In a previous guide, I demonstrated how to extract images from a security camera over Wi-Fi using Wireshark, provided you know the password. If you don't know the password, you can always get physical with the Hak5 Plunder Bug. Using this small LAN tap, we can intercept traffic like images from a Wi-Fi or IP security camera if we can get physical access to the Ethernet cable carrying the data.

If you're looking into buying shoes from DSW on Black Friday, then you can save an extra 20% — but only if you smile more.

The macOS 10.14 security update tried to make parts of the operating system difficult for hackers to access. Let's take a closer look at how its new feature works and what we can do to spoof the origin of an application attempting to access protected data.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

SSH is a powerful tool with more uses than simply logging into a server. This protocol, which stands for Secure Shell, provides X11 forwarding, port forwarding, secure file transfer, and more. Using SSH port forwarding on a compromised host with access to a restricted network can allow an attacker to access hosts within the restricted network or pivot into the network.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

RouterSploit is a powerful exploit framework similar to Metasploit, working to quickly identify and exploit common vulnerabilities in routers. And guess what. It can be run on most Android devices.

Apple announced upcoming changes today to prevent third-party tracking of users and prevent autoplay, on Safari. Safari will prevent the recording (by anyone other than Apple) of users' browsing behavior, and by doing so prevent advertisers from targeting ads based on individuals' history.

ProtonMail has long been the favorite of journalists and security-conscious professionals, with Edward Snowden the most famous example. But these days, everyone cares about anonymity, so it's no surprise that ProtonMail currently has over 2 million users. And now the service is even better.

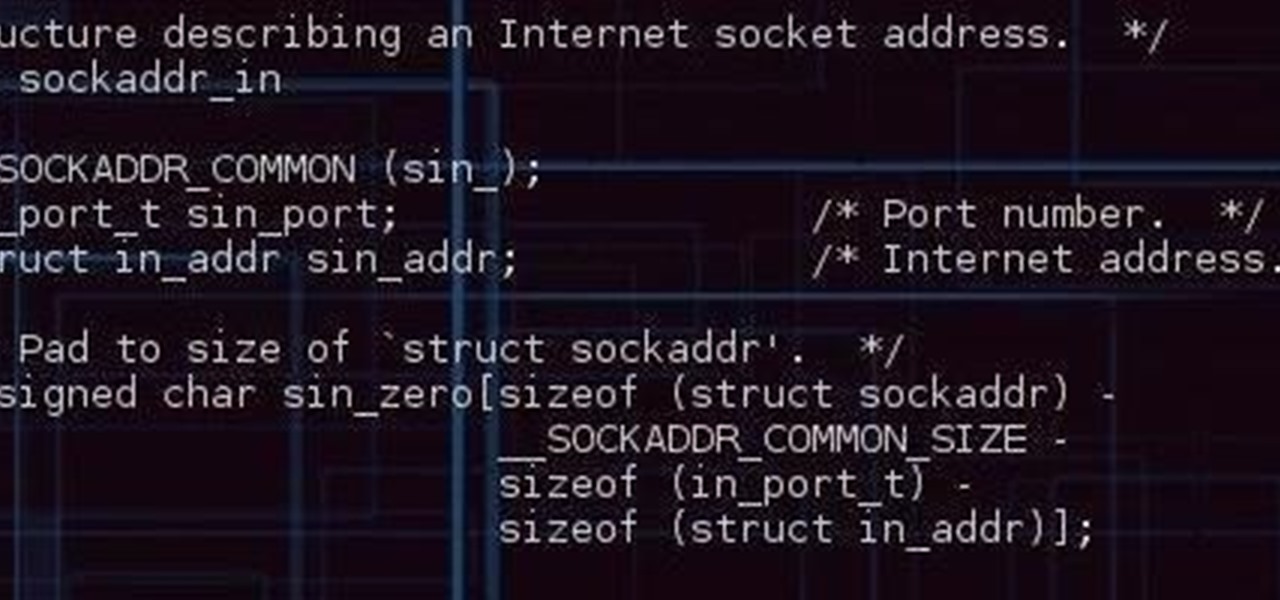
Hello ladies and gentlemen, welcome back to the Part 2 of our UDP & Wireshark adventure as I promised. Last time we discussed about what DNS is and how it uses UDP as its transport protocol but we left some unexplained parts behind and I'm about to investigate those with you. I would advice you to go back to Part 1 so you can have a clear understanding in case you don't feel comfortable with the topic. So our computer made its request to the DNS server and asked "Hey, I want to find out what ...

