This video shows you how to easily remove the Security Tool virus. The first thing you have to do is restart you computer. Once restarted, immediately hold down CTRL+ALT+DEL. In the Task Manager you should see: Security Tool. Quickly end it now. The virus is temporarily disabled. Now go to: Download and install Spyware Doctor. Scan your computer and click Fix All. It will ask you for an account...
Moniquewade will show you how to upload photos and videos to Facebook by using email. The user has seven steps for you to follow in order to upload photos and videos to Facebook using email services very fast and easy. The first step starts out by telling you to go to Facebook.com. By following each of the seven steps that are provided, you should be able to send different types of photos and videos to your Facebook account just by using email.

In Call of Duty 4: Modern Warfare 2, there's a glitch that you can take advantage of when you have both a javelin and a grenade in your hands. Modern Warfare 2 is pretty much the game of the moment, of the year, of the decade, so exploit this glitch while you still can! Fair warning, though: doing this glitch could get you banned by the powers that be at XBox Live.

The Visual Prototyper is a wireframe design solution that allows you to design a fully functional application wireframe and simulate it.

"Facebook is a social utility that connects people with friends and others who work, study and live around them. People use Facebook to keep up with friends, to share links, to share photos and videos of themselves and their friends, and to learn more about the people they meet." -- Facebook

Want to mix and scratch like a professional DJ? To be a good DJ you need to understand the concepts of mixing tracks, adding cool effects, and of course you need a good sense of rhythm to line up the beats. This how to video explains how to use the American Audio CK1000 MP3 & CD player mixer combo. This video takes a small look at this twin CD/mp3 player. It has all the essentials needed for any DJ. To be honest, the feel and the user friendly look of it makes it perfect to take on the road t...

This innovative handset makes user convenience its priority. Created with the aim of overcoming the limitations of existing mobile phones, every function is available through a flexible layout of navigation keys. Fixed keypads are a thing of the past with the LG KF600 Venus cell phone.

Scosche Industries offers this instructional users guide for its TA07 radio replacement interface in a 2007 Toyota Tundra. The TA07 will work with select 2004 and up Toyota vehicles equipped with JBL and JBL Synthesis systems. The TA07SR radio replacement interface was designed to make installation of any brand name aftermarket head-unit simple. The TA07SR allows the customer to replace the factory head unit with an aftermarket head unit and utilize their factory amplifier without having to "...

Spammers are the bane of every email user. No matter what you do, junk mail always breaks through the spam filters. And some of the best ones seem to come from legit companies, and that's because they aren't legit companies— they're spammers masquerading as legit companies.

Ok first thing first, you need to download the HackPack. In there is necessary things I use in the video. If you are on XP you must install .net frame work. ( the dotnxfx file) vista users don't have too.

Everybody's hacking these days. Everybody wants to be a hacker, but that's what happens as technology becomes more and more accessible. Hacks are due to a lot of things. The main point is that you allow your user to access your WordPress Admin section or any section. So, may a problem could come with your user or writer. So, you must know about your login details and failed login details. Then only do you know about your user and what they are doing in your WordPress Admin section.

On Monday, the social media giant Facebook suffered a massive outage that, as of this writing, is still in effect.

Yo dawg, Snap heard you using Snapchat augmented reality Lenses in your messages, so it's putting its AR Lenses in other messaging apps.

Mobile augmented reality for iOS typically comes through apps via ARKit, but Apple is borrowing a few pages from Google's playbook and bringing AR directly to iOS 15.

Apple released the newest update for iPhone, iOS 14.5.1, today, Monday, May 3. The update (build number 18E212) is the first since iOS 14.5, which Apple made available one week earlier on Monday, April 26.

Becoming a successful web developer is more than knowing coding languages. Learning to craft functional, intuitive designs is as much coding as knowing how the user will interact with what you've built. The Complete Become a UI/UX Designer Bundle can take you from introduction to mastery in designing the best user experience, and right now, it's only $34.99.

Google Poly, a repository of 3D objects for use in AR and VR experiences, is the latest Google offering to fall victim to the company's habit of axing products and services, regardless of popularity.

Your TikTok videos might be interesting, creative, fun, and appealing, but that doesn't necessarily mean you want the entire world to see them. While you're fine with strangers watching your videos, you may not want your close friends, family, and coworkers to see the kinds of mischief you're up to.

Every video you like on TikTok, whether it's a stranger performing a series of choreographed movements or a celebrity showing off their new workout, is saved to your profile. If you want to watch your liked videos at any time in the future, you can easily do so from your profile — but so can everyone else.

You may think you know Microsoft's apps, but did you know that you could be using them as a power user and make yourself way more productive in the process? Thankfully, the easiest way to master them from home is on sale right now, as The Premium Microsoft Office & Data Apps Certification Bundle is on offer for just $39.99 — a huge 97% off the regular price of $1,782.

The iOS 14.4 developer beta was pushed out a day ago, and now the iOS 14.4 public beta is out and ready for your iPhone. At first glance, there's not much to look at in the new beta release, and it's not yet known if it lays out the groundwork for missing features such as 5G data with dual SIMs, shared third-party app subscriptions, and Xbox Core Controller.

At the opening of its virtual Lens Fest, taking place Dec. 8-10 and open to the public, Snap is furthering its facilitation of AR development with new tools for Lens Studio version 3.3 and a planned investment into its AR creator community.

The true crime genre has long been popular on television and more recently on podcasts with shows like Serial.

If you want to be truly competitive and successful in the world of web and app development, it's not enough to simply know a handful of programming languages and coding platforms. Today's best sites and apps require pro-level graphics and user interfaces, and knowing how to work with a wide range of graphic design tools is essential if you want to land lucrative positions as either an employee or a freelancer.

