
Hack Like a Pro: Linux Basics for the Aspiring Hacker, Part 11 (Apache Web Servers)
Welcome back, my aspiring hackers!


Welcome back, my aspiring hackers!

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.
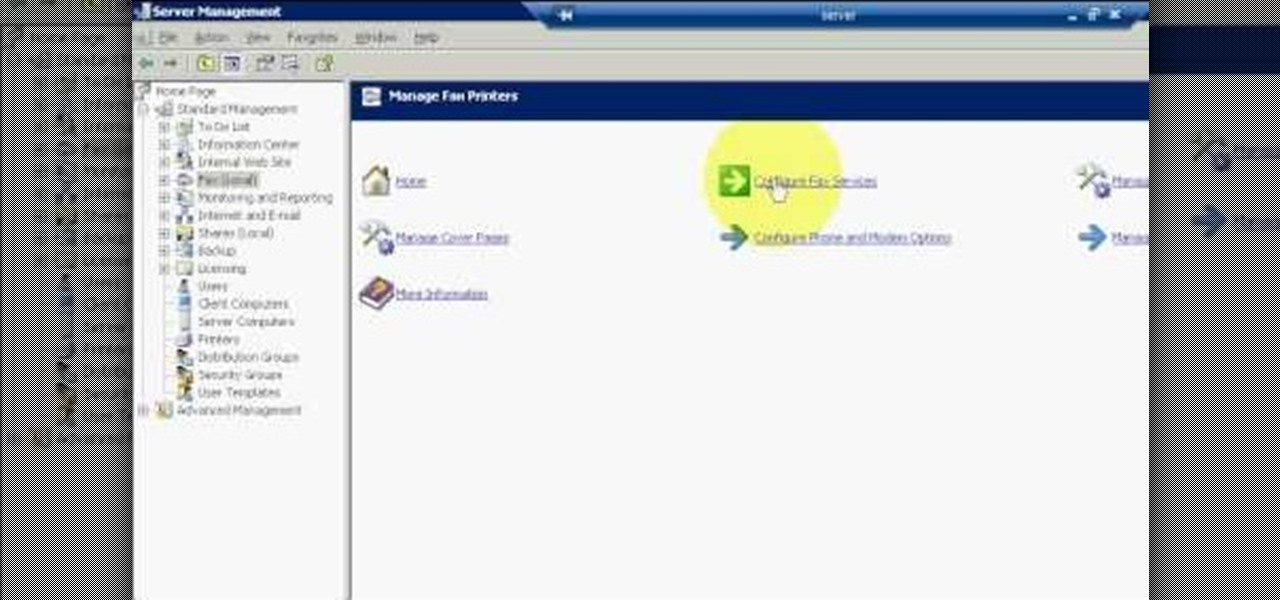
The first step to create a fax using Outlook 2003 and 2003 server. Using add/remove windows component make sure your fax equipment is properly installed. Under the start menu select the printers and fax option and select the share option. Then under administrator tools/users/new/users/fax to enter your password to turn our fax information transfer on. You must now select fax user and select advanced settings and double check to make sure the fax is able to see the object it needs to send the ...

The programming language LISP is definitely not as well known as XML or C++, but it's been around for a very long time and is one of the easiest computer programming languages to learn if you want to create a web server. It is a contemporary of Cobal and was devloped by John McCarthy. To learn how to use LISP for beginners, check out this tutorial.

