While websites may run smoothly without any noticeable vulnerabilities, there's always the looming threat that any background weakness in the site can be exploited by hackers. Once a site is compromised, it can be difficult to get it fixed without the proper help. Google has recently launched a new series entitled "Webmasters help for hacked sites”, which teaches web developers and site owners how to avoid getting hacked and how to recover their website if it gets compromised in any way.

Want to secure your home? There are plenty of ways to go about it. You can make your doorbell send you a text if someone rings it while you're not home, or build a motion-triggered security camera. Even better, you can beat potential crooks at their own game by installing a door they can't even find.

While the Google Play Store is filled with big name magazines like Time, Forbes, Sports Illustrated and Maxim, it also panders to smaller audiences, like with Coin Prices, Soap Opera Digest, Watch Journal and Quilter's World (which yes, is all about quilting). If you have a select few that you enjoy reading, prices aren't usually a problem; issues range from $1.99 to $4.99 for each one, or from $19.99 to $39.99 for yearly subscriptions. If you're someone that is a magazine connoisseur, prices...

Skype is a great way to stay in contact with friends and family over the internet, and people tend to share a lot in their chats, so why not try and find a way to hack it! Once a Skype account is hacked, you can view all conversations within the last three months, see how long each video call was, and even access files that were shared through chat.

I use Google Chrome every day for my browsing needs, and I had no idea they were hiding something from me. So, I was pretty surprised to see that Chrome has an entire hidden experimental add-ons section. There are add-ons that work for Mac, Windows, Linux, and Chrome OS, so there's something for everybody.
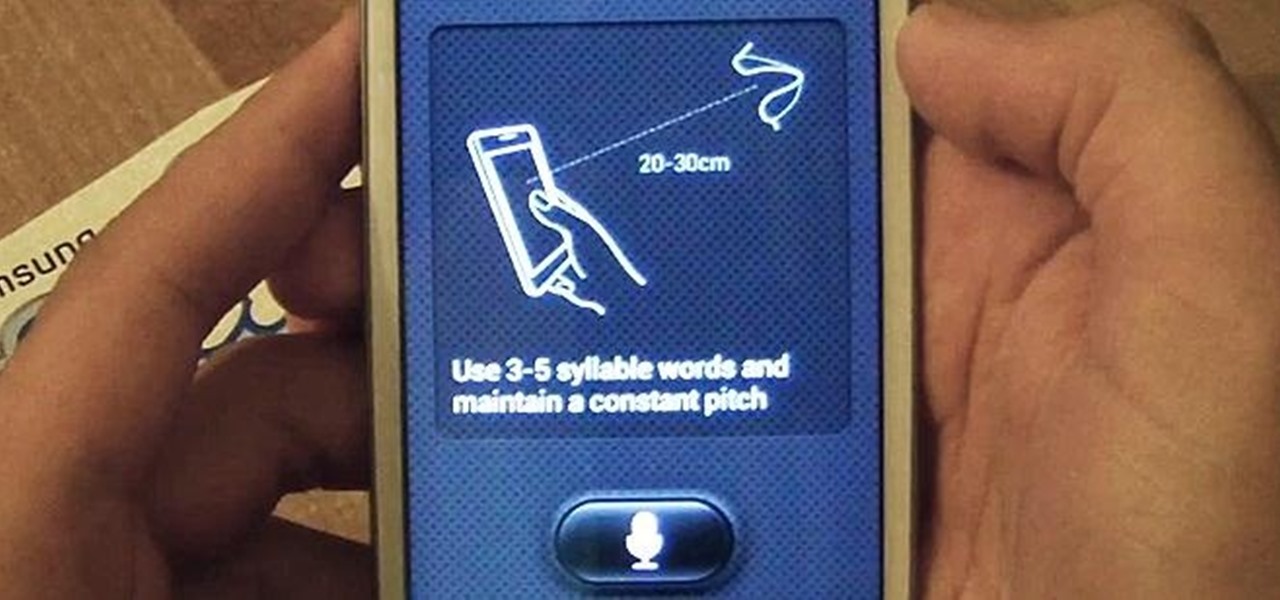
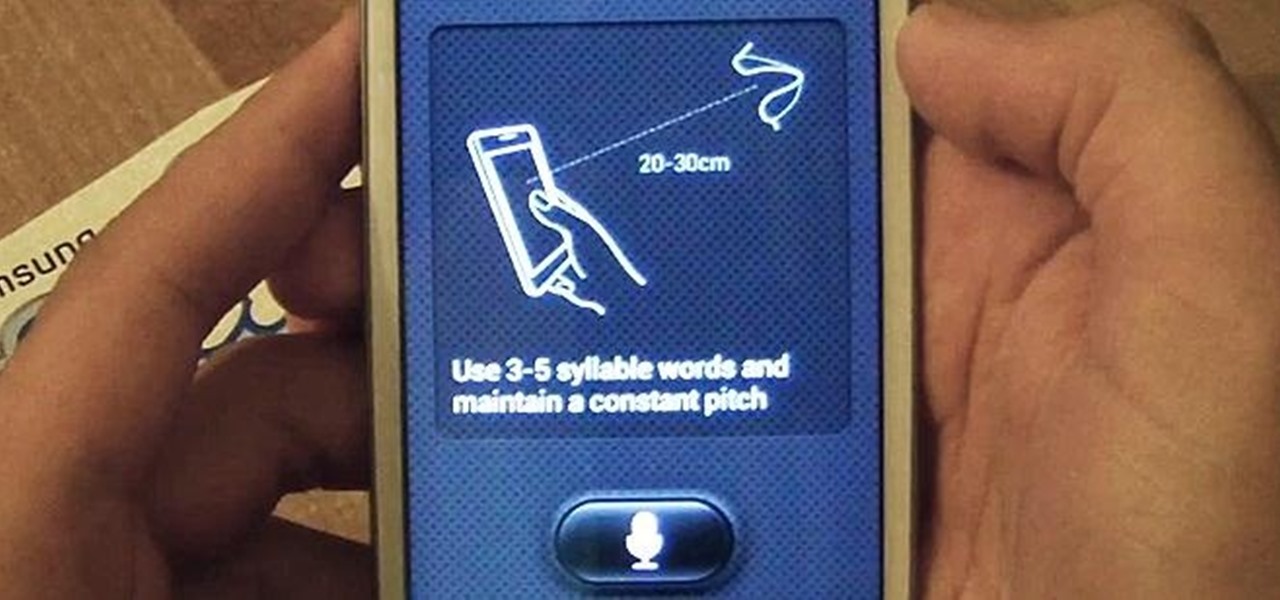
With voice commands becoming conventional on most new smartphones, it's only ideal that their abilities increase as well. Thanks to Apple's Siri, you can do things like update your Twitter account and look up who the president of Costa Rica is.

