From personal photos and videos to online banking passwords saved in your web browser, your phone has all kinds of sensitive data that needs to be protected. One of the best things you can do for your Samsung Galaxy S4's data is have a lock screen with a hard-to-guess PIN or password.

The Nexus 5 is the current Google flagship packed with the latest and greatest of all things Android, but what if you never made the leap from your Nexus 4 smartphone?

Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack.

While iOS offers a plentiful mix of excellent and exclusive features, what you see is what you get. Apple doesn't leave much room for customizability, meaning most people's iPhones look relatively the same. You can make yours stand out, however, by giving your apps unique and personal icons.
"You can never know too much" is a saying you hear all the time. Funny thing is, I have no idea where it originated, and neither do most of the people who continually say it. Nevertheless, it's a statement that very few would argue with.

Despite the security concerns that have plagued Facebook for years, most people are sticking around and new members keep on joining. This has led Facebook to break records numbers with over 1.94 billion monthly active users, as of March 2017 — and around 1.28 billion daily active users.

Many of us in the Steampunk community have pets that we love and cherish, myself included, and we want those pets to share our joy of Steampunk. In reality, they couldn't care less, but for some reason we still love to dress them up. Their reactions usually range from bemused acceptance to temper tantrums, but the awwwws we get from onlookers usually makes it worthwhile.

People are always looking for ways to save money, and for the most part, saving money and cheating the system are synonymous when it comes to things like free internet access. Practically every new gadget is capable of connecting to the web, which means more and more people are looking for ways around those hefty internet bills.

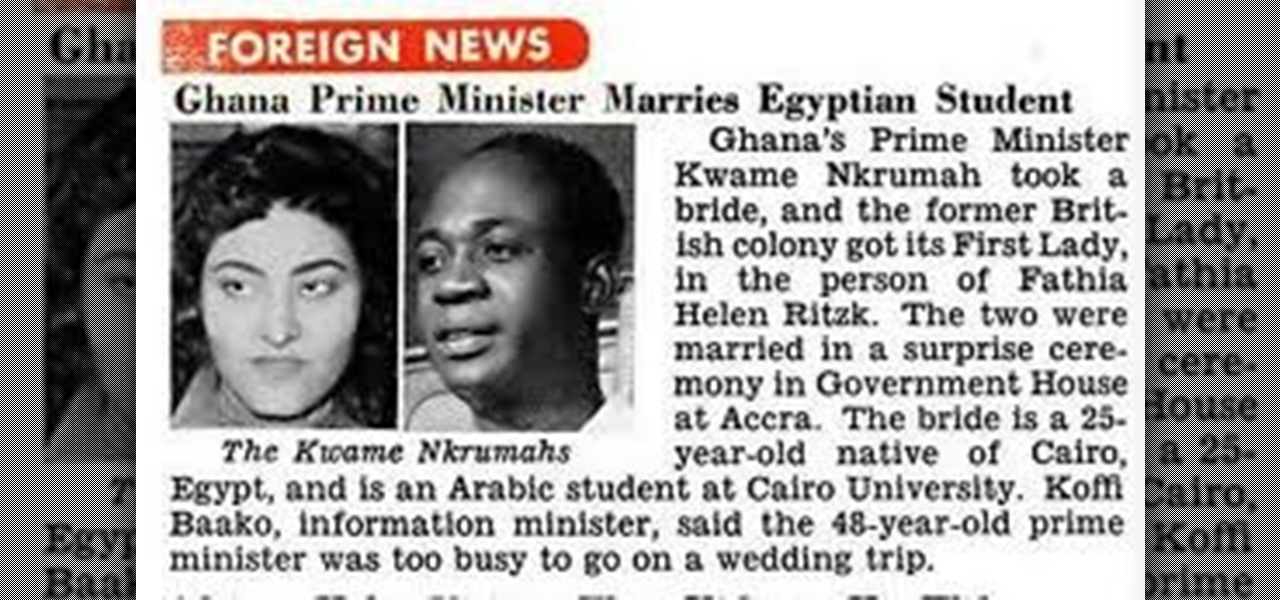
OSAGYEFO DR. KWAME NKRUMAH (1909-72) Founder and Father of the Nation Osagyefo Dr. Kwame Nkrumah, the first Prime Minister and President of Ghana, stands out not only among the Big Six but also among the greatest statesmen of history. It was he who canalized the discontent of the people of the Gold Coast Colony into the highly organized movement of protest against British rule, and within a relatively short period won political independence for Ghana on March 6, 1957. With Ghana independent, ...