In this tutorial, we learn how to set up your AIM/AOL e-mail accounts in Outlook. First, go to Outlook and open up e-mail accounts through the tools menu. Now, add a IMAP serve, then add in your user information. After this, enter in your server information, and click the settings button. Change the name of your folder if you are using multiple accounts, so you don't confuse them. In the next tab, check the outgoing server mark, then on the advanced tab, change the last number to 587. Press o...
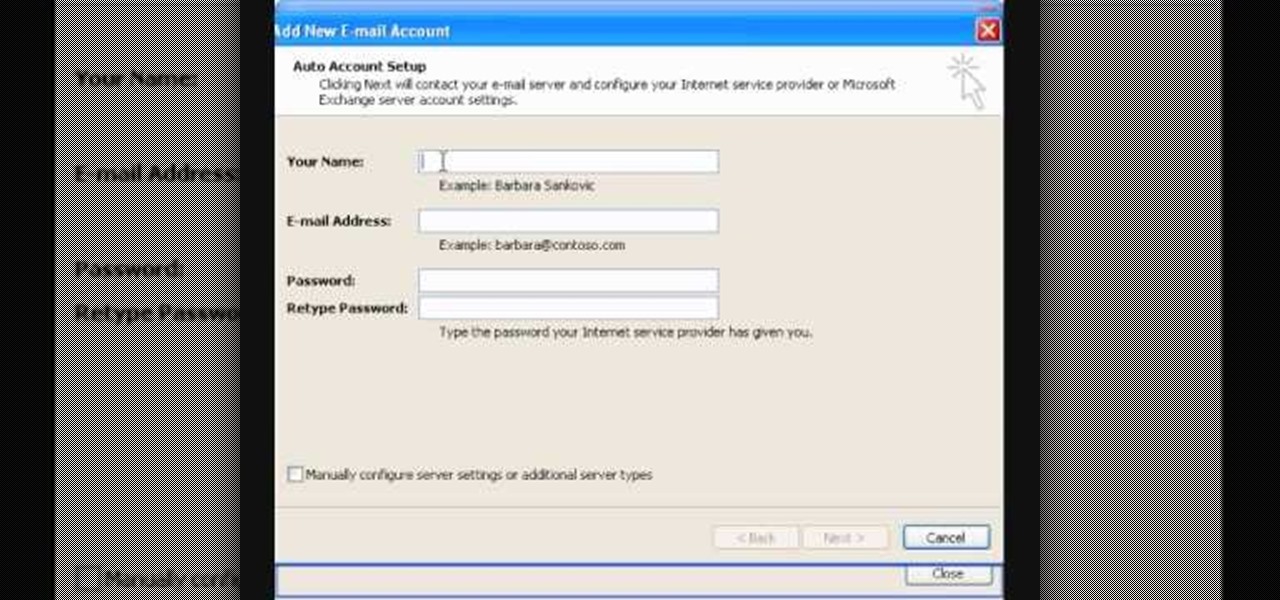
In this video tutorial, viewers learn how to setup Microsoft Outlook 2007. Begin by opening the Outlook Express 2007 program. Then click on Tools and select Account Settings. Under the Email tab, click on New. Now type in your name, email address and password. Then click on Next. Select Internet Email and click on Next. Now type in your user information, server information and log on information. Then click on More Settings and click on the Outgoing Server tab. Check the first box and then cl...
