Check out this tutorial that teaches you how to apply pink and purple eyeshadow drag queen style. You will need Elizabeth Farrell Eye Shadow in Pink, Maybelline Eye Shadow in Lasting Lilac, (Darker Shade), Urban Decay in Polyester Bride, Clinique Lash Doubling Mascara in Black, and Sugar is Good For You Palette. This is a perfect tutorial for drag queens and transexuals. Watch this how to video and you will be able to create a pretty pink and purple eye look.

Learn how to apply a drag queen makeup look inspired by Adele with this tutorial. You will need CoverGirl Liquid Foundation in Classic Ivory, CoverGirl Powder Foundation in Classic Ivory, CoverGirl Blush in Plumberry Glow, Clown Make Up in White, Rimmel Eyeshadow in Moonstone, Jane Eyeshadow in Clubbing, Almay Liquid Eye Liner in Black, CoverGirl Perfect Point Plus Eye Liner in Black Oynx, Clinique Lash Doubling Mascara,and Bath & Body Works Colorfill Lip Plumpling Lip Gloss in Miami Peach. T...

Graffiti— do you have the guts to get out there and tag some property? There's a whole lot more than just spray paint involved. To be great, you'll need things like a sketchbook, pencils, pens, markers, spray can tips, latex gloves, legal (or illegal) wall, and most importantly… creativity. If you think you’ve got what it takes to be an urban graffiti artist, follow these steps to become da ’hood’s next da Vinci.

In this installment of Show Me the Curry, you'll learn how to make a delicious fresh fruit tart fit to rival any made for the Red Queen. For a detailed, step-by-step walkthrough of the recipé and instructions outlined below, watch this free video cooking lesson!

With the iPhone, it's possible to share URL's you find on the internet with your friends. Take a look at this tutorial and learn how to share your URL's through the iPhone.

There are many things your iPhone or iPad can do, and Apple does an excellent job of documenting everything on its website. But there are some features that won't show up in any Apple manuals or help pages.

If you enjoy watching music videos, live concert recordings, or bedroom cover songs on YouTube, then YouTube Music is worth your consideration. In fact, YouTube will show a "Switch to YouTube Music" button on some music videos that opens the song in the YouTube Music app — but not always.

With Shortcuts, Apple has designed a way to create your own tools and automations right on your iPhone. And to top it off, your creations can be accessed in a variety of ways, including Siri phrases, widgets, and the Shortcuts app itself. Perhaps even more useful is adding them as custom actions to your Share Sheet and making them available to you system-wide.

Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a crucial pen-tester skill.

Some websites block image downloads on their webpages so you can't save them for reuse. That means long-pressing or force-pressing on protected images in Safari on your iPhone will not do anything or will omit the "Save Image" option. Taking a screenshot is the obvious solution to bypass restrictions, but you won't get the best quality. Thankfully, there's another way.

Having an efficient workflow is an integral part of any craft, but it's especially important when it comes to probing apps for vulnerabilities. While Metasploit is considered the de facto standard when it comes to exploitation, it also contains modules for other activities, such as scanning. Case in point, WMAP, a web application scanner available for use from within the Metasploit framework.

There's nothing more fun than unlocking a hidden Snapchat filter or lens and beating everyone to that perfect first selfie. So when a new filter or lens comes out, like the current Uganda Knuckles one, it's always interesting to see how things will turn out.

Sophisticated hackers have been exploiting vulnerabilities in Chrome and Firefox to trick even the most careful internet users into logging into fake domains for sites like Apple, Google, and Amazon.

