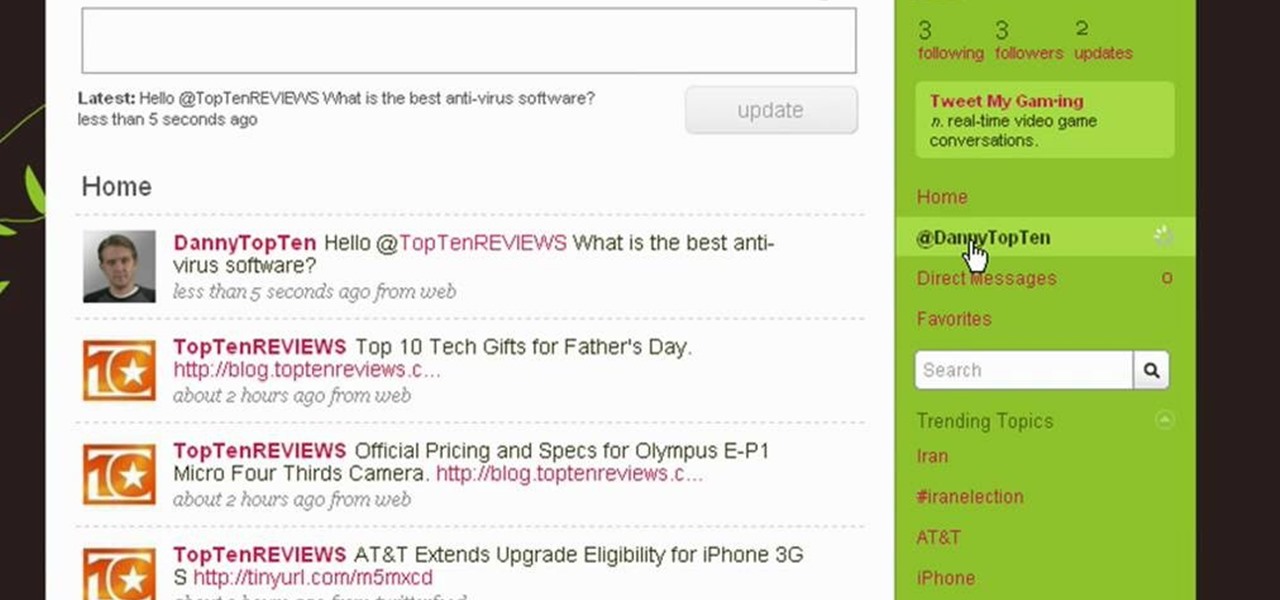
Twitter is a powerful social networking website which can be used to update you friends on what you are doing. To send different messages through twitter you will need a twitter account. Twitter account can be registered for free. Log in to your twitter account and go to your home page. There is a text box provided at the top with the text 'What are you doing?'. Enter the message you want in the text box provided. Click update and this message will be shown to all the people that are followin...

In this video tutorial, viewers learn how to uninstall the program on an Android phone. Begin by clicking on Settings and select Applications. Click on Manage applications. Now users will be revealed a list of all the applications that are installed on the phone. Simply scroll through the applications and select the unwanted application(s). Users will now see the information about the application, click on Uninstall. Now click OK and click OK again when the application is finished uninstallin...