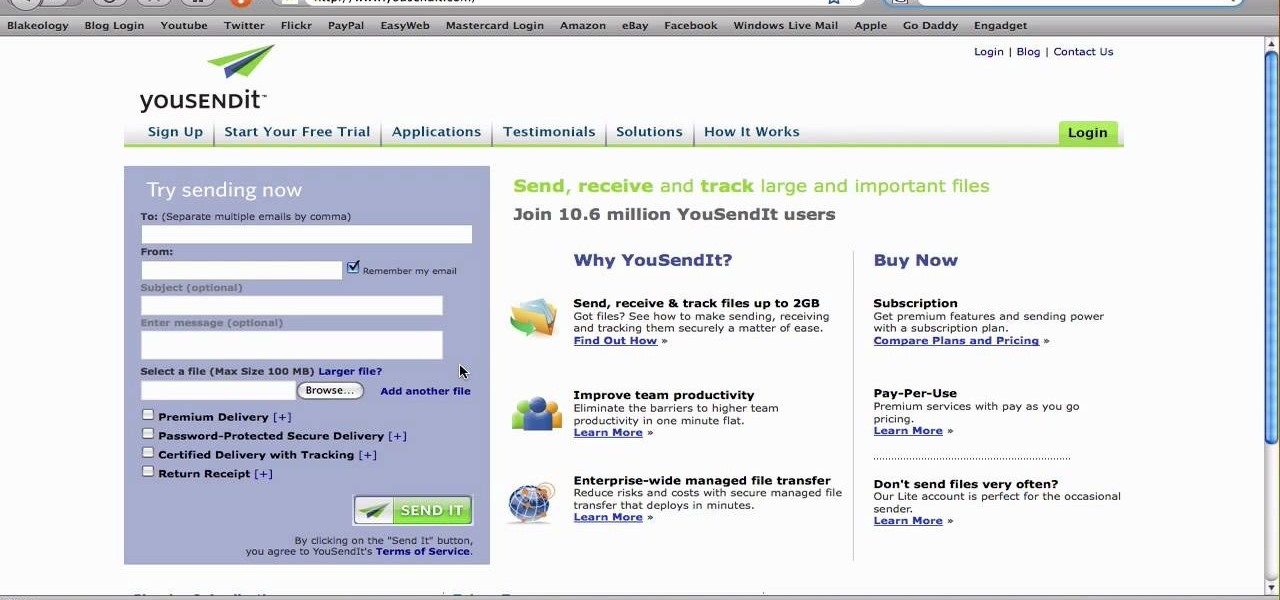
Most e-mail servers cut you off at about 10mb for attachments. If you need to send a larger file, watch this tutorial. In it, you will learn how to send files upwards of 100mb for free and avoid server limits. This clip will show you how to send quick and easy files to your friends without worrying about them not fitting in your messages. This video will show you step by step how to accomplish this in less than five minutes.
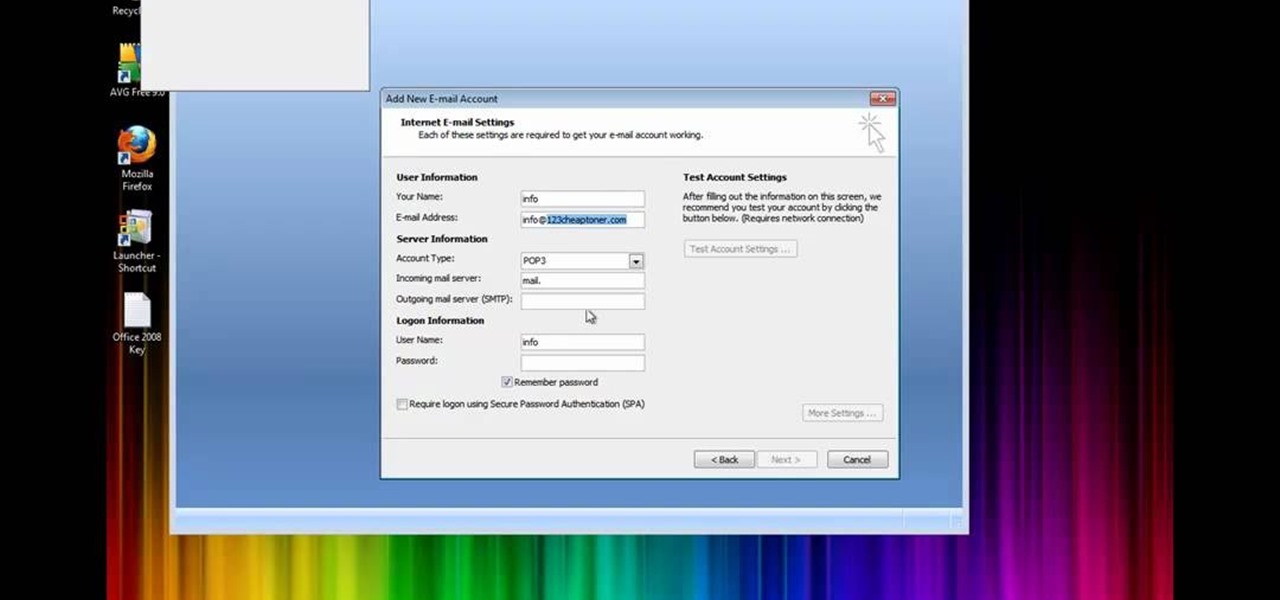
In this how to video, you will learn how to set up Outlook 2007 in Windows 7, XP, or Vista. First, open the program. Click next and and check manual configuration. Select the top option in the next window. Now you must fill in your name, email address, and server information. Lastly, fill in your user name and password. Click more settings and select the outgoing server tab. Here you will authenticate your email address. Once this is done, click okay and next. Click finish and the program can...