It seems like every other day there's a new security threat or data leak in the news. Whether it's your credit card PIN or your smartphone's apps leaking your email address, no one wants their personal information out there, especially passwords. And if you use the same email address and/or password for more than one site, the effects of someone getting hold of your credentials can be catastrophic.

Some of us use our smartphones for almost everything. Manufacturers know this, so they try to make their devices as convenient as possible to use, but sometimes that convenience comes with a cost to security. The very same technology that allows you to easily share music with friends and make purchases can also put you at risk. Photo by sam_churchill

If you're trying to hack someone's wifi, a useful bit of software you may want to try is called Wireshark. Wireshark is a wifi packet sniffer, which is an essential step in actually breaking into someone's wireless system. Of course, this is illegal, so make sure you're only doing it to test a network's security, or for your own educational purposes. Check out the video, follow the steps and see how secure network is. Hack, hack, hack!

If you've recently upgraded you doorknob to an elegant Schlage Plymouth Handleset, then it's time to match your front entry locks and install a new electronic high-security Schlage Plymouth Keyless Entry Deadbolt. This keypad is great if you never want to lock your bottom handleset (or doorknob). Watch this step-by-step installation video to see how it's done! You'll need a phillips head screwdriver or electric drill. To see how to install the matching handleset, click here.

In this video, we learn how to protect your privacy while using Twitter. Your personal information can get stolen in an instant with the internet. With Twitter, when you are doing updates showing where you are and what you are doing, someone could try to find you and potentially create harm to you. To help you avoid situations like this, you need to go to the security settings of your Twitter account. When you go here, you can change the account so that it only allows people you want to follo...

In this tutorial, we learn how to use the notepad to get by school internet blocks. First, open up Notepad on your computer, then type in "<html>" "<body>", "iframe src=http://www.youtube.com", then "height=100%", then "width =100%". To finishe, type in "<iframe>>/body><html>". Save this as hack.html as all files. After this, open up your browser, then you should be able to go to the website that you wanted to go to! This is a great way to get around the security settings that your school has...