Linux has been one of the most popular desktop operating systems for nearly three decades, ranking fourth in the world behind Windows, macOS, and Google's Chrome OS. The open-source operating system is loved for its quick, powerful, text-based interface and efficient communication tools.

Instagram makes it easy to view a public account without that person or business knowing unless, you know, your finger accidentally slips and hits the like button on a post. Aside from that, if you're careful, you can browse anonymously through an account without anyone noticing — only you can't do that with Instagram Stories.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement.

It is a scary time to be alive. As states start to ease back shelter-in-place restrictions, the new world you're entering is still unsafe. With a vaccine months away, your best bet is to follow CDC guidelines and use the tools at your disposal.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

Hacking web applications can sometimes be challenging due to the sheer amount of moving parts they possess. At the core of these apps are HTTP requests and parameters, but these things are often concealed from the user, due to security reasons, convenience, or both. However, a tool called Arjun can be used to discover hidden HTTP parameters in web apps.

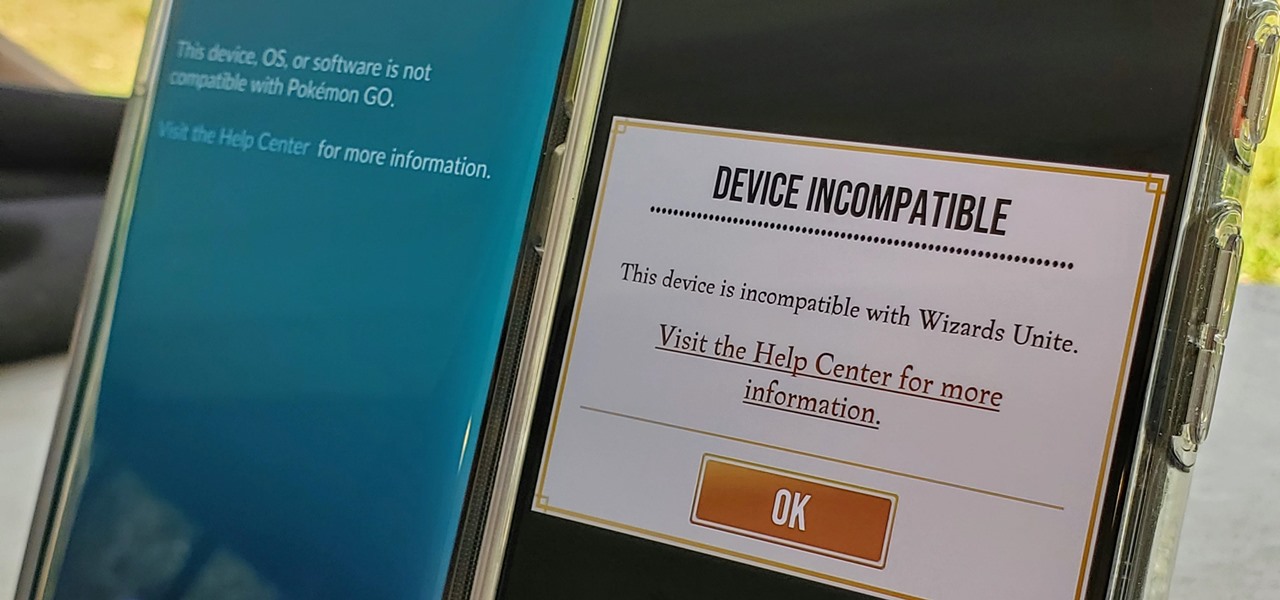
Both Pokémon GO & Harry Potter Wizards Unite are augmented reality games developed by Niantic, and neither needs much introduction. Pokémon GO, all by itself, created a worldwide phenomenon that still carries a strong fan base years later — Wizards Unite is working on doing the same. However, things are not all fun and games, as you might think in the world of monsters and magical creatures.

Are you thinking about upgrading your iPhone this year? Apple sure wants you to. Of course, that's no different than any other year, but Apple really wants you to upgrade this year. How do we know this? The rumors point to not three, not four, but five brand new iPhones in 2020, with two very different release schedules. All this begs the question what the hell is Apple thinking?

After facing reports of financial troubles over the past month, Magic Leap came out swinging this week with a big push for the enterprise segment of AR, including a repackaged Magic Leap 1, a suite of enterprise apps, and updates to Lumin OS and its supporting development ecosystem. Oh, and its AR headset managed to win a starring role in the marketing juggernaut for the forthcoming Star Wars movie.

The wearables space experienced its "big bang" moment back in 2015 when Apple released its first wearable device, the Apple Watch. Although the device was initially dismissed by some as an unnecessary charm bracelet packed with frivolous tech, in very short order, the public learned just how useful the Apple Watch can be.

There's a direct correlation between the proliferation of augmented reality apps and the demand for 3D content, and PTC just quantified that in dollars.

If you have friends who aren't privacy-conscious, you've surely heard the old "What do I have to hide?" excuse. Despite the fact that billions of people are using the internet each day, many of them don't know the dangers that can find them. And many don't know the tools to combat them.

Move over, Star Wars. You're not the only Disney property that can play in the Lenovo Mirage AR headset anymore.

|Choose Your View: Quick Bullet Points | Detailed Descriptions Android's newest major update is a special one — it's the tenth full version of the world's most commonly used operating system. The latest release, dubbed simply Android 10 (codename Android Q), was first showcased as a beta back in March 2019, so we've been digging around in it for several months. There's one dramatic visual change, plus there are a lot of goodies in general.

One of the most common web application vulnerabilities is LFI, which allows unauthorized access to sensitive files on the server. Such a common weakness is often safeguarded against, and low-hanging fruit can be defended quite easily. But there are always creative ways to get around these defenses, and we'll be looking at two methods to beat the system and successfully pull off LFI.