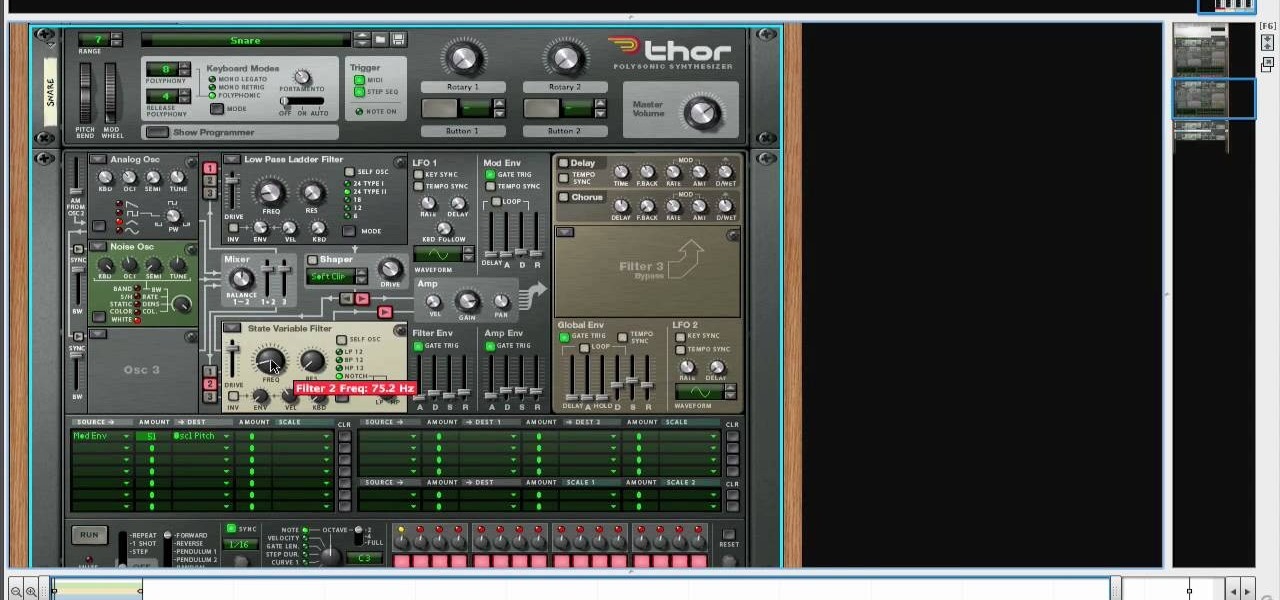
Create drums sounds using Reason's Thor synthesizerYou can use the Thor synthesizer to make a kick, snare, hat and clap sound.Kick:Use the analog oscillator with triple wave form octave3. Set the source to mod envelope 45 destination oscillator 1.Use a very short attack to K and release time. You get the short effect of pitch. Try different oscillator types to get different textures.Snare: Use the same basic patch that we created for the kick. We will keep it as the basis for most patches for...

Everyone who drives should know how to use a car jack in case of a flat tire or blowout. Check your owner's manual to find out where your car jack and spare tire are located. In most cases, they are somewhere in the rear of the car. The video shows us how to use a telescoping jack, though the more common type of jack requires a scissor motion to raise the car and lifts from the side rail. The telescoping jack lifts from the axel and to raise the jack you need to insert the rod into the hole n...

Pushups are a great workout. But if you think you're ready to take it to the next level, you should consider incorporating backback pushups into your workout. The added weight will give your muscles added strength and give an exciting new take on a simple exercise.

First of all put a bucket under the trap. Now use your hand to loosen the handle of the PVC type trap. Loosen both the two plastic nuts on the ends. Remove the nuts that are holding to the drain pipe. Now when you remove this trap from the drain pipe a little dirty water comes out of it which gets collected in the bucket. Now check the trap for some hair and other clogs. This you have to remove and clean it out completely. Also check the drain pipe outlet for removing any hair or other clog. ...