This video teaches you to sync Google Calender with the Apple iPad Calender app. The first step involves going to 'Settings' and then to 'Mail Contacts Calenders'. Add an account to the application. For doing this, go to Microsoft Exchange. Type in your email ID in the space provided for it and skip domain. Type in your username and password. Click on 'Next' and 'Accept' in the resulting box. Then a box named 'Server' appears. For the server type 'm.google.com' and click 'Next'. Turn off the ...
In this Computers & Programming video tutorial you will learn how to update a website with an FTP client (v† la FileZilla). Download FileZilla client from www.filezilla-project.org. Find your server IP address from your web host, which will be found in the hosting control center. In the video, it is GoDaddy.com. Open your filezilla client and put in the IP address of your web host and your username and password for your hosting account. Then click ‚Äòquickconnect‚Äô. This will connect you to ...
This video discusses how to change your IP address in Windows XP. Start by clicking on the Start Button and then Run. Type in "cmd" and press enter. This will open a Command Prompt box. From here type in "ipconfig" which will show your current IP configuration, including your IP Address, Gateway, DNS Servers, etc. Next type "ipconfig /release". This will release all IP information from your current network adaptor. Next open up network connections, right click on Local Area Connection and sel...
This video demonstrates the technique to setup a Yahoo email on an iPod Touch. You start going into settings and then clicking account. On the next screen you will click "Other" and then click on "Pop". At this point you enter your name and email address that you use for your Yahoo email account. Incoming server or host name is "pop.mail.yahoo.com", next is the username (which is your yahoo email address without the @yahoo). You will then enter your password and the out going smtp server whic...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to turn any Windows application into a service.