In the first part of this series, we took a factual and technical look at the history of the Internet. I explained how all of these wires and servers got here in the first place. Obviously, a firm did not just create and build the Internet around 1995! Now that we know how the Internet came to be, we can get into the really fun stuff—what the Internet looks like now! Well, that's not quite the network design I was talking about, but it does show what the Internet looked like back in 2007 befo...

If you've run out of time for all of our more time-consuming Halloween costume ideas, here are some places on the web for free, downloadable paper masks. There must be at least 100 options among these links to satisfy your last-minute costume needs! Just download, print, and cut 'em out to the appropriate size, then either glue a stick/handle on or tie some elastic string on.

Update (February 2019): The methods below will help on older Android versions, but we've recently revisited this topic. So if you have a newer Android phone and you want to get rid of Google, head here.

Fall is my favorite time of year, yet I cringe every time it begins. Why? Because it seems like every business is in a frenzy to start the Christmas shopping season the day after Halloween ends. For those of us who are fans of pumpkins, that's a buzzkill.

Pumpkin carving and decorating is a favorite October pastime. After you've carved an amazing design or face into a pumpkin or two, you want to show it off through your window or set it out on your porch for the neighbors to see.

Welcome back, my neophyte hackers! I have already done a few tutorials on password cracking, including ones for Linux and Windows, WEP and WPA2, and even online passwords using THC Hydra. Now, I thought it might be worthwhile to begin a series on password cracking in general. Password cracking is both an art and a science, and I hope to show you the many ways and subtleties involved.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

Welcome back, my hacker apprentices! Metasploit framework is an incredible hacking and pentesting tool that every hacker worth their salt should be conversant and capable on.

One of the biggest problems in data security is authentication of data and its source. How can Alice be certain that the executable in her inbox is from the venerable Bob, and not from the not-so-venerable Oscar? Clearly Alice wants to know because if this file is actually sent to her by Oscar, the file might not be a game, but a trojan that can do anything on her computer such as sift through her email and passwords, upload her honeymoon pictures, or even turn on microphones and webcams. Thi...

Welcome back, my budding hackers! One of the most time-consuming, but necessary, activities in hacking is reconnaissance. Before we can hack a system, we need to know what operating system it's running, what ports are open, what services are running, and hopefully, what applications are installed and running.

If you actually had to look up what "DS" stands for in Nintendo DS, that probably means you weren't a huge fan of the portable game system. To be honest, I never was. It's fairly bulky and has two tiny displays.

Remote Desktop gives you access to your Windows 8 PC or device from wherever you are to run your applications and access your files remotely.

A few weeks ago, Facebook published a blog post called "Proposed Updates to our Governing Documents," which outlines a few changes in their policies and user voting system. These changes would essentially take away users' right to vote on future changes to Facebook's data use policy while also taking away Facebook's responsibility to alert users of those changes. If the new policy is enacted, the vote will be replaced with "a system that leads to more meaningful feedback and engagement," what...

The new iPhone 5 was just revealed yesterday, and it's 18 percent thinner and just 1/5 the weight of its 4S predecessor. It's also taller with a larger screen, which gives you a fifth row for apps now. As far as speed is concerned, it has a speedy A6 chip and can tap into wireless 4G LTE networks for fast Internet. Both the iSight and front-facing FaceTime cameras were improved, too. The only downside seems to be the tinier "Lightning" connector, which replaces the standard 30-pin connector w...

