Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Your freezer is no one-trick pony. While it does excel at keeping your food fresh for as long as possible, it has a few secret talents it doesn't want you to know about. Like making soda slushies and pyro-friendly smoke mix, as well as reviving dead hard drives. Even better—it can help you do laundry.

Shortly after Apple's iOS 8.0.1 update fiasco ruined many iPhone users' cellular reception (which was fixed with iOS 8.0.2), developers were treated to the first beta release of iOS 8.1, which will be the next big update for iPad, iPhone, and iPod touch.
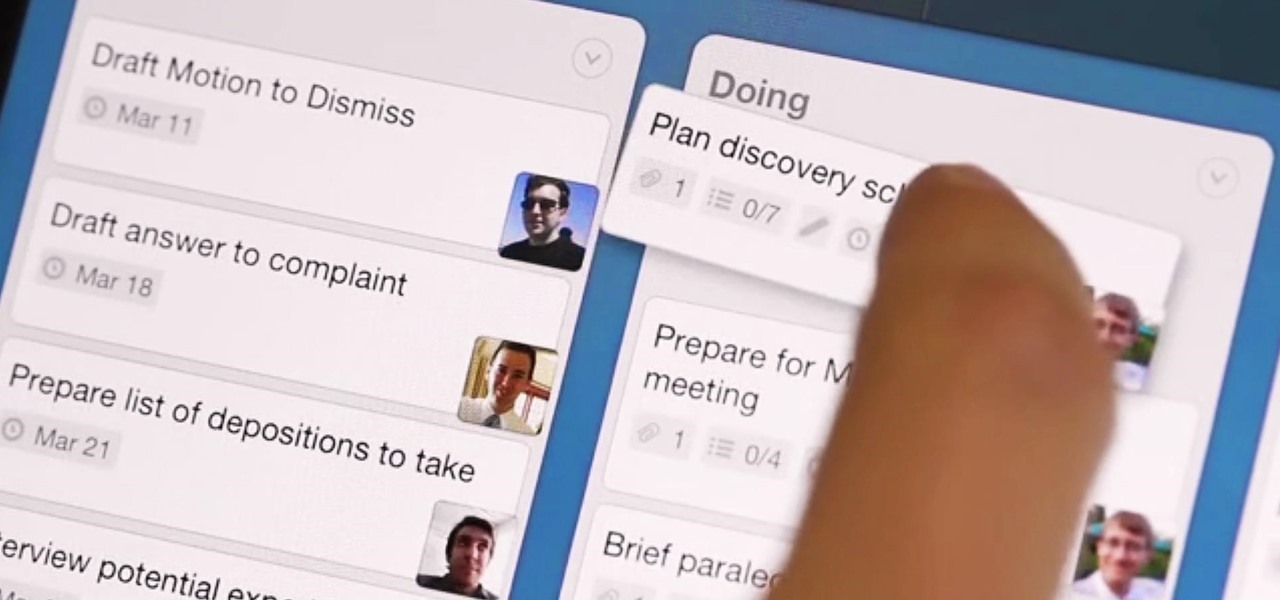
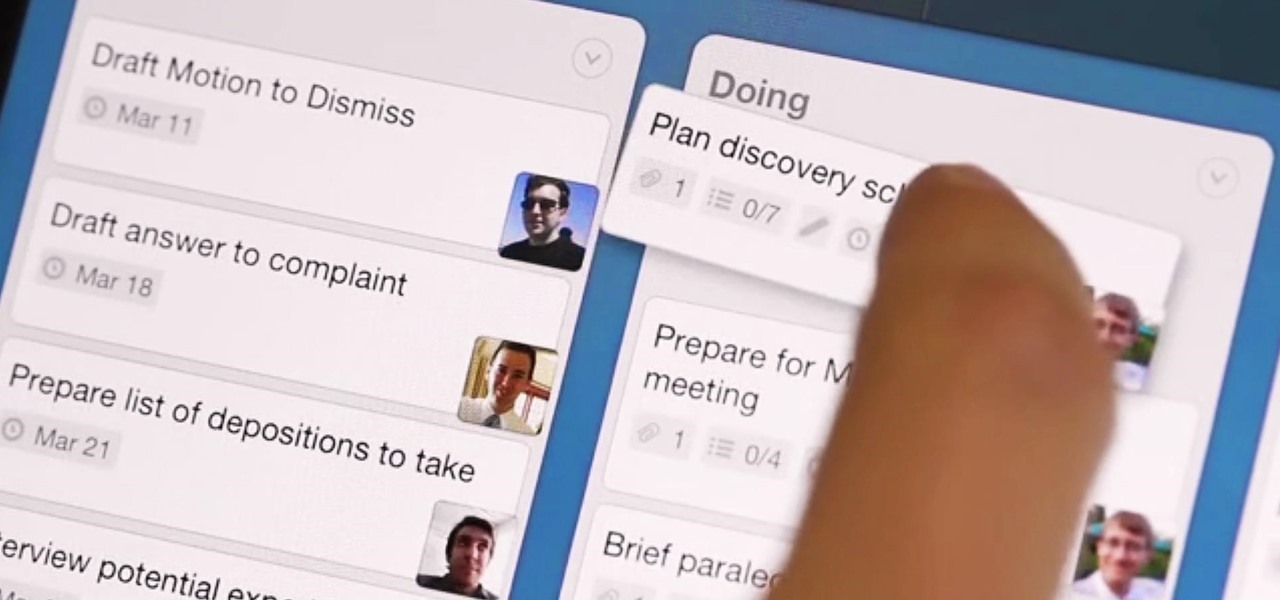
What separates the work habits of the ultra-productive from us mere mortals struggling to check items off our never ending to-do lists? While the answer to that question is by no means simple, one undeniable factor in their success is a clearly defined, highly organized workflow.