Alright so last time I gave you a homework assignment. This week we're gonna look at my version of the UDP-Flooder.

Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scanning, with Nmap for port scanning, and with its numerous auxiliary modules, nearly unlimited other hacking related capabilities.

The first time a friend or family member asks if they can borrow your phone or tablet, you probably just hand it over without a second thought. But the second, third, and fourth times? Now it's starting to become a habit, and something probably needs to be done about it.

If you're a U.S. expat living, traveling, or studying abroad, or just someone who typically uses virtual private networks (VPNs) in order to access the North American video libraries of services like Hulu or Netflix, you were probably surprised to see that these video streaming services don't work on your Chromecast or Chromecast 2.

Hello all, this is my first submission to null byte! I noticed something a little strange, particularly that whenever Meterpreter is discussed, it is virtually always in the context of Windows. Granted, the Windows Meterpreter is more powerful than the version that can run on OS X (it has several more commands/options), but I think it is still worth noting how to do it. I've even seen some people mistakenly say that Meterpreter can only be run on Windows, which is not true. Meterpreter can ea...

So, we all probably know that when you run a trojan made by Metasploit, nothing will appear to happen. This is a sign for me to immediately check my Task Manager, but for an unsuspecting victim, it will just seem like a broken file. It is likely that they will delete this "broken file" once they see that it "doesn't work." In order to prevent this, we need to disguise the trojan.

Thanks to a couple of photoshopped images that made rounds across Twitter last year, iPhone users were duped into thinking that iOS 8 included a security feature that would lock individual apps. Of course, none of it ended up being true, but we covered other features and apps that could accomplish roughly the same thing.

When Google released Android 4.2, a new feature was introduced for tablets that allowed for multiple accounts to be used on a single device. In order to create a unique experience for each user, apps and personal data were kept separate, and switching between users became as simple as tapping your profile photo from the lock screen.

Welcome back, my hacker novitiates! In previous guides, we have used one of the most powerful hacking platforms on the planet, Metasploit, to perform numerous hacks. They ranged from exploiting Windows XP and Windows 7/8 vulnerabilities, to installing a keylogger and turning on a webcam remotely. We have even been able to save the world from nuclear annihilation, see if our girlfriend is cheating, spy on suspicious neighbors, evade antivirus detection, and more.

Many of my aspiring hackers have written to me asking the same thing. "What skills do I need to be a good hacker?"

There are several ways to get around location restrictions on subscription sites like Netflix and Hulu using apps, extensions and proxies, but they tend to only work on laptops and computers. Users who want to access content from mobile devices and gaming consoles are usually out of luck.

Since The Guardian published leaked documents exposing the depth of the NSA's spying powers, many people who've never put much effort into protecting their privacy are finally starting to pay attention. Evidence of public opinion concerning PRISM can be seen from the rise in traffic for pro-privacy sites like DuckDuckGo to the petitions demanding that the program be scaled back or done away with altogether. Some would argue that you waive your right to privacy by signing the terms of agreemen...

Welcome back, my fellow hackerians! Today we'll be hacking Facebook profiles on your local network. You may think, "How is this useful, nobody but me is using my network." Well, you can use this on other Wi-Fi networks that are available for free (like at Starbucks) and crack their precious Facebook profile!

Configuring user accounts is extremely important for those with a family shared computer or anyone using a work computer. Assigning different accounts with their own distinctive accessibility, customizations, and applications is the best way to manage a computer with multiple users.

What's your Twitter handle worth? If it's considered "desirable" (aka short and simple), it'll get you around 100 bucks, or, if you prefer, the affections of a teenage girl.

Cashcroppimp teaches you how to open your XBox 360's NAT with Verizon Fios. You first have to find your IP address. For this, you simply point your internet browser to http://findmyip.com to find IP. This is also calling the default gateway. Make sure to write this down somewhere. Now you need to input this number in your internet browser. Enter your username and password and proceed to the next step. Now go to Firewall settings-DMZ Host. Here you will need the IP address from the XBox 360, w...

This video will show you a few easy steps to remain anonymous on the Internet by replacing your ip address for a fake one.

This video will show you how to use the Windows command prompt and ip-address.com to find the location of any website. This is a PC based trick and will not work with a MAC OS.