In this video tutorial, viewers learn how to test their system performance. Begin by clicking on the Start menu and select Control Panel. Then click on System and Security, and select "Check the Windows Experience Index" under System. Now click on "Rate this computer". The system will then begin to run some tests. This will take about 1-2 minutes. The Windows Experience Index assesses key system components on a scale of 1.0 to 7.9. This video will benefit those viewers who use a Windows 7 com...

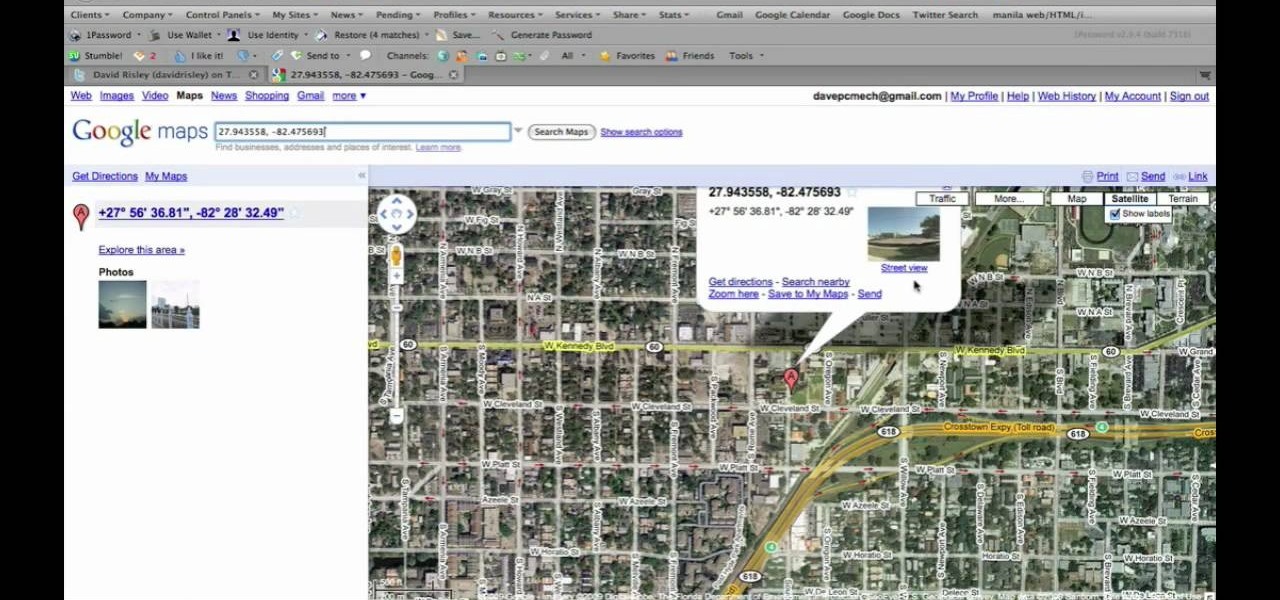
Many applications, especially those found in the Android Market are more effective when they know your physical location; like an app that's going to find the nearest gas station, restaurant or ATM. One of the salient advantages of a Google Android smartphone over, say, an Apple iPhone, is the inherent extendibility of the open-source Android mobile OS. There are a seemingly infinite number of settings to tweak and advanced features to discover and use. This free video tutorial, in particular...

Fashion designer Cate Adair demonstrates dressing with a sarong for Modern Mom. She also discusses how to buy or extend a sarong when the one you find isn’t long enough. One important consideration for beginners is finding a sarong that can wrap around the body twice for security. One way she wraps is to simply wrap under the armpits twice and tie a flower or ornament with the corner. Another way is to put the full sarong on from the front, wrap each end backward and then over the shoulders...

In this video, Mike Callahan shows us how to make our unlock pattern visible on an Android phone. First, unlock your phone and go to the home screen. Then, go to 'settings, location & security". After this, click the button that says "use visible pattern" so that the check mark and button are both gray instead of green. To test this, tap back on the home screen and lock your phone. Now, when you draw in your pattern you will be able to see it on the screen. This way you can see the pattern as...