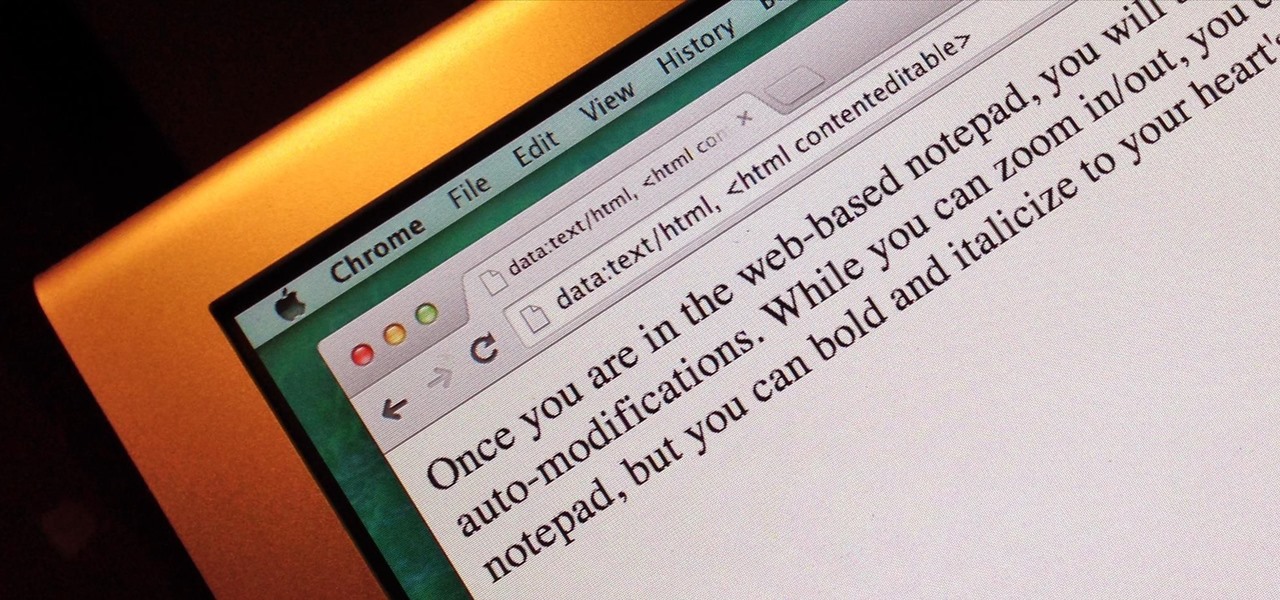
Do you take your notes on a word processor while browsing the web? Well, stop. There's an easier, less RAM hungry way to take notes by turning the tab of your web browser into a notepad. Whether it's an email address, a line of code, a new how-to, or an idea you don't want to lose, you can easily jot it down without slowing down.

Bridge is one of the most popular games in the world. The rules may seem overwhelming, but all you need are a few easy steps to learn the basics.

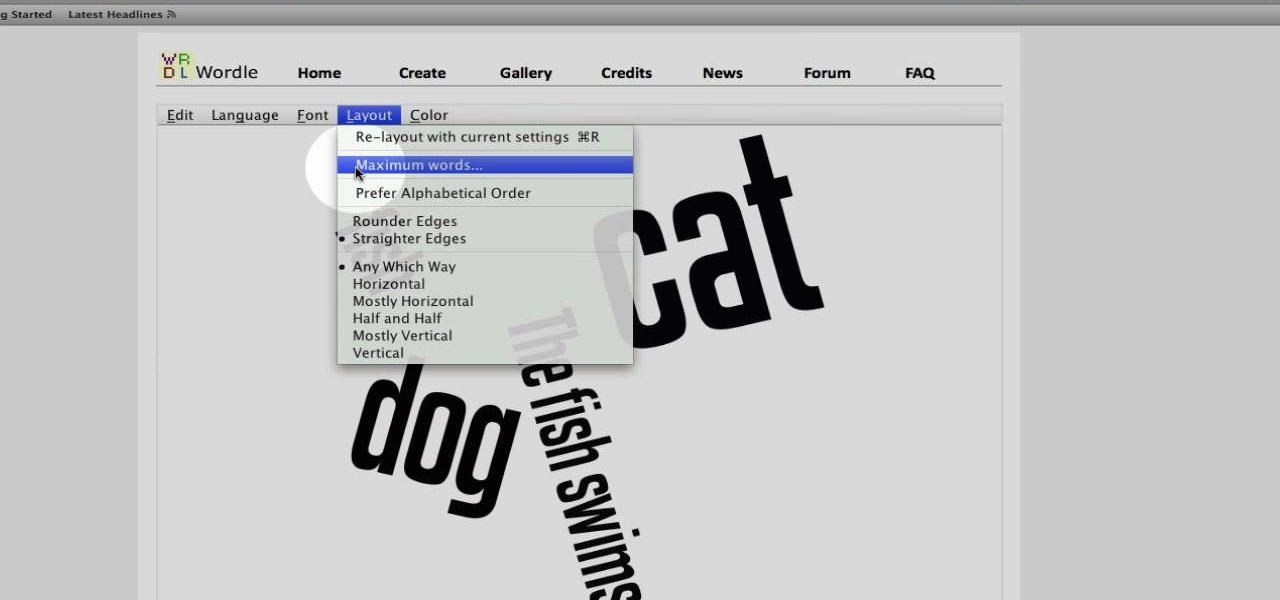
This video tutorial belongs to the Computers & Programming category which is going to show you how to use Wordle to create word clouds. Go to Wordle and click on the 'create your own' link. In the first box, type in your text, and in the second box enter the URL of any blog, blog feed or any other web page that has an Atom or RSS feed. In the 3rd box enter your del.icio.us username, if you have one. After typing in, hit 'go' and you get your Wordle file with the words written in different sty...