In this video tutorial, viewers learn how to perform hanging knee ups. This exercise targets the abdominal muscles. Users will need to use a smith rack for this exercise. Begin by hanging on the top of the smith rack. Users should have a bar behind the rack that will support the back area. While hanging, users will point the chin down and bring the knees up. Then raise the chin up and bring knees down. Continue performing this movement in a series of sets and repetitions. This video will bene...
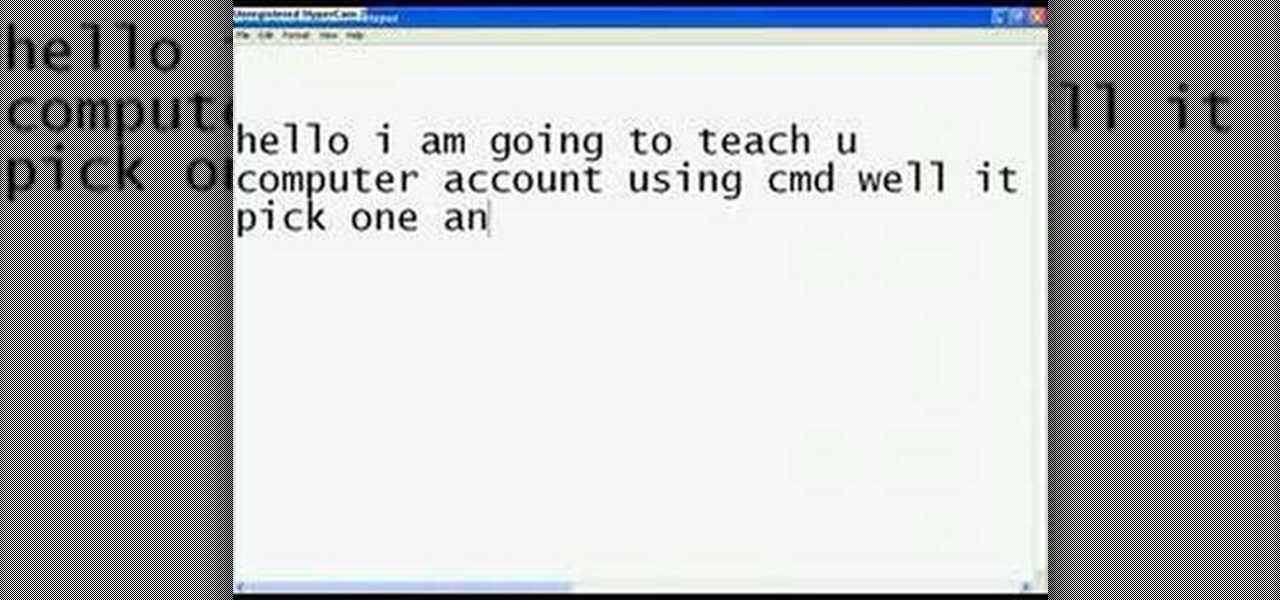
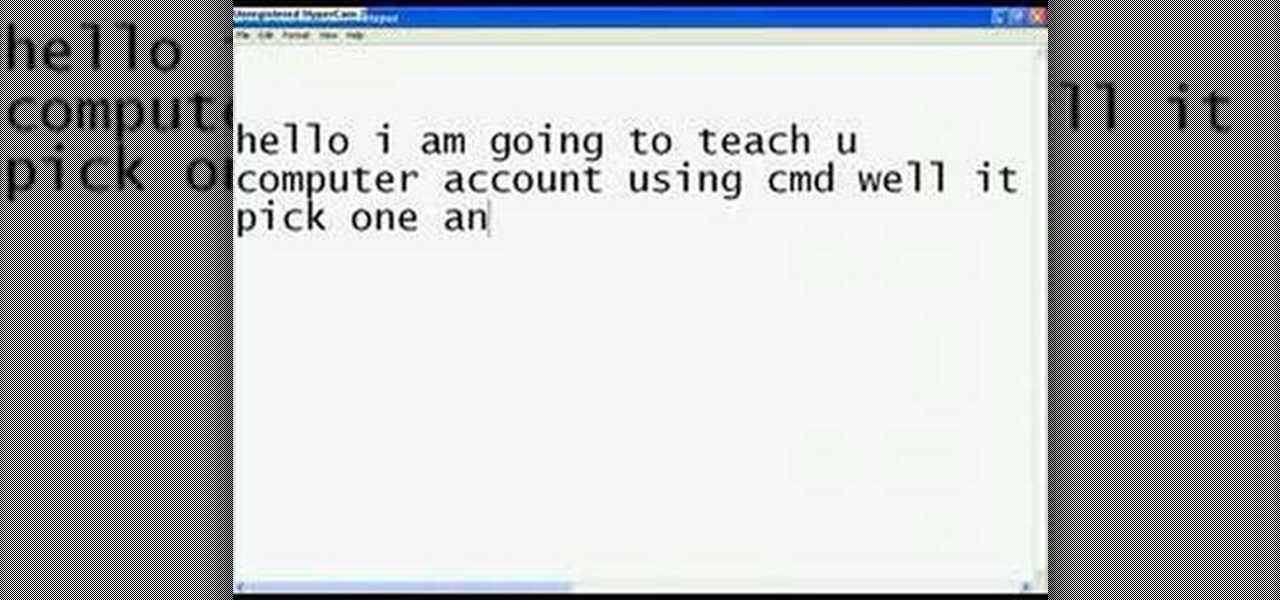