In this four-part video tutorial, Joe Stagner will demonstrate, using ASP.NET, uploading a single file from the client machine to your server.

Most of us stay with a certain computer operating system - or a specific version of that system - because it gives us a great amount of ease. But what if you're using an older edition and it's starting to look a bit, well, outdated? Make your Windows Server 2003 look newer by installing the Windows XP Luna theme. You'll have to enable Themes to make this work. Check out this video for the tutorial.

Installing Joomla on a Windows server can be tricky, on Windows running IIS even more so. Installing Joomla 1.5 in this scenario has caused many frustrations.In this video, we take the process step by step and jump over the hurdles that cause some people to wind up pulling their hair out. If you follow along closely, you will be up and running in no time, and if you haven't already tried to do this, you will wonder why people find it so difficult. There are some prerequisites to the steps in ...

When you try running Apache, Joomla, PHP and MySQL at the same time, you should expect a few hiccups. But there are ways to get them running smoothly and effortlessly together, and this video will outline the process of getting your Joomla Content Management system up and running correctly on Windows.
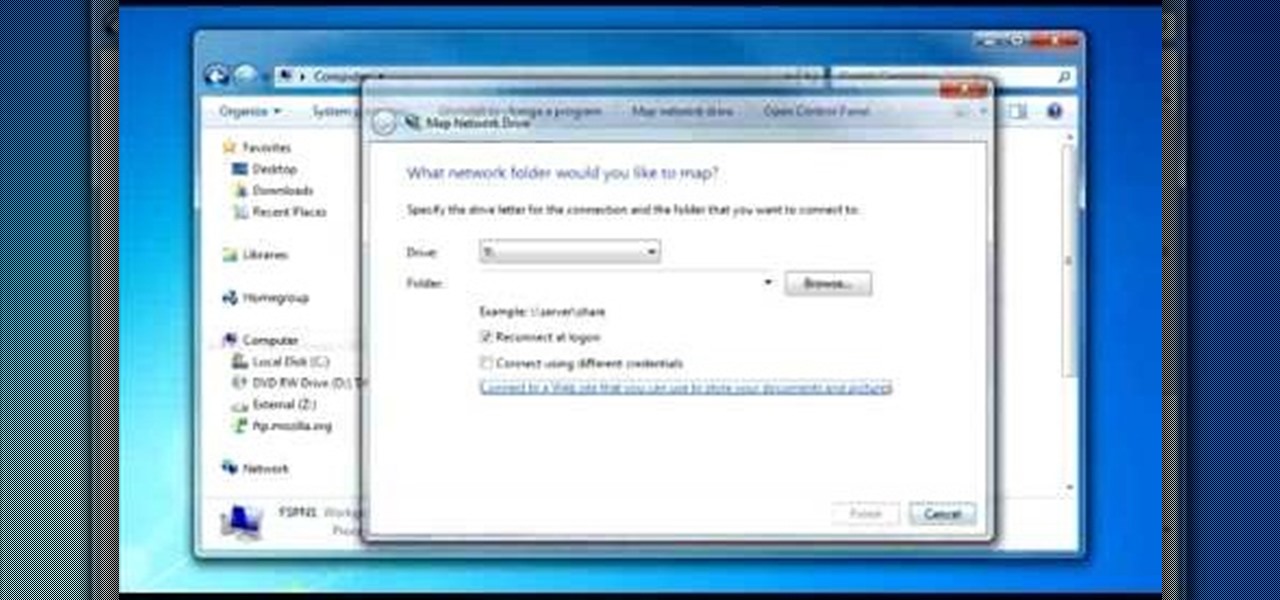
To do that click on tools in windows explorer and choose map network drive. Now click on "connect to a web site that you can use to store your documents and pictures" and then click on next and next. Now you have to type your internet or network address for example you type ftp://ftp.mozilla.org. This is a public server and it does not require a user name or password. Now click on next and there make sure you selected "log on anonymously" but if your server require a password then you have to...

This video takes us through a process of speeding up our internet connection using OpenDNS.com. Open the webpage and go to solutions and click on the icon open the DNS page and it lists computer or router, she selects computer and list of operating system is listed, she selects vista. She goes to start and selects control panel, click on view network status and connection, in that select view status and then click on properties and on the networking page, go to internet protocol version 4 and...
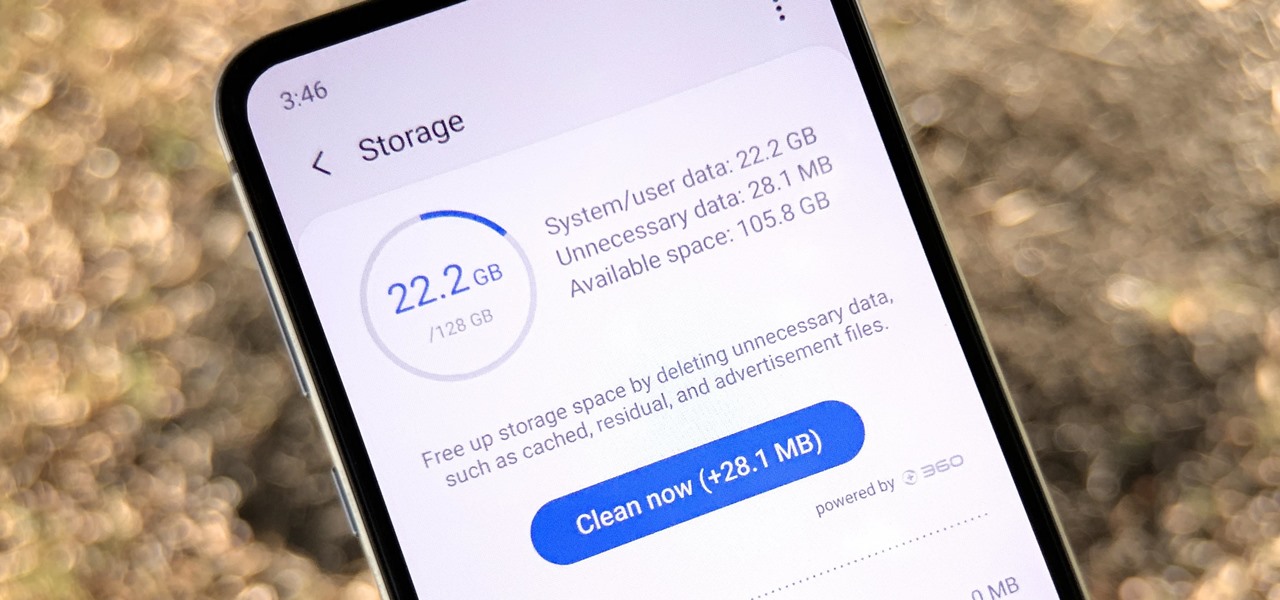
Samsung, like other OEMs, partners with third-party companies to include their apps on Galaxy devices. For example, Microsoft pays Samsung millions to pre-install certain Office apps. But one of these partners might not be on the up and up.