In this Computers & Programming video tutorial you will learn how to make a favicon for your site in Photoshop CS3. A favicon is a little symbol that shows up on url bars and also on browser tabs. Open a new project in Photoshop by pressing ctrl+N. Select height and width to 64 pixels and click OK. Now open the title tool and type in whatever you want. In the video, it is ‘F’. Open the background layer and do a color overlay of black. Now change the color of the title to white so that it ...

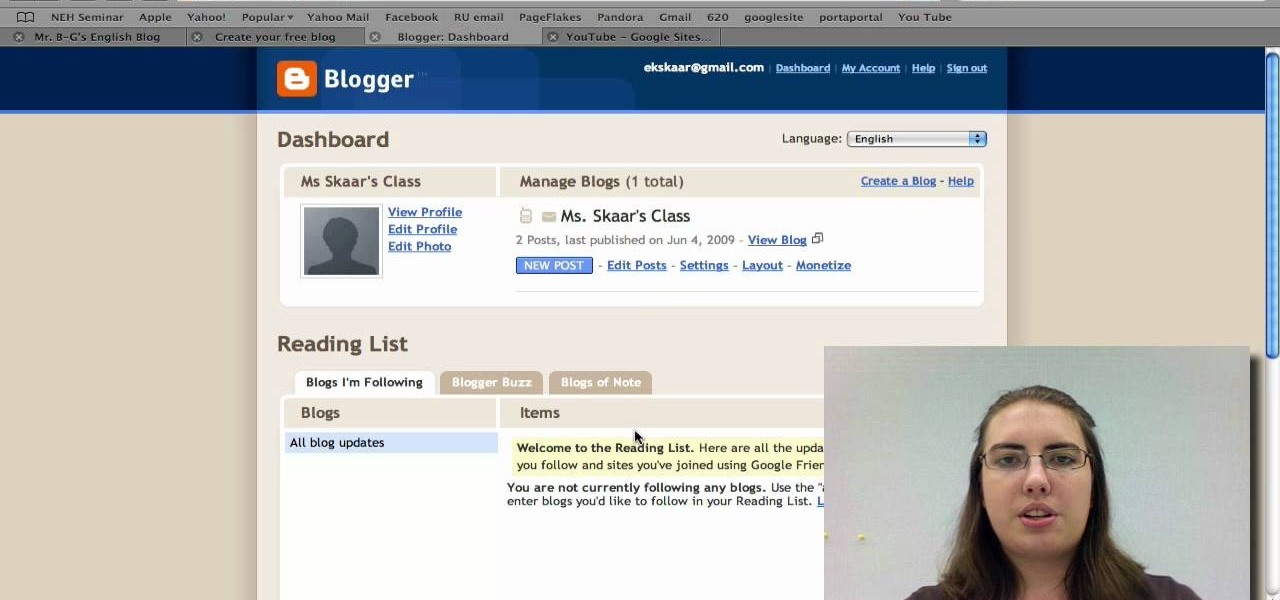
Radford University demonstrates how to upload pictures, embed videos and then publish them in Blogger. Log into blogger and go to your dashboard page. Click edit posts or create a new post. In the blog editor choose edit image from the toolbar. You can now add an image from a URL or upload one from your computer by choosing the choose file option. Next, choose your image position and size. Then, click the upload image button and then click done. Your image will now appear in your post. To emb...