This video takes us through a process of speeding up our internet connection using OpenDNS.com. Open the webpage and go to solutions and click on the icon open the DNS page and it lists computer or router, she selects computer and list of operating system is listed, she selects vista. She goes to start and selects control panel, click on view network status and connection, in that select view status and then click on properties and on the networking page, go to internet protocol version 4 and...

Making a rose arrangement is not difficult, but there is some skill to it. In this video tutorial from Fresh Flower Ideas, learn the tips and tricks of creating an arrangement with a dozen red roses for Valentine's Day. In this tutorial, a dozen red Freedom roses are used, but you can use whatever grade and type you want. You will also need sprigs of babies breath, leather leaf, and tree fern. To begin, clean off the stems and the rest of each rose. Add once piece of leather at an angle in th...

For inserting a picture, from the INSERT Tab click picture. Then the insert dialog box gets opened. From there you can locate the desired picture. Locate the picture to be inserted and double click it. We can also replace the picture selected. For replacing any one of the following can be done: Under PICTURE tools, on the FORMAT tab, in the ADJUST group, click Change picture OR right click the picture to be replaced and click CHANGE PICTURE. Locate a new picture, and double click it.

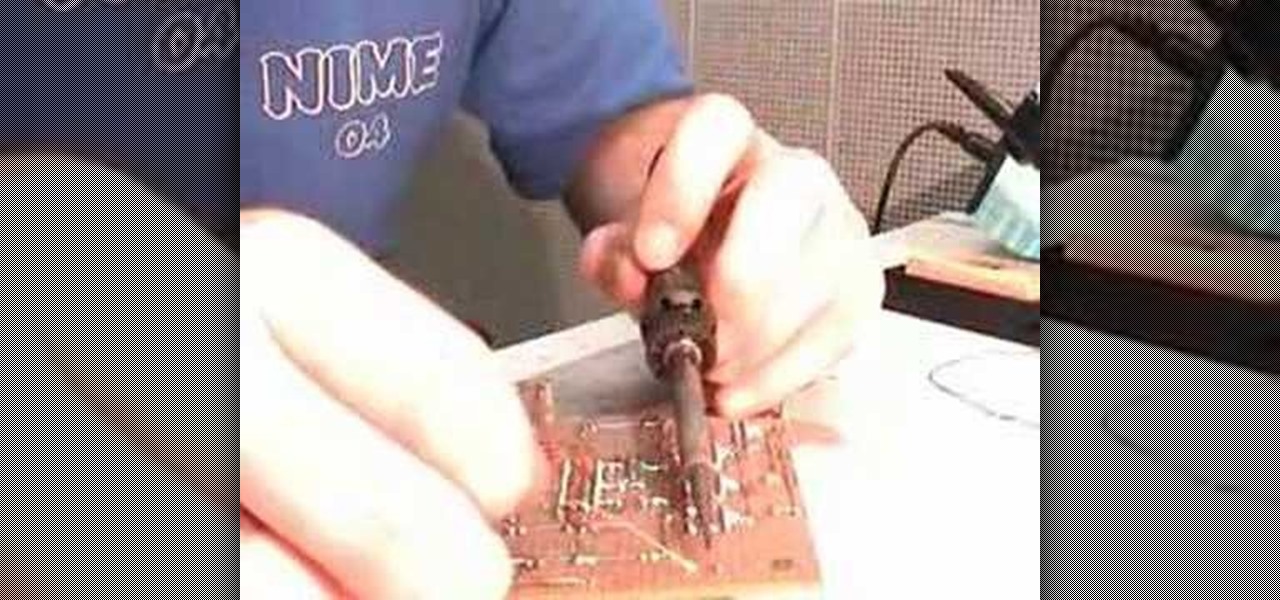
Learn how to solder wires with this video. Clean the area to be soldered, scraping the wire down to bare metal and then wiping it clean with alcohol or acetone. Use rosin-core solder for electronic applications. This solder normally comes in coils. Tin (coat with solder) the soldering tip first: Wrap one or two inches of solder around the tip while the iron is cold; set the iron to the solder's temperature range; and allow the solder to melt. Clean the tip with a sponge. Set the soldering too...