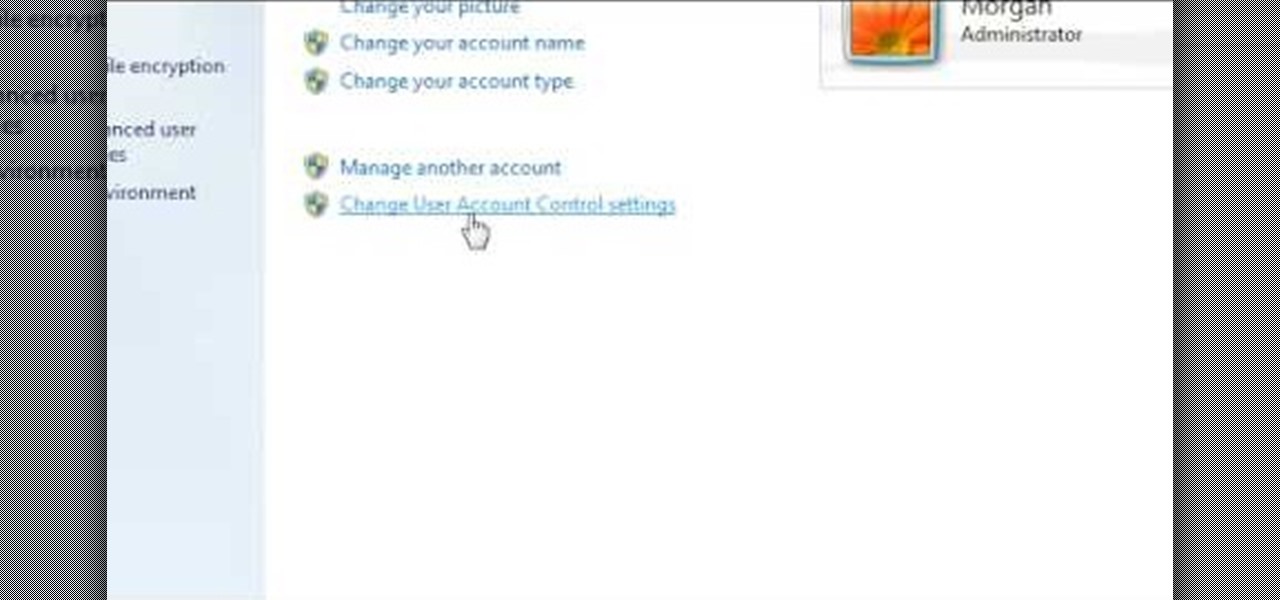
In this video, we learn how to turn off user account control (UAC) in Windows 7. First, go to your desktop and then the start menu. From here, go to the control menu and then user accounts. After this, go to change your user account control settings and a new window will pop up. From here, change the bar from the top to the bottom where it does not notify you, or wherever you want it to be that suits you the best. To finish, you will save this and then exit out of all the windows and your set...

This video describes how to create a new user account on an Apple Mac OS X 10.6 (Snow Leopard) computer to tell whether your Pro Tools problem is user-specific or global. Whether you're new to Digidesign's Pro Tools 8 or simply looking to pick up a few new tips and tricks, you are certain to benefit from this free software video tutorial. For complete instructions, take a look.

This session is about page view sharing. Click collaborate, send collaborate live. It works with Acrobat. It opens a live chat session. Log in with Adobe ID. You can invite others to collaborate. Click to select name, attach a file and send an email. File can be saved on Acrobat. Access can be restricted to those who are invited. Collaborate live panel opens. You can open the invitees computer. Invitee needs to sign in. You have the ability to chat. Start page sharing. Pages are synchronized....

Want to keep other users from accessing certain applications, files or folders? This video tutorial will show you how it's done! It's easy! So easy, in fact, that this home-computing how-to can present a complete overview of the process in just over a minute's time. For more information, including detailed, step-by-step instructions, watch this Win 7 user's guide.

This Blender user's tutorial covers camera movement from camera view, the render panel, and the ambient occlusion panel. Whether you're new to the Blender Foundation's popular 3D modeling program or a seasoned graphic artist just interested in better acquainting yourself with the application, you're sure to be well served by this free video tutorial. For more information, including detailed instructions, take a look.

Microsoft has released its latest rendition of the Windows operating system, Windows 7. Windows 7 succeeds Windows Vista and comes with many improvements and useful updates. To install the update one a personal computer running Windows, a backup of the user's personal files and data onto a detachable hard drive is recommended to prevent data loss during the update process. The ISO image of the Windows 7 OS is burned onto a DVD. A partition is optionally created on the user's computer to allow...

Revision3 Internet Television and Tekzilla Daily with Veronica Belmont demonstrate how to unlock Vista's super user mode. First, open the start menu and type CMD. Right click the command prompt and select the run as administrator option. Type the code net user administrator / active:yes. Hit enter. Your system should reply with the command completed successfully message. Then, the next time you restart your system, you'll see the administrator as an option in the welcome screen. If you use th...