This video given by the Library of Congress gives you a great demonstration on the galliard step. This classical Renaissance dance was a favorite of Queen Elizabeth I of England. However this video does not give you step by step instructions on how to learn this dance, but a first rate demonstration of the galliard dance.

This video tutorial instructs you on what a key logger is and how to make a key logger which records your computers key strokes for later review. There are software or hardware based key loggers that intercept the connection between the keyboard and computer. Hardware key loggers consists of a micro controller for data logging. Software key logger is a script that runs in the background then processes and saves the key strokes to a text file. To make a key logger you'll need to know a program...

Before you attempt this firmware install, if you have already installed custom firmware on your PSP this measure might brick it. Don't double install if you have already hacked your PSP.

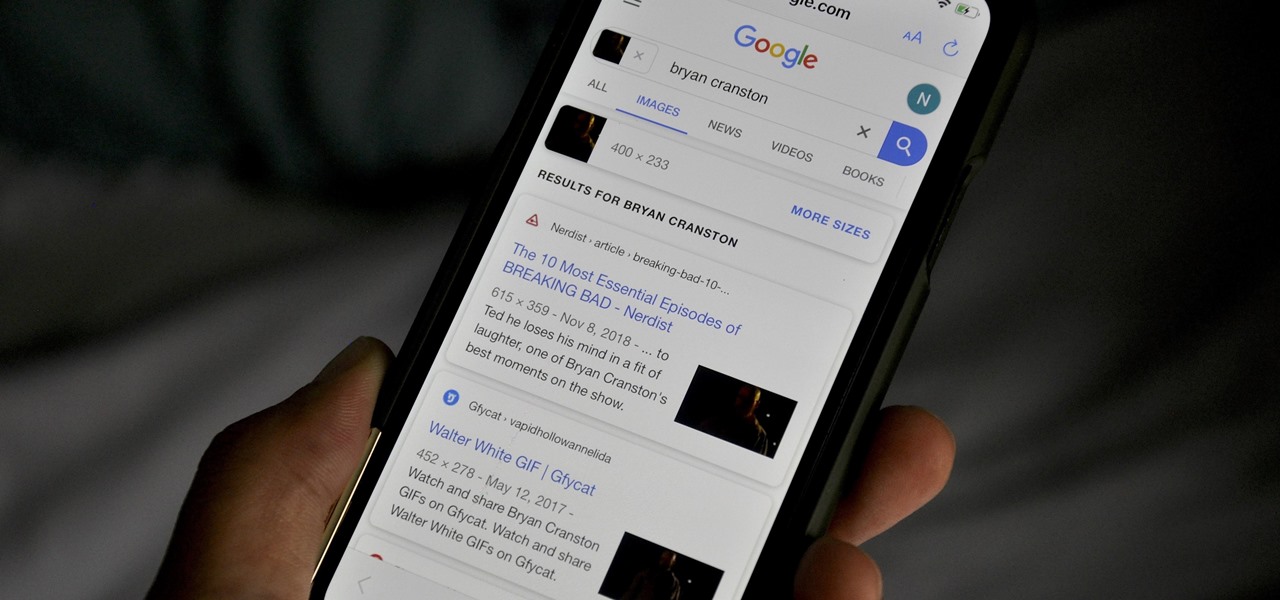
Google Images, TinEye, and other reverse image search engines can help you find where images appear on the internet. You can discover what TV show or movie an image comes from, who took a photo, and if the profile picture of someone you're talking to online is really them, among many other uses. And there's a shortcut for iOS that makes running a reverse image search easy.

Information gathering is one of the most important steps in pentesting or hacking, and it can often be more rewarding to run things on the target itself as opposed to just running scripts against it remotely. With an SQL injection, a hacker can compromise a server and, ultimately, upload and run the "unix-privesc-check" script locally in order to further identify possible attack vectors.

There is no shortage of defenses against cross-site scripting (XSS) since it is so prevalent on the web today. Filters are one of the most common implementations used to prevent this type of attack, usually configured as a blacklist of known bad expressions or based on regex evaluation. But there is hope with a wide variety of techniques that can be used to defeat these filters.