This video describes how to draw an anime face viewed from the front. Anime faces are enjoyed by everyone because they depict unique personalities. Anyone can draw an anime face using their imagination. These steps make it simple:

The video is from the DJ tutorial and it shows us the basic principles of scratching for the beginners. And the first lesson you should learn is that there are basically four movements and here you will actually be not going to scratch put will be moving the record forward and backward. These four moves form the basis for starting to learn scratching. First you need are the type of sounds which are either acapella (song with no music) or with sounds (tracks with breaks on it). Before starting...

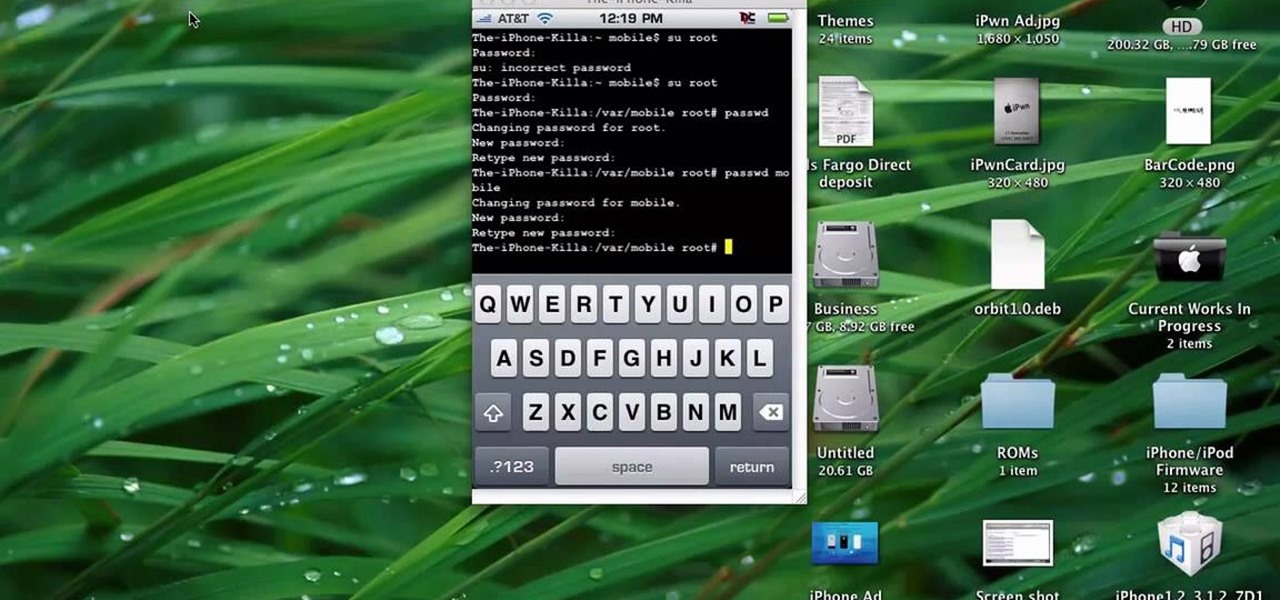
This quick tutorial runs you through a fast and easy way to make your iPhone or iPod Touch more secure. However the best security is abstinence. Just don't run the programs that leave your devices vulnerable unless you need them.

Syncing your bluetooth earpiece to your BlackBerry device can be tricky. But pairing your bluetooth enables BlackBerry with your earpiece is actually quite easy. Best Buy has answers. The Best Buy Mobile team explains how to connect a Bluetooth earpiece to your mobile device. See how to access connections set-up on your Blackberry and also see how to wear a Bluetooth headset.

Kate Hemmings on The Crafts Channel shows that covering a cake isn't as tricky as you may think. You will need a type of icing that rolls out, such as fondant icing. Ideally, you will want to have fondant icing with glycerine, and so the Pettinice brand is excellent in this case. If you use this icing, you will not encounter problems with cracking of the icing when you try to shape it over the cake.