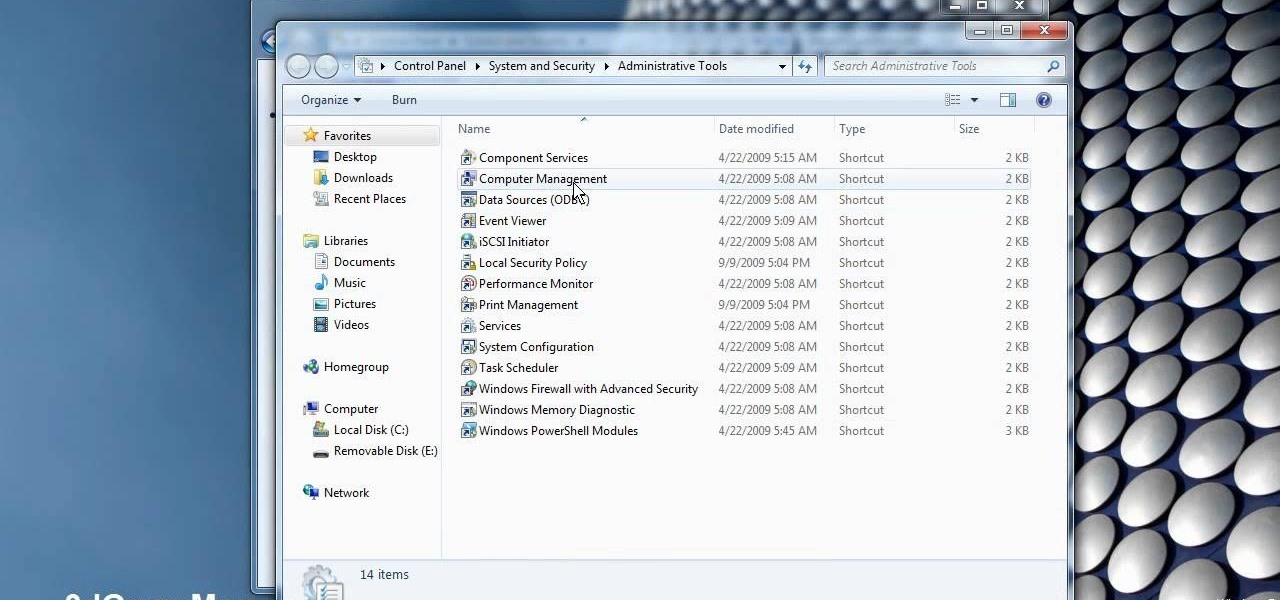
This video demonstrates how to change a drive letter to a certain drive in your Windows 7 computer. On you Windows 7 computer, go to Start > Control Panel. In the Control Panel, select System and Security then open the Administrative Tools. Look for and open the Computer Management tool. On the left side pane of the Computer Management window, select Disk Management. Look for and right click on the drive you want the drive letter changed. Select 'Drive Letter and Paths...'. Click change and s...

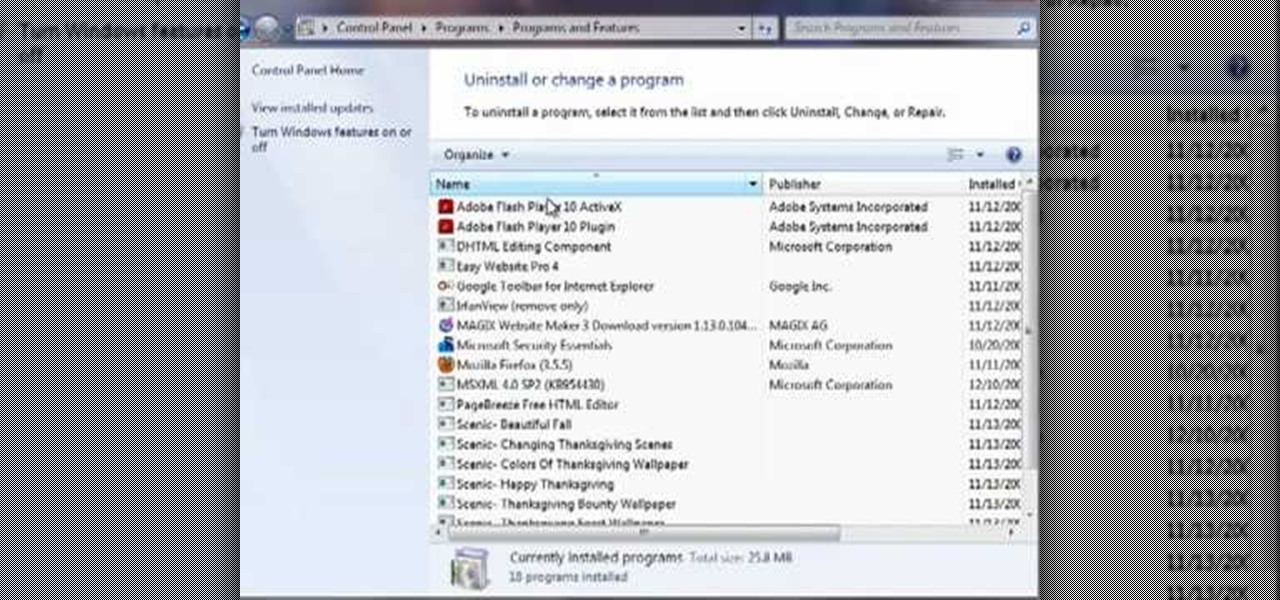
This video by Butterscotch shows viewers how to uninstall a program in Windows 7. To begin, click on the start button at the bottom-left of the screen. Click 'Control Panel' in the boxes that pop up. Click 'System and Security'. On the left side of the window, there will be a link marked 'Programs'. Click on it. Click 'Uninstall a program' beneath the 'Programs and Features' heading. Highlight the program you want to uninstall, then click the 'Uninstall/Change' button near the top of the wind...