Know thy enemy — wise words that can be applied to many different situations, including database hacking. It is essential to performing adequate reconnaissance on a system before even thinking about launching an attack — any type of attack — and this is no different for SQL injection.

If you want to become a food Instagram star, you may want to consider having babies. Well, to be more specific, you might need Mike Chau's two adorable children, Matthew and Samantha.

When Microsoft release an update to the HoloLens Development Edition at the end of May, there were a bunch of cool new features added in. Among them: New voice controls that make working in the HoloLens operating system much easier.

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

You know what ladies love? A man who can handle his tools. What do the ladies love even more? A man who can say checkmate. Well, except maybe this lady.

Video: . Optimize your Marketing with a Mobile Website

This video explains how you can watch YouTube movies and videos on your iPod. First of all you need to open your web browser and do a search for Realplayer (in this case Realplayer version 11). Next, click on the link for Realplayer. You will need to download and run the installation file. Once the installation has run you need to accept the default and then load your web browser (Explorer or Firefox). From here you can choose any YouTube video you would like then add "&fmt=18" to the url add...

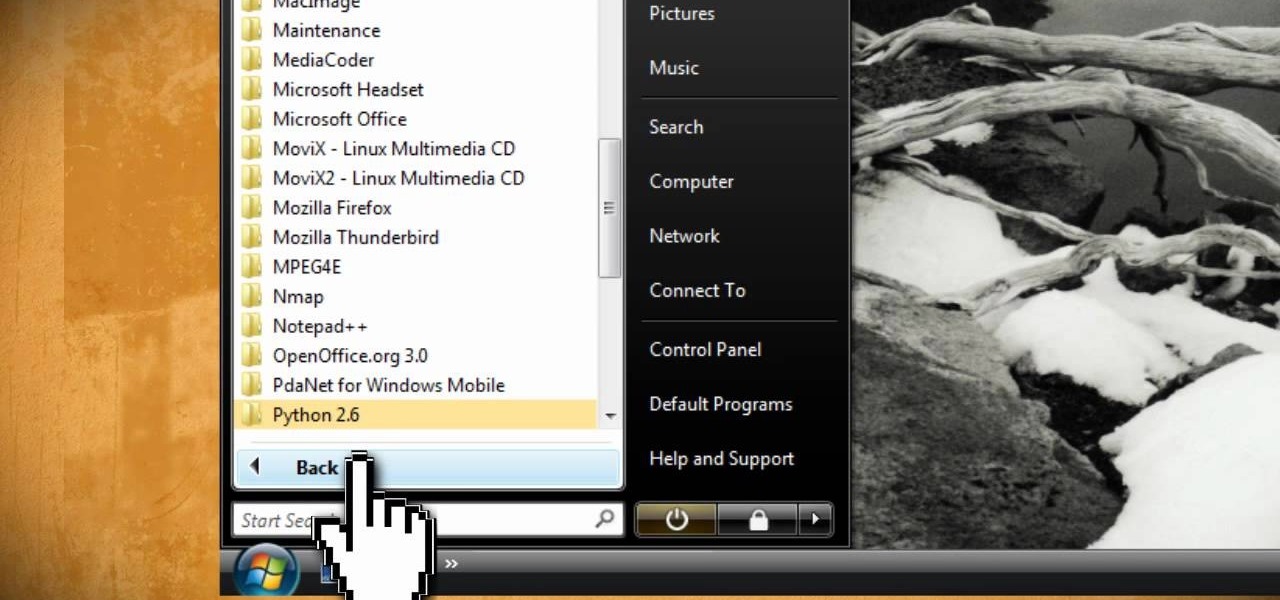
Dr.Quillo from Quillo video tutorial is explaining about downloading high quality wav sound files. According to him this is much more efficient, less time consuming and the result is of higher quality than using Audacity or winrec32. He asks us to use internet browser, preferably Firefox. He guides us through the process of downloading various tools like Mediacoder, virtualdub, fast video download through google or any search engine. Mediacoder is a freeway software device which converts .flv...