This tutorial shows you how to make a quick and easy pizza dip. First you need to get an oven proof bowl, your size depends on how much you want to make. Start with cream cheese and press or spread evenly into bottom of your bowl, not too thick not to thin. Next use pizza sauce or any type of tomato based sauce and spread out. The third layer is cheese we are using mozzarella cheese, but you can use any you like. Next layer you can use whatever you want on your pizza. We used diced tomatoes o...

This will hack speed on Typing Maniac. Sometimes slowing down the process is the only way you'll win. If that's the case, then use Cheat Engine to slow down time and become the ultimate typer.

In this six-part video tutorial, learn how to create an access database. The following six parts go over the following:

Cheat your way to the top of Typing Maniac with Cheat Engine. Cheat Engine solves all of your playing woes by doing all of the work for you.

New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to install Zekr (Qur'an Study Tool) on Ubuntu Linux, Windows, and Mac OS.

You're in a Zoom meeting, and you're click-clacking away at your keyboard, typing important notes from the call. More realistically, you're doing something unrelated to the meeting, such as browsing the web, playing a game, or messaging friends. Whatever it is you're typing, if your microphone is on, everyone on the Zoom call will be able to hear the sound of you typing.

The ability to hide entire pages on your iPhone's home screen is an excellent privacy upgrade packed into iOS 14. That said, it can be a bit of a pain to find and open the hidden apps on those pages in a timely fashion. Luckily, iOS 14 has a solution that makes opening those apps, as well as any others, faster and more convenient — and we're not talking about the new App Library.

Not all 5G is equal. Even if you dropped the cash on a true 5G phone and you see it's connected to 5G in the status bar, that doesn't mean you're surfing the web, streaming Spotify, and binging Netflix faster than your friends with LTE phones.

With more digital content than ever, the search feature on smart TVs is essential. But typing is such a terrible experience when you're forced to use voice dictation or peck around with the remote control. Thankfully, there's a better way.

After many years of rumors, the second-generation iPhone SE is here. At $399, it is the most inexpensive iPhone Apple has sold since the original iPhone SE came out. And while the new SE comes with Apple's typical five-watt power adapter, the smartphone supports fast charging — you just need to get a fast charger separately.

Wi-Fi networks come in two flavors: the more common 2.4 GHz used by most routers and IoT devices, and the 5 GHz one offered as an alternative by newer routers. While it can be frustrating to attack a device that moves out of reach to a 5 GHz Wi-Fi network, we can use an Alfa dual-band adapter to hack Wi-Fi devices on either type of network.

Apple has implemented a new sensor on the rear camera of its fourth-generation iPad Pro, and it's pretty exciting. It's called the LiDAR Scanner, a scanning "light-detection and ranging" sensor, and you may very well be acquainted with it if you follow any driverless car news. Will we also get it on the upcoming iPhone 12 Pro?

Pinning a tweet is a great way to get the point across because it's the first post people see when they visit your Twitter profile. When you pin a tweet, reply, or retweet, it sticks to the top of your profile, whether you create new tweets or not. It's the perfect spot to place one of your more popular tweets, a fantastic blog you wrote, or even just a joke that shows your personality.

Estimates say that there are roughly 441 million Apple Pay users in the world, but with almost a billion active iPhones in the world, some of you have yet to jump on board the digital payment method. But once you're ready — or if you just need a refresher — adding your debit and credit cards to Apple Wallet is simple.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

It seems like each day our phones become more integrated into our lives. School, work, shopping — so many tasks either require a phone or heavily benefit from one. But our phones are a double-edged sword that can easily distract us and harm our mental health as well.

A lot of time can be wasted performing trivial tasks over and over again, and it's especially true when it comes to hacking and penetration testing. Trying different shells to own a target, and testing out privilege escalation commands afterward, can eat up a lot of time. Fortunately, there is a tool called One-Lin3r that can quickly generate shells, privesc commands, and more.

Post-exploitation information gathering can be a long and drawn-out process, but it is an essential step when trying to pivot or establish advanced persistence. Every hacker should know how to enumerate a target manually, but sometimes it is worth it to automate the process. Metasploit contains post modules that can quickly gather valuable information about a target, saving both time and effort.