The video shows us how to use a proxy to bypass the Internet Filters. Most of the times in our schools and colleges most of the websites including the social networking ones will be blocked for security reasons and makes us unable to log into those websites. In such cases even the ones from the YouTube, several videos will be blocked. So in this video, we will be shown how to bypass those filters and log into those sites. Firstly go to the website Proxapp and over there you will be asked the ...

RAID, or Redundant Array of Independent Disks, lets you divide and replicate data among multiple hard disk drives for information storage security. This video tutorial demonstrates how to install Ubuntu in a RAID 0 array. Before starting, you'll need at least 2 hard drives and an Ubuntu alternate installation CD. RAID 0, or striped disks, let's you install an operating system, such as Ubuntu, on a partition, while using others for data storage, as illustrated in this instructional segment.

In this video you will learn how to update your version of Windows 7 and how to check the system settings for automatic updates. In order to do this you need to go in the Start Menu and then in the Control Panel. Then you need to click System and Security. The next step is to click Windows Update. A new window will pop-up and you will see two types of updates: Important Updates and Optional Updates. To install them just click on the blue link and then check the boxes. To check for updates you...

Microsoft recommends a unique user ID and password for every user. In order to switch user ID or log off one need to click to the 'Start' menu as shown in the video. Press the move button at the shut down menu as shown. In the sub menu you can see the Change user and Log off. The window will typically shut down and restart on change of user ID or Log Off. In case you need to leave your PC unattended you can press 'Lock' from the same menu which will refrain anyone from changing your desktop s...

Check out this Mahalo video walkthrough of Marshlands in Resident Evil 5. Resident Evil 5 (RE 5) is the sequel to 2005's Resident Evil 4. This game guide shows you BSAA emblem locations, treasures, and includes strategies for all 6 missions and boss fights.

VNC stands for Virtual Network Computing. It is remote control software which allows you to view and fully interact with one computer desktop (the "VNC server") using a simple program (the "VNC viewer") on another computer desktop anywhere on the Internet. The two computers don't even have to be the same type, so for example you can use VNC to view a Windows Vista desktop at the office on a Linux or Mac computer at home. For ultimate simplicity, there is even a Java viewer, so that any deskto...

In this tutorial, Mike Lively of Northern Kentucky University gets you started in getting the Adobe Air Content Management System up and going.

The HP 2710p business notebook has a number of innovative security tools to make sure your data stays where you want it.

For Infinity Exists Full Disclosure's first Website Hacking episode, we demonstrate how to exploit a security vulnerability occurring in a website's database to extract password hashes. Sql (Structured Query Language) is a computer language designed for the retrieval and management of data in a system's database. The Attack, known as Sql Injection, manipulates Sql statements before they are sent to the Sql Server, allowing the Attacker to create, change, or retrieve data stored in the database.

In today's world of social media, there's really only two powerhouses—Facebook and Twitter. And those of you with Twitter accounts know the power of a Tweet. Getting more followers means reaching more people, but the vast majority of Tweeters are following only a handful of Twitterers themselves. Do you ever wonder why them? What's so special about these selected followed users? Is it worth it to follow them, too? That's up to you, but if you're searching for more people to follow, then it's ...