Welcome back, my greenhorn hackers! I recently began a series on scripting and have received such positive feedback that I'm going to keep this series going. As I've said before, to graduate from the script kiddie to the pro hacker, you'll need to have some scripting skills. The better you are at scripting, the more advanced your hacking. Ultimately, we are leading up to developing the skills to build your own zero day exploits.
There has been much talk about how unsecure the cloud is because of PRISM’s newfound ability to demand all of your data without any resistance. This has spin doctors in the Cloud Storage industry losing their mind. They suddenly went from a central hub for 10GB of your files, to an easy window for Big Brother to track you through. Centralized cloud storage is no longer a safe way to keep your files, but we still need a way to access our files anywhere we go.

Welcome back, my novice hackers! Most of my tutorials up until this point have addressed how to exploit a target assuming that we already know some basic information about their system. These include their IP address, operating system, open ports, services running, and so on.

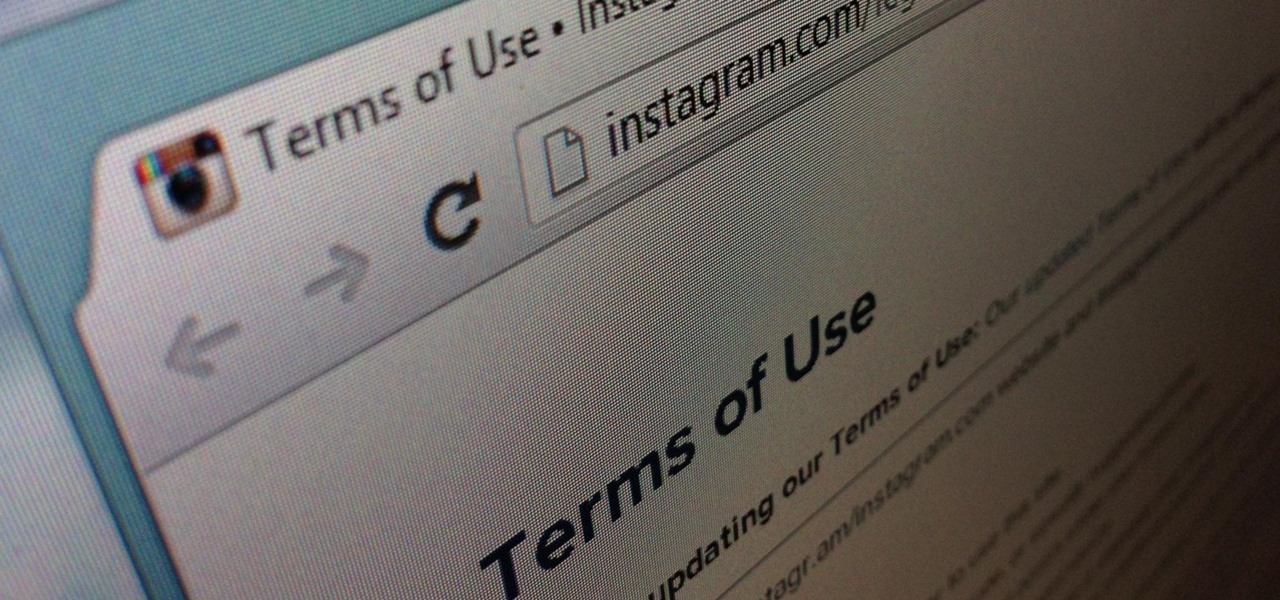
Instagram's controversial terms of service update this past month has spurred an onslaught of dismay and anger from users of the popular photo-sharing social network. The specific set of the new terms that set off this firestorm basically said that businesses could use your uploaded photos for advertisement, without you receiving any of the profit.