The next libSSH or OpenSSH exploit may be just around the corner. Keep your SSH service out of Shodan's database before hackers find new ways to bypass the password protecting the server.

While hackers have taken advantage of numerous vulnerabilities in Adobe's products to deliver payloads to Windows users via PDF files, a malicious PDF file can also wreak havoc on a Mac that's using the default Preview app. So think twice before double-clicking a PDF open on your MacBook — it might just be a Trojan with a rootkit inside.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website was viewed. There's no doubt Coinhive, an innovative mining method, is being abused and exploited by hackers in the wild.

Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.

At this point in our series on creating a customized hacking container, you should be able to use Docker to save and retrieve customized instances of Ubuntu from your own machine. Make sure to revisit part one and part two if you need a refresher.

Backdoors are convenient to leave behind once you've already found a way into a server, and they can come in handy for a variety of reasons. They're good for developers who want a quick way into machines they're working on, or for systems administrators who want similar access. Of course, backdoors are also a hacker's best friend, and can be added in a variety of ways. One good tool for doing this is Weevely, which uses a snippet of PHP code.
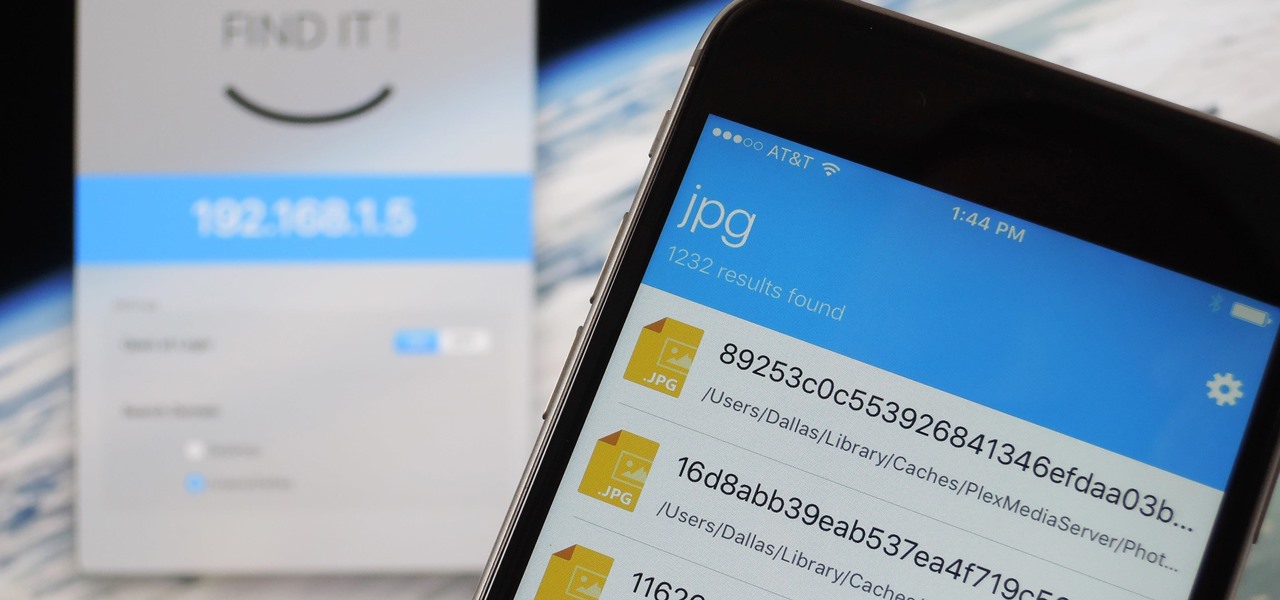
When it comes to sharing files between a smartphone and a computer, there are several solutions available for a Windows and Android pairing. But for those of us with Apple devices, the selection of apps in this category isn't quite as great. You can use AirDrop to quickly share files, but searching for files is not so easy.