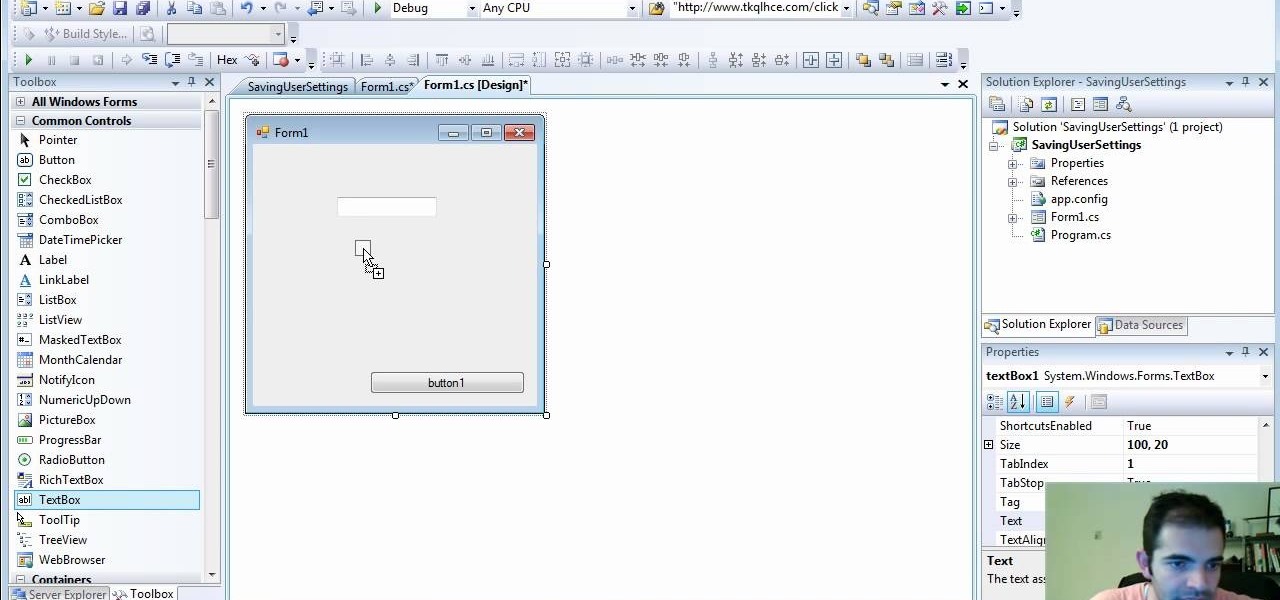
Check out how to save your user settings in Microsoft Visual Studio using C# programming, that way when you restart the program, it can remember some of your important information. This will specifically show you how to save your user settings using the .NET Framework instead of working with custom INI files.

Want to delete your Pro Tools user preferences in Mac OS X Snow Leopard (10.6)? Whether you're new to Digidesign's Pro Tools 8 or simply looking to pick up a few new tips and tricks, you are certain to benefit from this free software video tutorial, which presents a complete overview of how to trash your Pro Tools user preferences.

Depending on what your website is for, you may or may not care about allowing your users to download files from you. If hosting downloadable content sounds like something you want to do, watch this video! It will teach you how to allow your users to download files from your website using Dreamweaver. It's not very hard, and your users will probably be thankful that they don't have to go on the web every time they want to access your content.

Almost every website on the web has buttons that enable users to interact with it. They are easy to make, but making them interesting and reactive to user's activities is more of a challenge. This video demonstrates how to create animated rollover buttons in Adobe Flash CS4 quickly and easily. Your website will be much more dynamic and enticing if you apply the skills taught in this video.

In this 14th video in a series about JAVA game development, "thenewboston" (Bucky Roberts) explains how to redefine your screen to avoid annoying flickering. Flickering in JAVA games often occurs because of time lags as the viewer watches the computer draw a new screen, pixel by pixel. Pre-installed code in JAVA can be used to eliminate this problem by taking advantage of "Buffering" and "Page Flipping". These functions permit you to delay the composition of a new screen until it is finished,...

Users will need an exercise ball to perform this exercise. Begin by going on your knees and elbows on the ball. Users basically go into a plank position in the ball. Now users will need to go into a straight position from the shoulders to the knees. Now users will draw the alphabet using their elbows, while rolling the ball. To make the exercise more challenging, users may choose to lift one or both knees off the ground while doing the exercise. This video will benefit those viewers who want ...