This video teaches you how to change your computer's account password using the DOS command prompt. The first step is to get to the command prompt, you can do this simply by clicking run in the start menu and typing "cmd." You next type "net user" which will show you all of the user accounts on the computer. Choose the one you would like to change the password for and type "net user (account name)." It will then ask you for a new password, you may type anything you like here keeping in mind t...
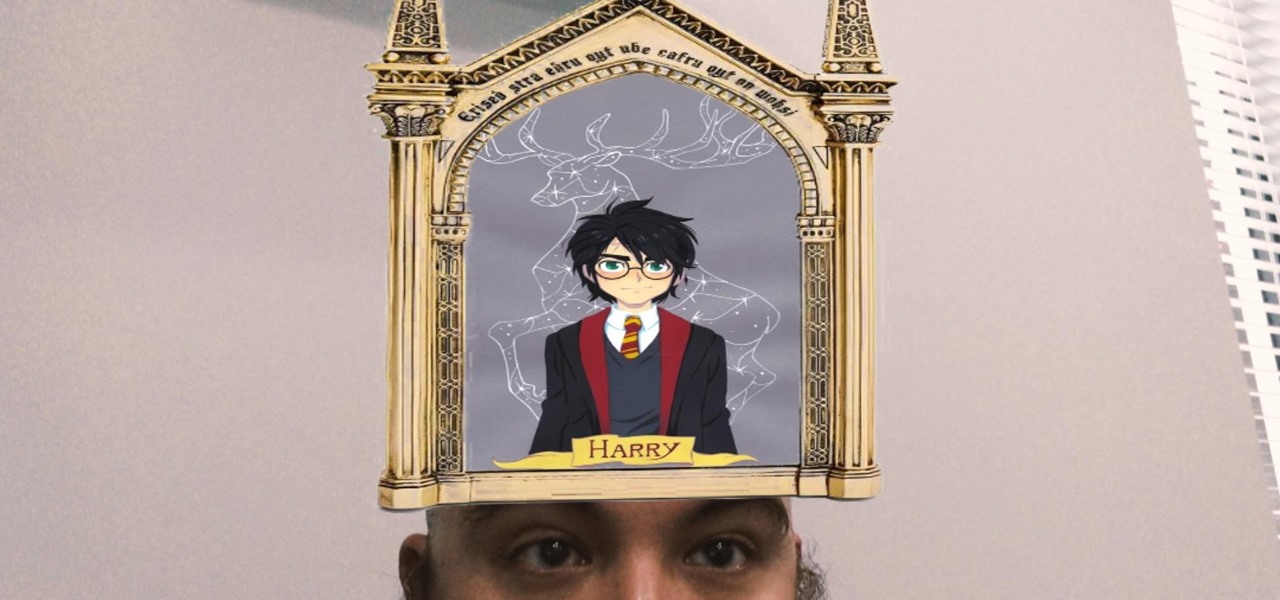
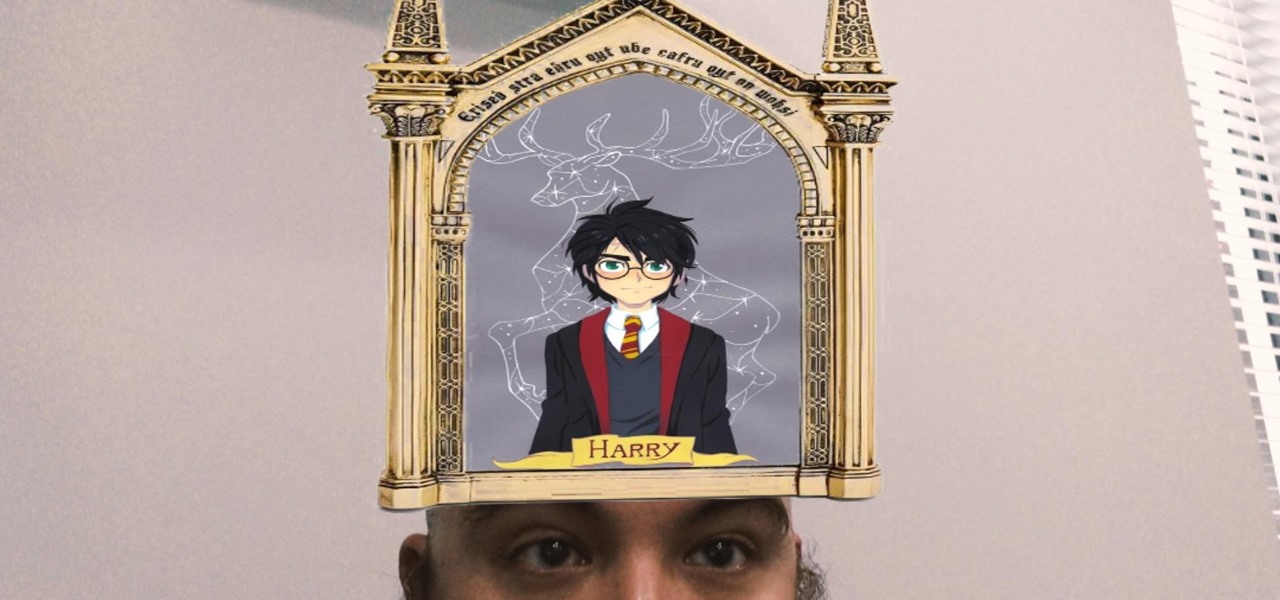
The developer who gained notoriety for his What Disney Are You? augmented reality filter on Instagram is striking again while the iron is hot.