In this series you will learn how to use PHP to perform attacks, gather information, and setup backdoors. Along with performing attacks you will learn how to protect yourself from them. In this part you will learn about PHP as well as install Apache and PHP. What you'll need for this series

Good day people, today we will examine some basic, for some people well-known attacks, also we will take a look at some advanced attacks.

This is a quick and easy method for receiving the backend IP (1) of a server who is hidden behind a proxy (2) or a firewall (3).

If you remember last time, we successfully uploaded picture with a small hidden PHP command executer embedded in it onto a server. Now, our goal is to take this a step further and get an interactive shell. To do this, we need to upload another file that either binds a port for us, or connects back. For this tutorial, we will use a Python reverse Meterpreter shell.

Welcome back, my budding hackers! We've spent a lot of time learning to compromise Windows systems, and we've successfully compromised them with Metasploit, cracked their passwords, and hacked their Wi-Fi. However, very little time was spent developing ways to extract the information from the system once inside.

Welcome back, my greenhorn hackers! Earlier in this series, I showed a you a couple of different ways of fingerprinting webservers. Probably the easiest way, is to use netcat and connect to port 80 and pull the webserver banner.
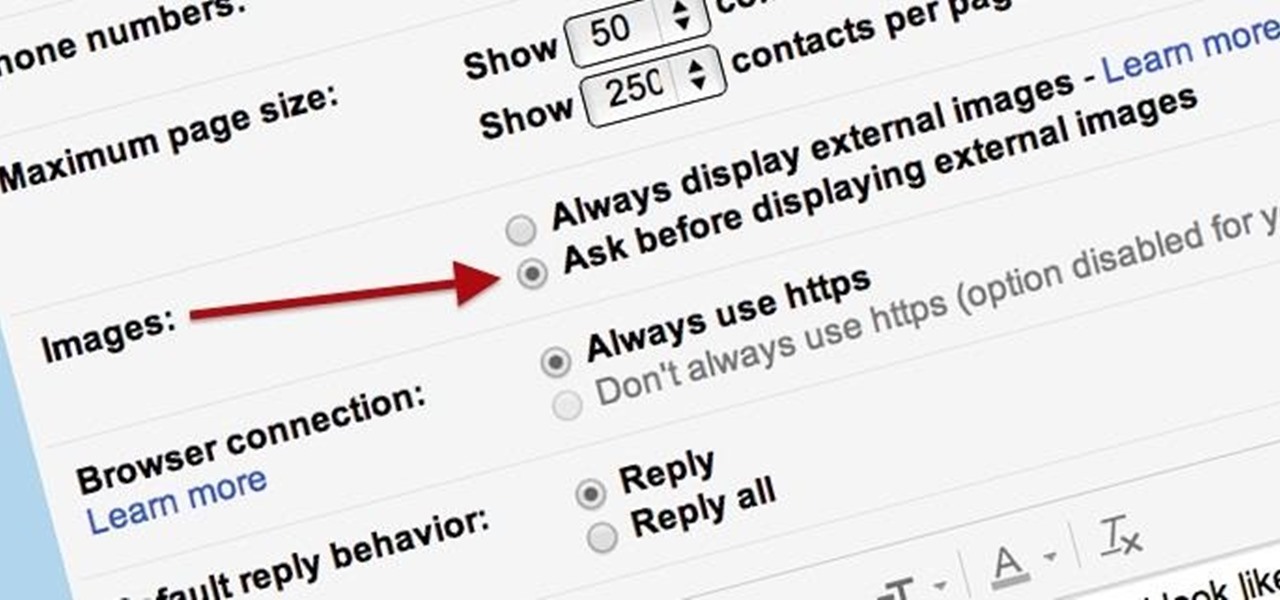
Securing your email address is one of the most important things you can do on the internet. Hackers, spammers, and overly aggressive marketers can turn your Gmail inbox into a heap trash if you're not careful.