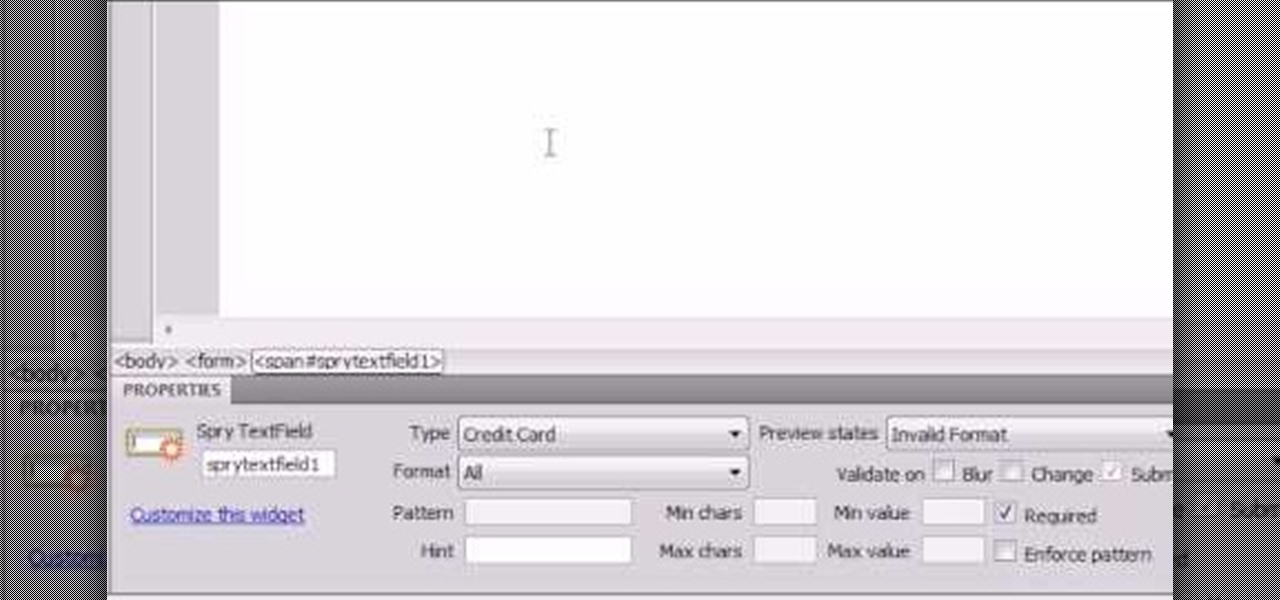
Here the New Boston shows you some tips about using the Spry Validation Text Field. To begin you will go to the Spry Validation Text Field, on Dreamweaver CS4. Looking at the bottom of the page notice the various options that are available for Properties. You find drop-down boxes for Type, Pattern, Minimum or Maximum values, Required, Enforce pattern, Format, Validate on, Blur or Change and Preview States. You can see the types of text available for validating by left mouse clicking the Type ...

Check out this awesome tip from CNET on getting FREE eBooks of the web and onto your Amazon Kindle for easy and cheap reading. They show you the exact process for getting free ebooks for your Kindle, so watch and learn. It's worth it!

This video is about how to download torrent files. The first thing that you will have to do is to open your uTorrent. After opening your uTorrent, open your browser and browse torrent sites that suit you best. Once you have found the site that you like, search for torrent files that you are interested in. Once the results have been displayed, refer to the number of seeds since this increases the download speed. Once you have found the largest number of seeds, click on the title of the file. A...

This is a javascript trick that will work on any website. Just go to the webpage you would like to view go bananas, erase the url from the address bar, insert this code into the empty address bar, hit enter, and enjoy:

Watch this video to learn how to download images from Yahoo using Firefox. 1. Click to open Firefox. 2. Surf or open the Yahoo main website by typing www.yahoo.com. 3. Click the Images tab. 4. Click the Search Box and type the word of the image that you are searching for. 5. Click Image Search tab. 6. Thumbnails of images will appear. 7. Note the name of the file, dimensions, file size and URL. 8. Choose a picture that you like and click on it. 9. The picture will become a bit bigger and will...

This how-to video explains how to copy and paste text in the browser in a Motorola Droid phone.

Tinkernut has all the answers when it comes to MP3 music files, and they're sharing a few of their favorite tips to help you build the ultimate MP3 collection! Watch all three of these videos for the best practices to manage your music files.

To make roman columns, ideal to create space between door and living room. Materials required :