It may take practice to get to Carnegie Hall, but a new mobile app gives the average iPhone or iPad owner the experience of walking on stage with a live orchestra.

In recent months, the Magic Leap One has frequently tied promotions to groundbreaking entertainment properties, but the latest may be the startup's biggest coup yet.

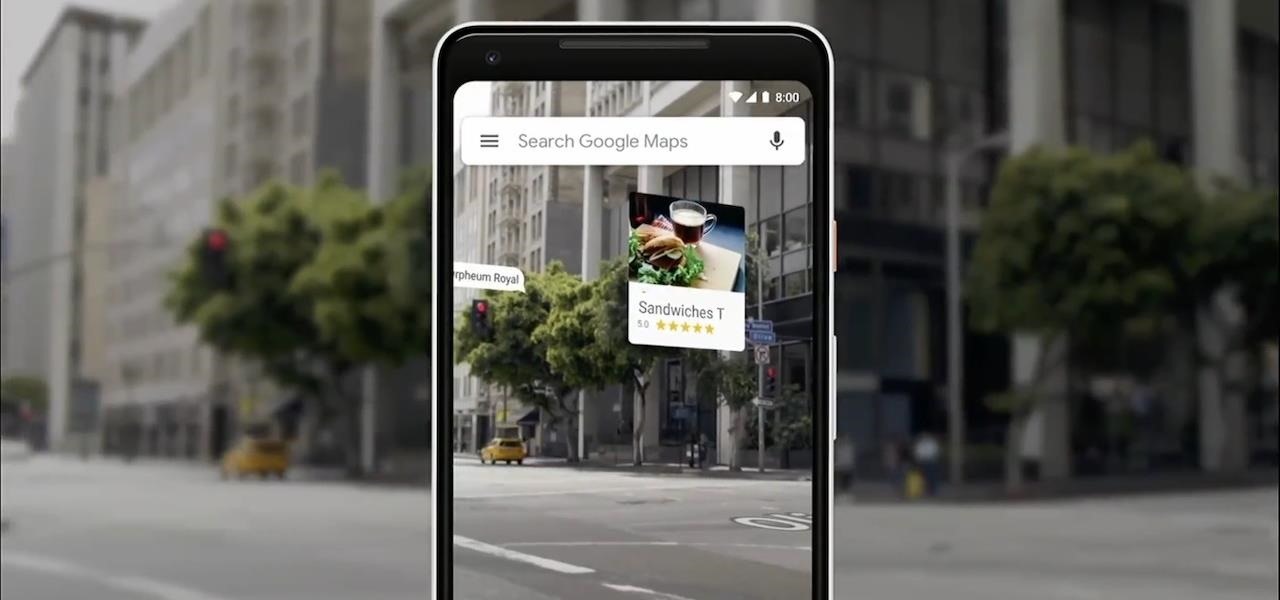
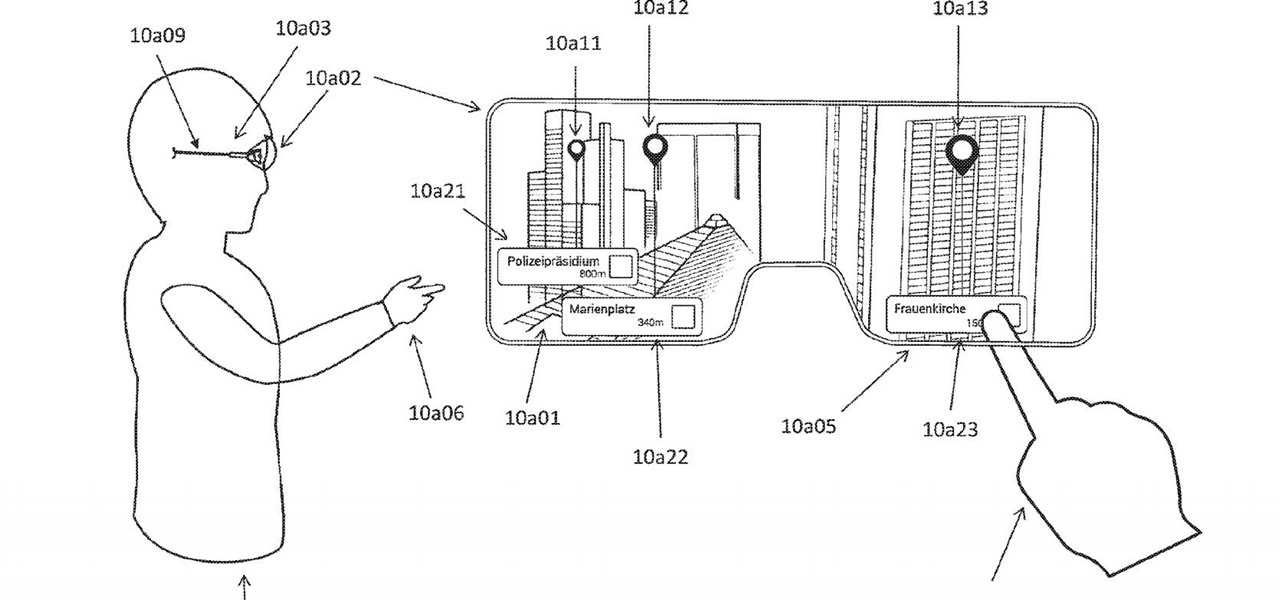
The augmented reality walking navigation mode for Google Maps appears to be closer to an upcoming release for the general public.

In the realm of internet security, it's becoming clear that augmented reality is not immune to the increasing wave data breaches plaguing users.

For the entirety of its existence, Snapchat has lived on mobile, but in its quest to lead the augmented reality industry, the company is now bringing those mobile AR experiences to desktops.

We've seen all the Magic Leap One glamour shots, and we've even shown you a bit of what it looks like to view augmented reality on the device. But there's something else us super geeks appreciate more than anyone else: the grand unboxing!

Augmented reality avatars that mimic facial expressions are no longer the exclusive province of Animojis on the iPhone X or AR Emojis from Samsung. Camera app Snow has added its own alternative to Apple and Samsung's features, which it also calls AR Emoji, for iOS and Android.

When it comes to augmented reality apps, visually immersive experiences are plentiful, but audio experiences are somewhat underrepresented. A new app for iPhones and iPads seeks to shift the AR paradigm toward the latter.

For social media platforms like Facebook, augmented reality represents a whole new art form with which users can express themselves online. Now, Facebook is giving those users a new brush.

A Swedish digital artist has developed an app for the iPhone X that creates mind-bending 3D illusions that correlate to the user's point of view.