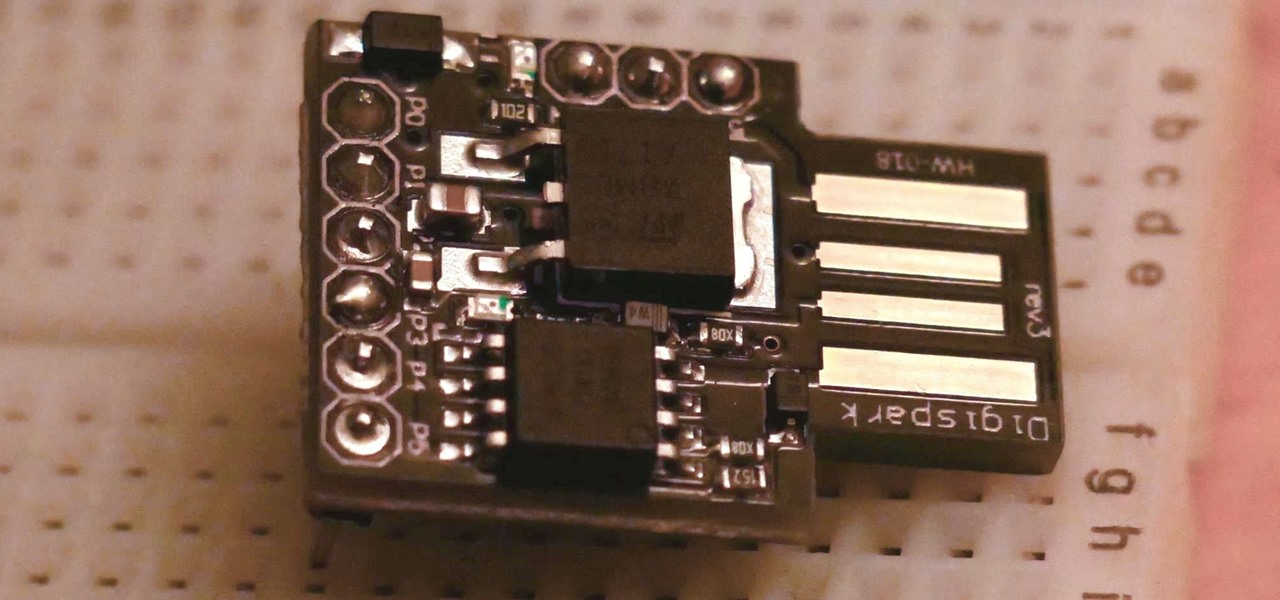
The USB Rubber Ducky is a famous attack tool that looks like a USB flash drive but acts like a keyboard when plugged into any unlocked device. The Ducky Script language used to control it is simple and powerful, and it works with Arduino and can run on boards like the ultra-cheap Digispark board.

Web application firewalls are one of the strongest defenses a web app has, but they can be vulnerable if the firewall version used is known to an attacker. Understanding which firewall a target is using can be the first step to a hacker discovering how to get past it — and what defenses are in place on a target. And the tools Wafw00f and Nmap make fingerprinting firewalls easy.

TWRP won't be ready for the Pixel 4 and 4 XL until months after release. But since you can already root with Magisk and tinker with the OS, you might find yourself in a situation where your phone won't boot, yet you don't have a custom recovery installed to fix it. Luckily, there's still a way around this.

Google is an incredibly useful database of indexed websites, but querying Google doesn't search for what you type literally. The algorithms behind Google's searches can lead to a lot of irrelevant results. Still, with the right operators, we can be more exact while searching for information that's time-sensitive or difficult to find.

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

While you might suspect your MacOS computer has been infected with malware, it can be difficult to know for sure. One way to spot malicious programs is to look for suspicious behavior — like programs listening in on our keyboard input or launching themselves every time we boot. Thanks to free MacOS tools called ReiKey and KnockKnock, we can detect suspicious programs to discover keyloggers and other persistent malware lurking on our system.

The Files app received a big update in iOS 13. Before, it was limited to local and cloud-based files, but now you can access data from external storage devices, including SD cards and USB drives. But before you try to connect your favorite card or drive to your iPhone, there are a few things you need to know.