After everyone updated their shiny Apple devices to iOS 6 a few months ago, they were shocked to find that their beloved YouTube app was missing. As it turned out, Apple decided to kick YouTube off their list of pre-installed stock apps. The new YouTube app (found in the iTunes App Store) is definitely better than the native one from iOS 5, but it's lacking a direct upload to YouTube option. Sure, you could upload videos from your iPhone's Camera Roll, but the options are limited as to what y...

Feelings can get hurt on Twitter as fast as an update. Everything is fine and dandy because two people are mutually following each other, then out of nowhere, one person has unfollowed the other out for seemingly no reason. Twitter doesn't notify users when someone has unfollowed them, so there are millions of people out there who get used for their follow! Well, now you can find out who unfollows you on Twitter with these mobile apps.

Facebook has always been notoriously difficult to customize. Personally, I think this is an improvement over MySpace's totally open platform (some people should not use code), but users should still have the option to change a few things if they want. While you'll never be able to choose your own background image or add an obnoxious number of aWeSoMe quiz results to your profile, there are a few browser plugins that let you at least change the color scheme.

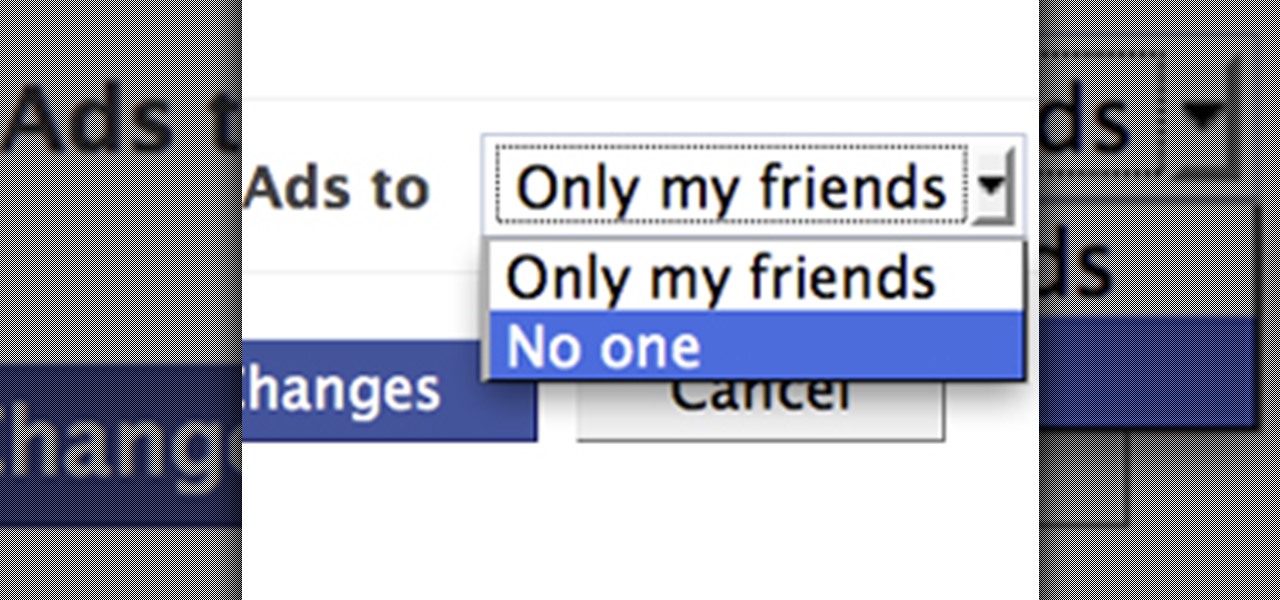
Facebook is constantly evolving, and lately it seems like a bad thing, at least for its users. First, you had to opt out of Instant Personalization, which shared your personal information with Facebook's partner sites. Then, you had to take drastic measures to secure your home address and mobile number from third-party apps and websites. And now?—Now you need to opt out of Facebook Ads.
Welcome to the server website.

Previously, we talked about how to secure Firefox. Today, we will talk about securing a Chromium based Browser. Why? Because Chrome recently beat Firefox in holding more customers.

Google's sociable equivalent to the Facebook Like button is finally here, and it works very similar to your favorite social network's recommendation system, except it shows up directly in Google search results. Whenever your Google friend gives a website or webpage the +1, you'll see it in your search results, as long as you're signed into your Google Account.