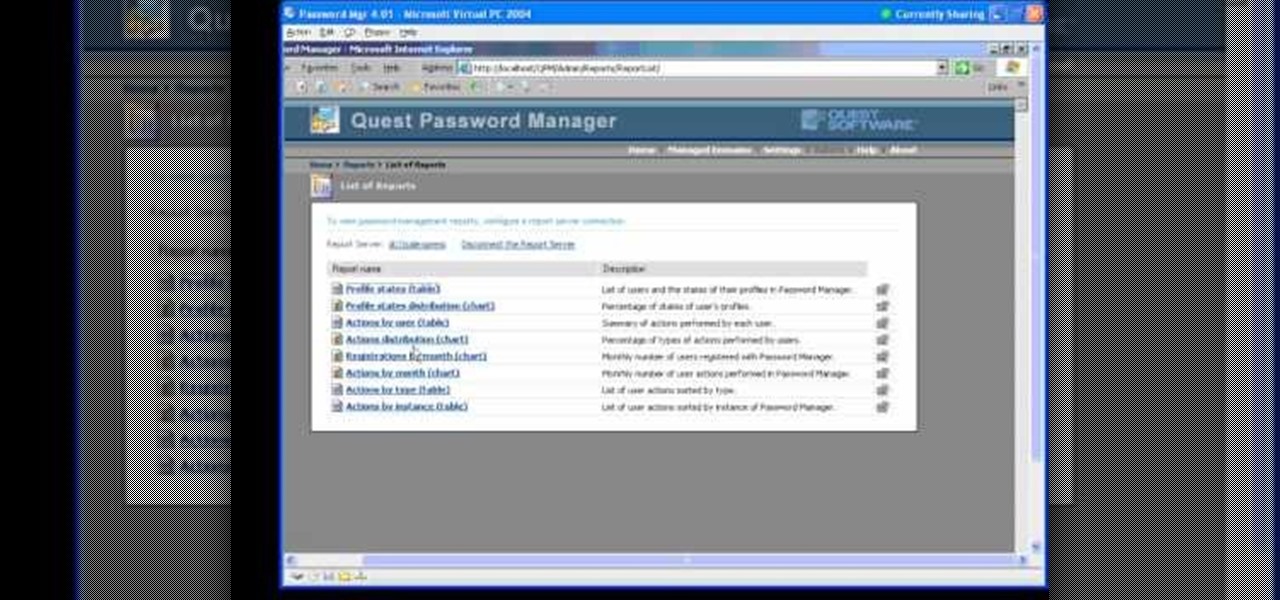
In this Webcast, Password Management for Windows and Beyond, you will learn how to: Increase security standards cross-organization by easily customizing and enforcing password policies for Windows, Unix, Linux, and Java users.

Consider this reason 1,001 why we love the internet: Using Google, you can hack into almost any webcam or security cam, in any part of the world and even control the webcam to move around so you can get your full panoramic shot. Don't believe us? Then check out this video tutorial to learn the steps you need to take.

The passcode, or the four-digit code you enter in order to access an iPhone or iPod touch, was created to ensure security and prevent hacking. But what if you haven't touched your iPhone in a month and you simply don't remember what your passcode is anymore?

Different ways of using a proxy bypass to access blocks sites is shown with ease in this video. Many places explained to be blocked with internet security such as libraries and schools. Using a search engine such as Google you need to search for a proxy site. After a proxy site has been found you will use it to access the blocked websites through another servers internet provider. The narrator explains that proxies are just a way to bypass internet blocks by avoiding using the blocked compute...

In this video from apexcctv we learn how to find your public IP address and then use dynamic DNS to keep it updated in regards to your security needs. If you go to Whatismyip.com you will see your IP address. You can also go to Google and search for "find my IP address." A service called Dynamic DNS keeps track of your customers IP address. It will map a name to an IP address. Static DNS entries do not change. To set up DNS you can go to CCTV tutorials on the ApexCCTV website. You should set ...

This video tutorial is in the Computers & Programming category which will show you how to hack a wireless network with WEP encryption. This video is intended only as a means of testing the security of your own network. Go to Backtrack Linux, download the backtrack4 and burn it to a DVD. Now put it in a computer with a wireless card and restart the computer so that it boots to the DVD. When it boots up, type "startx" to start the interface. Bring up the command prompt and type in "/etc/init.d/...