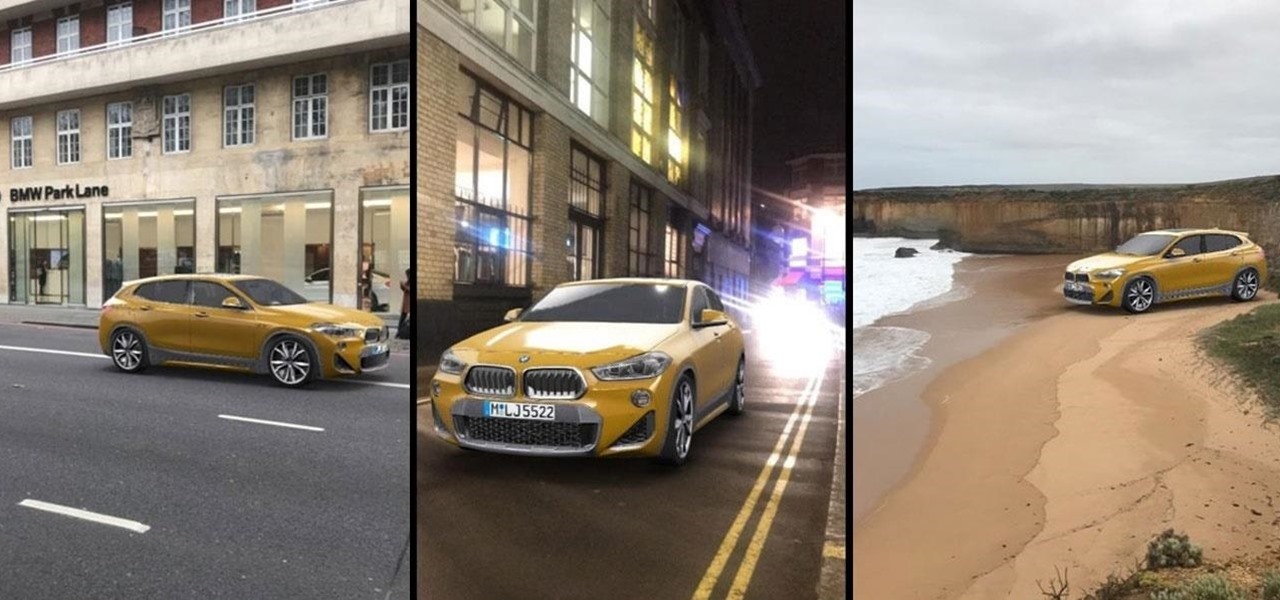
Snapchat has broken new ground in its augmented reality advertising efforts, as BMW has opted to show off its new X2 model in AR with the Augmented Trial Lens.

Online glasses retailer Warby Parker built its reputation by selling fashionable yet affordable eyeglasses, so it perhaps a surprise that it's one of the first developers to take advantage of the technology in the least affordable iPhone yet.

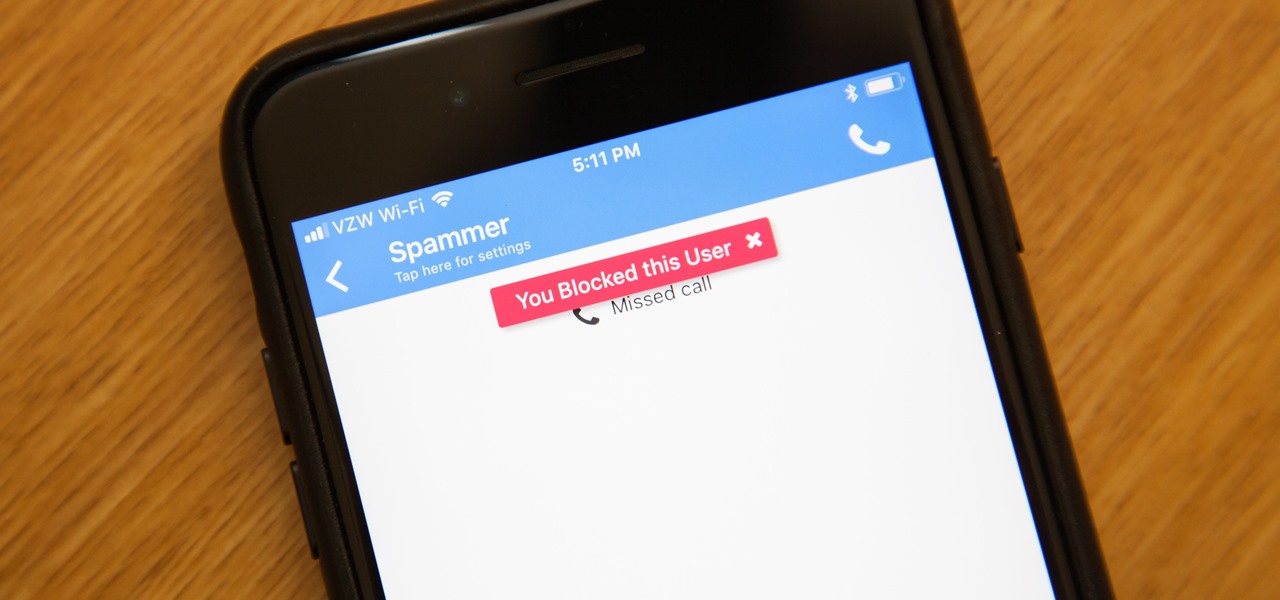
While it's a more secure platform for messages and calls, Signal's job isn't to prevent unknown users from contacting you, so you run into the same issues you would with a regular phone number. People you know that you don't want to talk to may try to strike up a conversation and you'll still get spam messages. Luckily, it's easy to block these suckers.