This video shows how to hack the computer password for Vista. We can change the computer password without knowing the actual password. First go to Start menu. Type in the Search "cmd". Then right click on that folder and run as administrator. Then we get a pop up. Type in their net users. Pick the user that we want to hack into. After picking the user type in net user the username and then * . After typing this hit enter key and it should say the command completed successfully and we have to ...

In this video tutorial, viewers learn how to negotiate with a credit card company. There are 3 main items that users can negotiate. The first item is the date of payment. Users are able arrange a more convenient date for payment. The second item is the annual fee. Users are able to work out a way to not have to pay an annual fee for using a credit card, which will help save money. The third item is the interest rate. Users can negotiate and try to lower the interest rate that they must pay. T...

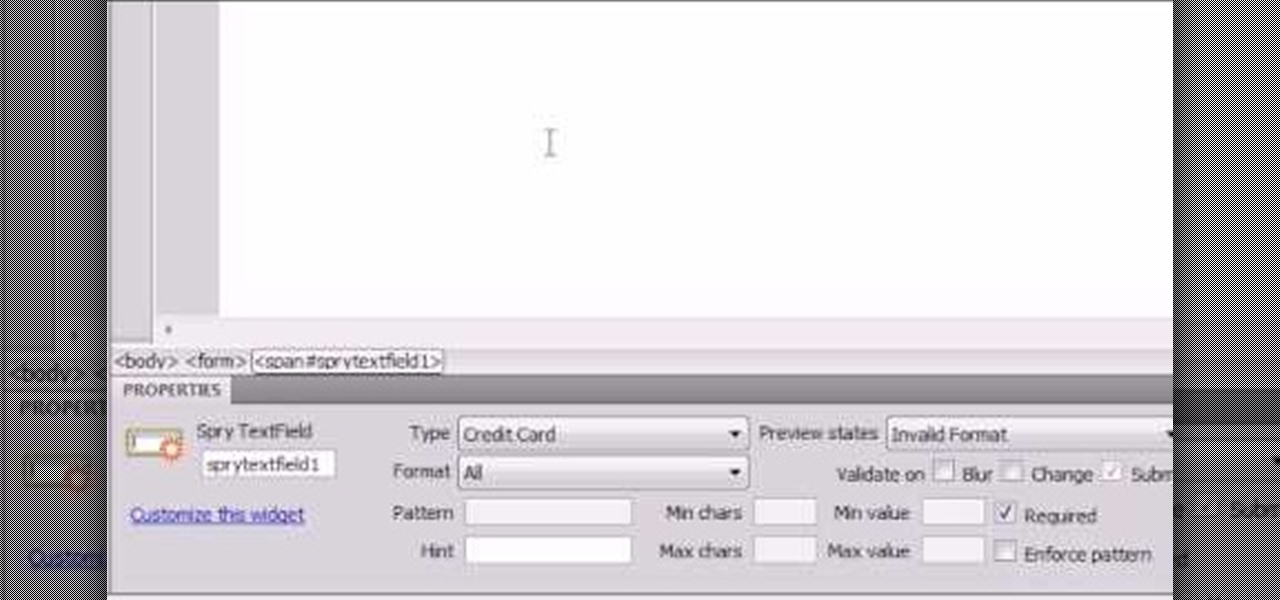
Here the New Boston shows you some tips about using the Spry Validation Text Field. To begin you will go to the Spry Validation Text Field, on Dreamweaver CS4. Looking at the bottom of the page notice the various options that are available for Properties. You find drop-down boxes for Type, Pattern, Minimum or Maximum values, Required, Enforce pattern, Format, Validate on, Blur or Change and Preview States. You can see the types of text available for validating by left mouse clicking the Type ...

HighQuality Tutorials demonstrates how to change your iPod Touch alpine default password. Changing the default password is useful when using your iPod Touch in a public setting to make it less vulnerable to hacking. To change the default password, first open up your internet connection and search for Putty. Download the Putty program. Open and run the Putty program. Your host name will be your IP address for your iPod Touch. Select port 22 and SSH and open up the program. Log in as root and c...

In this video tutorial, viewers learn how to block certain users from seeing their Facebook account. Begin by logging into your account and go to your home page. Click on the Setting tab and select Privacy Settings. At the bottom of the page, under Block List, there will be a space for users to type in a persons name to block and click Block. Select the person from the list of people and click Block. This video will benefit those viewers who use Facebook, and would like to learn how to block ...