All kinds of people pretend to be someone they're not on the internet, including scammers, people attempting to wind others up, hackers and web predators. Almost all of these people will leave bases uncovered and they're all easy to expose when you understand how to. Here are my favorite ways of finding out when somebody is lying quickly. Image Search

Are you interested in beginning research of your family's history? I began this journey about 3 or 4 years ago and here is what I found. I've done almost ALL of my research online, and gotten farther, faster and more comprehensively than anyone else who has researched my family the old fashioned ways. This is the kind of thing that technology is made for. Here's how to use it.

If you read my article on the OSI model, you got a good overview on communications from that model's perspective, but how does that relate to TCP/IP? We're going to take it a step further, getting into the idea behind the two address concept. How does an IP address and a MAC address work together? If you want to hijack sessions and all sorts of lulz like that, you need to understand these concepts. Let's get into it, mates!

From the article: Foursquare, one of the net’s hottest startups, got an unwanted message on June 20 from a white-hat hacker: it was leaking user data on a massive scale in plain violation of its privacy policy.

Log In First, log in to your Facebook account.

Monty Don explains the benefits of hand weeding, demonstrating how to keep unwanted weeds at bay. A weed is simply a plant in the wrong place. Weed your garden all year round, particularly in the spring. Learn some handy tips for hand weeding. Weed your garden by hand.

Mustaches happen to the best of us, even women. This how-to video shows a way to remove hair safely and easily in the comfort of your own bathroom. Follow along with the simple steps to get rid of any unwanted hair, without unnecessary pain. Watch this video hair removal tutorial and learn how to wax your lip. Wax your lip at home.

Use Photoshop to reduce the unwanted shine and flash in your photo images. This video shows you how. Reduce flash in an image using Photoshop.

This tutorial gives tips on how to work with still images in Camtasia Studio 5. It covers importing images, adjusting the duration, and removing unwanted borders. Work with still images in Camtasia Studio 5.

This is a 2 part HD video tutorial set on how to make your own acapellas from full songs. This technique uses Ableton's EQ8 device in mid/side mode to isolate the vocal and the Multiband Dynamics device in downwards expansion mode to reduce unwanted elements from the instrumental backing.

This episode shows you how to use the cropping tool to re-frame and compose your image by removing the unwanted parts in Photoshop Express. Crop an image in Photoshop Express.

Color cast? What is it? It refers to an unwanted tint of a particular color in your photograph, which effects the whole picture evenly. It can be a ghastly sight, destroying an otherwise beautiful photo, but there is a cure. It's a common problem in digital photography, but a common fix in digital photo software, like Adobe Photoshop. This video will show you 6 different techniques to removing color casting in your images. Remove strong color cast from images in Photoshop.

This interactive Kodak EasyShare camera tutorial takes you through every step necessary to review your pictures and videos. If you have a Kodak EasyShare digital camera, you're going to need to know how to do this important step in maintaining and using your camera. Let Kodak teach you how. It's easy to look at your videos and pictures, reviewing them for beautiful or unwanted files, and is basically the same on all Kodak EasyShare digital cameras. Review photos and videos on a Kodak EasyShar...

This interactive Kodak EasyShare camera tutorial takes you through every step necessary to delete pictures and videos. If you have a Kodak EasyShare digital camera, you're going to need to know how to do this important step in maintaining your camera. Let Kodak teach you how. It's easy to remove unwanted media and is basically the same on all Kodak EasyShare digital cameras. Delete pictures and videos on a Kodak EasyShare camera.

If your land is frequented by unwanted coyotes, then a land trap could be the solution. This instructional video shows how to set a single dirt hole land trap for catching coyotes. Make sure to keep the hidden trap area free of rocks and sticks, as canines will not generally dig at these objects, and as an added lure, cover the trap backing in urine. Set a single dirt hole land trap.

This video will take you through a detailed example using the clone stamp and healing brush tools. You will learn how to use the Photoshop’s clone source panel to remove an unwanted section of a picture and then clean up the image using the healing brush. Whether you're new to Adobe's popular image editing application or simply looking to brush up on Photoshop CS4, you're sure to enjoy this free video tutorial. For detailed instructions, and to get started touching up your own images with the...

Hi all, in this tutorial, I'm going to show you how to block and delete unwanted adds (even those in apps, videos or music stream) without having to install an application or jailbreaking your iOS device.