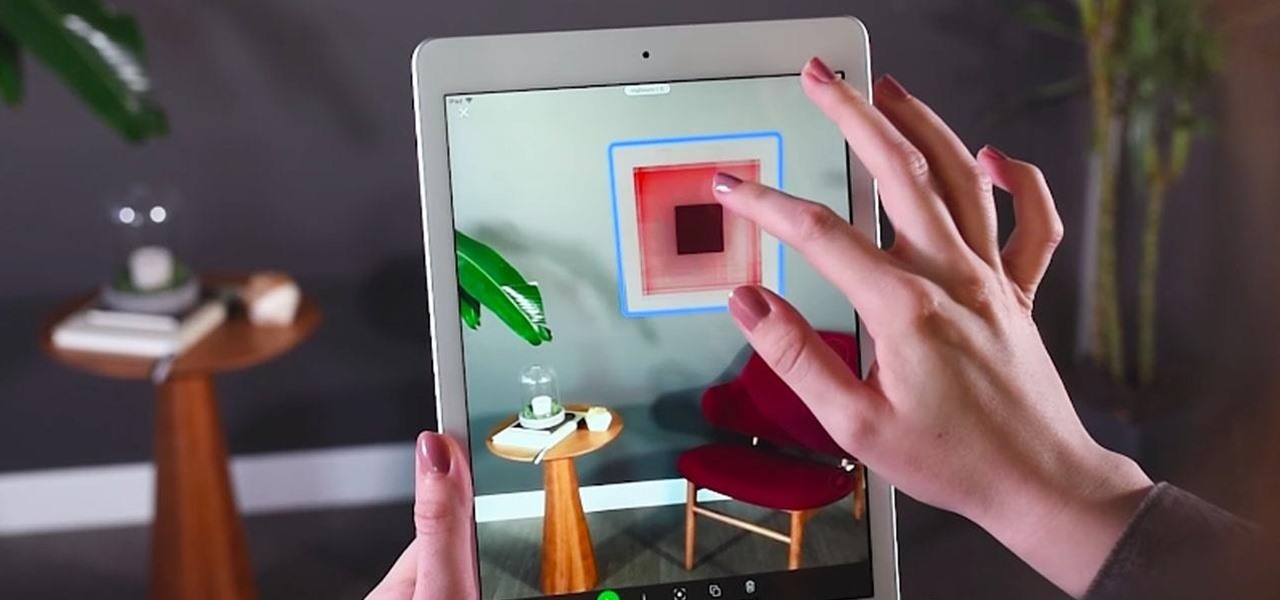
Apple has sprung a massive AR following since the announcement of their ARKit, with users waiting to see what exactly the tech giant will do next.

iCloud can occasionally be the worst part of being an Apple user. It's useful for backing up your information, however, sometimes the problems that stem from Apple's cloud service are so tremendously frustrating they almost seem intentional. Well, buckle in, because it's possible there may be a widespread login issue.

Cruise Automation is actively seeking to recruit a lead engineer to head its development efforts of 3D maps with expertise in city environments, signaling the GM driverless unit's move towards a mobility-as-a-service business model.

Nissan began to offer Level 2 driving capacities in a mainstream model when it debuted its ProPilot self-drive option for its Serena minivan in Japan last year.

To celebrate its tenth anniversary, PornHub has just exposed all of our porn habits. All. Of. Them. Before you panic, no individual information has been released. Instead, PornHub has exposed the adult video trends and preferences of a variety of demographics.

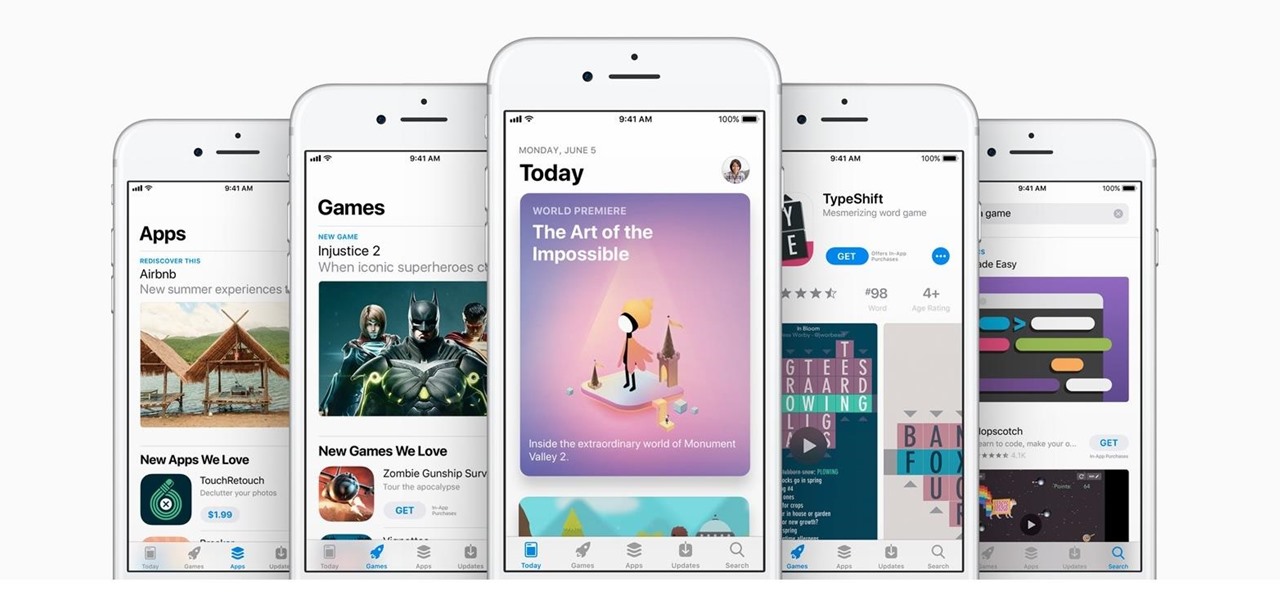
In the changes to the App Store Review Guidelines for iOS 11, Apple has announced that developers must use the App Store rating API. The API was introduced in the iOS 10.3 beta period as something that would eventually become mandatory. Now, Apple has followed through on that promise.

Google, the company that rules the internet, is now testing a method to leverage its machine learning with its ubiquitous presence on mobile devices. The new model they're employing is called Federated Learning, and it hopes to apply artificial intelligence to Google's services on Android without compromising user privacy.