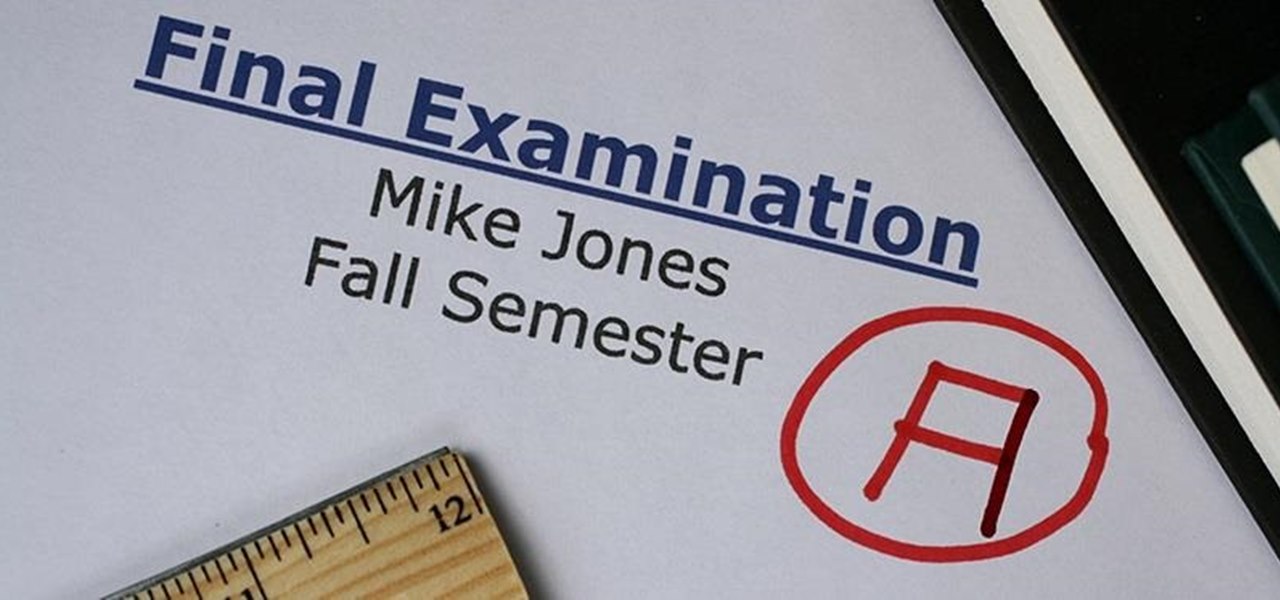
Welcome back, my fledgling hackers! If you're like most aspiring hackers, at one time or another you've probably spent too much time playing Call of Duty and not enough time preparing for your final exams.

Minecraft is such an incredible game that it allows players to create other games within their Minecraft servers. Here is one that is particularly fun. This is Blockey. Watch this video to learn how to build your own Blockey arena and get started playing.

So you want to start your own website / blog / forum / web empire. Good, at least you aren't getting into financial services! This video will show you how to install three important programs that will help you get started: XAMPP, Wordpress, and MyBB. These programs will help you set up your web server, blog, and forum respectively, three important tool that you will need to use effectively to become a force on the web.

Got banned from a website you love to torment? Well, there's a way to keep it going. You can get back onto a site by changing your IP to get past the servers. This will only work if your IP is banned. If your username is blocked directly, you will have to find another way.

This time on the show, bypassing restrictive firewalls with a free and open source virtual private network server for Windows and Linux that will have you connecting back to the home or office with just a web browser! Best of all? It's free! Check out this video for detailed information on how to build an SSL VPN.