Pretty much the highest quality spray paint, great stuff.

There are hundreds of websites that claim you can win cash or prizes by signing up and using their website. Sadly, most of these are scams but there are a couple out there that are legitimate. I have investigated many of these websites and tried them out personally, with many failures. The one that sticks out the most, for me and many other people, is beezag.com. Beezag is a website that hooks you up with companies that are currently offering cash or sweepstakes entries for prizes they are gi...
So precisely what is an affiliate marketer? Essentially, an affiliate marketer has an online site and also refers guests to some other sites, called 'merchants'. When these site visitors buy things, the other websites pay the particular online affiliate marketer a payment, which depends upon online monitoring softwares which monitors web customers purchases.
This is a great website with many resources in regards to sweatshops.

Here is the trailer for BATTLE Official Website Here
HI WHY DON'T YOU CHECK OUT MY CLOWN WEBSITE BEST WISHES BERNIE

Video for Top Impresa corporate website Credits:

Sold from Korean Website 10x10

Available at on the Brass Tacks Press website: www.lifeasapoet.com

Available at on the Brass Tacks Press website: www.lifeasapoet.com

Available at on the Brass Tacks Press website: www.lifeasapoet.com

Available at on the Brass Tacks Press website: www.lifeasapoet.com

1. Type in WWW.sendthisfile.com in the web toolbar and press enter 2. Click on Register found on the top right side

First of all create a website. Go to 'file' and then click 'new'. Choose it as ‘general’ and then as 'empty'. Name this as 'practice site'. Click 'ok'. Now create your first webpage. Click on 'general', 'html' and then 'ok'. Now click on the 'file ' and then choose 'ccs' to create an external style website. This is basically a text file given a '.css' extension. Now click 'ok'. Now go back to your 'html' page and then 'save' it. Now you have to type in 'index' to replace 'default', and th...

Ownspy is powerful program which can be used to backup your iPhone remotely. This program can be used in both good and bad ways. If you have children you can keep track of them by installing this program on the phone. This regularly uploads the content from the phone to the website. So in this way you can know in what way the phone is being used. Also this can be used by a jealous boy friend to spy on his girl friend. This programs tracks your location, backs up your messages, pictures. It al...

This video will show you how to use the program Skype for online video calls. Skype is a free program that can be used through your computer to make phone and video calls. Go to Skype and download either Mac or windows depending on your platform. It will ask you to fill out some user information, including a user name. Be sure to pick a good user name as you cannot change it later on. Some features include free Skype to Skype calls, instant messaging, free video calls, calling phones and mobi...

This video describes how to insert keywords and SEO with the fusion essentials in the website. He asks you to first go to the site mode and then click on the home page and from there you can get in to the property box. There you can find three choices or tabs. He explains that the first one can be used to change the page name and page title and also can adjust the master border. The second tab is used to mention the page status, if it is done and can be displayed to the viewers or if it shoul...

In this video from PCRescueRepair we learn how to record streaming audio from any website using audacity. To get audacity just go to google, type in audacity, click on the link for audacity, and download audacity to install this on your computer. Also you need the LAME mp3 encoder which is on the audacity website. Now he takes you through the steps to do this task. Go into audacity and from the drop down change to stereo mix from microphone. On output adjust to max. and on input adjust the vo...

In this video the author gives an HTML Website Design tutorial showing how to make a side menu bar. He goes on to show how to write the HTML page, explaining about the different HTML tags like <html>, <head>, <title>, <table> etc., He shows how to set page color and add styling to the page. He shows how to align the page elements and does the font settings. He goes on and makes a HTML table. Next he shows how to make a menu bar using the table element and shows how to do the various settings ...

Even if you never took home ec, you can create simple projects by learning the basics of sewing machine use.

It was bound to happen with all those numbers floating around in your brain – you've forgotten your Windows password. Here's how to recover it.

Although mainly demonstrational, this video shows you how to play "The Dimming of the Day" by Richard Thompson. This video is intended for advanced players who learn easily by watching or listening. Read the useful tips posted below to aid your guitar learning:

Whether you are protecting your children or hiding personal information, there are ways to block unwanted websites from your computer. Follow this tutorial and learn how to accomplish this on a Windows PC easily.

So, you broke a plate and are afraid you'll get in trouble? No worries! This tutorial is coming to the rescue! Turn that old plate into a very cool distressed flower vase. Everyone will be so distracted by your crafty creation, they won't even mind that you used Grandma's China to make it.

No need to make a bad situation worse when running into an ex boyfriend or girlfriend. There is no need to be petty or spiteful when keeping to a nice yet vague conversation will ultimately leave you looking like a real class act.