It's happened to all iOS users: You're talking to a friend or watching TV, and all of a sudden, you hear "I'm not quite sure what you've said." Apparently, your phone heard something that resembled "Hey, Siri," and activated the assistant. But now, thanks to a new patent from Apple, the days of unexpected Siri may be numbered.

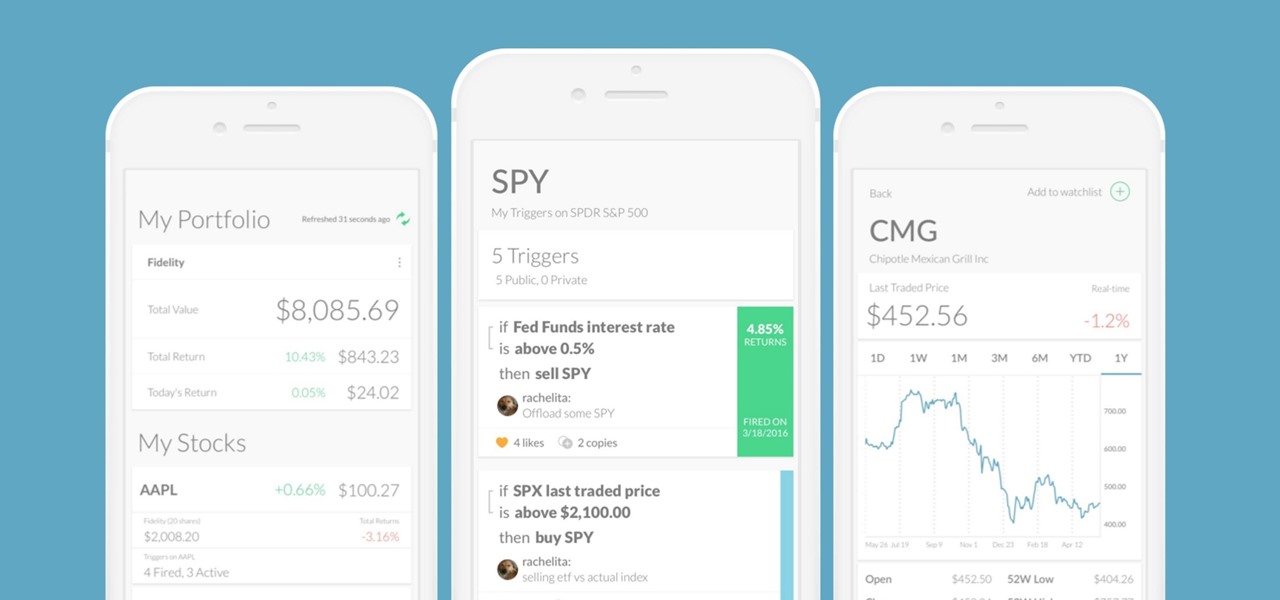
Every time Donald Trump tweets about a stock you own, Trigger Finance, or just Trigger—the app founded on the "if this, then that" rule to track and invest in the stock market—alerts you with a notification for real-time analysis of financial data.

Reading through various internet forums, it certainly sounds like the Google Pixel and Pixel XL are attracting more iPhone users than any of Google's previous Nexus devices. The sales figures seem to back that up, too, as the Pixel is outpacing last year's Nexus 6P, and pre-order demand has exceeded Google's expectations, causing delays in shipments. (We reached out to Google but they wouldn't give us any specifics on sales numbers or numbers of switchers.)

Avocados aren't just having a moment—they're having an extended stay in the spotlight. From mainstays like guacamole to buzz-worthy variations of avocado toast, this silky green fruit is the Hulk of the food world right now. I, for one, welcome any avo-centric trend with open arms... and an open mouth, of course.

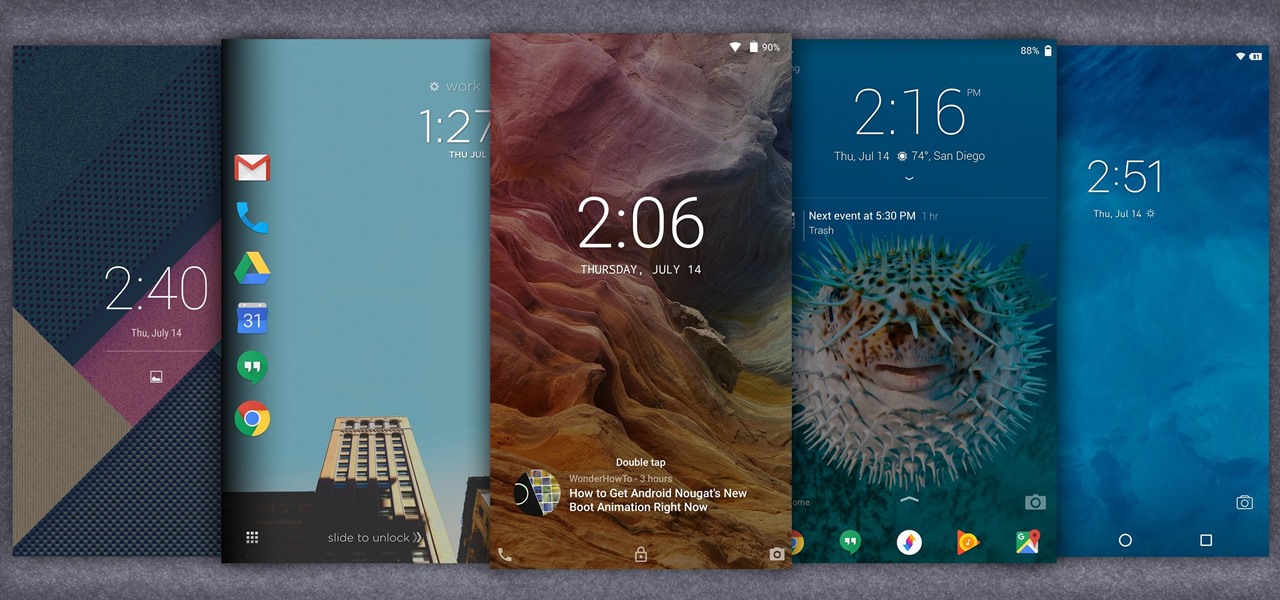
When it comes to customization, you just can't beat Android. Not only can you replace your home screen, switch your default apps, and apply icon packs, but you can even replace your entire lock screen by installing a simple app. Considering that the lock screen is the first interface you encounter when you pick up your phone, that last one might even be the biggest change you can make without root access.

It's hard to argue with the notion that wine and pasta are a winning combination. I mean, millions of Italians can't be wrong.

We used to saunter into the grocery store and gaze longingly at the pre-made roasted chickens, wistfully thinking of things we could do with the golden fowl if only we didn't already have dinner plans.

The morning started out like most of them do: I was hungry, and it was time to chow down on some breakfast. However, this particular morning had me craving something besides the usual milk and cereal.

In the last iteration of how to train your python, we covered basic string manipulation and how we can use it to better evaluate user input. So, today we'll be covering how to take user input. User input is very important to scripting. How can we do what the user says if we can't tell what the user wants? There are multiple ways to take input, we can give the user a prompt and take input from them directly, or we could use flags/switches, and take their input before the script is even execute...

Like most people who spend a good deal of time in front of their computer—whether for work, school, or play—I jump back and forth from window to window, working and playing with different things at the same time to get my work done faster or procrastinate harder.

Welcome back, my tenderfoot hackers! Hacker newbies have an inordinate fixation on password cracking. They believe that cracking the password is the only way to gain access to the target account and its privileges. If what we really want is access to a system or other resources, sometimes we can get it without a password. Good examples of this are replay attacks and MitM attacks. Neither requires us to have passwords to have access to the user's resources.

A recent update to Google Chrome replaced the colored avatar menu in the top-left (Windows) or top-right (Mac) corner of the browser that let you easily switch from profile to profile with a plain gray button that simply names what profile you're in.

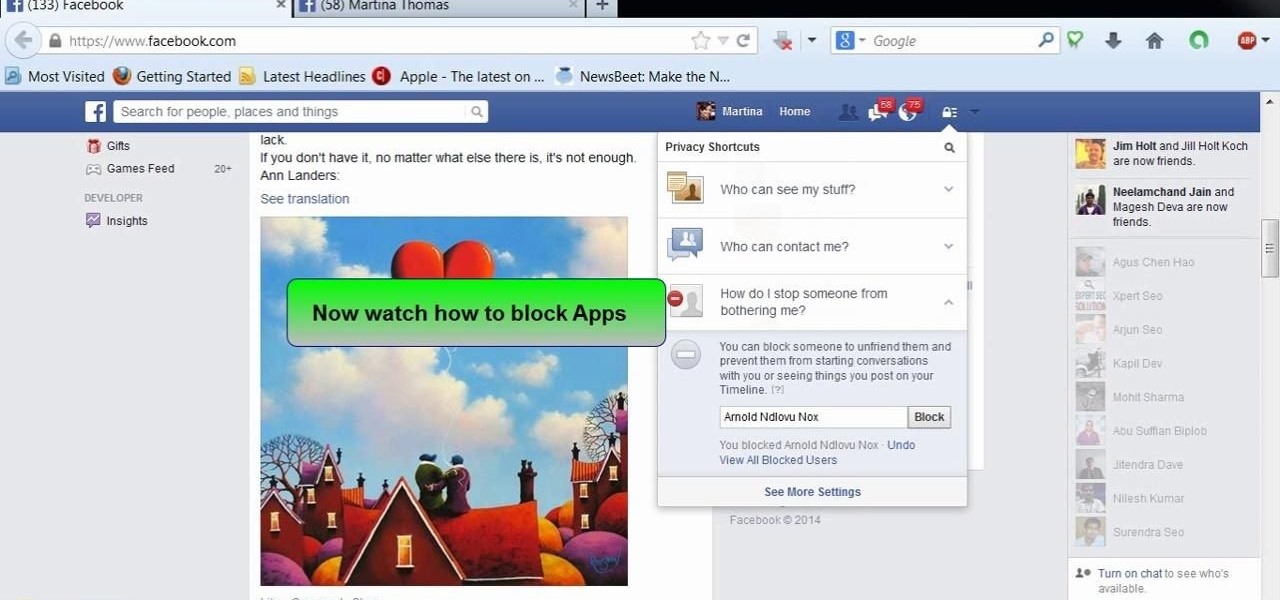
This video will show you how to block users and app invites on Facebook. You can also block apps from sending you notifications. If you accidentally blocked any user or app you intended you could unblock them easily. So please watch the video and employ the technique in your Facebook account.

This video will help you how to disable user account in windows 7. This is very easy to employ. Watch the video and follow all the steps to disable user account in your PC.

Instagram recently released their new Instagram Direct messaging feature in their Android and iOS apps, which lets users share private photos and videos directly with individuals or groups of up to 15 users. However, there are no restrictions on who you can send private photos or videos to.